Contents:
Throughout the past couple of decades, cyber threats have grown drastically in size and complexity and rendered traditional security defences insufficient. For this reason, cybersecurity prevention and mitigation methods were compelled to keep pace with these ever-growing threats.
Although all cybersecurity strategies should be based on a prevention-first mindset, this approach alone will not suffice. Instead, monitoring and remediation should also be included, especially when it comes to mitigating targeted, high-profile attacks. It’s not only about ensuring absolute prevention – but it’s also about understanding how to respond should an incident occur and achieving a state of cyber resilience.
A means of defending your IT infrastructure is through the cyber kill chain framework. Regardless of what vectors of attack we’re looking at and no matter if they’re coming from the inside or outside the organization, they can be successfully identified thanks to this model.
What is the Cyber Kill Chain?
The cyber kill chain is a cybersecurity model used to describe and track the stages of a cyberattack. Fundamentally, the cybersecurity kill chain is the visualization and study of an attacker’s offensive behavior.
This cybersecurity framework allows infosec teams to impede the assault during a certain stage and consequently design stronger security and enhance their incident response and analysis capabilities.
The cyber kill chain is a blueprint for operating in a staged way, that incident response teams, forensics experts, and malware researchers can use to detect and stop cyberattacks at different stages of the chain.
Who developed the Cyber Kill Chain Model?
The cyber kill chain or “cyber-attack chain” was created in 2011 by Lockheed Martin. The framework has evolved since its beginning to help predict and detect various cyber threats, such as insider attacks, social engineering, ransomware or other sophisticated malware, APTs, data breaches, etc.
“Kill Chain” is a concept that was first adopted by the military to describe the actions used by an adversary to attack and destroy a target. In essence, it relates to what an assault would look like from a military perspective and describes all stages that attackers go through. Recognizing the kill chain phases will help the line of defence correctly identify the intruders and stop them faster.
The Cyber Kill Chain Steps
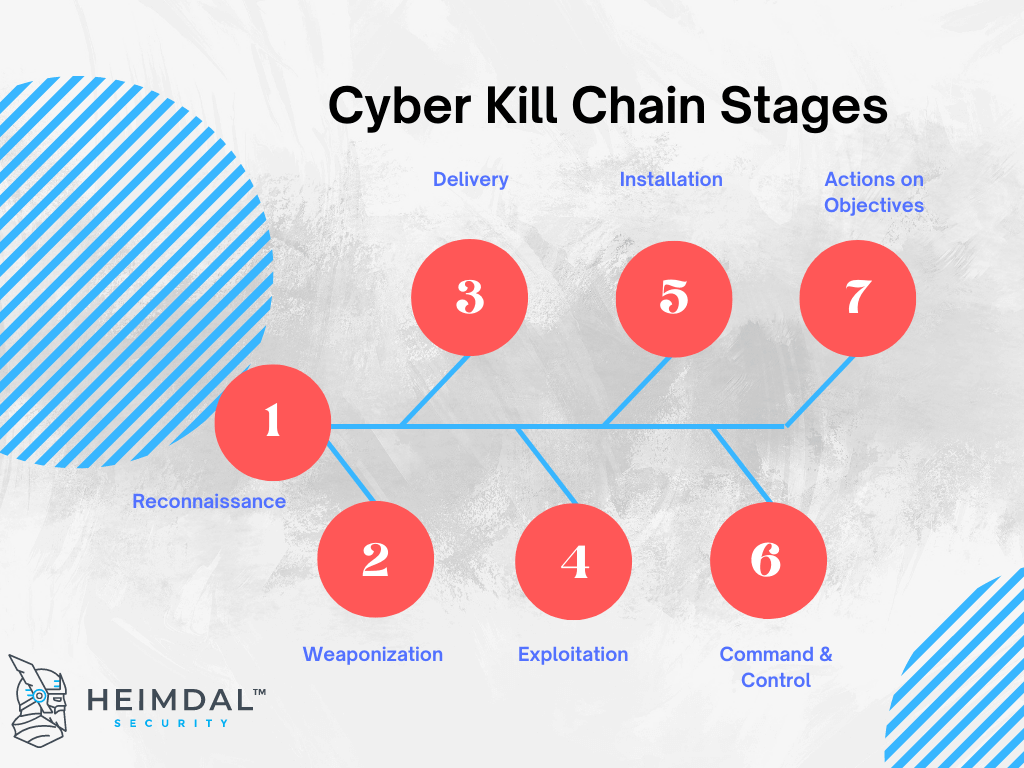
The cybersecurity kill chain is comprised of seven key steps: reconnaissance, weaponization, delivery, exploitation, installation, command & control, actions on objectives.
It offers a mechanism of breaking down a dynamic attack into generic steps so that they can be better examined. This layered tactic would allow observers to fix smaller and simpler challenges, while also helping defenders thwart each stage by designing protection and mitigation methods.
Now, let’s break down each of the kill chain stages.
1. Reconnaissance
This stage involves collecting data about the future target (a person or an organization).
It is further necessary to break down reconnaissance to target identification, selection, and profiling.
Cyberspace identification primarily means crawling the World Wide Web (e.g. websites, conferences, blogs, social relationships, mailing lists, and network tracing software) to obtain information about the target. In later phases of the cyber kill chain, data collected from reconnaissance is used to plan and distribute the payload.
The reconnaissance stage is classified into two types:
- Passive recognition: This move is achieved by collecting target information without him/her being aware of it.
- Active recognition: This stage requires much thorough analysis of the target.
Reconnaissance offers information about potential targets, which will allow the intruder to determine the type of weapon necessary to infiltrate the target, potential types of delivery methods, issues with malware installation, and the protection measures that need to be circumvented.
Next, you will see how advanced malware is created using the knowledge obtained in the reconnaissance stage.
2. Weaponization
The cyber kill chain’s Weaponization stage deals with the creation of a backdoor malware and a penetration strategy using the knowledge gathered from reconnaissance to enable the backdoor to be delivered successfully. In this instance, a Remote Access Trojan (RAT) will be used.
Weaponization entails the creation and development of two components:
- RAT (Remote Access Trojan)
Typically considered the payload of a cyber-weapon, RAT is a piece of software that executes on the machine of the victim and allows the intruder remote, secret, and unobserved entry. It can provide “system exploration, file upload or download, remote file execution, keystroke monitor, screen capture, webcam or system power on/off with limited or user-level privileges”, Yadav notes.
- Exploit
This is the part of the weapon which allows the RAT to run, acting as a carrier for the RAT and leveraging system or software vulnerabilities. The key aim of using exploits is to evade user detection by using the RAT to construct a silent backdoor entry. There can be several kinds of infection sources, such as MS Office files, PDFs, audio/video, or web pages. More vulnerabilities such as privilege escalation exploits can be used on the target after having a RAT installed to get elevated privileges, and then further disseminate the RAT, ensure permanent access or even break the entire system.
Cyber Kill Chain Weaponization Case Study
Bank Security’s Excel weaponization via the Metasploit SMB delivery module
Bank Security’s case study proved that even something as an innocuous an MS Excel document can be transformed into an exploit that fends off most inline-AVs. The case study showcases the way a malicious payload can be downloaded and executed on a machine, by embedding it in VBS macro.
Abstract: a module that contains a custom or ready-made code is loaded into Metasploit. The module is configured to exploit windows/smb/smb_delivery. Once the command is executed, the appropriate malicious Dynamic Link Libraries files are loaded. The target’s ID and .dll must also be specified. Once the config stage is over, the exploit command can be run. A Meterpreter reverse shell will be opened on the victim’s machine (this will be done after the meterpreter_reverse_tcp is set in place).
A command exploitation line will be generated. This must be run on the victim’s machine. Pasting it in the Run window will trigger detection by AV. Weaponization is achieved by embedding a malicious server-generated command line in an Excel VBS macro. Once the user opens the excel sheet, the command line will be automatically executed in the background, triggering the exploitation.
For additional details and full technical documentation, please refer to this on Excel weaponization.
3. Delivery
Delivery is a crucial component of the cyber kill chain and is responsible for an efficient and powerful cyber-attack. Any type of user activity, such as uploading and executing infected files or accessing malicious web pages will be necessary for most attacks.
For an intruder, delivery is a high-risk assignment because it leaves traces. Many of the attacks are thus carried out anonymously using online payment providers, hacked websites, and compromised email addresses.
Delivery mechanisms include:
- Email attachments
- Phishing
- Drive-by Downloads
- USB/Removal Media
- DNS Poisoning
4. Exploitation
After the cyber weapon is shipped, the next step is executing the exploit with the aim of silently installing the payload and executing it.
The exploit will only work on outdated systems and most probably will not be picked up by traditional security tools, like Antivirus or Firewalls.
Essentially, exploitation is the most critical stage within the cyber kill chain. We often bring up the importance of patch management and keeping up with the latest software updates to close security holes in your organization. So, on a side note, I suggest you check out our Patch & Asset Management solution, which enables you to achieve compliance, mitigate exploits, close vulnerabilities, deploy updates, and install software remotely and according to your schedule. Our tool covers both Microsoft and 3rd party application management and comes with customizable set-and-forget settings for automatic deployment of software and updates.
5. Installation
Traditionally, an infection vector such as corrupted disposable media will infect a device, which in turn would leave a malware executable that will operate every time the computer boots up. Consequently, users would report this executable to their security provider, who would evaluate it and come up with a signature to detect it and a removal tool. Modern malware no longer works in such a simple manner, now relying heavily on droppers and downloaders to distribute the malware modules in a far more advanced way.
6. Command & Control
The C&C server, used to send remote hidden instructions to compromised computers, is an essential part of any cyber-attacks. It also functions as the location where the data is exfiltrated. Throughout the years, due to the exponential growth of defense mechanisms, including antiviruses, firewalls, IDSs, etc, the design of C&C networks has greatly developed.
C&C server connections can be prevented with DNS filtering tools. For instance, Heimdal’s DNS security tool stops threats at the DNS, HTTP, and HTTPS-level, detecting and stopping DNS hijacking, exploits, ransomware, data leaks, and more.
7. Act on Objectives
In the final stage, the intruder executes the commands after the connection with the target device is established. The command used by the attacker depends on the attack’s purpose.
Mass Attack
Mass attacks are aimed towards reaching as many targets as possible – multiple systems combined are of concern in mass attacks, rather than a single system. Many of these assaults have the objective of harvesting the victim’s credentials. Botnets, which are mostly used for DDoS attacks and virtual coin mining, are some examples of mass attacks. I’ve also written an article on how to prevent a botnet attack from compromising your business, so I suggest you check it out as well.
Targeted Attacks
Targeted attacks are more sophisticated and more carefully conducted and are aimed towards a single entity, with the purpose of exfiltrating data such as login credentials. For example, when the target is a single enterprise, moving laterally inside the network becomes a primary goal.
How To Effectively Use The Cyber Kill Chain in Your Cybersecurity Strategy
The cyber kill chain model approach to threat detection & mitigation incorporates elements from MITRE’s attack/response shell. As opposed to the rather theoretical framework proposed by MITRE, CKC has a more ‘hands-on’ approach, and can easily be integrated into the formulation of a cohesive and proactive cyber-defence strategy. Although not a solution on its own, CKC can provide an insightful glimpse into the mind of a cyber-criminal and aid the CSIR team in formulating ‘kill’ phase-based counter-actions.
There are 6 layers of security controls that can be implemented at different stages to prevent or stop an attack.
- Detect – Analyze and find the intrusion attempts.
- Deny – Stop the attacks as they happen.
- Disrupt – Stop the data communication
- Degrade – Reduce and limit the efficacy of the attack.
- Deceive – Lead the attackers in the wrong direction.
- Contain – Conceal and restrict the attack’s reach so that it only affects a portion of the organization.
Let us take a closer look at how to devise an appropriate strategy based on the associate kill phase.
1. Reconnaissance stage
The counteractions in this stage are Detect & Deny.
Detection: Web analytics, Threat Intelligence Platform (TIP), Network Intrusion Detection System (NIDS)
Deny: Firewall, Network Intrusion Prevention System (NIPS)
2. Weaponization stage
Appropriate counteractions
Detection: Network Intrusion Detection System (NIDS)
Deny: Network Intrusion Protection System (NIPS)
3. Delivery stage
Possible counteractions
Detect: User Vigilance, Email Security, Endpoint Protection (EPP, EDR), DNS Filtering
Deny: Privileged Access Management, Zero-Trust, Application Control, Proxy Filter, Host Intrusion Prevention System (HIPS), DNS security
Disrupt: Antivirus
Degrade: Queuing
Contain: Router Access Control Lists, Application-aware Firewall, Trust Zones, Network Intrusion Prevention System, Network Segmentation
4. Exploitation stage
Possible counteractions
Detect: Endpoint Protection, Host Intrusion Detection System (HIDS)
Deny: Patch Management, Privileged Access Management, Application Control, Secure Passwords, Zero-Trust
Disrupt: Data Execution Prevention (DEP), Antivirus
Contain: Application-aware Firewall, Trust Zones, Intrusion Prevention System, Network Segmentation
5. Installation stage
Possible counteractions
Detect: Security Information and Event Management (SIEM); Host Intrusion Detection System
Deny: Privileged Access Management, Secure Passwords, Two-Factor Authentication, Application Control, Zero-Trust
Disrupt: Router Access Control Lists, Antivirus
Contain: Application-aware Firewall, Trust Zones, Network Intrusion Prevention System, Network Segmentation
6. Command & Control stage
Possible counteractions
Detect: Network Intrusion Detection System (NIDS), Host Intrusion Detection System (HIDS)
Deny: Firewall Access Control Lists, DNS Filtering
Disrupt: Host Intrusion Prevention System (HIPS), Network Intrusion Prevention System (NIPS)
Degrade: Tarpit
Deceive: DNS Redirect
Contain: Trust Zones, DNS Sinkholes, Network Segmentation
7. Action on Objectives stage
Possible counteractions
Detect: Endpoint Protection (EPP, EDR), Log review
Deny: Encryption Protection
Disrupt: Endpoint Protection (EPP, EDR)
Degrade: Quality of Service
Deceive: Honeypot
Contain: Incident Response
Bottom Line
The rise of sophisticated attacks carried out by threat actors, who now can gain access to advanced resources and technologies that help them achieve a pervasive and undetected presence, is one of the main challenges faced by organizations. The cyber kill chain examines the cyber-attack flow, with each stage being of critical importance.
Studying the cybersecurity kill chain at every stage of the assault can help security teams detect and minimize threats. The sooner the identification is completed, the better the damage can be mitigated.
Cyber security incident response is a must, regardless of company size or profile. Second-generation malware is more insidious and viral compared to their distant cousins and simple antivirus solutions are simply not designed to detect & mitigate this type of incursions.
Cyber kill chain is not a panacea – implementing this detection & mitigation model does not preclude malicious data exfiltration and system compromise. As always, vigilance and well-managed cybersecurity grid is the key to prevent any future incursions.
See how the Heimdal cybersecurity solutions work in synergy to detect and stop attacks at every stage of the kill chain.

- End-to-end consolidated cybersecurity;
- Complete visibility across your entire IT infrastructure;
- Faster and more accurate threat detection and response;
- Efficient one-click automated and assisted actioning










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








