Contents:
The DNS in and of itself has never been secure. Being created in the 1980s when the Internet was a complete novelty, protection had not been a priority in its design. Throughout time, this has led malicious actors to take advantage of this issue and develop elaborate attack techniques that leverage the DNS, such as DNS spoofing.
In the following lines, I will go over the definition of DNS spoofing, as well as the most common methods cyberattacks employ for it. In addition to this, I will also present a simple, step-by-step overview of an attack and a few tips on how to prevent it. So, without further ado, let’s get into it.
Read on to learn:
- What is DNS spoofing
- DNS spoofing methods
- How DNS spoofing works
- How to Protect your endpoints against DNS spoofing
What is DNS spoofing?
DNS spoofing is a cyber-attack in which fake data is introduced into the DNS resolver’s cache, which causes the name server to return an incorrect IP address. In other words, these types of attacks exploit vulnerabilities in domain name servers and redirect traffic towards illegitimate websites.
When a recursive resolver sends a request to an authoritative name server, the resolver has no means of checking the response’s validity. The best the resolver can do is check if the response seems to come from the same IP address where the resolver sent the query in the first place. But relying on the source IP address of response is never a good idea since the source IP address of a DNS response packet can be easily spoofed.
Security-wise, due to the faulty design of the DNS, a resolver can’t identify a fake response to one of its queries. This means cybercriminals could easily pose as the authoritative server that was originally queried by the resolver, spoofing a response that seems to come from that authoritative server.
In a nutshell, an attacker could redirect a user to a malicious site without the user noticing it. In a nutshell, DNS spoofing refers to all attacks that attempt to change the DNS records returned to the user and redirect him/her to a malicious website.
DNS spoofing methods
A DNS spoofing attack can occur under many guises. The most widely spread techniques used by hackers for this are DNS hijacking, cache poisoning, and man-in-the-middle (MITM) attacks. Perpetrators can use one of these methods, or a combination of them to achieve their nefarious goals. Let’s have a quick look at how each tactic works.
DNS hijacking
Also known as DNS redirection, DNS hijacking is a type of spoofing attack in which a user’s query is resolved improperly to redirect them to a malicious site instead of their target destination. Cybercriminals use various tactics to achieve this, either taking over routers, intercepting DNS communications, or deploying malware on the target’s endpoints.
DNS cache poisoning
In the case of cache poisoning, cyber attackers utilize modified DNS records to redirect online traffic to a malicious website that is designed to resemble the user’s intended query. This technique is usually employed to steal login credentials, as targets are immediately prompted to login into the fraudulent page. In addition to this, the website might attempt to install malware on the user’s endpoint to grant the perpetrator long-term access to the company network.
Man-in-the-middle attacks
DNS spoofing can also act as a type of man-in-the-middle attack, where a malicious actor intercepts a DNS query and returns a duplicitous page instead of the real thing. Besides directing potential victims to a phony site that is designed to replicate the user’s intended destination, hackers attempting a MITM attack sometimes simply relay the traffic of the real website and steal your information silently, in the background.
How DNS spoofing works
As I mentioned above, DNS spoofing comes with a few different methods which hackers can use independently or in tandem. Regardless of their MO, however, an attack of this sort will always have three essential steps – recon, access, and attack. Here’s a breakdown of what happens at each point in the operation.
Step 1 – Recon
The first step in launching a DNS spoofing attack is recon – the DNS server’s MAC address, software versioning, known vulnerabilities, average requests handled per hour, any kind of DNSSEC (Domain Name System Security) employed, communication protocols, and encryption algorithms, etc.
Step 2 – Access
Once recon’s complete, the malicious actor would go about gaining access to the DNS server. Bear in mind that the hacker doesn’t want complete and utter control over the server. That would be pointless. Instead, he will inject fake DNS entries to reroute connections.
This step achieves three goals: corrupt a ‘healthy’ DNS registry, dupe the client into connecting to a malicious server, and, last, but not least, ‘convince’ the DNS server that the entry for the malicious site is correct and legit. So why is it also known as poisoning? Because, just like poison permeates every tissue and cell, so do spoofed DNS entries.
How does this ‘contagion’ spread? DNS servers don’t act of their own accord – they communicate with other DNS servers. A single server doesn’t know the numerical addresses of all websites. But they can ask others for help.
Imagine what happens when a ‘poisoned’ DNS server contacts another server to inquire about an address? The second one gets infected as well. And the process goes merrily on until the faulty entries are detected and purged.
Step 3 – Attack
As a consequence, the user is going to find himself in a world of trouble. So, you send the query to the DNS server for, let’s say facebook.com. The server which, at some point, became ‘poisoned’, searches for the entry, and sends back the request.
Keep in mind that the server is unaware that its records have been tampered with because it doesn’t employ any form of security. Now, the user will be redirected to the address indicated by the DNS server.
Only it’s not the real Facebook, but a cloned website that looks exactly like the real one. From there, the hackers can perform various data exfiltration operations on the victim’s machine: data-stealing forms, malicious payloads embedded in auto-run Office macros, install spyware or traffic sniffers, launch DDoS, etc.
In 2022, a staggering 88% of organizations fell victim to DNS-based attacks, with an average of 7 attacks per organization, each costing around $942,000 and leading to application downtime for 70% of these entities.
But despite the high prevalence and cost of DNS attacks in 2022, where 24% of organizations experienced data theft, a concerning 43% still did not employ a dedicated DNS security solution.
2022 Global DNS Threat Report by IDC
How to protect your endpoints against DNS spoofing
While DNS spoofing attacks are undeniably cunning, they can also be prevented with a few additional security measures, as well as advanced solutions. Here are a couple of actionable tips that will help you prevent an incident of this kind in your enterprise and cover all attack vectors.
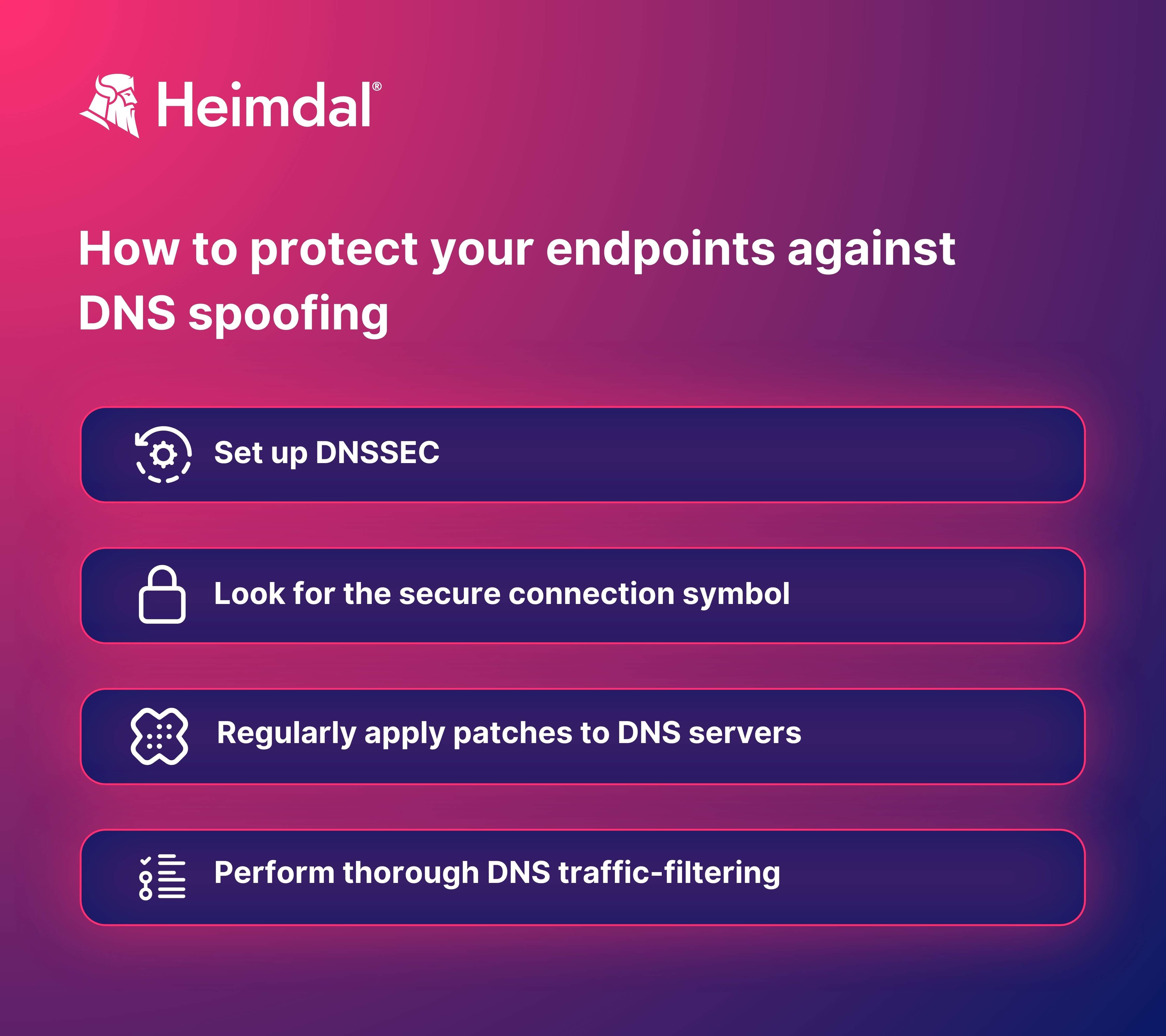
1. Set up DNSSEC
DNS Security Extensions (DNSSEC) are widely used to protect the server’s register against outside tampering. Through complex cryptography, digital signatures, and additional methods, the DNSSEC system validates responses to domain name queries, ensuring that duplicitous redirections do not occur at any point during the process.
There are two main steps in activating DNSSEC for a certain domain. First and foremost, you need to add DNSSEC-related records to your DNS zone. Then, you have to publish the respective DNS records, and the change will take up to 24 hours to come into effect. For more information on how to do this on Google domain name servers and custom domain name servers, you can have a look at the dedicated Google Support guide.
2. Look for the secure connection symbol
Navigating the Internet safely is made easy by the secure connection symbol that indicates a page is authentic. When opening a website, look for the padlock symbol next to the address bar. This indicates that your connection is secured. No padlock indicates that the website may have been cloned for malicious purposes, so it’s best to steer clear of it to protect your data and other digital assets.
3. Regularly apply patches to DNS servers
Patching is not only important to endpoints and the software that is installed locally on them. DNS servers need them as well, as they have their own vulnerabilities. Ensure that the DNS server you’re using has been patched to the latest version to avoid any breaches. Using automated patch management software can help you ease this process along.
4. Perform thorough DNS traffic-filtering
Advanced DNS traffic filtering has proven to be the best method to identify and combat DNS-delivered attacks. Consider deploying a cybersecurity solution that packs active DNS filtering, such as our Heimdal® DNS Security.
DNS Security comes with a proprietary, two-way traffic filtering engine that works at DNS, HTTP, and HTTPS levels. Our solution actively hunts for tampered Internet traffic, preventing unfortunate occurrences of DNS spoofing from affecting your company’s endpoints.
Heimdal® DNS Security Solution
Conclusion
DNS spoofing affects the server’s DNS registry, actively redirecting the client to a malicious address during a query. How does your organization protect itself against spoofing attempts?
A DNS filtering solution like our Heimdal® DNS Security hunts, prevents, detects, and blocks threats at the traffic level. Traditional defenses don’t offer protection against DNS attacks. But thanks to its machine learning-driven DNS filtering system, Heimdal brings you full DNS protection and malware blocking.
Contact us today at sales.inquiries@heimdalsecurity.com if you’d like to learn more.
If you want to learn more about DNS Security, make sure you also check out this video:










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security









