Contents:
DNS over HTTPS (DoH) prevents hackers from reading or changing your DNS queries and responses. Although it also has some downsides, DoH made online communication safer and reshaped the digital landscape.
In some cases, DNS over HTTPS can clash with your cybersecurity solution. To make it work to your advantage and enjoy the benefits of safer network communications, you need to implement DoH right.
Key takeaways
- DNS over HTTPS (DoH) helps you get better privacy, due to DNS queries encryption.
- DoH is different than DNS over TLS (DoT). They use different ports.
- Enabling DoH in browsers or operating systems can impact in place DNS traffic filtering tools.
- Windows 10 doesn’t offer a DNS over HTTPS option. You can only enable the DoH feature in Windows 11.
What Is DNS over HTTPS (DoH)?
DNS over HTTPS (DoH) is an internet security protocol that communicates domain name server information in an encrypted way over HTTPS connections. DoH uses port 443, just like HTTPS does. It blends in DNS requests in HTTPS queries, so DNS traffic gets unobserved among other HTTPS activity.
The standard released by the IETF allows DNS protocol to be enabled over HTTPS connections, which is HTTP’s safer version.
In 2018, Mozilla was the first to encrypt DNS traffic before it sent it through HTTP or HTTP/2.
In the years that followed, big internet brands, like Apple, Microsoft, and Google implemented DNS over HTTPS (DoH) to prevent eavesdropping and DNS data manipulation.
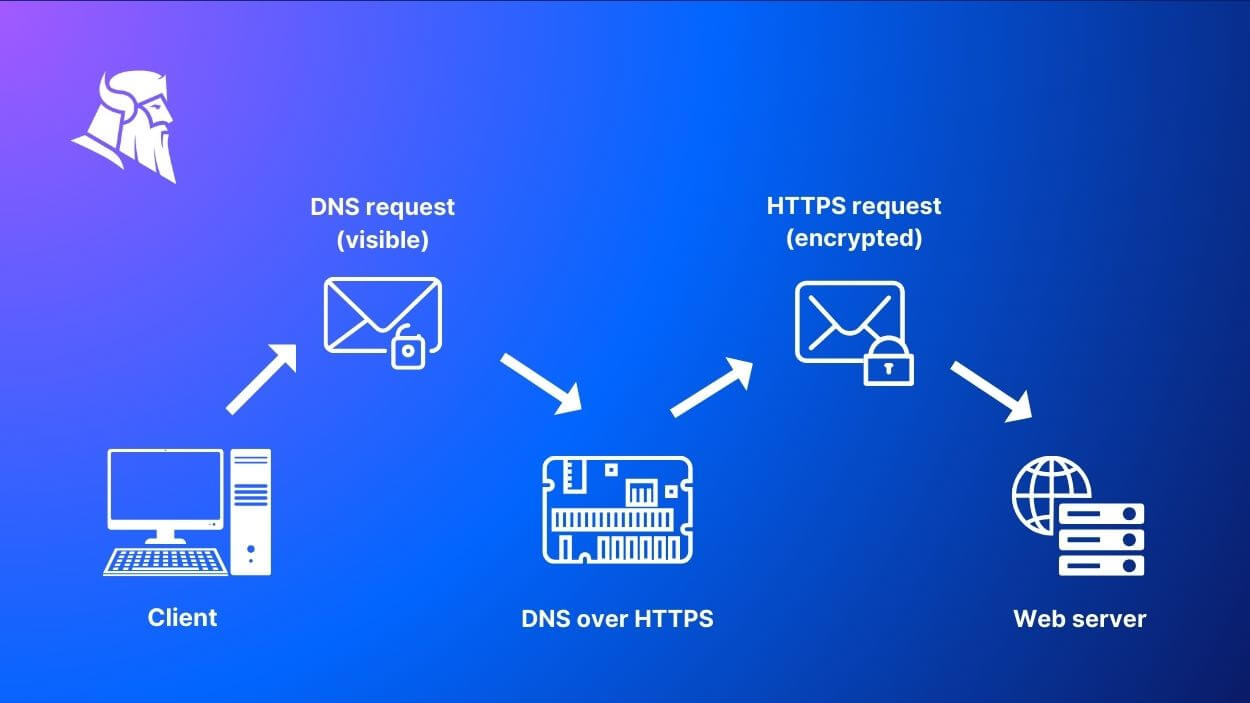
The route of a DNS query when DoH is enabled.
Standard DNS vs. DNS over HTTPS (DoH)
Networks using standard DNS communications risk man-in-the-middle attacks if they don’t use a traffic filtering solution. This is because all DNS queries are written in plain text.
The DNS over HTTPS protocol uses built-in application HTTPS standards to encrypt queries. If hackers get access to your encrypted DNS queries, they won’t be able to read them. Your communications will still be private. DNS over HTTPS makes Man-in-the-middle attacks more or less useless.
Otherwise, the threat actor can see what domains you are trying to access. Additionally, activating the DoH hides the data within the enormous amount of HTTPS requests that pass through the network.
The difference between DNS over HTTPS (DoH) and DNS over HTTP is that the second one doesn’t use encryption.
DNS over HTTPS (DoH) vs DNS over TLS (DoT)
Some think DNS over TLS (or DoT) is more or less the same thing with DoH, but this is false. Yes, both types of protocols, DoH and DoT encrypt your DNS communications. However, each type of DNS protocol uses a different ports:
- it’s port 853 for DNS over TLS
- and port 443 for DNS over HTTPS
Further on, the DoH encryption allows, theoretically, network admins to view the encrypted DNS traffic in case an issue arises. Unlike it, DoT encryption can protect data even from admins.
The fans of DoT protocols state that this DNS over TLS standard is a better fit for human rights concerns in problematic countries.
At the same time, in countries where freedom of speech may be limited, the only effect of enabling DoT encryption may be that it draws attention. Simply put, authoritarian regimes may frown upon those who adopt DoT instead of the mainstream DoH.
How Are Browsers Implementing DNS over HTTPS (DoH)
During the past years, both Google Chrome and Mozilla included DNS over HTTPS by default in their browsers.
Chrome
After the Chrome team experimented with the new DoH protocol only for a limited number of users, in May 2020, it introduced a secure DNS feature that implemented DNS over HTTPS. However, Chrome does not automatically switch DNS server to DoH. So, you need to enable DNS over HTTPS in Chrome yourself, either on your machine, or through Group Policy. To enable it on your endpoint, follow the steps:
- Open Chrome and click the three-dotted button on the top-right corner to open the Menu.
- Select ”Settings”.
- Click on ”Privacy and Security”.
- Click the ”Security” option.
- Scroll down and enable the ”Always use secure connections” and ”Use secure DNS” options.
Mozilla
Mozilla has been working on DNS over HTTPS implementation for a longer time than Chrome. Since they have released version 63 of Firefox, Mozilla can enable DNS-over-HTTPS (DoH) by default for its users.
In 2019, Mozilla succeeded rolling out DoH by default to all Firefox desktop users in the US. Canada followed in 2021. Starting March 2022, Firefox desktop users in Russia and Ukraine got default DoH to. Other countries followed
Firefox allows both users and organizations – through enterprise policies and a special-purpose domain lookup – to disable DoH. This is a useful measure in case it interferes with other preferred policy.
To enable or disable Mozilla DoH, follow the steps:
- Select
- In the panel, scroll to Network Settings and click ”
- In the dialog box that opens, go down to Enable DNS over HTTPS.
- On: select the Enable DNS over HTTPS checkbox. Select a provider or set up a custom provider (see below).
- Off: deselect the Enable DNS over HTTPS checkbox.
In the end, simply click ” to save your changes and close the box.
Can You Enable DNS over HTTPS in Windows 10?
The short answer is no. You can’t enable DoH in Windows 10.
A DNS over HTTPS feature was indeed tested in an Insider Preview Windows build. It was way Microsoft announced releasing Windows 11. For some reason, developers decided not to backport the DoH feature to the updated version of Windows 10. Instead, they made it available in Windows 11.
It’s true, for a while you could enable DoH on Windows 10 Insider Preview Build 20185. However, general users never got the DoH feature on Windows 10. At the moment, DNS over HTTPS is only available for Windows 11.
How to Enable DNS over HTTPS in Windows 11
- Press Start on Windows 11
- Enter Settings and go to Network & internet.
- Click Ethernet or Wi-Fi. If you’re using Wi-Fi click connection properties setting
- Go to DNS server assignment and click Edit
- Choose Manual from the drop-down menu.
Turn on IPv4
- In the Preferred DNS and Alternate DNS sections set the primary and secondary DoH IP address from either:
- Cloudflare:
1.1.1.1
1.0.0.1
- Google:
8.8.8.8
8.8.4.4
- Quad9:
9.9.9.9
149.112.112.112
- Go to the DNS over HTTPS drop-down menu and:
- Select On (automatic template)
or
- Choose other encryption preferences:
- Off: Transmits all DNS traffic without encryption.
- On (automatic template): Sends all DNS traffic with encryption (recommended).
- On (manual template): Allows you to specify a specific template. Only required if the DNS service doesn’t work automatically or has a template that works as expected.
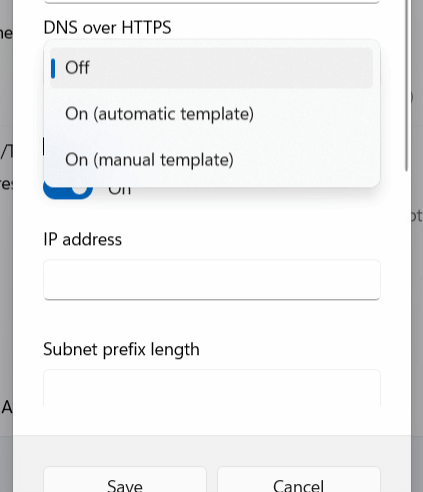
- Turn off Fallback to plaintext. This feature enables the system to encrypt DNS traffic, but queries will still be sent without encryption.
Turn on IPv6
- Under Preferred DNS and Alternate DNS sections set the primary and secondary DoH IP address from either:
- Cloudflare:
2606:4700:4700::1111
2606:4700:4700::1001
- Google:
2001:4860:4860::8888
2001:4860:4860::8844
- Quad9:
2620:fe::fe
2620:fe::fe:9
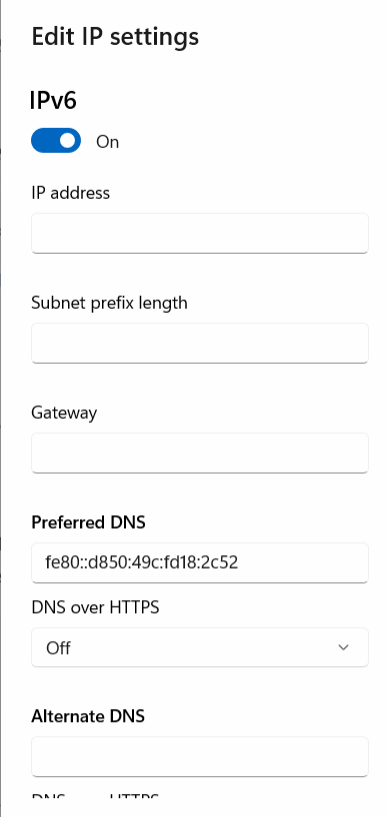
- Go to the Preferred DNS encryption drop-down menu
- Press the On (automatic template) option.
- Turn off Fallback to plaintext
- Hit Save.
DNS over HTTPS Benefits
Encrypting the DNS traffic communications brought about more privacy and better security for users and organizations. The main benefits are:
- DoH encrypts the DNS Name resolution traffic to hide the users’ online activities. Their DNS queries will remain private not only to the ISP, but to anyone else.
- Encrypting DNS over HTTPS prevents Man-in-the-Middle attacks
- DoH also prevents DNS spoofing, as the communication between the DNS servers and the web browsers can no longer be read or tampered with.
DNS over HTTPS Risks
DNS over HTTPS can have unwanted impact on network security in a business environment. If you don’t know how to handle DoH, it might bypass your security tools.
Here are some of the risks:
- Ineffective DNS Firewalls – since all queries are encrypted, users would be able to access social media or malicious links from phishing emails
- DNS traffic monitoring is not possible anymore
- No DNS blocking and filtering to handle take-down notices
- Exposure to cyber threats that exploit the lack of visibility to communicate with C2s.
Why Is DoH a Challenge for DNS Traffic Filtering Solutions
DNS traffic filtering tools are an important part of the cybersecurity strategy. While DNS over HTTPS increases privacy, it doesn’t replace compliance or security measures.
Because it encrypts DNS queries, using DoH can block the filtering tools’ activity. Before you enable DNS over HTTPS across your infrastructure, make sure you check it is compatible with the cybersecurity tools you use.
When you choose a DNS traffic filter solution, make sure that they support DNS over HTTPS correctly. Our Heimdal™ DNS Security solution, for example, comes with a solid integration of DoH.
With Heimdal DNS Security Endpoint’s support for DoH, it is easy to implement and run the privacy and security enhanced DNS over HTTPS protocol, while still maintaining the high level of security offered by the Darklayer Guard DNS filter.
The endpoint based Heimdal Agent will intercept all normal DNS enquires on the endpoint, scan them for malicious traffic requests and encrypt them locally before passing legitimate requests on the internet based DoH server chosen by the customer.
Mikkel Pedersen, Head of Global Sales Enablement and Cyber Sec Speaker @Heimdal
Can Threat Actors Abuse DoH?
Just like with any other tool, you can use DoH for a good or for a malicious purpose.
Back in 2019, Godlua, a Linux DDoS bot, was the first malware strain detected using DoH to hide its DNS traffic. The malware was written for Linux servers and used DoH to hide DNS traffic.
More recently, a Chinese threat group was discovered infecting Linux devices with malware named ”ChamelDoH”. The malware enables DNS over HTTPS communications with attackers’ servers.
Heimdal® DNS Security Solution
How We Cover DoH within Heimdal® DNS Security
DoH makes sure that any communication between the browser and the DNS server is encrypted. This way it keeps your IT environment safe from DNS spoofing and man-in-the-middle (MitM) attacks.
Heimdal is the world’s first vendor to integrate true DNS over HTTPS in a product – DNS Security Endpoint. Thus, we offer more than the standard rerouting of DNS packages.
Our functionality encrypts DNS traffic by circulating all queries through an HTTPS-encrypted session. As a result, no threat actor will be able to compromise the resolution request results and direct the end user’s browser toward a malicious website.
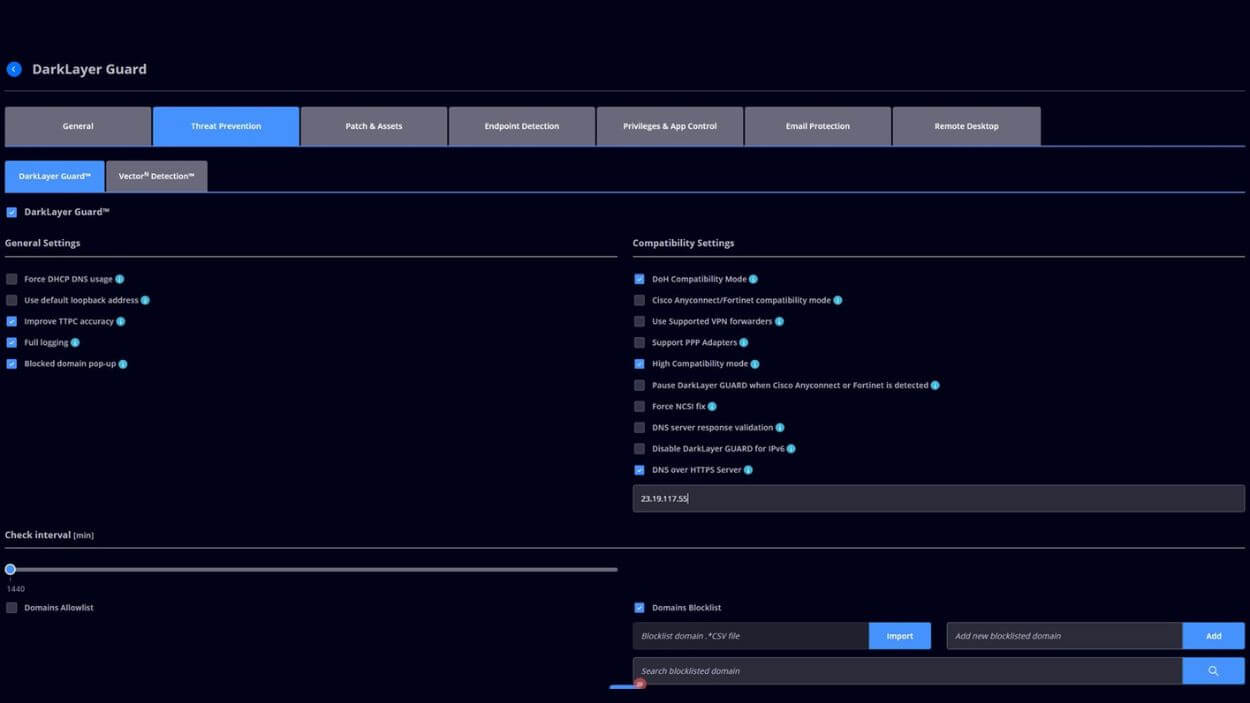
How to enable DoH in Heimdal Dashboard
As a user of DNS Security Endpoint, all you need to do is go to Endpoint Settings -> Threat Prevention Endpoint -> Compatibility Settings area of the Heimdal™ dashboard. Then tick the check box called “DNS over HTTPS Server”.
Once you enabled it, all DNS queries will be resolved via the DoH server that is set through the Group Policy settings, except the server itself.
Wrapping Up
Like any IT innovation, DNS over HTTPS did pose a few challenges at first, until everyone got aligned with it. Some might say it still is a challenge. However, once DoH became the standard, its benefits greatly outweighed the difficulties it once posed.
Integrating DoH with endpoint security makes maintaining effective DNS filtering possible despite the encryption of DNS traffic.
DNS over HTTPS FAQs
Is it good to use DNS over HTTPS?
Yes, because using DoH increases privacy. It prevents ISPs, governments and hackers from following your DNS requests and tampering with them.
Should I enable DNS over HTTPS Windows 11?
Enabling the Windows 11 DoH feature offers more privacy for your online activities, including browsing. Before you enable it, check if it is compatible with your cybersecurity solution. DoH can sabotage your DNS filtering tool if you don’t configure it properly.
How can I implement DoH in my network?
Configure your DNS clients – browsers or operating systems – to use a DoH-compatible DNS resolver. Largely used browsers like Mozilla and Chrome support DoH and you can enable the feature from their settings. If you want DNS over HTTPS to cover more than browser activity, set your operating system to use a DoH-enabled DNS server.
Can network administrators block DoH?
Yes, network administrators can block DoH traffic. They can either block known DoH servers or use deep packet inspection techniques.
How does DoH enhance privacy?
DNS over HTTPS enhances privacy by encrypting the DNS query and response. If third parties get access to your DNS requests, it will be impossible or extremely hard for them to read or spoof DNS traffic.
This means ISPs, hackers and oppressive governments won’t be able or will have a hard time seeing what websites you tried to access.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and Youtube, for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security