Contents:
DNS stands for Domain Name System, a technical process that translates domain names into IP addresses. The domain name or hostname is a word or phrase that you can easily remember. It is related to an IP address, which is a series of numbers that identifies a device on the internet or a local network.
To reach a website, you will use the domain name, while the machine will use the IP address to find the website for you. The Domain Name System simply translates the domain names into a numerical IP address that the servers involved in the lookup process understand.
This way you won`t have to memorize the numerical sequences that make up IP addresses: 66.94.29.13 (IPv4) or 2001:0000:3238:DFE1:0063:0000:0000:FEFB (IPv6). For this reason, people currently know the DNS as the phonebook of the Internet.
How Does DNS Work?
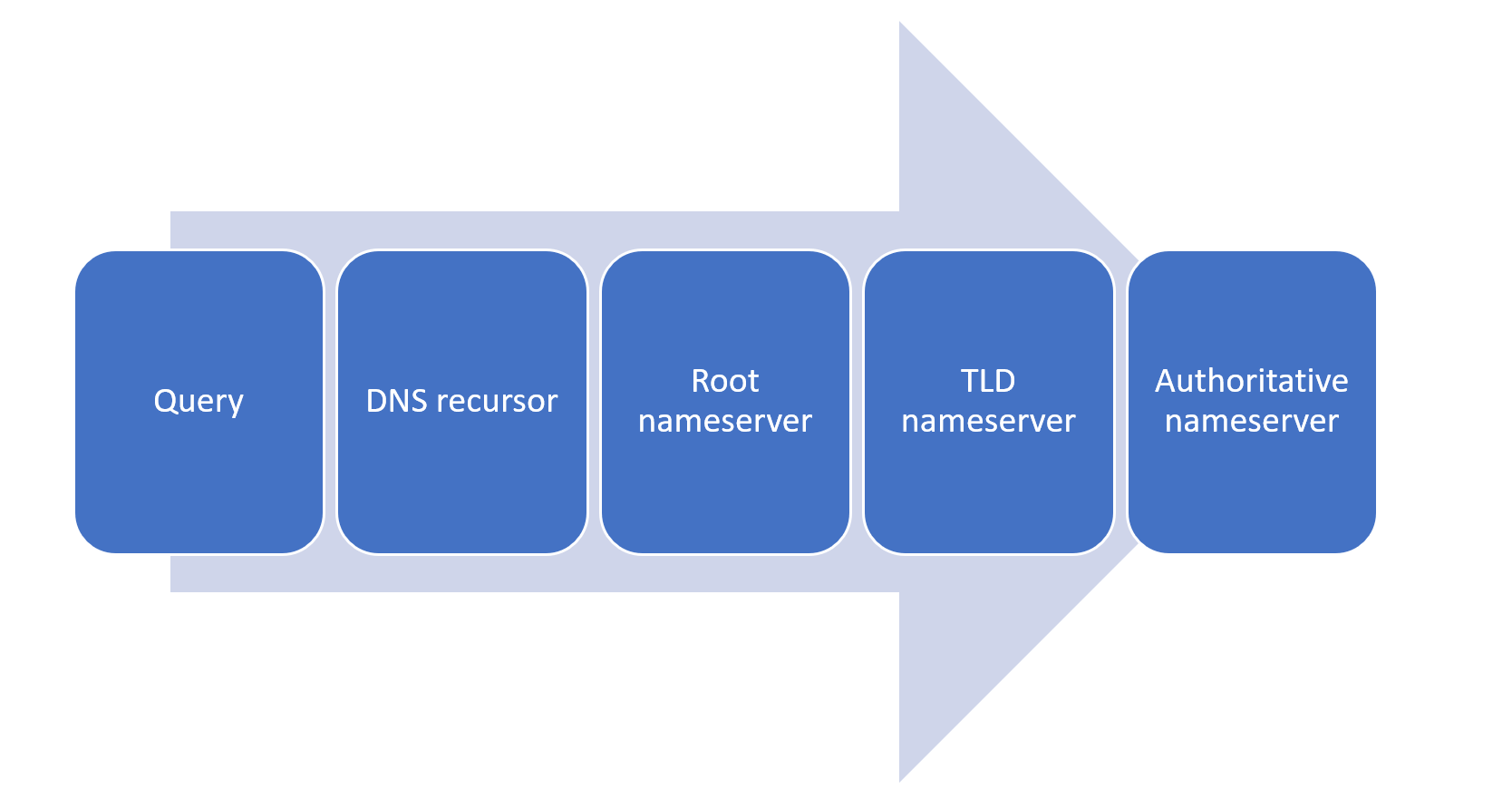
The DNS is hierarchical and decentralized, which means that it is made of multiple layers and managed by more than one organization. The DNS functions through a process called DNS resolution, which is the act of converting domain names into IP addresses. This involves four types of DNS servers:
- DNS recursor or recursive resolver
- Root nameserver
- TLD nameserver
- Authoritative nameserver
The four DNS servers listed above communicate with each other during every stage along the way. Their goal is to send the Internet user to the webpage they query. Each type of DNS server has a certain role.
Types of DNS Servers
DNS Recursor
The DNS recursor is the first server engaged in the DNS lookup process. It is also known as the recursive resolver, and it reacts when you type an address in your browser’s search bar. Its purpose is to receive queries from client machines and connect them further with the desired DNS record. For this reason, this particular DNS server is also known as the librarian of the Internet. The recursive resolver is the guy who searches for the particular book that you asked for.
To get the job done, the recursive DNS server usually makes multiple requests at a time. Users don`t get to see this process, which happens very fast and in the background. You`ll only see the result.
The process doesn`t take long, despite the multitude of possible destinations one could reach on the World Wide Web. This is due to data caching. This nifty feature helps the recursor reach the client’s queried destination a lot faster than it would on its own.
Root Nameserver
The DNS lookup process continues at the root nameserver, which is the first to translate human-readable domain names into numerical IP addresses that machines recognize. It doesn’t reference a specific location in the hierarchy, but rather a cluster of them where the desired query destination is to be found.
Keeping in tune with the same librarian and library analogy from the previous section, the root nameserver would be the index pointing to a series of book racks. The customer’s requested book is located on one of them, but the index doesn’t get any more specific than that.
TLD Nameserver
The next step in identifying the IP address associated with a particular domain name is the TLD nameserver. TLD stands for top-level domain, and common examples include .com, .org, .net, .edu, or .gov. In the library that is the Internet, it can be associated with the particular bookrack where the volume requested by the customer lies.
Authoritative Nameserver
Finally, the authoritative DNS nameserver is the last server engaged in the DNS lookup process. This is where you can find the DNS records and where the translation between the domain name and the IP address occurs. Acting as a dictionary of the online world, it then returns the IP address of the desired webpage to the DNS recursor server that made the request.
The DNS Resolution in 10 Steps
Now that we’ve established where each server stands in the DNS resolution process, let’s take a look at a practical example. Here is what goes on behind the scenes when you are requesting your browser to go on a particular website.
1. A user types www.domain.com into their browser.
2. The DNS recursor receives the query.
3. The DNS recursor further queries the root nameserver.
4. The root server sends the address of a top-level domain (.com here) back to the recursor.
5. The DNS recursor queries the .com TLD nameserver.
6. The TLD nameserver responds with the IP address of the authoritative nameserver.
7. The DNS recursor then queries the domain’s authoritative nameserver.
8. The authoritative nameserver returns the IP address of the desired domain.
9. The DNS recursor feeds the IP address into the browser.
10. The user accesses the webpage they queried for.
While it is true that a lot of server work goes on in the background of a DNS lookup, the process is almost instantaneous on the user side. Due to the hierarchical and decentralized nature of the DNS, as well as the wonders of data cache, this process only takes a couple of seconds.
Is DNS Secure?
The Domain Name System was not built with security in mind. Hackers discovered various ways to exploit the DNS for their malicious activities.
Common tactics include corrupting DNS cache, misusing open DNS servers for amplification attacks, tunneling through DNS queries, taking over subdomains, or overwhelming DNS servers with fake requests. A DNS security solution can help you mitigate this type of threats.
Once the researchers discovered the many ways in which hackers could hijack or exploit the DNS structure, they released a set of standards to make accessing a website safer. However, DNS Security Extensions (DNSSEC) and other standard practices are not enough to offer total DNS security. According to the Global Cyber Alliance’s report on The Economic Value of DNS Security, over one-third of all cyberattacks are carried out over DNS.
What is more, a study by IDC published in June 2022 revealed that 88% of organizations experienced at least one DNS attack last year. Each one of these attacks had an average financial impact of $942,000. Additionally, 70% of these incidents led to application downtime.
For more information on DNS security, you can also check out the DNS Security for Dummies eBook, Heimdal’s tell-all guide to how DNS works, how to secure it and protect your organization from DNS attacks.
An eBook that gives a comprehensive role-based security approach and addresses the numerous dangers to the Domain Name Systems (DNS) as cyberattacks increase globally.DNS Security for Dummies
How Heimdal® Helps with DNS Security
Securing the DNS has been at the forefront of our priority list here at Heimdal® ever since we launched our first product in 2014.
Our core offering of Heimdal DNS Security – Endpoint is the upgraded version of the initial product, using state-of-the-art machine learning technology combined with a highly effective DNS filtering module that helps you predict tomorrow’s threats today with 96% accuracy.
Heimdal DNS Security – Endpoint expertly identifies cyberattacks that would otherwise remain undetected by traditional antivirus, all with no interruptions and minimal impact on your resources. Our code-autonomous endpoint solution helps you detect malicious URLs and processes before cybercriminals have the chance to penetrate your infrastructure.
Wrap Up
The DNS is part and parcel of the structure of the World Wide Web. It is a crucial tool in any work environment. Therefore, knowing how it works and how to properly secure should be at the top of your company’s priority list. Heimdal® can help you with that. Book a demo with us today or reach out to us at sales.inquiries@heimdalsecurity.com for more information.
FAQs
Is it necessary to use DNS?
It’s a fundamental pillar of internet functionality. Without DNS, you would have to remember long sequences of numbers (IP addresses) to reach the websites you need. If a DNS fails to match a domain name to its corresponding IP address, accessing the intended website becomes impossible.
Is DNS in my router?
Yes, your router often acts as a DNS relay for devices on your network. It forwards DNS queries to a designated DNS server, unless it has cached records. Your ISP (internet service provider) typically provides a default DNS server for your router. However, you have the option to change it to alternative, safer DNS servers, like Heimdal‘s.
What is my DNS IP address?
Open Command Prompt via the Start menu or search for “Cmd” in the Windows task bar. Then, enter ipconfig/all and hit Enter. Search for the “DNS Servers” section. The initial address is your primary DNS, followed by the secondary DNS.
What is DNS filtering?
DNS filtering is a technique that blocks or allows access to specific websites based on their domain names. It intercepts DNS queries and decides whether to return the IP address for the requested domain or block the query. Security admins use it for content filtering, to block inbound and outbound malicious communication.
Is DNS filtering safer than VPN?
DNS filtering and VPN serve different primary purposes. The first filters domain name requests to block access to specific websites or categories of websites. Filtering DNS traffic helps security teams prevent phishing and ransomware attacks, for example.
The VPN encrypts internet traffic between your device and a remote server, masking your IP address.
Who invented the DNS?
The story of the Domain Name System begins in 1966 when U.S. Internet pioneer Bob Taylor created the ARPANET. The acronym stood for Advanced Research Projects Agency Network. ARPANET was the precursor of the Internet as we know it today. Three years later, in 1969, the first computers went online. The implementation of the Network Control Program followed, in 1970.
Originally, the ARPANET stored names to address translations in a very simplistic manner. There was a single table in a document named HOSTS.TXT. American information scientist Elizabeth J. Feinler created it, back in 1974. Things worked fine at first. However, due to the rapid expansion of the online world, it was clear that it won’t be sustainable.
In 1980, more and more computers went online. So, the scientist in charge of manually documenting the numerical addresses asked Paul Mockapetris to find a solution. You might recognize his name as the man credited with the invention of the DNS.
And so, the Domain Name System was born in 1983. Security specialists published the first set of Internet standards shortly after.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and Youtube, for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security









