Contents:
A DNS server is a computer that has DNS software installed. Its role is to match domain names with IP addresses, on request.
DNS servers store databases of hostnames and their corresponding IPs. Not only do they store and translate, but they also exchange information with one another using special protocols.
In this article, I’ll explain some of their basic principles. You’ll find out how DNS servers work, how many DNS server types are out there, and the role they have in making the Internet work. Are DNS servers vulnerable to cyberattacks? Yes, they are. By the end of this article, you’ll know what types of attacks they are vulnerable to and what you can do to improve their safety.
Key takeaways:
- it takes 4 DNS server types to locate a website for the first time when you make a DNS request
- The process of finding the correct IP address of a domain name is called a DNS resolution
- the DNS server responsible for questioning other servers is called a Resolver
- DNS servers are vulnerable to more than 5 different DNS attack types
- You can use Heimdal’s DNS Endpoint Security or DNS Network Security to keep your assets safe from DNS attacks
What is the purpose of a DNS server?
The DNS server acts as an intermediary between humans and computers.
All machines connected to the internet, from our computers and smartphones to the servers that deliver content for large websites, use numbers to locate and communicate with one another.
These numbers are referred to as IP addresses. The DNS server helps translate these numerical addresses into the human-readable domain names.
Here’s an example. If you want to access heimdalsecurity.com, you will normally just type this domain name into the address bar. Now, what if instead of the domain name you will have to type 52.157.161.254 (the actual IP address of the website).
Not so easy to remember, right? Without a DNS server to do the translation for us, we would have to memorize all the IPs of the websites we want to reach.
How does a DNS server work?
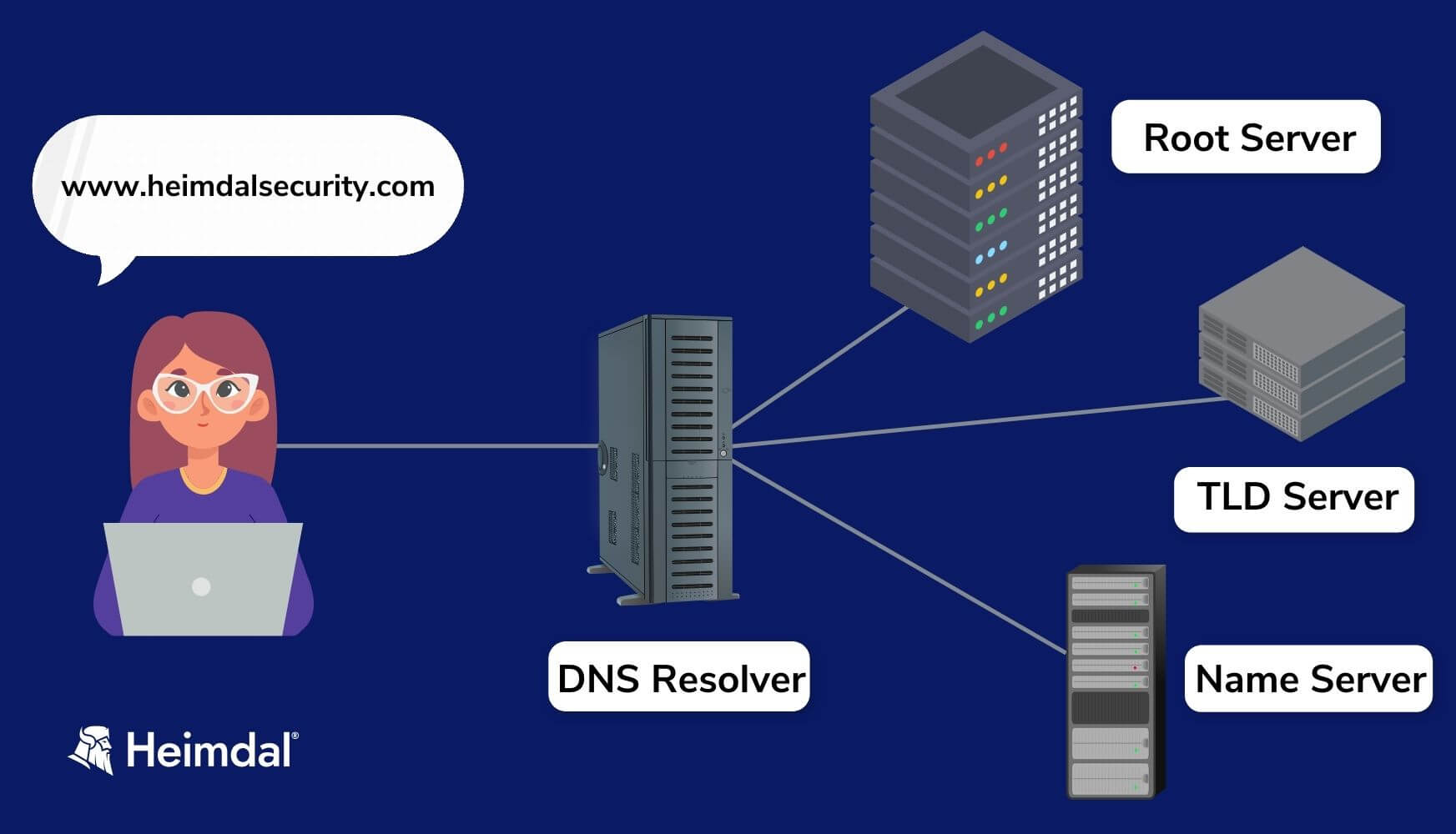
The DNS query goes to 4 different DNS servers
When you type a website’s address into your browser for the first time, a DNS server starts looking for the site you want to visit. This triggers an activity called a DNS lookup which matches the domain name with its IP address.
In case the information doesn’t already exist in your DNS cache, the DNS query will travel on to a series of DNS servers.
What happens when you send a DNS query?
In this searching and matching process, the computer you sent the DNS request from is called a client. The process of translating and looking up names is known as a DNS resolution.
In a complete DNS resolution, each server translates a different part of the domain name you entered. Your DNS query will go from the browser through four different DNS server types.
Types of DNS servers
Here are the 4 DNS resolution actors I told you about when describing the process:
The DNS Resolver
The DNS resolver is the first to get the request to locate a domain name from you, the DNS client. It’s also called a DNS recursor.
As it doesn’t know the answer, this server is the one who does the questioning for you. It passes the DNS query, further on to other servers. The first in line will be the root server.
The Root Server
The root server makes the first step towards translating the domain name into an IP address. It sends the DNS resolver the address for the top-level domain (TLD) DNS server that stores the information for its domains.
A top-level domain is the .com or .net section of the domain name that you typed into the address box. At this point, you need to know there are 13 primary DNS root servers in the world maintaining a directory of all domains and their corresponding public IPs.
These top DNS servers are identified by the first 13 letters of the alphabet (A through M). The United States is home to ten of these servers, while London, Stockholm, and Japan each host one.
The root servers are managed by companies, universities, and government agencies. They are appointed by ICANN, which stands for Internet Corporation for Assigned Names and Numbers. You can check out the full list of root servers all over the world here.
The TLD Server
After it gets the response from the root server, the resolver queries the TLD server. This one knows where the domain’s authoritative name server is located. So, it returns its IP address to the DNS resolver.
The Authoritative Name Server
Querying the Authoritative Name Server is the last step in the resolver’s quest. The Authoritative DNS Server will send it the precise IP address of the website you asked for.
Although it sounds like a lot of work, this whole process happens within a few seconds, without you even perceiving it.
The second time you visit a website, the DNS resolution can even happen within milliseconds. Why? Because unless you clear your browser’s cache, it will retrieve the information he already stored in. The browser is not the only one to cache information. The DNS resolver does that too, in order to move faster and provide better services for the client.
DNS Cache Locations
Servers can store the IP addresses obtained from DNS queries in a cache for a certain amount of time. DNS caching is good for efficiency because it lets servers respond quickly the next time someone asks for the same IP address.
There are several places where DNS data can be cached. Here are the common ones:
- Browser
Browsers such as Apple Safari, Google Chrome, and Mozilla Firefox store DNS data for a set time. When a DNS request is made, the browser first checks the cache. It only passes the request on, to a local DNS resolver server, if it doesn’t find the information in the cache.
- Operating system (OS)
Many operating systems have built-in DNS resolvers called stub resolvers that cache DNS data and handle queries before sending them to an external server. Most of the time, the OS is queried after the browser, or another application is queried.
- Recursive resolver
The recursive DNS resolver can also cache the result of a DNS query. Some of the DNS records that can give a response may be available to resolvers. This will allow them to skip some steps in the DNS resolution process.
The problem with the DNS cache is that hackers can exploit it to send the user to a malicious website. This kind of DNS attack where an attacker inserts fake information into the DNS cache is called DNS cache poisoning.
Primary and Secondary DNS servers
When you subscribe to your internet service provider (ISP), they typically set up your router or computer with a primary and secondary DNS server. Using multiple DNS servers ensures service continuity.
If the primary DNS server breaks down, the system will use the secondary server to resolve your DNS queries
Default vs Alternative DNS Servers
If you experience DNS server errors or want more privacy for your browsing activity, you might want to consider changing the default DNS servers provided by your internet service provider (ISP). So, you’ll start using other DNS servers from a more reliable and trustworthy company.
You can also use alternative DNS servers that are free and open to the public, provided by Google, Quad9, or OpenDNS, to name a few. Check out the complete list of the most trustworthy public DNS servers as well as a guide on how to configure or change your primary and secondary servers here.
Google is the biggest public DNS server in the world right now and it has been around since 2009.
To use this DNS server, you will need to change your IP addresses to 8.8.8.8 and 8.8.4.4.
Google hosts its public DNS servers in data centers worldwide, ensuring that when you access a website using one of the two mentioned IP addresses, the system automatically directs you to the nearest server for faster response times.
This brings us to another two categories of DNS servers:
- Public DNS Servers, which are accessible to anyone connected to the internet. Typically, the ISPs are the ones to set them up. These servers help manage authoritative name servers by providing traffic steering and load balancing. They improve network performance.
- Private DNS Servers can only be accessed by authorized people in an organization. Private DNS servers are protected by firewalls and help locate internal websites. They are usually part of the virtual private network (VPN) of a company and only work with internal IP addresses.
Are DNS servers vulnerable to attacks?
According to a study by IDC for 2023, 90 % of organizations experienced at least one DNS attack last year. Each one of these attacks had an average financial impact of $1.1million. Additionally, 73% of these incidents led to application downtime.
The DNS was not made with security in mind, but afterwords, researchers published security standards to ensure website safety. While DNS Security Extensions and other best practices are helpful, they have their limitations.
DNS servers are still vulnerable to various attacks including spoofing, amplification, DoS (Denial of Service), and private information extortion.
If you want to keep using the Internet, you can’t avoid using the DNS. So, you’d better prepare to know the threats it faces and how to mitigate them.
The most common DNS attacks
Cybercriminals use DNS attacks in various ways. The main categories of DNS attacks are:
- DoS attacks. This cyberattack tries to temporarily or indefinitely interrupt the services of a network-connected host. Perpetrators typically accomplish this by flooding the target, which is typically a website, with redundant DNS queries, seeking to prevent legitimate searches from passing through.
- DDoS attacks. In a DDoS attack, the source of the excess traffic has multiple points of origin. DDoS attacks are more common than DoS attacks. This happens because bots and botnets are widely available on the dark web, and volumetric attacks get a higher success rate than DoS attacks.
- DNS Hijacking. In this cyberattack, a malicious server redirects traffic away from its intended destination. Thus, hackers can trick visitors into visiting a malicious website. This technique has several other versions such as DNS poisoning, DNS rebinding, DNS typosquatting and DNS tunneling.
More on DNS security in this video:
How Can Heimdal® Help?
Since the launch of our first product in 2014, we have placed DNS security at the top of our priority list.
Our primary service, Heimdal® DNS Security – Endpoint, is an enhanced version of the original product that combines cutting-edge machine learning technology with a highly efficient DNS filtering module to let you predict threats with 96% accuracy.
Heimdal DNS Security – Endpoint skillfully detects threats that would otherwise go undetected by typical antivirus. It does so without causing interruptions and with minimum impact on your resources.

Heimdal® DNS Security Solution
- Machine learning powered scans for all incoming online traffic;
- Stops data breaches before sensitive info can be exposed to the outside;
- Advanced DNS, HTTP and HTTPS filtering for all your endpoints;
- Protection against data leakage, APTs, ransomware and exploits;
Wrapping Up
The DNS server works its magic daily, every time you type a domain name into the address bar. In the process of locating your desired website, 4 types of servers work to exchange information and deliver it to you in a matter of seconds.
While their superpower is speed, the four types of DNS servers are not immune to cyberattacks. At Heimdal we aim to enhance DNS security with innovative, efficient, and reliable solutions. Book a demo to discover our approach to DNS protection.
If you want to delve deeper into domain name system security, check out our free eBook – DNS Security of Dummies, and learn more about securing your DNS infrastructure or the one of your organization.
FAQs
What is a DNS server and why is it used?
A DNS (Domain Name System) server translates human-friendly domain names (like www.heimdalsecurity.com) into IP addresses that computers use to identify each other on the network. It’s essential for internet navigation, allowing users to access websites using easy-to-remember names instead of complex numerical IP addresses.
How do I find my DNS server?
To find your DNS server, use Command Prompt on Windows (ipconfig /all), Terminal on macOS (scutil –dns), or Linux (cat /etc/resolv.conf) to view network settings. For devices using router-assigned DNS, check the router’s admin page, typically found under DHCP or LAN settings, to see the DNS server details.
What happens if DNS is off?
If DNS is off, devices can’t translate domain names into IPs, blocking access to websites by name and disrupting internet usage. You’ll face connectivity errors despite an active network connection. Essential online services and applications requiring domain name resolutions will fail, significantly hindering your ability to navigate and use the internet.
What causes DNS problems?
DNS problems can stem from server issues, network connectivity disruptions, misconfigured DNS settings, firewall or security software blocking DNS traffic, corrupted DNS cache, outdated router firmware, and malicious DNS hijacking or spoofing attacks.
How do I clear my DNS cache?
To clear your DNS cache, use Command Prompt as Administrator on Windows (ipconfig /flushdns), Terminal on macOS (sudo dscacheutil -flushcache; sudo killall -HUP mDNSResponder for Catalina and newer), or Terminal on Linux (sudo systemd-resolve –flush-caches). This action may temporarily disrupt internet usage as the cache rebuilds. More in this article: How to Clear DNS Cache on Windows, macOS, Linux & Browsers.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and Youtube, for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security