Contents:
HTTPS security is important for both business executives and regular home users. Read on to find out what is HTTPS, how it is used, what are its benefits and limitations – and more.
What Is HTTPS?
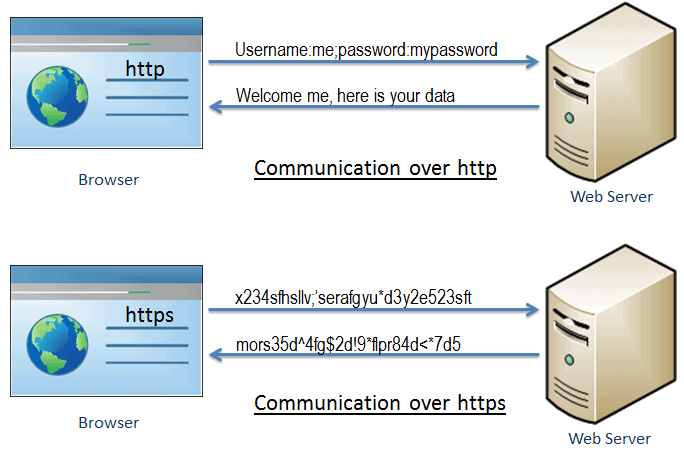
Simply put, HTTPS (HyperText Transfer Protocol Secure) is the secure version of HTTP, an application protocol that allows data communication (HTML files, images, query results, etc) between two systems, e.g. the browser and the webserver, as can be seen in the following illustration:
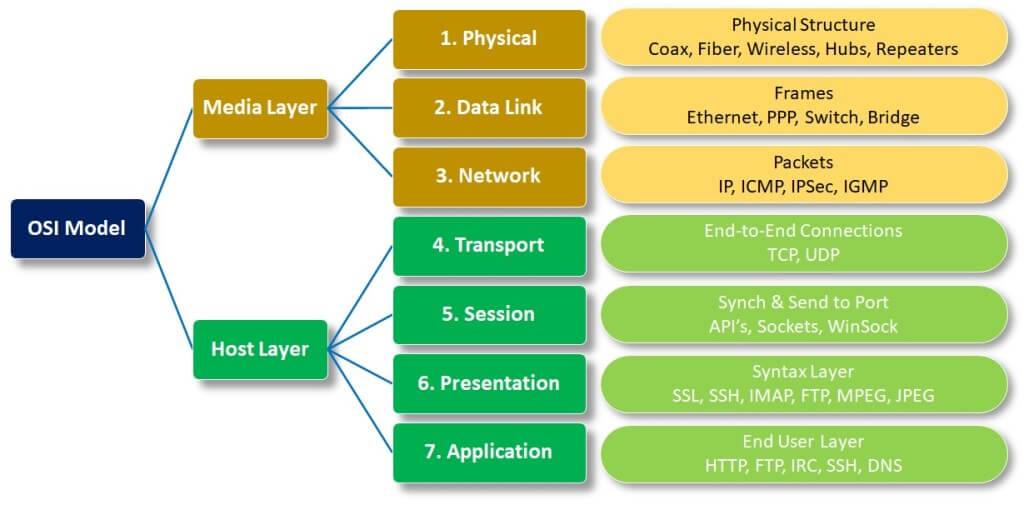
The Internet protocol suite represents
the conceptual model and set of communications protocols used in the Internet and similar computer networks. It is commonly known as TCP/IP because the current foundational protocols in the suite are the Transmission Control Protocol (TCP) and the Internet Protocol (IP). […]
The Internet protocol suite provides end-to-end data communication specifying how data should be packetized, addressed, transmitted, routed, and received. This functionality is organized into four abstraction layers, which classify all related protocols according to the scope of networking involved. From lowest to highest, the layers are the link layer, containing communication methods for data that remains within a single network segment (link); the internet layer, providing internetworking between independent networks; the transport layer, handling host-to-host communication; and the application layer, providing process-to-process data exchange for applications.
In the OSI (Open Systems Interconnection) Model, the “conceptual model that characterizes and standardizes the communication functions of a telecommunication or computing system”, HTTPS is the TCP/IP protocol of the application layer.
HTTP vs HTTPS
Before talking about how HTTPS is used, it’s important to note the difference between HTTPS and the original HTTP:
HTTP was designed as an unsecured, clear text protocol – which makes it vulnerable to various types of cyberattacks, like eavesdropping and man-in-the-middle. By adding encryption to the equation, HTTPS prevents the data that is sent over the Internet from being intercepted and read by third parties.
As CIO.GOV explains,
HTTPS verifies the identity of a website or web service for a connecting client and encrypts nearly all information sent between the website or service and the user. Protected information includes cookies, user agent details, URL paths, form submissions, and query string parameters. HTTPS is designed to prevent this information from being read or changed while in transit. HTTPS is a combination of HTTP and Transport Layer Security (TLS). TLS is a network protocol that establishes an encrypted connection to an authenticated peer over an untrusted network.
To check if a certain website is secure, the simplest way is to look at the security status icon that’s located to the left of the web address:
![]()
“Secure” means that the “Information you send or get through the site is private.” However, Google Chrome advises to “always be careful when sharing private information. Look at the address bar to make sure you’re on the site you want to visit.”
“Info or Not Secure” means that “The site isn’t using a private connection. Someone might be able to see or change the information you send or get through this site.”
“Not secure or Dangerous” means that you should proceed with caution or leave the website and completely avoid entering any private information on that page.
What Are the Benefits of the HTTPS protocol?
HTTPS brings a variety of benefits to Internet users and website owners alike. From a security stand of point:
- Integrity – Through encryption, HTTPS is excellent at protecting the integrity of communication between a website and a browser.
- Privacy – HTTPS plays an important role in keeping users safe from having their credit card numbers and passwords scooped up while shopping or banking online.
Other benefits:
- Compatibility – The recent tendencies show that HTTP might actually become incompatible with current browsers like Mozilla Firefox or Google Chrome.
- SEO boost – Search engines like Google also use HTTPS as a ranking signal when they generate search results, which is something website owners should keep in mind if they’re interested in an easy SEO boost.
Does HTTPS Have Any Limitations?
Since no solution or application can be 100% certain, HTTPS does have, of course, certain limitations:
- HTTPS does not encrypt IP addresses and destination domain names.
- the encrypted traffic can indirectly reveal important information: the time spent on a certain website, or “the size of requested resources or submitted information.”
- phishing scammers might imitate the lock icon that suggests that a website is secure or, of course, register domain names that are very similar to the domains they’re trying to impersonate – and you might not pay attention to the little “s” missing from the address bar.
HTTPS only guarantees the integrity of the connection between two systems, not the systems themselves. It is not designed to protect a web server from being hacked or compromised or to prevent the web service from exposing user information during its normal operation. Similarly, if a user’s system is compromised by an attacker, that system can be altered so that its future HTTPS connections are under the attacker’s control. The guarantees of HTTPS may also be weakened or eliminated by compromised or malicious certificate authorities.
How Can You Secure Your Website?
If you want to make sure that your websites are secure, there are certain things you need to do:
- obtain a security certificate from a reliable source that offers technical support and make sure your certificate is always up to date;
- use permanent server-side redirects from HTTP to HTTPS for ensuring that your users and search engines always go to the HTTPS webpages and make sure that the content is the same on both HTTP and HTTPS websites.
- check if your HTTPS pages can be crawled and indexed by Google – you can use an URL inspection tool. Do not use the noindex tag.
Other Security Recommendations
To make sure you and your employees browse safely on the Internet and avoid threats like phishing or man-in-the-middle, we recommend you enhance your HTTPS security by using a solution that can filter the traffic at the DNS, HTTP, and HTTPS layers.
Our Heimdal™ Threat Prevention can block attacks before they reach your network, servers, or endpoints, thanks to the unique combination of local and cloud filtering. The solution is available both for network and endpoint protection, and you can use them connected or as standalone modules.
Heimdal® Network DNS Security
Wrapping Up
HTTPS security is essential for the cybersecurity of any company and any user of the Internet – ignoring it might lead to cyberattacks with serious consequences like money loss, time loss, brand damage, and so on.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security









