Endpoint detection and response (EDR), also known as Endpoint Detection and Threat Response (EDTR), is a collection of integrated endpoint security tools that combine data collection and analysis, forensics, and threat hunting, with the end goal of finding and blocking any potential security breaches in due time.
In this article, you will find out:
- What Is Endpoint Detection and Response (EDR)
- How Does EDR Work?
- Key Functions of EDR
- Main Endpoint Threats
- Why Is EDR Important for Companies?
- Benefits of Endpoint Detection and Response
- EDR Challenges
- EDR vs Antivirus – What’s the Difference?
- Heimdal’s Approach to EDR Security
What Is Endpoint Detection and Response (EDR)?
Endpoint Detection and Response (EDR) refers to a set of integrated security solutions designed to detect and respond to potential security breaches on connected devices, known as endpoints. These endpoints include devices such as laptops, desktop PCs, mobile devices, servers, IoT devices, and cloud workloads, all of which can access an organization’s data and network.
How Does EDR Work?
EDR systems combine data gathering, analysis, forensics, and threat-hunting capabilities to quickly detect and prevent security breaches. Unlike traditional antivirus (AV) solutions, which rely on signatures to detect malware files, EDR solutions take a proactive approach by identifying suspicious patterns that may indicate a potential security threat. By doing so, EDR systems can effectively detect and respond to complex malware and cyberattacks.
EDR technologies document the activity and events across all endpoints and workloads, granting IT teams the visibility they need to detect incidents that might otherwise go unnoticed. An EDR product should offer ongoing, detailed real-time insight into endpoint activities for effective security monitoring.
Once a threat is identified, EDR systems can either alert security teams or automatically take predefined steps to control and mitigate the threat. This proactive approach guarantees immediate response to security incidents, minimizing the risk of significant damage or data breaches.
Key Functions of EDR
The components and features of an endpoint detection and response system can vary greatly from vendor to vendor. Broadly, an EDR solution should have the following capabilities:
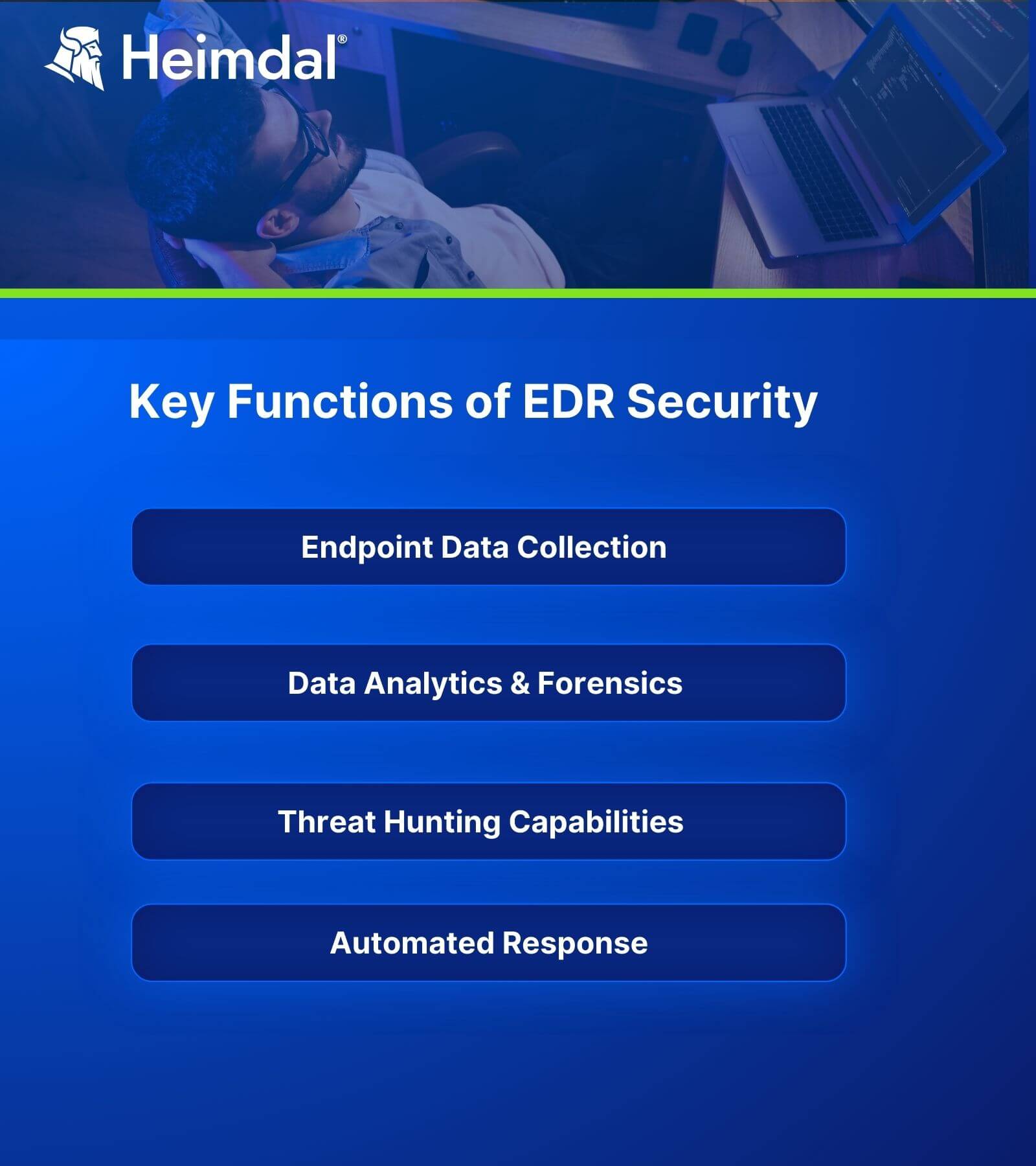
Endpoint Data Collection
The software gathers a wide range of data from endpoints by using a software agent installed on each machine.
The security system then sends the gathered data to a centralized location. The EDR vendor often provides a cloud-based platform for this purpose.
Data Analysis and Forensics
Now that the data is collected, algorithms and machine learning technology are starting to sift through it. This highlights potential irregularities.
It can be considered that many such solutions can “learn” what normal user behavior and endpoint operations are. They then make decisions based on this analysis.
This security solution can also correlate gathered data across multiple sources as threat intelligence feeds. These provide real-world examples of ongoing cyberattacks to compare them to the activity within an organization.
Threat Hunting Capabilities
If the EDR platform views any events or actions as suspicious, it generates an alert that the security teams can easily review.
Threat hunting is a proactive approach regarding endpoint threat detection. Endpoint Detection and Response software will not wait for an incident to happen. This is contracting with other reactive methods, focused on post-factum – after an attack – actions.
Automated Response to Block Malicious Activity
By using the automation capabilities that exist in your EDR security solution, the companies can have a faster response to a threat.
This type of solution can temporarily isolate an infected endpoint from the rest of the network to prevent malware from spreading. Consequently, this blocks lateral movement, one of the threat actors’ favorite techniques.
Main Endpoint Threats
Ransomware
Ransomware is a type of malware that encrypts all of the data on a computer or mobile device, making it impossible for the owner to access it. Following the infection, the victim receives a message alerting him or her that they must pay a certain amount of money (usually in cryptocurrency) to gain the decryption key.
The ransom is usually paid within a certain amount of time. If the victim pays the ransom, there is no guarantee that the decryption key will be delivered.
Usually, ransomware attacks have similar stages: infection, security key exchange, encryption, extorsion, unlocking, or recovery.
Phishing
Phishing is a deceptive tactic used to steal personal data, such as credit card details, usernames, and passwords from users. To deceive the victims into exposing their data, the attackers pose as a trustworthy entity (typically by imitating the appearance and feel of a well-known brand).
The most common types of phishing are email phishing, spear phishing, whaling, CEO fraud, vishing, and quishing.
Malvertising
Malvertising, also known as malicious advertising, involves using online advertisements to distribute malware. Cybercriminals inject fraudulent or malware-laden ads into legitimate ad networks and web pages, targeting users who may not have encountered the ads due to security solutions. Malvertising can lead to the download of malware directly onto users’ devices or redirect them to websites that spread viruses, ransomware, and other dangerous applications.
Drive-by Downloads
Drive-by downloads occur when cybercriminals compromise websites and insert malicious elements, such as malvertisements or malicious redirects. These elements exploit vulnerabilities in users’ devices to download and execute malware without their knowledge or consent. Drive-by downloads can lead to the installation of various types of malware and the theft of sensitive data.
Unpatched Vulnerabilities
Unpatched vulnerabilities are a significant risk for organizations. Threat actors often exploit these vulnerabilities to gain unauthorized access to systems and networks. Organizations that fail to apply security patches on time leave themselves vulnerable to attacks that exploit known vulnerabilities.
Insider Threat
Insider threats refer to security risks posed by individuals within an organization, such as employees, former employees, business associates, or contractors. These individuals have inside knowledge of the organization’s data, computer systems, and security processes, making them potential sources of fraud, theft, or sabotage. Insider threats can result in espionage, unauthorized information disclosure, IT sabotage, and the loss or degradation of an organization’s resources.
Endpoint Detection and Response Components
EDR security solutions serve as a key center for collecting, correlating, and analyzing endpoint data, as well as coordinating notifications and countermeasures to threats.
An EDR system’s components and functionalities can differ significantly from one vendor to the next. However, every EDR system should, in general, have the following characteristics:
Endpoint Data Collection
Context is critical for correctly distinguishing actual threats from false positives. To make informed judgments about potential threats, EDR security systems employ as much data as possible.
A software agent placed on each device can collect a wide range of data from endpoints, which is subsequently transferred to a centralized location – frequently, an EDR vendor’s cloud-based platform.
Data Analysis and Forensics
EDR software employs algorithms and machine learning technology to filter through the gathered data to identify any potential anomalies. Many EDR solutions can be said to “learn” what regular user behavior and endpoint activities are and make judgments based on this information.
As threat intelligence inputs, the obtained data can be correlated across numerous sources. These are used to depict real-life examples of currently underway cyberattacks that may be contrasted to internal corporate activity.
Threat Hunting
Threat hunting involves actively monitoring network activity and traffic to identify any anomalies that may indicate a potential data breach. EDR solutions continuously monitor events and actions on endpoints, flagging suspicious events for security experts to review and investigate.
Automated Response
An EDR solution’s pre-configured rules can detect when incoming data signals a particular type of security breach and initiate an automatic response, such as logging off the end-user or sending an alert to a staff person.
Companies can have a faster response to a threat by utilizing the automation features found in many EDR security systems since this type of solution can temporarily isolate a compromised device from the rest of the network to prevent malware from spreading.
Why Is EDR Important?
Compared to traditional security solutions, EDR provides enhanced visibility into your endpoints and allows for faster response time.
Furthermore, Endpoint Detection and Response tools detect and protect your organization from advanced forms of malware (such as polymorphic malware), APTs, phishing, etc.
It’s also worth mentioning that some EDR security solutions are based on AI and machine learning algorithms designed to spot yet unknown types of malware. They will subsequently make behavior-based categorization decisions.
Benefits of EDR
Here are some major advantages of Endpoint Detection and Response solutions:
Increased Network Visibility
These solutions provide continuous monitoring for real-time threat detection and response, detecting malicious traffic and investigating attack sources. It delivers detailed insights into endpoints, including running processes, applications, files, and registry settings, aiding in fast threat identification and remediation.
Improved Compliance
EDR helps organizations adhere to data storage and access regulations like HIPAA or GDPR by keeping track of suspicious activity and investigating potential threats. This ensures that companies remain compliant with industry standards.
It detects unauthorized access and monitors user behavior anomalies, enabling companies to address and resolve any compliance-related concerns proactively. Additionally, EDR offers detailed reporting, useful for demonstrating compliance to auditors.
Reduced Risk
Endpoint Detection and Response services reduce a company’s risk by constantly monitoring the network and endpoints, enabling prompt detection and response to threats in real-time. EDR’s detailed endpoint information helps identify and fix vulnerabilities quickly before they are exploited. It also tracks user behavior, identifying suspicious activities that could indicate insider threats.
Additionally, EDR’s comprehensive reports on threats and activities aid companies to better assess their overall risk posture and take proactive measures to minimize risks.
Cost Efficiency
Such systems help companies save money by providing real-time monitoring and quick response to security threats, which cuts down on the costs related to managing security incidents. By swiftly identifying and fixing vulnerabilities, EDR also reduces the likelihood of expensive breaches and fines, leading to long-term financial advantages.
Stronger Security Posture
By adopting an EDR approach, you can enhance your defense against cyber threats by reducing false positives while still identifying real threats swiftly. This allows you to take action accordingly to safeguard your company from additional damage caused by threat actors trying to obtain unauthorized access to sensitive data.
Endpoint Detection and Response (EDR) Challenges
Because cybersecurity is a game of cat-and-mouse, EDR solutions also encounter some challenges that have to be addressed. Let us have a closer look:
The Need for Comprehensive Coverage
EDR users must assess whether the program is working or disabled on affected devices such as non-compliant hosts. Furthermore, it may be difficult – or costly – to maintain data for all endpoints for the minimum 6+ months required for threat hunting.
IoT and Mobile Threats
The risk imposed by IoT, mobile devices, and BYOD policy, especially in the context of Work From Home or Work From Anywhere, is a challenge for endpoint security in general.
The rise of IoT devices has increased cybersecurity vulnerabilities for businesses at an alarming rate. These devices are the primary contributors to the growing problem of shadow IT since they boost the number of weak spots in enterprises’ security systems and collect extremely sensitive data in large quantities.
When it comes to BYOD, the fact that many employees use their mobile devices daily means that they are more likely to be infected with malware. A malicious actor would have a clear path to get unauthorized access to sensitive data and resources if an infected device connects to a resource on an organization’s network. They can then wreak havoc with more complex attacks, like ransomware.
Third-Party Software
Organizations have minimal control over applications on an employee’s device by default. Third-party programs, however, are a major threat vector. A vast number of mobile flashlight programs, for example, have been discovered to include malware, and free software downloaded on an employee’s laptop can encompass a plethora of harmful applications.
Even if a company has control over what applications employees install on personal devices, the programs may pose hazards that the organization is unable to prevent. For example, if a company does not control a device, and a new vulnerability in an application necessitates a security patch update, the organization will simply not know if it was installed or not.
General Visibility
Lack of visibility into the entire network and all endpoints is a significant challenge for organizations. With the increasing adoption of remote work and the use of personal devices, organizations need complete visibility and control over all endpoints. Without this visibility, organizations face increased cyber risk and potential breaches.
EDR vs. Antivirus – What’s the Difference?
Here are the key differences between EDR and Antivirus:
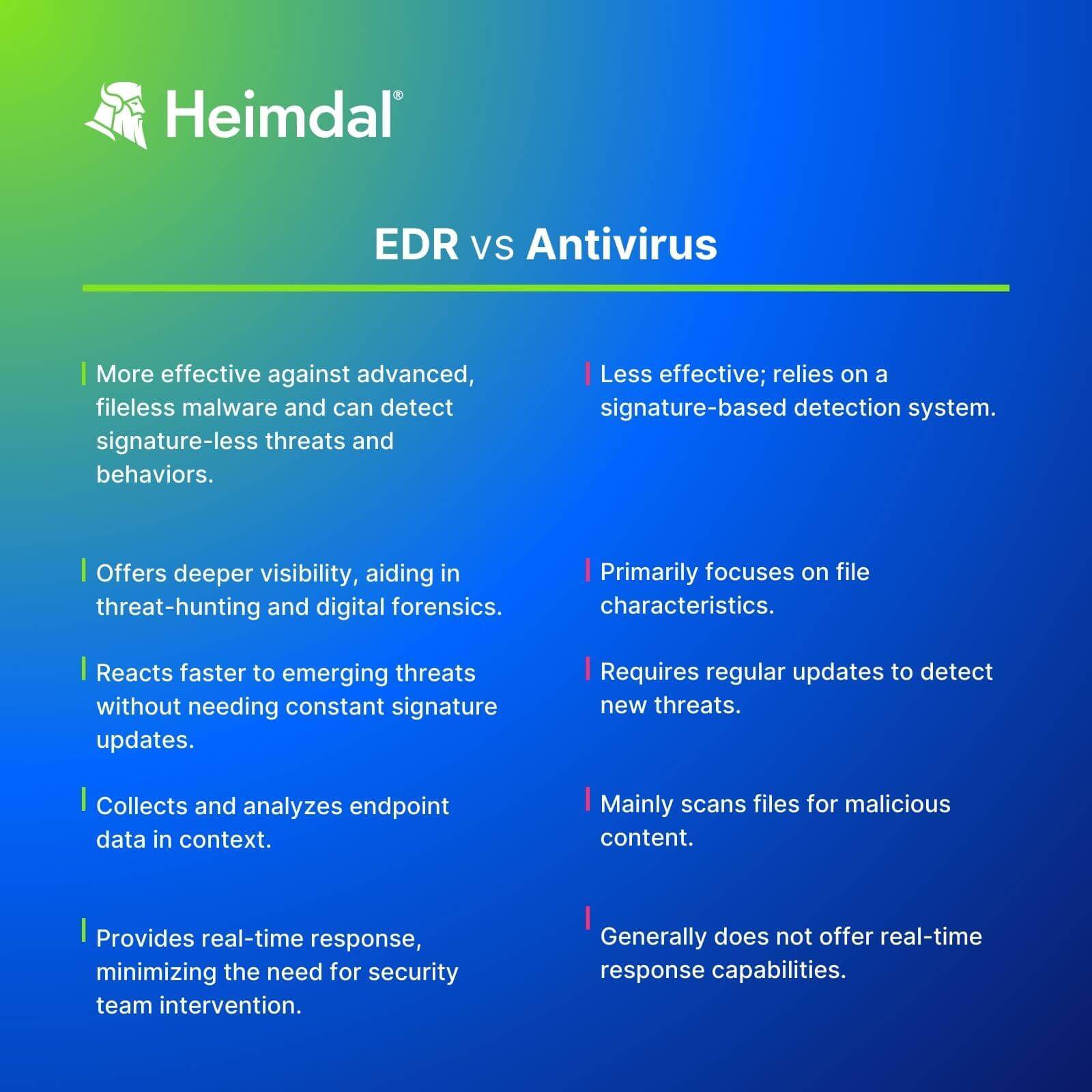
- EDR is more effective against advanced, fileless malware that can bypass Antivirus due to its signature-based detection system. Furthermore, it can detect signature-less threats and behaviors, providing better protection against sophisticated attacks.
- Using EDR offers deeper visibility into malware behavior, aiding in threat-hunting and digital forensics. By comparison, Antivirus primarily focuses on file characteristics.
- EDR reacts faster to emerging threats without requiring constant signature updates.
- Antivirus mainly scans files for malicious content, while EDR collects and analyzes endpoint data in context.
- EDR provides real-time response to incidents, minimizing the need for security team intervention.
- EDR is designed for breach situations, enabling damage control, countermeasures, and investigations.
- Antivirus is user-friendly and resource-efficient but offers less comprehensive protection compared to EDR’s continuous monitoring.
Heimdal®’s Approach to EDR Security
We’ve combined an Endpoint Protection Platform (EPP) with Endpoint Detection and Response (EDR) and achieved what we consider to be the golden standard in cybersecurity: EPDR (Endpoint Prevention, Detection, and Response).
Heimdal’s EDR brings you real-time proactive security via DNS filtering, smart threat hunting, proactive behavioral detection, automated patch management, a next-gen Antivirus, and a module for automated admin rights escalation/de-escalation procedures.
Thus, we deliver a layered security approach within a single and lightweight agent. Our customers get access to next-gen endpoint threat prevention and protection from existing and undiscovered threats. Plus a market-leading detection rate and compliance, all in one package.
By combining Heimdal Threat Prevention and Heimdal Next-Gen Antivirus & MDM you will obtain proactive IOCs and enhanced IOAs and gain a unique ability to mitigate even concealed or unknown malware.
Our dashboard always provides you with notifications and warnings for all active clients. It offers real-time threat and status reporting, delivered at the interval of your choosing. Your endpoint data will be graphed and scaled daily, weekly, or monthly and it can also be integrated into SIEM via API.
The Heimdal Security Unified Threat Dashboard (UTD) stores the entire history throughout your customer lifecycle and helps you perform compliance audits and risk assessments. Alongside weekly reports, data exports, e-mail alerts, and built-in data drill down, the Heimdal UTD offers a powerful yet simple way to manage your environment.
Our platform also enables you to define policies for each of your components in great detail. For example, you can refine the blacklisting of websites, files, processes, or patches per active directory group of your environment. This will give you the powerful option to individually tailor your IT environment and create policies to fit your exact needs across the Active Directory groups in your organization.
Once configured, the Heimdal deployment is simple and easy and can happen through any MSI deployment tool.
Because we’ve considered the evolving needs of the global enterprise, our EPDR technology works anytime and anywhere in the world, for both on-site and remote work set-ups.
Last but not least, our multi-layered security suite combined into our EPDR system comes in a user-friendly and easy-to-deploy agent, that will be extremely lightweight on your systems and will certainly become the greatest time-saver for your sysadmins.
Here’s a detailed product demo for you to check out:
Simple standalone security solutions are no longer enough.
HEIMDAL® ENDPOINT DETECTION AND RESPONSE SOFTWARE
Conclusion
No matter which solution you end up choosing, make sure it can be scaled up and down and that it fits your organization’s needs.
Should you want to try out our EDR technology, please register on the website or contact us at sales.inquiries@heimdalsecurity.com.
Here’s a detailed product demo for you to check out:










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








