Contents:
What Is a Drive-by Download Attack
Drive-by download attacks refer specifically to malicious code installed on your endpoints without your consent or unintentionally.
They are often used to deliver malware, such as worms, trojans, and ransomware.
Types of Drive-by Download Attacks
There are a few different types of drive-by download attacks that can occur:
- Exploit kits: They’re collections of codes used by attackers to take advantage of software vulnerabilities on the victim’s device. You can get infected this way through emails, messaging platforms, or even through a simple visit on a website that hosts an exploit kit.
- Malvertising: Codes inserted by threat actors in ads on legitimate websites. When clicked, this ads will redirect the victim to websites hosting an exploit kit, or it will automatically download the kit on the endpoint.
- Cross-site scripting (XSS) attacks: Such attacks happen when a website doesn’t validate or sanitize the user input before processing it, leaving space for threat actors to inject malware and spread them to users visiting the site.
- Phishing attacks: A well known one, in such attacks threat actors use social engineering tactics to tempt the victim into clicking an infected link or download malware-filled files. They’re usually conducted through emails, social media, and online messaging apps.
- Watering hole: These attacks target a specific group of users who are known to visit particular sites and resources on a regular basis.
Drive-by download attacks can be difficult to prevent because they often exploit vulnerabilities that are not yet known or patched.
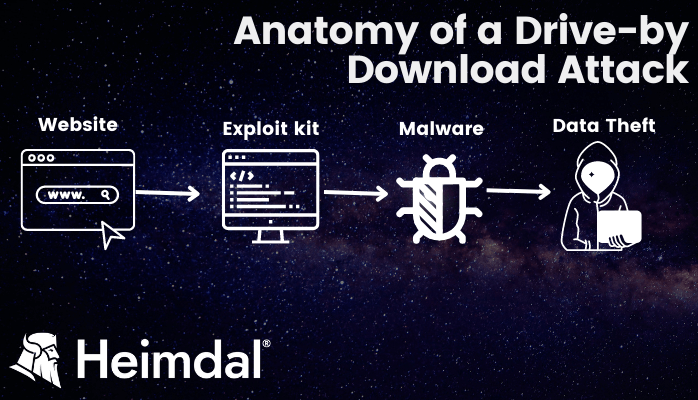
How Drive-by Download Attacks Work?
There are two types of drive-by download attacks: active and passive.
1. Active Drive-by Download Attacks
This type of attack needs the user to interact with the malicious content. The attacker will try to fool the victim into clicking an infected link, or download a file carrying malware.
2. Passive Drive-by Download Attacks
The attacker uses browser vulnerabilities to infect the victim’s computer with malicious code without their knowledge or interaction.
The type of drive-by download will determine what the payload will be. For example, if the goal is to steal data, then the attacker may create a malicious script that runs when the victim visits a specific website. This script would then collect information such as login credentials and send it back to the attacker. Consequences range from adware infections of the operating system to financial loss or even data encryption (in the case of ransomware).
What Does a Drive-by Download Attack Look Like?
Once installed, the malware can be used to steal sensitive information from the infected computer, such as passwords, financial data, and personal information. Through a drive-by download, the attacker can also take control of the infected computer and use it to launch attacks against other endpoints.
Drive-by download attacks are becoming increasingly common as attackers look for new ways to distribute their malware. Drive-by downloads are often difficult to detect and can have serious consequences for users who are infected.
Types Of Drive-by Download Payloads
These drive-by download attacks are used to introduce a series of malware into the victim’s operating system. These include:
- Adware: They target users’ devices through various online (banners, pop-ups)
- Trojans: Trojans disguise themselves as legitimate software, but in reality it contains malware
- Keyloggers: They track the user’s keystrokes to steal sensitive data such as financial details, login credentials, or others.
- Ransomware: It’s a type of cyberattack where the threat actors once infiltrated into the victim’s system steal important information, encrypts them or removes the owner’s access, and demand a ransom to be paid to get back the data.
- Botnets: These payloads are used mainly for DDOS attacks or in lateral movement of attacks.
Types of Data Targeted in Drive-by Downloads
There are many different types of data that hackers target in a drive-by download. These include:
- Login credentials: Usernames and passwords.
- Personal information: Names, addresses, email accounts, phone numbers, security numbers and anything else tied to a person’s identity.
- Financial information: Credit card details, banking operation details or account numbers for instance.
- Browser data: Cookies, bookmarks, search history.
- Business data: Any files tied to the business such as data, strategies, internal communications, R&D data to name a few.
Steps to Protect Yourself from Drive-by Downloads
Though it can be hard knowing whether a website is safe or hosting malicious programs, there steps you can take to protect yourself and your devices from drive-by downloads:
1. Keep your operating system updated
Remember to update operating systems with the latest security patches. These can help prevent hackers from using a drive-by download to ultimately get ahold of your sensitive data.
2. Download legitimate software
When downloading programs, especially free ones, always verify their source. Hackers can create seemingly legitimate programs that trick people into thinking they are downloading the right thing. They can be bundled with drive-by downloads full of malicious code.
3. Keep an eye out for pop-ups and stay away from suspicious websites and links
One of the best ways to protect yourself from drive-by downloads is by being aware of the websites you visit. You’ll know you’re on a safe site if you see “https://” or padlocks in the address bar.
If you enter a website and several pop-up windows appear, close them all and leave the site immediately. These windows could be trying to lure you into accidentally deploying a drive-by download onto your computer or mobile device, compromising your data and network via malicious software.
4. Remove unnecessary programs and apps
The more applications and plug-ins you have on your computer, the more security vulnerabilities you must manage. And you know who likes bugs and security flaws? You guessed it, drive-by downloads.
5. Install antivirus software
Antivirus software acts as your first defense against drive-by downloads, other emerging online threats, and malicious files. With a watchful eye protecting your information, you’ll be able to surf the web with confidence and an extra layer of security.
6. Start using a traffic filtering software
As it scans inbound and outbound traffic to make sure no malware program is about to come near your PC, it also prevents private and confidential information from leaking to any suspicious receivers.
One such software is our own Heimdal® DNS Security solution, which is a powerful blend of cybercrime intelligence, advanced ML, and AI-based prevention.
Heimdal®’s DNS solution ensures unparalleled accuracy in proactively protecting your organization from future threats. Our tool scans your users’ online traffic in real time, effectively blocking infected domains and thwarting communication with cybercriminal infrastructures.
Try our solution and you will benefit from:
- True DNS over HTTPS filtering: We are the first vendor in the world to integrate true DNS over HTTPS in a product, evolving past the standard rerouting of DNS packages.
- Advanced Malware Detection: Take full control of your DNS, HTTP, and HTTPS communications through unique machine learning-computed threat intel that empowers you to move the needle from traditional antivirus threat detection to a prevent & hunt posture.
- Unparalleled Proactive Protection: Unleash the ability to combat insider threats, detect and eradicate shadow IT instances, and neutralize any form of malicious activity linked to compromised accounts.

Heimdal® Network DNS Security
- No need to deploy it on your endpoints;
- Protects any entry point into the organization, including BYODs;
- Stops even hidden threats using AI and your network traffic log;
- Complete DNS, HTTP and HTTPs protection, HIPS and HIDS;
How Can Website Owners Avoid Drive-by Downloads?
As a website owner, you play a critical role in protecting your visitors from potential hackers and drive-by downloads. Consider reinforcing your infrastructure with the following tactics to provide your users with the maximum security and peace of mind:
1. Keep all website elements up to date
Update all website components regularly, including extensions, add-ons, plugins, and other infrastructure aspects that could allow in malicious code.
2. Remove outdated or unsupported components
Remove any obsolete software or website components to prevent drive-by downloads. When security patches are not applied regularly, obsolete software becomes an attractive target for thieves and malicious code.
3. Use strong passwords and usernames for administrator accounts
Use strong passwords and usernames for your administrative accounts to increase security. For increased security, use password generators and a password manager.
4. Keep an eye on website advertisements
A Drive-by download frequently takes advantage of advertisements. Maintain vigilance to ensure that your users are not exposed to suspicious adverts.
5. Implement Web Application Firewalls (WAFs)
Use WAFs to monitor and filter website traffic, protecting against potential threats and drive-by downloads. WAFs can also help detect and block malicious communications helping you to stay safe.
6. Use HTTPS for secure communication
Make sure your website uses HTTPS rather than HTTP, a secure protocol for data exchange between your website and consumers’ web browsers. Hackers will find it more difficult to intercept and inject harmful code with this encryption.
7. Limit the use of third-party content
Use caution when including widgets or advertisements from third-party sources on your web page, as such content is typically the cause of drive-by downloads onto a computer.
Conclusion
Drive-by download attacks are a serious threat to data security, and threat actors have been increasingly leveraging them for malicious purposes. Organizations and individuals alike need to recognize the potential risks that these types of attacks pose, as well as the available countermeasures they can take to mitigate them.
Take proactive steps such as keeping systems up to date with patches, using strong passwords and antivirus software, running regular scans for malware, and avoiding suspicious links or downloads from untrusted sources, this way you can reduce the risk of becoming the victim of drive-by download attacks.
Frequently Asked Questions (FAQ)
What is meant by drive-by downloads?
Drive-by downloads refer to malicious software or code downloaded unintentionally onto an endpoint.
Are drive-by downloads still possible?
Yes, drive-by downloads are still very possible and can come in many ways: accessing an infected link, clicking on an infected ad, or downloading an infected file.
What do drive-by download attacks exploit?
Drive-by download attacks exploit vulnerabilities that are not yet patched or discovered.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security