Contents:
Identity theft is a growing problem in today’s digital world. With more of our personal information available online, it can be difficult to protect ourselves from malicious actors who may use our data for malicious purposes.
While it might seem like an intimidating issue to tackle, this 20 steps guide on how to prevent identity theft will equip you with the knowledge you need to stay safe and protect your personal data.
What Is Identity Theft?
Long story short, identity theft is the illegal use of someone’s personal information.
The U.S. Department of Justice explains that identity theft refers to when a criminal uses someone else’s personally identifiable information (PII) to commit fraud, usually done for financial gain. There are many ways to commit identity theft, including hacking, financial and social media account takeovers, credit card fraud, phishing, and even ransomware attacks.
When cybercriminals commit identity fraud, they might use a stolen identity to:
- Open new accounts or credit lines
- Receive medical care with your stolen insurance information
- Steal tax refunds
- Provide your personal credentials in the event of an arrest (name, date of birth, address, etc.)
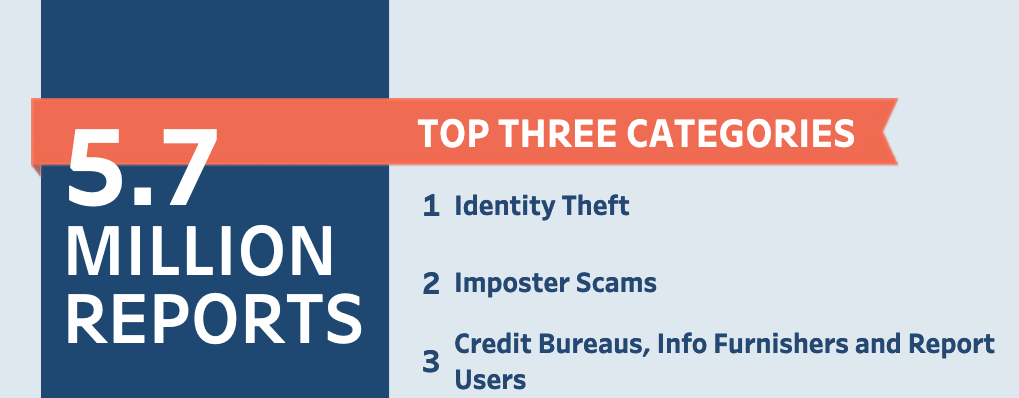
In 2021, traditional identity fraud losses, meaning those involving any use of a consumer’s personal information to achieve illicit financial gain, amounted to $24 billion (USD) and ensnared 15 million U.S. consumers. Losses involving identity fraud scams (direct contact with victims) totaled $28 billion and affected 27 million consumers in the United States.
Types of Identity Theft
There are many different types of identity theft, and each one can be devastating. Here are some of the most common types:
- Financial identity theft: This is when someone uses your personal information to open new accounts in your name and run up debt. This can ruin your credit score and leave you with a lot of debt to deal with.
- Medical identity theft: This is when someone uses your insurance information to get medical treatment or prescription drugs. This can lead to false claims on your insurance, higher premiums, and even denial of coverage.
- Tax identity theft: This occurs when someone uses your personal information to file a tax return in your name and claim a refund. This can leave you owing money to the IRS or state tax agency, and it can take months or even years to resolve the issue.
- Criminal identity theft: When someone uses your personal information to commit crimes in your name. This can lead to arrest and imprisonment, even if you have not actually committed any crime yourself.
- Child identity theft: This is when someone steals the personal information of a child for their own use. Children’s identities are often used for financial fraud or other crimes, as they generally have clean credit histories. This can have a major impact on the child’s future finances and well-being.
Warning Signs of Identity Theft
There are a few key warning signs that can indicate that your identity has been stolen. If you see any of the following red flags, it’s time to take action to protect your identity and your finances:
- You receive bills or collection notices for accounts you don’t recognize
- There are unexplained withdrawals from your bank account
- You get calls or letters from businesses about products or services you didn’t purchase
- You notice new accounts or loans on your credit report that you didn’t open
- You get denied for credit or loans because of information on your credit report that doesn’t seem right
If you suspect that your identity has been stolen, the first step is to contact the credit bureaus and place a fraud alert on your file. You should also reach out to your financial institutions and any businesses where you think the thief may have opened new accounts in your name. By taking these steps, you can help protect yourself from further damage and start the process of reclaiming your identity.
How to Prevent Identity Theft?
As Bruce Schneier said:
“Identity theft is the new crime of the information age. A criminal collects enough personal data on someone to impersonate a victim to banks, credit card companies, and other financial institutions. Then he racks up debt in the person’s name, collects the cash, and disappears. The victim is left holding the bag. While some of the losses are absorbed by financial institutions — credit card companies in particular — the credit-rating damage is borne by the victim. It can take years for the victim to clear his name.”
Once identity theft occurs, it is extremely difficult to recover the information that cybercriminals have stolen. Many times, you aren’t even aware of how or when it happened.
That’s why it’s always better to take proactive security measures, that will prevent fraudsters from stealing your personal details and information. It’s easier to play it safe instead of only react once the damage is done and it’s too late to keep it under control.
Protect Your Identity from Online Threats

1. Choose a good password for your online accounts
One of the most important steps is: always make sure that your passwords are strong and unique. Make them around 15 characters long, use both uppercase and lowercase letters, as well as numbers and symbols.
Don’t use your birth date, phone number, social security number, family members name or your pet’s name – these can be easily guessed by an attacker, usually just by looking over your social profiles.
Additionally, don’t reuse passwords between your accounts. If you used the same pass everywhere, attackers will be able to access all of your other accounts.
But how exactly are we supposed to do this, if we create so many online accounts?
First of all, don’t write them down – not on a paper on your desk, not in an email draft, not on a text file that you leave on your desktop. Those are unsafe locations.
Instead, you can start using a password manager. It will remember all your passwords and store them in a secure way.
Another key security step is to activate the two-factor authentication wherever it’s available.
2. Don’t post confidential information online
Think twice before publishing information about you. Everything that we post online will remain there and be available for everyone who wants to see it.
As much as we’d like to think that we have control over our privacy, the truth is we can never be sure who’s watching us. We will never know where that information will end up. Even if we take all the possible security measures, we still depend on other services and systems, that might not be as safe as they claim they are.
That’s why it’s important that we pay attention to all the data that we place in comments, private messages, posts, check-ins, photos or anything else that we display online.
And by “online” we mean posts, photos, check-ins or comments on blogs, social networks (Twitter, Facebook, LinkedIn, Instagram, etc), but also websites such as AirBnB, TripAdvisor, Booking and so on.
3. Think twice before you post personal information about you on social networks
There is no discussion that social media is an important part of our lives. Especially nowadays, when all our friends, work colleagues or family members have a social media presence. It’s the one place where we can find almost anyone.
This leads to an increasing danger for our personal information, since it’s a blurred line between what’s public and what’s private.
No matter how careful you are with the privacy settings, you can never fully be in control.
Here are more tips on how to keep your Facebook account secure.

4. Watch out for phishing scams
Phishing is one of the oldest cyber threats, but it still causes a lot of damage. Attackers have constantly improved their techniques and fraud methods.
The main phishing schemes and campaigns appear when:
- we shop online
- we check our email account
- access social media networks
Though phishing uses multiple channels to get our credentials, email spam campaigns remain the main successful method.
5. Be careful when you shop online
Online shopping needs a step of its own, as the online medium has undoubtedly become extremely convenient when it comes to shopping. We have more options than ever in just one place, one click away, saving us lots of time and money.
The most crucial aspect when buying online is to ensure you find yourself on a legitimate website.
Here is how you can make sure you don’t send your financial details to cybercriminals:
- Shop from known, trusted websites. This will reduce any odds of unpleasant surprises.
- Check if the connection is encrypted. You can do this by looking at the address bar: is there an icon of a green lock? Does the address start with “https” instead of “http”? The extra “s” means that the website has SSL (Secure Socket Layer) certificate.
- Also make sure that you activate a second-authentication factor when paying online. You will receive a final identification code on your phone before placing the order.
- Safest way to go is use a separate card just for online shopping. Transfer money on it only when you want to buy something, otherwise keep it with a low amount on it (for maintenance taxes). This way, in case something bad happens, you still have a safety net.

6. Secure your browser settings
Our browser is the main tool for connecting to websites. For this reason, an important degree of attention needs to be given to it.
- Make sure you have the last browser version that contains all the available security patches.
- There is no such thing as a free program, so make sure you double-check how secure and legit a free program is with a quick web search before you download it.
- Use a private browsing session if you connect from a public computer. You don’t want your browsing history details to be recorded locally.
- To make sure your connection is safe, you can encrypt it using VPN software or Tor browser. It hides your browsing activity by routing your traffic through the Tor network of computers.
Here are more tips on how to improve your browser’s security settings.
7. Protect your computer with multiple security products
Identity thieves use multiple tools to get to your personal data. We are not talking about common viruses here, we refer to advanced malware and spyware tools, such as keyloggers, exploit kits and remote administration tools. These are capable to retrieve sensitive information from a system without your knowledge.
Advanced malware is designed to evade normal antivirus detection. Sometimes a long time will pass until you become aware of its presence. Precisely this is why a good antivirus is a must-have. It minimizes the times you have to enter damage control mode to clean up the mess caused by a successful malware attack.
8. Use a specialized security solution against financial and data stealing malware
Traditional security solutions may not be able to fight advanced pieces of code developed by cyber-criminal minds.
To assure financial security for banking operations and protection against zero-day malware, you need an advanced scanning technology that can protect you from the latest threats.
9. Keep your operating system safe from spyware
Spyware is a type of software capable of installing on your computer in order to launch pop-up windows, redirect your browser to malicious locations and monitor your browsing sessions and your overall internet connection.

10. Keep your system and software up to date
Keep your system up to date with the latest security patches available. The same thing you should do for your vulnerable applications and programs.
If you don’t want to bother checking and keeping those apps up to date every day, you can also use a dedicated solution to do the job.
11. Use alerts
You think you know what purchases you have operated that month; you might even have SMS alerts activated. However, threat actors always find ways to steal just small amounts of money, in order to test your attention.
There are so many cases where customers’ credit card information has been “read” and used in restaurants and stores, only to find out later about this, when it was already too late.
A good idea is to activate the option to receive alerts for any sum of money that has been retrieved. Many financial institutions will text or email when transactions are made. Sign up so that you know when and where your credit cards are used, when there are withdrawals or deposits.
Protect Your Identity from Physical Threats
The following steps are meant to address physical theft attempts, as they can cause just as much damage as online threats.
12. Who’s watching you?
You are in front of an ATM machine or at the local shop and try to withdraw some money or just insert your PIN to pay.
Before placing your sensitive data, make sure there is no one around you that might be able to see you information. Even if you don’t see anyone around, there may still be special surveillance mechanisms in place, so just to make sure you are on the safe side and try to hide the numbers you insert.
13. What do you carry with you?
Before you leave your home, take some time to consider which things to take with you. By carrying only the necessary items, you’ll limit the potential loss.
Furthermore:
- Don’t leave your bag unattended in a public place or place it far from you.
- Don’t leave your wallet or purse in a jacket just hanging around. Don’t make things easy for a thief.
- Consider distraction elements for the thieves. You can keep a fake wallet or simply don’t place important things in the bag that can be stolen. Keep the important stuff close to you.
14. Destroy any documents or papers you don’t need anymore
We all keep important data in our homes. It can be information from past workplaces, medical records, certifications and diplomas, maybe even confidential information related to your work.
We all have the tendency to collect various papers and pieces of information. Some of them we might not actually need anymore, such as receipts or bank statements. Though we may not need that data anymore, it doesn’t mean that for fraudsters it’s not an important element that can be used.
Make sure you destroy those papers before you throw them away. Don’t just place them in a garbage can, use a shredder for example.
15. Protect your mailbox
Try to think like an identity thief. You need to find personal information, especially financial details about someone. How do you do it? Where do you start from?
The easiest way is to start with those less protected areas, such as the mailbox. And now that you know where they will attack, just think about it:
What type of information do you receive in the mailbox? Do you receive important documents from the bank, maybe the next credit card? If you do, you need to contact the bank and have them stop this type of correspondence. If you have important stuff you need to collect, just go to the bank and pick it up.
Do you receive invoices for every service in the house? Maybe it doesn’t seem like too much data for you, but an identity thief can use this information to correlate it to other sources in order to have an image on your financial situation. It would be easier to receive the invoices by email, since today most services providers offer this option.
How well did you secure your mailbox? If anyone can access your mailbox and you know that vital information is delivered there, probably you should get a high security locking mailbox or a personal one in the post office.

16. Do you know who’s calling?
Yes, an identity thief may call you, posing as a bank agent or official representative and ask for private details or financial data.
How does the thief know what’s your bank? Well, keep in mind the previous points. It isn’t that hard to obtain information about you. They may look through your mailbox, they may watch you at the shop or at the ATM, or they may even look through your garbage. It is not difficult to discover this piece of information.
And don’t be fooled by the professional tone they use or the fact that you’re talking to a nice woman. This criminal profession knows no limits. Therefore, do not provide important information over the phone, unless you initiated the phone call, and you really know who you’re talking to.
One more thing to be aware of, when you’re answering the phone – AI voice cloning. Scammers are now able to steal the voice of your relatives, friends, or coworkers. Jacob Hazelbaker explained how this relatively new scam works:
17. Destroy your digital information
Nowadays we all use cloud services to store our important files, no matter if they are work documents or personal photos.
However, along the years we collected various types of information on CDs, DVDs or external hard drives. And sometimes, we have been forced to throw into thrash a hard disk which didn’t seem to work anymore, without thinking about the private data we left on it.
To understand how the information from an abandoned disk can harm you, just think about all the photos, documents and private details you left on them.
Using special tools and software, a hacker who finds such a disk can retrieve all that information easily and use it against you – even if you deleted it and formatted it before throwing it.

To make sure that an insecure disposal of old disks doesn’t become an opportunity for identity thieves, you need to be sure that you destroyed that data.
The following options are available:
- Overwrite the data a few times and make things a bit more difficult for an identity thief. You can also use specialized software that will do this for you.
- Physically destroy that hard disk or that CD/DVD.
- Did you know printers and photocopiers also have hard disk built in? So don’t just throw away that printer before removing the hard disk first.
18. Protect your Social Security number
This is one of the most important steps you need to take to protect your identity from thieves, since this piece of information can be used in multiple situations.
An identity thief can use your social security number to apply for a new credit card or open a bank account, ask for a loan or even rent a house.
It can also be used to prove your identity over the phone or online, in order to access private information.
Here are a few techniques to protect it:
- Don’t use it as a password on any online account.
- Don’t just take it with you anywhere, unless you really need it.
- Don’t send it over the email.
- Don’t store it on your computer, your smartphone or your cloud drive.
19. Keep your smartphone safe
Nowadays we can do all our work just by using smartphones. We use them to take pictures, to stay informed, to keep in touch to our friends, to access our cloud storage or even run financial transactions.
And this becomes our greatest risk. Just think about the amount of information one can gain just by accessing our smartphone.
That’s why we need to underline a few steps you can follow to make sure your smartphone’s data doesn’t fall into the wrong hands:
- Download apps from well-known companies, especially apps that are used for financial transactions.
- Secure the mobile device with a strong password or better yet, use 2 methods to keep it sealed from any breach. Biometric authentication, such as locking it with your fingerprint, might prove to be the most secure one.
- Use the best apps available to protect your smartphone. Most of them include a GPS feature and a remote wipe out mechanism.
Here’s an extended guide on how to keep your smartphone secure.

20. Back it up
We don’t mean the computer back-up, but rather the idea of backing something up in the event that certain thing may become lost at some point.
Let’s try to answer a few questions so that we may clear this up and find solutions:
- Are you keeping all your money on one credit card? Why? Use at least two and split the money between them.
- Do you carry both cards with you when you go out? Why? Just take one. Or at least don’t place them both in the same place. This way, you’ll limit the potential loss.
- Do you need to verify your identity somewhere? Ok, take an identification paper or document with you, but don’t take the ID, the driver license and the passport along.
- And do you really need an official document with you? Maybe you can replace it with a photocopy. In any case, make sure you always have photocopies for all the important documents, especially when travelling.
- Do you have a phone number where you can call for help in case you lose an official paper or the credit card?
Conclusion
Identity theft is a serious issue that can have devastating effects on victims. We hope this guide has provided you with the essential knowledge and tools to help protect yourself from identity theft. Keeping your personal information safe should be your top priority, so remember to always keep an eye out for anything suspicious and take proactive steps when it comes to protecting yourself online. By taking a few simple steps, such as locking down your accounts, using strong passwords, being aware of phishing scams, and keeping track of your credit score, you can protect yourself from potential identity theft. Taking these precautions now will save you time and money later on down the road.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, YouTube, and Instagram for more cybersecurity news and topics.
Did you ever have to deal with an identity theft attempt? How did it happen and what did you do to control the damage?
Share your experience with us in the comments below.
* This article was initially published by Aurelian Neagu in April 2015 and brought up to date by Mihaela Marian in January 2023.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security







