Contents:
The principle of least privilege (POLP) is a security concept that limits users’ access rights to only what is strictly required to do their jobs As the landscape of threats gets more complex, so too must the tactics we use to stay protected.
In this blog, we explain everything you need to know about least privilege and how to implement it.
What Is the Principle of Least Privilege?
Any business that’s serious about cybersecurity in 2024 needs to think about least privilege. In today’s cloud-based world, there’s no other effective framework or policy that can both reduce the possibility and scope of a potential attack.
Bogdan Dolohan, Head of Technical Support, Heimdal®
The principle of least privilege (POLP) is a cybersecurity concept that limit the access rights of users to only what is strictly needed to do their jobs. It’s an approach that has become increasingly popular over the last few years. For many, it’s now simply the default setting for effective, modern security.
At its simplest, it means giving access to all sensitive information and critical systems on a strictly ‘need-to-have’ basis.
The goal here is to reduce service and user access permissions to the lowest possible amount of privilege access. Of course, that involves revoking access permissions to any users who don’t absolutely need them.
But for the strategy to really achieve its goals, it needs to look far wider than just grating access permissions – more on this below.
But before we start, there are a few overlapping terms that it can be helpful to get our heads around:
- Principle of Least Authority (POLA) – Another way of describing POLP
- Principle of Minimal Privilege (POMP) – Another way of describing POLP
- Zero Trust – A security concept based on the idea that organizations shouldn’t automatically trust anything inside or outside their environment. Instead, everything should be verified. Least privilege is a component of zero trust. Technically, least privilege refers to only the aspects of zero trust relevant to access permissions – but increasingly the two terms are used interchangeably. In this blog, the strategies we discuss are relevant to both terms, since they’re effectively two sides of the same strategy.
- Privileged Access Management (PAM) – Privileged access management refers to any policies an organization uses to manage access to sensitive information, sensitive data and assets. Least privilege is therefore a framework through which effective PAM can be achieved, which lowers the risk of a security breach happening.
Done right, the benefits of least privilege are simple: better security.
By reducing the attack surface to its smallest possible amount, we can minimize both the risk of an attack and the potential damage a successful one can cause. It should also simplify your regular compliance and auditing tasks.
So where do you start?
Why Is Principle of Least Privilege (POLP) So Important?
At its core, the principle of least privilege is nothing new. The idea of restricting access to sensitive information is far older than the technology we rely on today – and it doesn’t take a genius to work out why it works.
The fewer people that have access to a sensitive asset, the less overall risk there is. In that sense, it’s pretty similar to the “need to know” principle of military and government organizations.
But over the last few years, least privilege has become increasingly important for modern cybersecurity – due to the complexity of today’s IT environments.
Once upon a time, companies could rely on all their accounts and assets being wired up to a physical network. Today, organizations are likely to use a whole range of different distributed assets and critical systems, including:
- Operating systems – Windows, macOS, Unix, Linux
- Endpoints – Desktops, servers, laptops, tablets, smartphones, internet of things (IoT) devices
- Computing environments – Cloud, on-premises, SaaS, DevOps environments, edge computing, virtual machines
- Identities and user roles – Including human, application, and machine identities
- Third-party – Suppliers, vendors, partners, contractors
As well as the complexity, today’s technology is also much more democratized. Where once IT admins had full control over the software, hardware, and assets being used – that’s no longer the case.
Now, everyday business users can install apps, provision software, and spin up virtual machines. This creates a whole new tier of users with privileged access – all of which need to be carefully monitored and managed.
All of this makes modern cybersecurity uniquely challenging – and that’s where least privilege comes in.
By applying the principle to each of the systems and endpoints listed above, we can achieve an effective cybersecurity strategy that’s properly tailored to the modern threats we’re trying to defend against.
The Modern Landscape of Privilege Access
Before we describe how to implement least privilege, it’s helpful to first understand the specific types of threats we’re trying to defend against.
Today’s hackers know how to use distributed cloud environments to their benefit. This has given rise to a wave of sophisticated attacks and entry points that modern cybersecurity strategies need to be aware of in order to defend against:
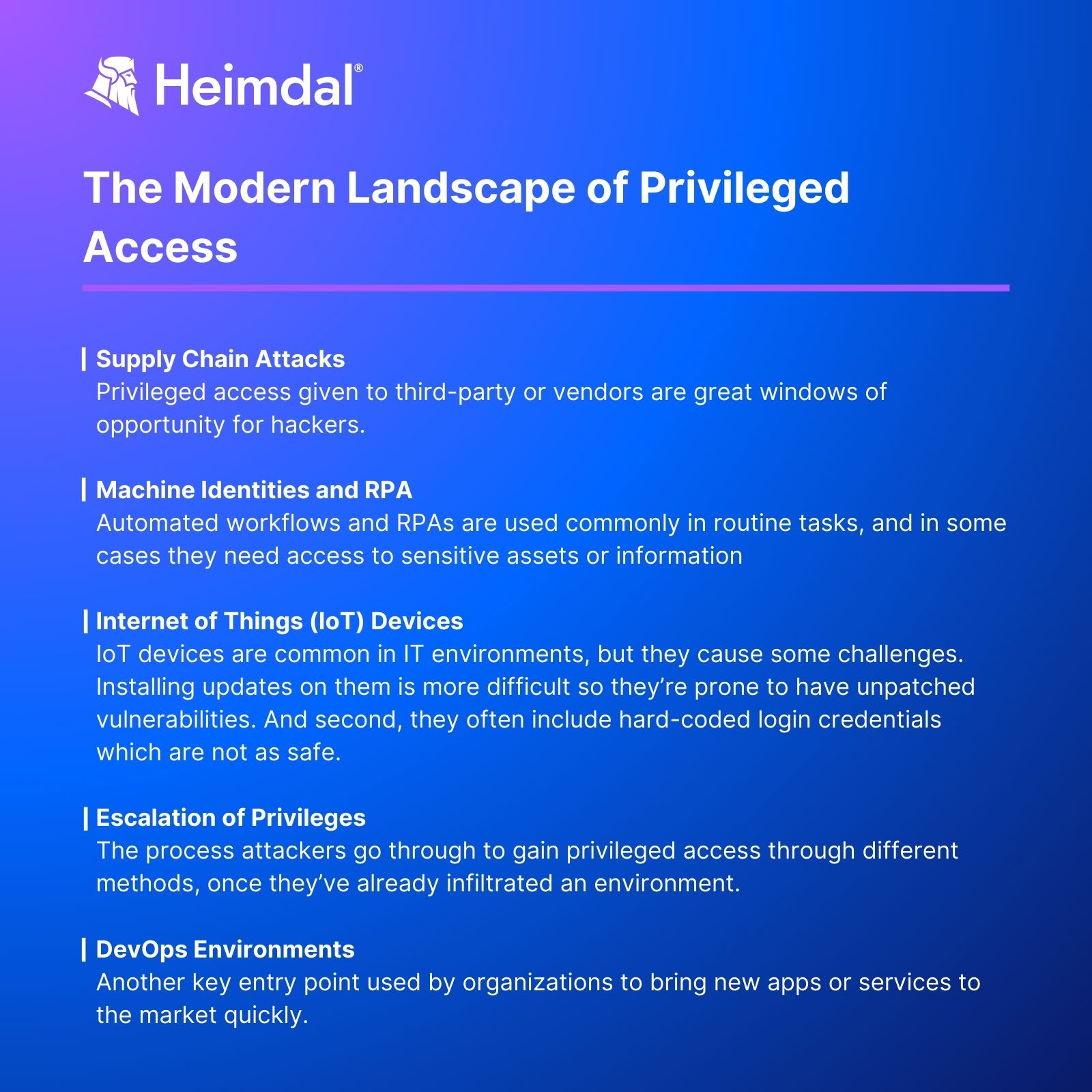
1. Supply Chain Attacks
Today’s businesses often need to provide privileged access to third-party partners and vendors. For hackers, this is a great opportunity, since it’s much more difficult to manage the security of a third party.
At least in the last year, we saw that supply chain attacks moved to the forefront of the cyber world. According to Verizon’s 2024 Data Breach Investigations Report, the use of vulnerabilities to initiate breaches grew by 180% in 2023, and of those, 15% involved a supplier or third party.
Take for example this case of 3CX, or last year’s supply chain attack on Okta to see the magnitude of supply chain attacks. But there is another example of a supply chain attack that took the cybersecurity space by storm.
The most famous example of this is the 2020 SolarWinds attack, when hackers gained access to the SolarWinds network and inserted malicious code into a seemingly innocuous software update.
That update was then installed by SolarWinds customers, which included multinational companies and government agencies. Many of these then suffered serious data leaks in the months and weeks that followed.
Companies looking to protect against similar risks need to extend least privilege policies to third-party vendors and suppliers, as discussed below.
2. Machine Identities and RPA
Automated workflows and robotic process automation (RPA) are now commonly used for routine admin tasks. In some cases, this requires access to sensitive assets (e.g. to install routine updates) or information (e.g. to retrieve customer contact details from a CRM).
These machine assets require privilege access in exactly the same way an IT admin or HR manager might.
These are referred to as ‘service accounts’ which, if unsecured, can provide an easy back door for hackers. Many organizations struggle to effectively manage these.
Many don’t understand what service accounts exist in their IT environment and the dangers they pose.
3. Internet of Things Devices
The days of endpoints being mostly computers, monitors, and printers are long over. Today, internet of things (IoT) devices are common in IT environments, including tech as diverse as voice assistants, digital sensors for manufacturing machinery, or smart kettles.
But these devices cause challenges for several reasons. First, installing software updates is usually more difficult than with laptops or computers, increasing the risk of attack via an unpatched vulnerability.
But here’s another problem: IoT devices often include hard-coded login credentials – which means anyone with access to the source code can see the passwords as plain text.
It also makes it more difficult to rotate or switch passwords. All of these factors add up to make IoT devices a handy entry point for hackers.
4. Escalation of Privilege
It’s easy to think that if your most sensitive accounts are secure, then you’re probably going to be ok. After all, even if a hacker is successful, they’re not going to be able to access anything important, are they?
Sadly, hackers are generally a bit cleverer than that.
Escalation of privilege refers to the process attackers go through to gain privileged access once they’ve already infiltrated an environment.
Generally, they will gain access through basic exploits, or phishing scams targeted at a non-privileged user account. These might not get flagged as high-risk by security tools, since they’re not directly targeting sensitive accounts or information. Then, hackers can use known or unknown vulnerabilities to escalate their own privileges or piggyback onto disused accounts that haven’t been deleted.
‘Pass-the-hash’ attacks are another popular way for hackers to move laterally through an environment.
These are long, encrypted strings of characters that are used to authenticate users in lieu of a password.
Hackers can retrieve these from active memory and use them to escalate their own privilege without ever having access to the plain text password.
Effective least privilege, therefore, needs to inhibit hackers’ ability to move through your IT environment – as well as simply stopping them from infiltrating in the first place.
5. DevOps Environments
DevOps environments are another key entry point. Often, they’re used by organizations to quickly bring new applications or services to market.
But the need to innovate quickly can often lead to lax security management.
Often, the software developers working on these projects require privileged access to make changes to software and infrastructure or spin up virtual machines.
But often, organizations will grant them more privilege than is needed, simply to avoid delays and friction. At the same time, accounts can be shared, and access often isn’t revoked once the task is complete.
This is a pretty classic example of ‘privilege creep’, where permissions gradually expand in an organization over time.
This isn’t specific to DevOps environments, but they’re a particularly notable example of where this can happen.
Least Privilege Best Practices
We’ve now discussed why least privilege is so important and the specific landscape of modern attacks it seeks to defend against. But if you want to implement it in your IT environment, where do you start?
Here are eight least privilege best practices to get you on the right track.

1. Remove Unnecessary Privileged Accounts
The first step is perhaps the simplest; work out what privileges you have and reduce them to the least possible amount. An effective modern privileged access management solution can automatically scan and identify what privileged accounts exist, including service, disused, and orphan accounts. Then, delete any accounts that are no longer needed and revoke permissions to all others that don’t need them.
2. Constantly Monitor
Least privilege is a journey not a destination. There’s no single app you can install, skill you can train, or process you can create that’ll get least privilege done. It’s all of these things and more. Done right, it’s a mindset that’s applied to everything you do. First, assume risk, then work backward from there to reduce that risk as much as possible.
Bogdan Dolohan, Head of Technical Support, Heimdal®
Privileges have a tendency to gradually expand over time, so it’s important to remain constantly vigilant. First and foremost, this requires regular least privilege audits, ensuring elevated access is regularly reduced to the lowest possible amount.
But the right software can also make a huge difference here. Ideally, you need to be implementing the most up-to-date privileged session management and user behavior analytics tools. These can spot suspicious behavior in an IT environment, making it easier to isolate privileged user sessions and revoke access when needed.
Privileged access management (PAM) tools can also automatically identify disused or ‘orphan’ accounts, making it easier to proactively reduce your overall attack surface over time.
3. Eliminate Superuser Accounts Where Possible
Some elevated accounts have more privileges than others. Naturally, those with the most access pose the most risk – so ‘superuser accounts’ are the biggest target. These are known as ‘root access’ accounts in Linux or macOS environments and ‘administrator’ accounts in Windows – and they often have unfettered access and control over the entire IT environment.
If a hacker gains access to these accounts, the consequences could be fatal. The best approach by far is to eliminate root or administrator privileges entirely and split privileges between different accounts. If you can’t, then reduce superuser accounts to an absolute minimum. If they are needed, you could increase their security by allowing access only through privileged access workstations (PAW). These are isolated machines with strict security controls that can be difficult for hackers to access.
4. Replace Hard-Coded Privileged Credentials with APIs
As we discussed above, hard-coded credentials pose a significant risk. Effective security policy requires passwords to be changed regularly, which is much more difficult to achieve when they’re embedded into an application’s source code.
Perhaps more importantly, if hackers can access the code, they can see the password in plain text form. This also applies to SSH keys, DevOps secrets, and other sensitive privileged credentials.
Ideally, you should avoid including passwords in source code in the first place – and refuse to work with third-party suppliers that do. But if you don’t know where to start – an effective privileged account management (PAM) tool can automatically detect any hard-coded credentials and force applications to instead authenticate via APIs or through a centralized password safe. Then, you can implement effective policies to govern how complex these passwords are and how often they have to be changed.
5. Extend Least Privilege to the Whole Supply Chain
With supply chain attacks becoming more and more common, it’s no longer enough to only focus on your own organization. It’s also important to extend your least privilege policies to the whole supply chain.
That means reducing any third-party access to sensitive information to an absolute minimum and ensuring any third-party access is monitored and audited in the same way as with internal identities. Any external vendors, suppliers, or partners you work with should also adhere to the same strict least privilege policies that we outline in this blog.
6. Rethink Passwords
Passwords have been the default setting for cybersecurity since the earliest days of technology. But they’re far from the best way to authenticate and are becoming increasingly redundant. Instead, organizations are turning to multi-factor authentication (MFA), digital tokens, one-time passwords, or single-sign-on. These can be used alongside traditional passwords or replace them entirely.
These alternative methods can make it difficult or impossible for hackers to access accounts. It also helps to avoid the risk of pass-the-hash attacks, by eliminating the need for hashes entirely or ensuring they’re already rendered obsolete by the time hackers get hold of them.
7. Enable Just-in-Time Access
Just-in-time access is another way to tighten and govern sensitive information. The idea is that no individual should be given unconditional or ‘standing’ privileges. Access should be conditional and time-limited, meaning users can only access sensitive data or assets when they actually need to.
Again, the solution here lies in technology. A privileged account management (PAM) tool should allow you to dynamically escalate and de-escalate privileges and establish expiry windows. It should also analyze realtime behavioral anomalies to identify suspicious behavior. This can include users logging in from a new device or location – making it easier to lock down accounts and deny access even when hackers do infiltrate.
8. Segment Your Network
As we discussed above, lateral movement can be a significant cybersecurity risk. Effective least privilege should make it as difficult as possible for hackers to elevate their own privileges. There are several ways to optimize your architecture to achieve this.
Ideally, you want to segment your network as much as possible to limit lateral movement. Firewalls can be used to create self-contained zones within your IT environment, either between guest and corporate WiFi, dev and production environments, or having self-contained servers, databases, and more.
It’s also possible to segment virtualized environments through the use of software-defined networking. All of this creates barriers in your IT environment that are difficult for hackers to pass through.
The truth is, the vast majority of modern attacks aren’t because of some new invasive cybersecurity method, or a superpowered AI hackbot. The vast majority of attacks are much more pedestrian; either simple phishing scams, or through hacking disused accounts that should have been deleted years ago. If you’re wondering where to start with least privilege, you can achieve a lot with just the basics.
Bogdan Dolohan, Head of Technical Support, Heimdal®
Heimdal®: How to Get Least Privilege Right
Implementing least privilege is possible without the right tools, but it’s difficult and often ineffective. Ultimately, the task of monitoring and auditing user and service accounts across a whole IT environment is simply too complex to be done manually.
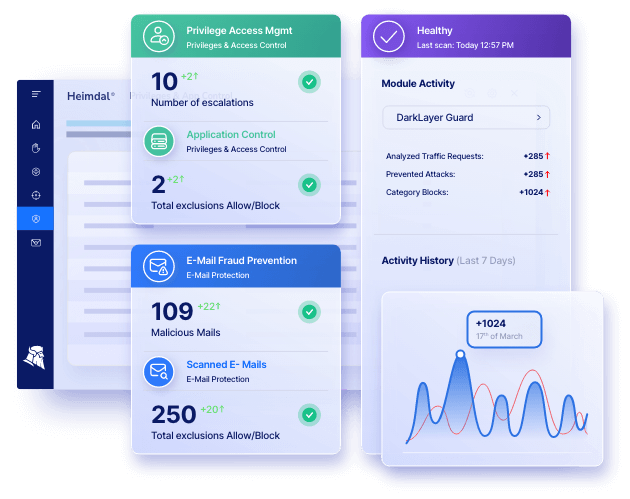
Without modern privileged access management (PAM) tools, it’s too easy for organizations to lose track of what accounts they have and what sensitive assets they have access to. And if you don’t know what you’re protecting against, you can’t hope to implement least privilege effectively. So how can the right software help?
- Automatically scan and identify all privileged accounts;
- Enable just-in-time access to avoid standing privileges;
- Identify and remove all hard-coded credentials;
- Implement multi-factor authentication, one-time passwords, digital tokens, and other security protections;
- Access ongoing monitoring and behavioral analytics to shut down suspicious behavior.
Heimdal® gives you the tools you need to make least privilege a reality.
FAQs: Principle of least privilege
What is the principle of least privilege?
The principle of least privilege (POLP) is a security strategy where individuals are granted only those access rights essential for performing their specific roles. This minimizes potential damage from accidents, errors, or unauthorized use. It restricts user privileges to the bare minimum necessary for their tasks.
How do you incorporate least privilege?
To incorporate the least privilege, begin by conducting a thorough privilege audit of user roles and access needs. Implement role-based access controls, regularly review user permissions, and promptly revoke any unnecessary or excessive privileged access. Employ tools for automated privilege management and continuous monitoring to enforce and update access policies.
What are the least privilege best practices?
Best practices for least privilege include regularly updating and reviewing user access rights, employing role-based access controls, using multi-factor authentication, and providing temporary elevated privileges when necessary. Continuously monitor and audit user activities, and promptly revoke access for departing employees.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security