Contents:
The Internet Control Message Protocol (ICMP) is a protocol built into the IP suite whose main function is to allow IP-based devices to communicate error messages and exchange information about network conditions. Network administrators mainly use ICMP for network traffic analysis and troubleshooting, but it can be exploited by threat actors too, as ICMP has the ability to both solve and cause network issues.
In this article, we’ll have a closer look at how Internet Control Message Protocol works, what are the most common cyber attacks that exploit ICMP, and discuss the role it plays in overall cybersecurity strategies. So let’s get started!
How Does ICMP Work?
The Internet Control Message Protocol (ICMP) works alongside the Internet Protocol (IP) as its companion. In fact, it makes up for its shortcomings such as its lack of error control and lack of messaging mechanisms.
When an IP packet encounters an error or needs to send a message to another device, it generates an ICMP message. The ICMP message is encapsulated within an IP packet and sent to the destination device. The destination device receives the IP packet, decapsulates the ICMP message, and processes it.
ICMP Message Examples
There are several types of ICMP messages serving different purposes, but the most common types are:
- Echo Request/Reply: These messages are commonly referred to as “pings”. Pings are usually used to test connectivity between devices. When a device sends an echo request, the recipient device responds with an echo reply message if it is reachable.
- Destination Unreachable: This message is sent by a device to report that it was unable to deliver a packet to its intended destination. This may occur if the destination device is unreachable, or if the packet was blocked by a firewall or other security measure.
- Time Exceeded: This message is sent by a device to report that a packet was discarded because it exceeded its allotted time to live (TTL). This may occur if a packet is routed in a loop, or if it takes too long to reach its destination.
- Redirect: This message is sent by a router to inform a device that it should send its packets to a different router in order to reach a particular destination.
- Router Advertisement/Discovery: These messages are used by devices to discover and configure the network topology. Router Advertisement messages are sent by routers to advertise their presence, while Router Discovery messages are sent by devices to discover routers on the network.
However, the most used, especially by network admins to troubleshoot network connectivity issues are ping and traceroute. Ping tests connectivity by sending and receiving ICMP messages, while traceroute traces the path of packets by sending ICMP messages with gradually increasing Time-to-Live values and tracking the Time Exceeded messages received from routers.
What Layer Is ICMP on?
In the OSI seven-layer model, the Internet Control Message Protocol (ICMP) is a third layer (network layer) protocol. In the TCP/IP four-layer model, ICMP is on layer 2 (internet/network layer).
ICMP in IPV4 and IPV6
ICMP serves diagnostic and error reporting purposes in both IPv4 and IPv6 networks. However, ICMP in IPv6 has been enhanced to support new features, such as Neighbor Discovery messages, which are used for tasks like address resolution and router discovery.
Is Internet Control Message Protocol Secure?
The Internet Control Message Protocol (ICMP) is generally regarded as safe because it is required for the proper functioning of IP-based networks. However, as I was mentioning at the beginning of this article, ICMP has the ability to both solve and cause network issues.
As a result, ICMP can be exploited by attackers to launch a variety of attacks, including DDoS (Distributed Denial of Service) attacks, that can overwhelm the target device’s network interface, consuming bandwidth and resources and causing the device to become unresponsive to legitimate traffic.
Here are the most common ICMP attacks:
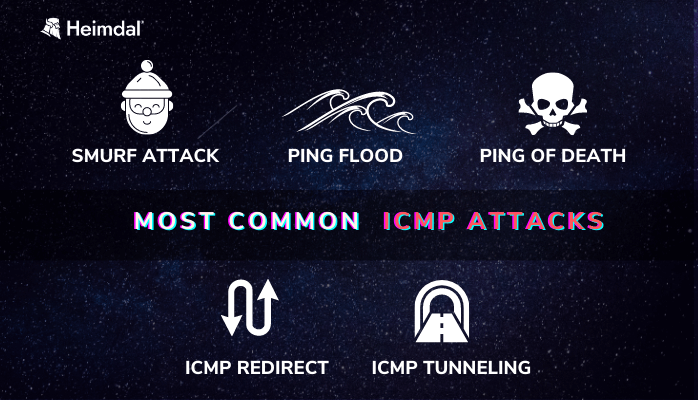
Ping Flood
The Ping Flood is a DDoS attack that involves flooding a network with a large number of ICMP Echo Request messages (pings), overwhelming the target device. Because each packet involves processing and a response, the device’s resources are depleted, preventing legitimate users from accessing it.
Ping of Death
A ping of death (PoD) attack is a type of DoS attack in which an attacker sends an ICMP Echo Request message (ping) that is larger than the maximum size allowed by the target device, causing it to crash or freeze up. When traveling toward its destination, the data packet is fragmented but is later pieced back together. At the receiver’s end, a buffer overflow causes the device to fail.
Smurf Attack
In a smurf attack, the attacker takes advantage of the fact that ICMP Echo Requests (ping) are typically broadcast to all hosts on a network. By spoofing the source address of the Echo Request, an attacker can cause all hosts on the network to reply, resulting in a flood of traffic that can overwhelm the target system.
ICMP Redirect Attack
This attack involves sending a spoofed ICMP Redirect message to a target device, causing it to send its traffic to a different gateway, which could be controlled by the attacker. This could result in a man-in-the-middle (MitM) attack, as it allows them to intercept and read any traffic passing through their system, including sensitive data such as passwords and financial information.
ICMP Tunneling
This is more of a technique that involves using ICMP messages to tunnel other types of traffic through a network, bypassing security controls.
ICMP tunneling can be used for both legitimate purposes, such as to bypass network restrictions in countries with censorship or monitoring, or for malicious purposes, such as to exfiltrate sensitive data or to launch attacks that are otherwise blocked by network security measures.
How to Protect Networks Against ICMP Attacks?
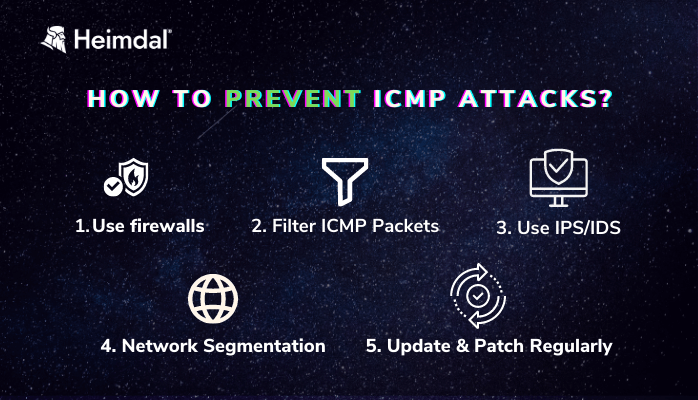
As we’ve established above, ICMP can be an attack vector for a network, which is why network administrators should put in place mitigation measures that can help improve the security of ICMP. Here’s a list of measures that we recommend:
- ICMP Filtering: By using a firewall or other network security device, network administrators can filter and block certain types of ICMP messages, such as Echo Request messages, to reduce the risk of ICMP-based attacks.
- Packet Filtering: By filtering out ICMP packets with suspicious or invalid data, such as packets with unusually large or small payloads, network administrators can reduce the risk of attacks such as Ping of Death.
- Intrusion Detection and Prevention Systems (IDS/IPS): IDS/IPS systems can detect and prevent ICMP attacks by analyzing network traffic for suspicious patterns and blocking traffic that matches known attack signatures.
- Network Segmentation: By segmenting networks into smaller, isolated subnets, network administrators can limit the impact of ICMP attacks by containing the attack within a single subnet.
- Regular Updates and Patching: By regularly updating and patching your systems, network administrators can ensure that known vulnerabilities and exploits are addressed, reducing the risk of attacks that exploit these vulnerabilities.
How Can Heimdal® Help?
To some degree, the measures above can help prevent ICMP attacks, but no single solution is foolproof. The best approach is to implement a multi-layered cybersecurity strategy that combines various solutions to provide comprehensive protection against a wide range of threats.
For example, although ICMP doesn’t use DNS, it depends on the DNS resolution. When the command is issued, the DNS entry is resolved into an IP address, and the ICMP operates with the IP address.
This means that using a solution that provides DNS traffic filtering might prevent ICMP attacks that use the domain name system to initiate or facilitate the attack. A DNS traffic filtering solution can identify and block requests from known malicious sources that may be used to launch the attack.
You can always try Threat Prevention, our award-winning traffic-filtering solution that is designed to actively monitor the entire network for any signs of malware entry from malicious infrastructures and restricts access to compromised domains by scanning user traffic in real time.
Threat Prevention – Endpoint is the ideal solution for securing your endpoints against DNS attacks by combining cutting-edge machine learning technology with a powerful DNS filtering module that has a 96% success rate in predicting threats.

Heimdal® DNS Security Solution
- Machine learning powered scans for all incoming online traffic;
- Stops data breaches before sensitive info can be exposed to the outside;
- Advanced DNS, HTTP and HTTPS filtering for all your endpoints;
- Protection against data leakage, APTs, ransomware and exploits;
Wrapping Up
ICMP is an important protocol that helps network administrators troubleshoot and monitor their networks. It has a variety of uses, such as ping, traceroute, and message-based communication between hosts.
And while ICMP can be very useful in networking, it can also be an attack vector if left unmonitored or misconfigured. This is why it’s important to take all the necessary precautions and put in place a strong, multi-layered security strategy, that will make all the difference when your network will face ICMP attacks. So, don’t wait too long and gear up!
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security