Contents:
In today’s technological world, we’re talking about millions of users communicating with different devices in different languages. That also includes various ways in which they transmit data along with the software they implement. Therefore, when discussing what is protocol and its types in networking, we need to point out that communicating worldwide would not be possible if there were no fixed ‘standards’ to govern the way users communicate for data as well as the way our devices treat that data.
What Is Protocol and Its Types in Networking?
According to the Florida Center for Instructional Technology, protocol is defined as a set of rules that govern the communications between computers on a network.
EDUCBA adds that network protocols are formalized requirements and plans consisting of rules, procedures, and types that describe communication among a couple of devices across the network.
In networking, protocol can be described as an approach to rules that allows entities of a communication program to transfer information through any type of variety of physical medium. The protocol “identifies the rules, syntax, semantics, and synchronization of communication and feasible error managing methods”.
Types of Networking Protocols
For two computers to communicate with each other, they must be speaking the same language. Different types of network protocols and standards are required to ensure that a computer (regardless of its OS, network card, or application used) can communicate with another one located in the next room or halfway around the world.
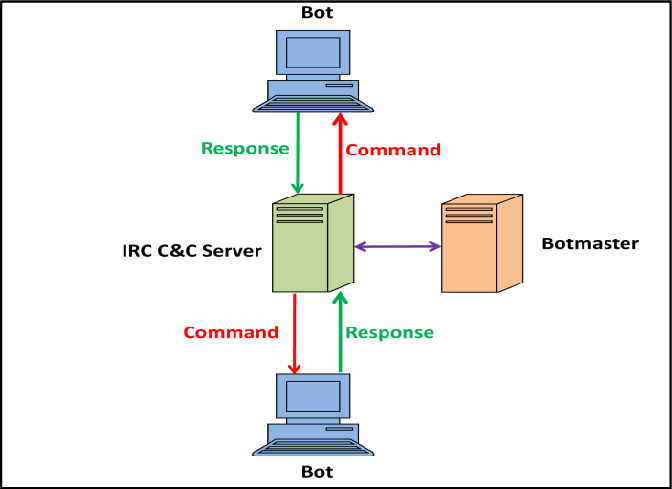
There are seven layers of networking protocols defined by the OSI (Open Systems Interconnection) Reference Model. The complexity of these layers is beyond the scope of this article, nevertheless, they were simplified below into four layers to help identify some of the protocols you should be familiar with.
Image Source: Florida Center for Instructional Technology
Below, I will discuss the different types of networking protocols.
Network Communication Protocols
#1. HTTP and HTTPS
Often referred to as the protocol of the Internet, HTTP/HTTPS stands for Hypertext Transfer Protocol and Hypertext Transfer Protocol (secure) respectively.
Image Source: EDUCBA
The majority of application-layer protocols employ this model, using one device on the client’s network; the other device on the network is the server.
In the case of HTTP, Client-server principles allow a client system for establishing a connection with the server machine for making a request. The server acknowledges the request initiated by the client and responds accordingly.
While HTTP is used for transferring data between the client browser (request) and the web server (response) in the hypertext format, in the case of HTTPS the transferring of data is done in an encrypted format. Therefore, we can say that HTTPS thwarts hackers from the interpretation or modification of data throughout the transfer of packets.
#2. FTP (File Transfer Protocol)
FTP allows users to transfer files (program files, multimedia files, text files, documents, etc) from one machine to another.
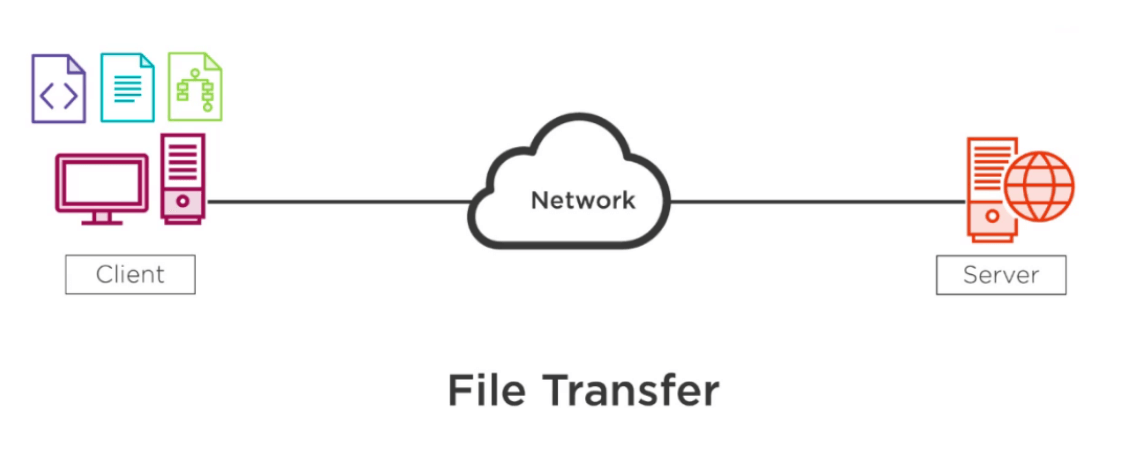
Image Source: EDUCBA
#3. TCP (Transmission Control Protocol)
TCP is a popular communication protocol that separates data into packets that can be distributed across a network. Afterward, they can be sent by devices such as switches and routers to the designated targets.
#4. UDP (User Datagram Protocol)
Although UDP works in a similar way to TCP, the main difference between the two is that TCP ensures a connection is made between the application and server, but UDP does not. User Datagram Protocol is mainly implemented for creating loss-tolerating and low-latency linking between various apps.
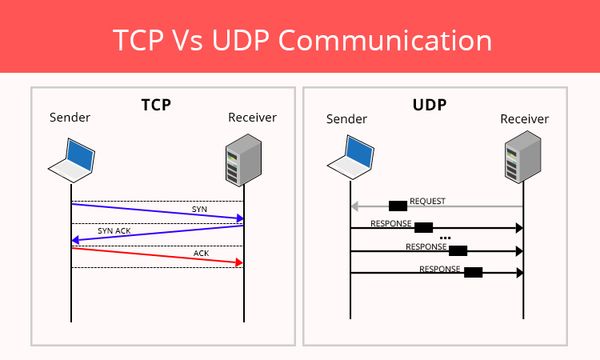
Image Source: CyberHoot
#5. IRC (Internet Relay Chat)
IRC is a text-based communication protocol that facilitates communication in the form of text. Although it supports private messages between two users, data transfer, and various server-side and client-side commands It is mainly used for group discussion in chat rooms called “channels”. This protocol works well on networks with numerous distributed machines.
Image Source: ResearchGate
Network Management Protocols
#1. SNMP (Simple Network Management Protocol)
SNMP is a standard protocol used to exchange network management information. It is part of the Transmission Control Protocol/Internet Protocol (TCP/IP) protocol suite. SNMP provides a tool for network administrators to manage network performance, find and solve network issues, and plan for network growth.
#2. ICMP (Internet Control Message Protocol)
ICMP is a network layer protocol mainly used to communicate with the source of a data packet about transmission issues. For example, if a datagram is not delivered, ICMP might report this back to the host with details to help discern where the transmission went wrong. It’s a protocol that believes in direct communication in the workplace.
Network Security Protocols
#1. SSL (Secure Socket Layer)
SSL is a network security protocol used for data protection on the transport layer, and it’s located between the transport and application layer of the ISO/OSI reference model providing security services to any application-based protocols, like HTTP, FTP, LDAP, POP3. The SSL protocol is used in any client/server environment, being able to provide a series of features for the parties involved in the communication process. Data transferred with SSL is encrypted to prevent it from being readable.
#2. SFTP (Secure File Transfer Protocol)
As its name suggests, this network security protocol is used to securely transfer files across a network. Data is encrypted and both the client and server are authenticated.
Final Thoughts on What Is Protocol and Its Types in Networking
Every time we use the Internet, we leverage network protocols. Though you may not know how network protocols work or how frequently you encounter them, they are necessary for browsing the Internet or digital communications in any capacity.
Forging strongly into parts of existence that nobody had predicted, digital networking is additionally strengthening us for the future. New protocols and requirements will come out, new applications can be developed, and our lives will probably be further transformed and improved.
I hope this guide on what is protocol and its types in networking has been helpful. Drop a line below if you have any comments, questions, or suggestions related to the topic – I look forward to hearing your opinion!










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security