Contents:
BianLian is a ransomware group that first appeared in July 2022, successfully infiltrating several high-profile organizations. It seems that recently, the ransomware group has shifted its focus from encrypting its victims’ files to only exfiltrating and extorting data found on compromised networks.
This operational development in BianLian was first reported by cybersecurity researchers, who saw signs of the threat group attempting to hone their extortion skills and put more pressure on the victims.
Recent BianLian Attacks
BianLian operators have maintained their initial access and lateral movement techniques while continuing to deploy a custom Go-based backdoor that grants them remote access on the compromised device, albeit a slightly improved version.
The threat actors post their victims in a masked form on their extortion site 48 hours after the breach, giving them roughly ten days to pay the ransom.
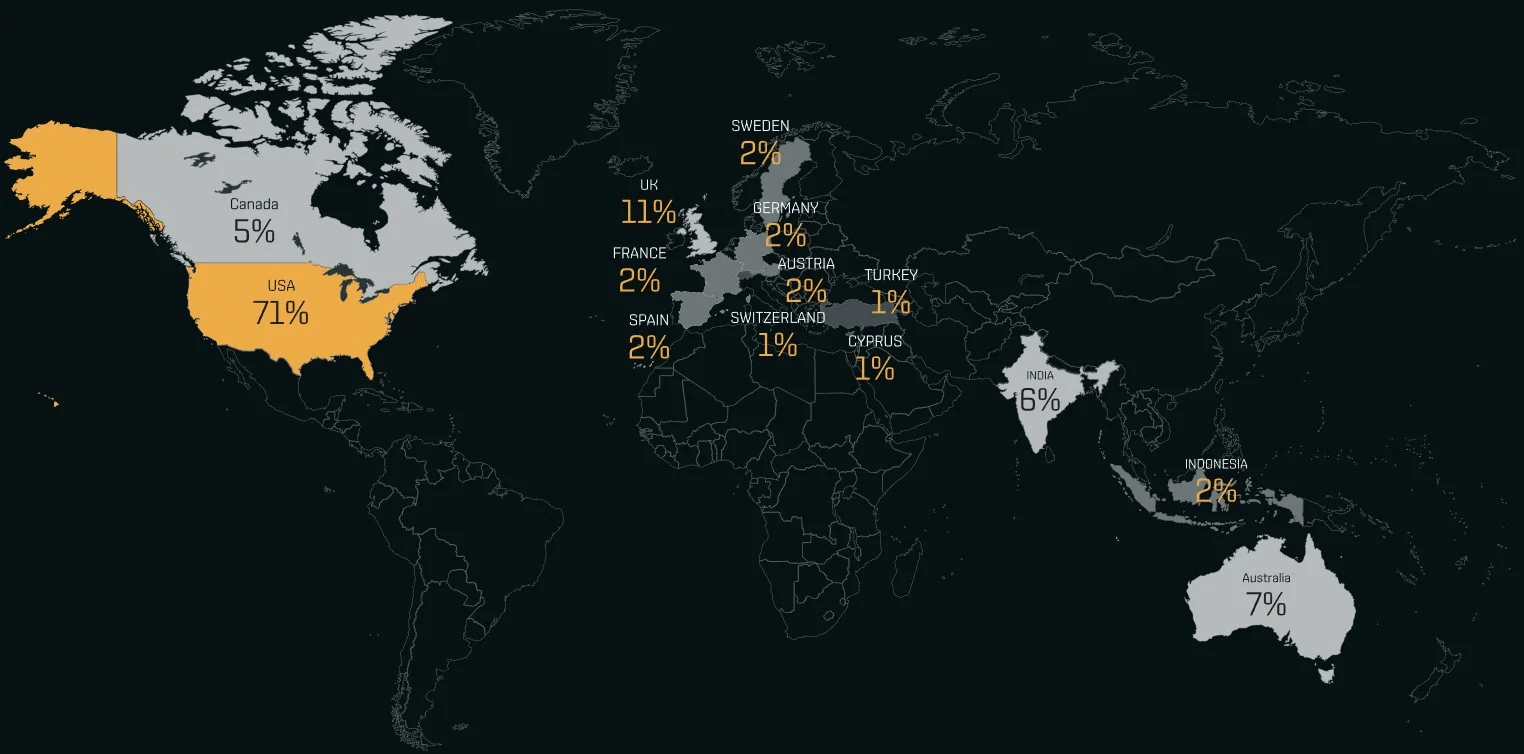
As of March 13, 2023, BianLian had 118 victim organizations listed on their extortion portal, with the vast majority (71%) based in the United States.
Extortion Without Encryption
Encrypting files, stealing data, and threatening to leak stolen files are all examples of “double extortion” tactics used by ransomware gangs to increase pressure on their victims.
However, due to the natural exchange between threat actors and victims, ransomware gangs discovered that, in many cases, sensitive data leaks provided an even stronger payment incentive for victims.
This gave rise to encryption-less ransomware operations like the late Babuk and SnapMC and extortion operations like RansomHouse, Donut, and Karakurt that claim not to use file encryption themselves (or at all).
Nonetheless, most ransomware groups continue to use encryption payloads in their attacks, as the business disruption caused by encrypting devices puts even more strain on many victims.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security