Contents:
As cyber attackers become more sophisticated, leveraging machine learning and other advanced techniques, the importance of robust XDR security solutions becomes paramount.
In this article you’ll discover the newfound power of XDR, and why is it crucial in today’s technology stack.
Key Points
- What is XDR?
- How XDR Works.
- Key Features of XDR.
- XDR Benefits.
- How to Implement an XDR Software?
- What is XDR?
- XDR vs. Other Security Tools.
- Heimdal XDR vs. EDR.
What is XDR?
The acronym standing for eXtended Detection and Response is not another security system, it’s a comprehensive security solution that monitors and addresses security incidents.
In essence, XDR is a cross-layered detection investigation and response tool. It gathers and correlates data from various security layers, including endpoints, emails, servers, clouds, applications, and networks.
This integration breaks down security silos, allowing for a more holistic approach to cybersecurity.
By utilizing XDR, security teams can detect, investigate, and respond to threats across multiple layers, moving beyond traditional endpoint protection.
This approach enhances cloud security, email security, and other facets, fortifying the organization’s defense and enhancing threat detection.
How XDR Works
XDR security solutions detect malicious threats by analyzing both internal and external traffic.
They use an integrated analytics engine and threat intelligence, which includes information on known attack strategies, sources, and tools.
This intelligence, combined with machine learning, can proactively identify potential attacks, including zero-day vulnerabilities, ensuring efficient threat detection and response.
A standout feature is its efficient graphical timeline, a tool for root cause analysis. It answers pivotal questions like:
- How did I get infected?
- Which was the entry point?
- What is the origin of the attack?
- Were there other parts involved?
- How did the threat spread throughout the system?
- Were other users exposed to the threat?
Key Features of XDR
Now that we’ve established what eXtended Detection and response is, let’s continue the discussion by seeing what it does.
Designed to improve an organization’s cybersecurity, it has several functions that you can add to your digital defense strategy.
Here are the main features of an XDR solution:
- Cyberattack detection and incident response
- Comprehensive security analysis
- Shared threat intelligence (internal and third-party)
- Automatic security alerts confirmation
- Complete data integration from various data sources, including cloud data
- Unified, user-friendly interface for ease of policy management
But what is XDR good for? What are the advantages it brings to your enterprise, should you choose to opt for this cybersecurity approach?
Enhanced endpoint detection and response capabilities, improved operational productivity, and reduced costs/ resource usage.
Enhanced Endpoint Detection and Response (EDR) Capabilities
As the acronym suggests, XDR is one step above traditional endpoint detection and response.
It beneficially impacts four areas of EDR that are specific to your company’s Security Operations Center (SOC): detection, threat hunting, investigation, and recommendation.
Detection
Through endpoint telemetry data and an AI-driven list of cybersecurity threats to compare traffic against, XDR has the aptitude to identify not only more threats but advanced ones as well.
Threat Hunting
An XDR solution does more than just detect known threats.
It actively hunts and analyzes suspicious online behaviors to discover previously unknown malicious domains and cyberattacks.
Investigation
Pairing XDR with a dedicated information security team within your company creates a strong human-machine correlation that will result in expert incident investigations and response.
Recommendation
Finally, the data gathered by XDR can also provide your IT team with proactive recommendations that will greatly minimize the risks of future attacks.
XDR Benefits
XDR provides security incident detection, improving operational productivity and reducing costs.
Its AI-driven approach offers a proactive stance against cyberattacks, ensuring that security teams are always a step ahead. Here are some of the main benefits of XDR:
Improved Operational Productivity
One of the main points of interest presented by eXteded Detection and Response is represented by the fact that it unites multiple solutions under one accessible interface.
This means that your SOC will be able to handle every step in the cybersecurity process in one place, which is advantageous for the overall productivity index of the enterprise.
Not only will this benefit your information security team, but other employees working on the company endpoints as well.
Reduced Costs and Resource Usage
Another plus of unifying all the moving parts of your digital defense in one dashboard is the reduction in operational costs and resource usage.
Not only will you save your employees a lot of time, but you will also save the company money as well.
What is more, XDR is usually lighter on the system than separate solutions that operate out of independent platforms, so there’s that as well.
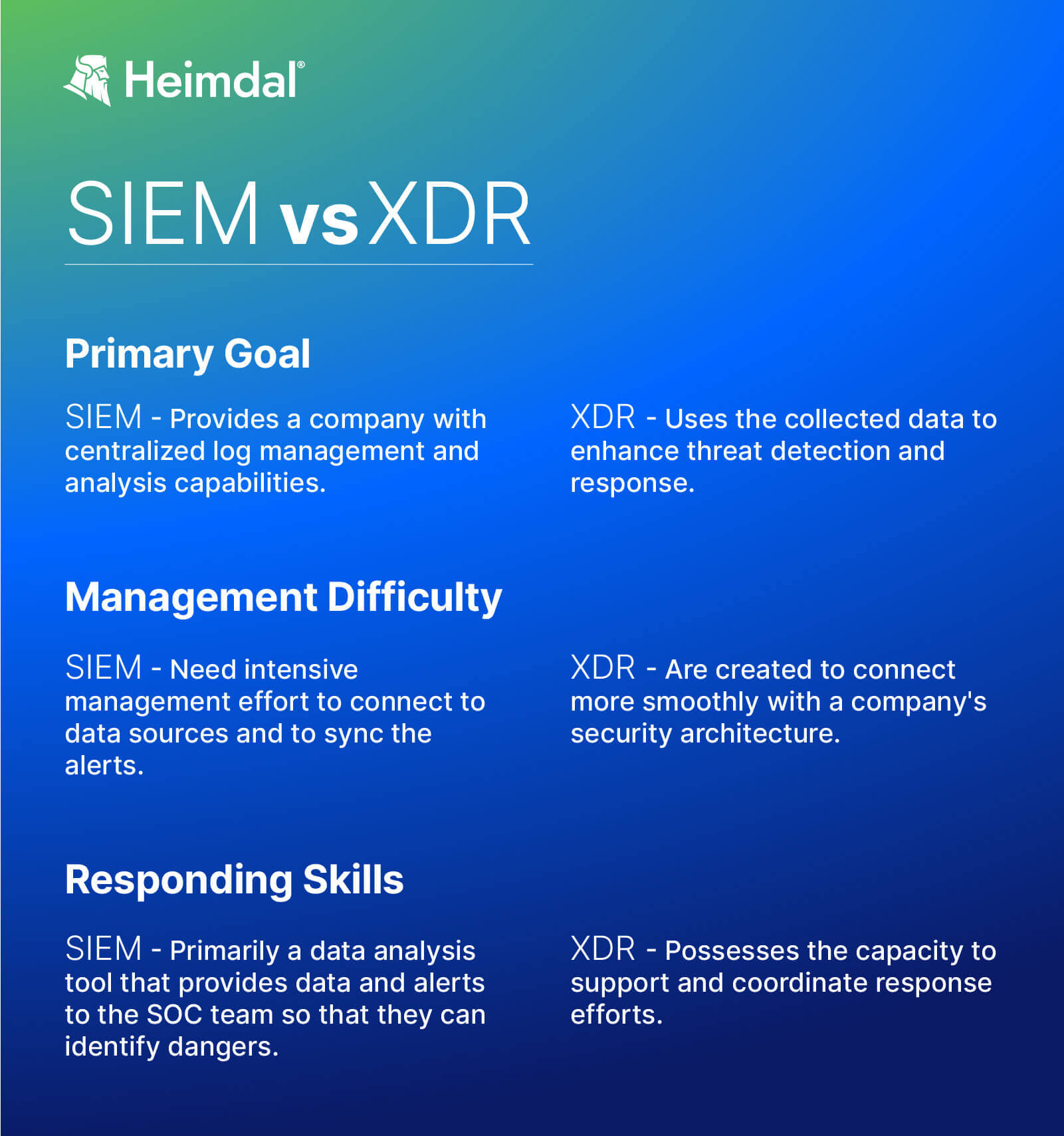
Boosting the SIEM
XDR integrates seamlessly with Security Information and Event Management (SIEM) systems, enhancing their capabilities.
While SIEMs consolidate vast amounts of security information, they can sometimes overwhelm security teams with numerous alerts.
XDR, with its data lake integration, refines this data, leading to fewer but more actionable alerts.
How to Implement an XDR Software?
Implementing XDR software is a strategic move to enhance an organization’s cybersecurity posture by combining various security investments into a cohesive detection investigation and response mechanism.
This includes integrating with managed detection and response services to ensure a comprehensive security approach.
Alternatively, businesses can opt for Managed Extended Detection and Response (MXDR), a service that provides the benefits of XDR without the need for in-house management, ensuring continuous protection through expert oversight.
XDR vs. Other Security Tools
XDR stands out from other security tools like SIEM and EDR solutions by offering a more comprehensive approach.
It’s not just about detection, it also includes incident response and network traffic analysis.
The future of cybersecurity lies in solutions like EPDR (Endpoint Prevention, Detection, and Response), which takes a proactive approach, unlike traditional EDR.
XDR vs. SIEM
XDR enhances the detection and response capabilities offered by SIEM.
Indeed, SIEM can seamlessly integrate with XDR, assisting in collecting, organizing, and analyzing vast data volumes for SOC analysts.
XDR vs. EDR
Before concluding this article, there is one more important question I want to raise: What is XDR’s value in the context of today’s cybersecurity landscape?
Is it the optimal solution in 2023 and beyond? The short answer here is (unfortunately) NO. Let’s see why.
Although the query of what is XDR can be easily answered by saying it is the more advanced version of traditional EDR, that doesn’t mean it’s the most cutting-edge one out there.
The current golden standard is EPDR, which stands for Endpoint Prevention, Detection, and Response.
EPDR refers to a new generation of EDR software, enhanced with threat prevention capabilities.
As a result, EPDR takes a proactive approach to cyberattacks, whereas normal EDR has a reactive one.
EPDR is the industry’s natural response to the technological advancements taking place behind enemy lines.
As hackers become more cunning and the inner workings of cyberattacks progress, so must we.
Prevention is more efficient than detection and response these days, and that’s exactly what EPDR brings new to the table.
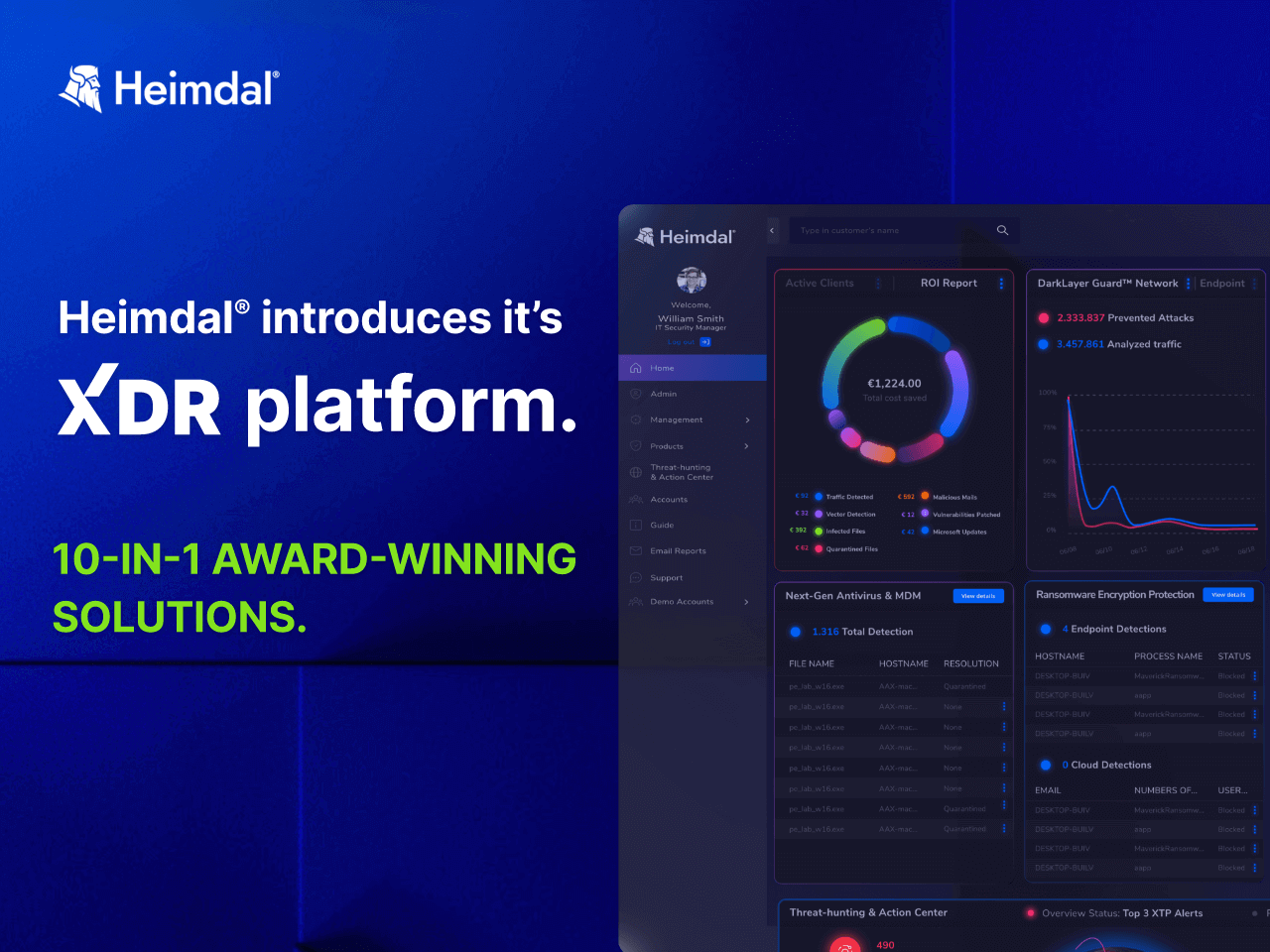
Heimdal XDR vs. EDR
From hunter (EDR) to overseer (XDR), Heimdal covers all attack venues regardless of surface, approach, or severity.
EDR and XDR are two sides of the same coin – while the former acts as a central hub for security intelligence and unlocks an entire arsenal of threat-hunting and attack mitigation tools, the latter will constantly monitor your communicational infrastructure, servers, endpoints, and attached devices for signs pointing to an impending cyberattack.
With EDR you can hunt, prevent, detect, and respond to threats when and where they happen.
XDR retains the overseer role – gathers data from across your environment to predict cyberattacks, monitors all devices connected to your networks, and plots courses of action based on factual, real-time information.
If you’re willing to find out more about how to select the perfect XDR solution for your business and what are the key elements that any good XDR software on the market must have, feel free to check Help Net Security’s XDR report here.
The paper includes a directory of notable players in the XDR market segment, including Heimdal’s CEO, Morten Kjærsgaard.

- End-to-end consolidated cybersecurity;
- Complete visibility across your entire IT infrastructure;
- Faster and more accurate threat detection and response;
- Efficient one-click automated and assisted actioning
Frequently Asked Questions (FAQs)
What is XDR and how does it differ from traditional EDR solutions?
XDR (Extended Detection and Response) integrates threat data from endpoints, networks, servers, and emails into a single system.
Unlike EDR, which focuses only on endpoints, XDR provides a broader view, enhancing threat detection and response across the entire IT environment.
How does XDR enhance threat hunting and incident response capabilities?
XDR enhances threat hunting and incident response by combining data from various sources into a unified system.
Advanced analytics and machine learning detect complex threats, allowing faster and more accurate investigations and automated responses, reducing the time to identify and mitigate threats.
What role does machine learning play in XDR solutions?
Machine learning in XDR analyzes large datasets to find patterns and anomalies that indicate threats.
It continuously learns from new data to adapt to evolving threats, improving detection accuracy and reducing false positives through cross-layer event correlation.
How does XDR integrate with existing security infrastructure?
XDR integrates with existing security tools via APIs and standardized protocols, enabling data sharing with SIEM systems, firewalls, and endpoint protection platforms.
This integration centralizes visibility and control, leveraging current investments while enhancing threat detection and response.
Wrapping Up…
In a world where enterprise security is continually challenged by evolving security threats, it’s crucial to stay updated with the best practices in cybersecurity.
XDR, with its comprehensive approach, offers organizations the tools they need to combat advanced threats effectively.
Whether on-premises or in the cloud, integrating XDR into your security services ensures that your attack surface remains minimal and well-protected.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security










