Contents:
I spoke with Dragoș Roșioru, a seasoned MXDR expert, about incident response best practices and challenges.
Get an in-depth understanding of the do’s and don’ts in incident response as Dragoș explains how to avoid the most common mistakes Security Officers make.
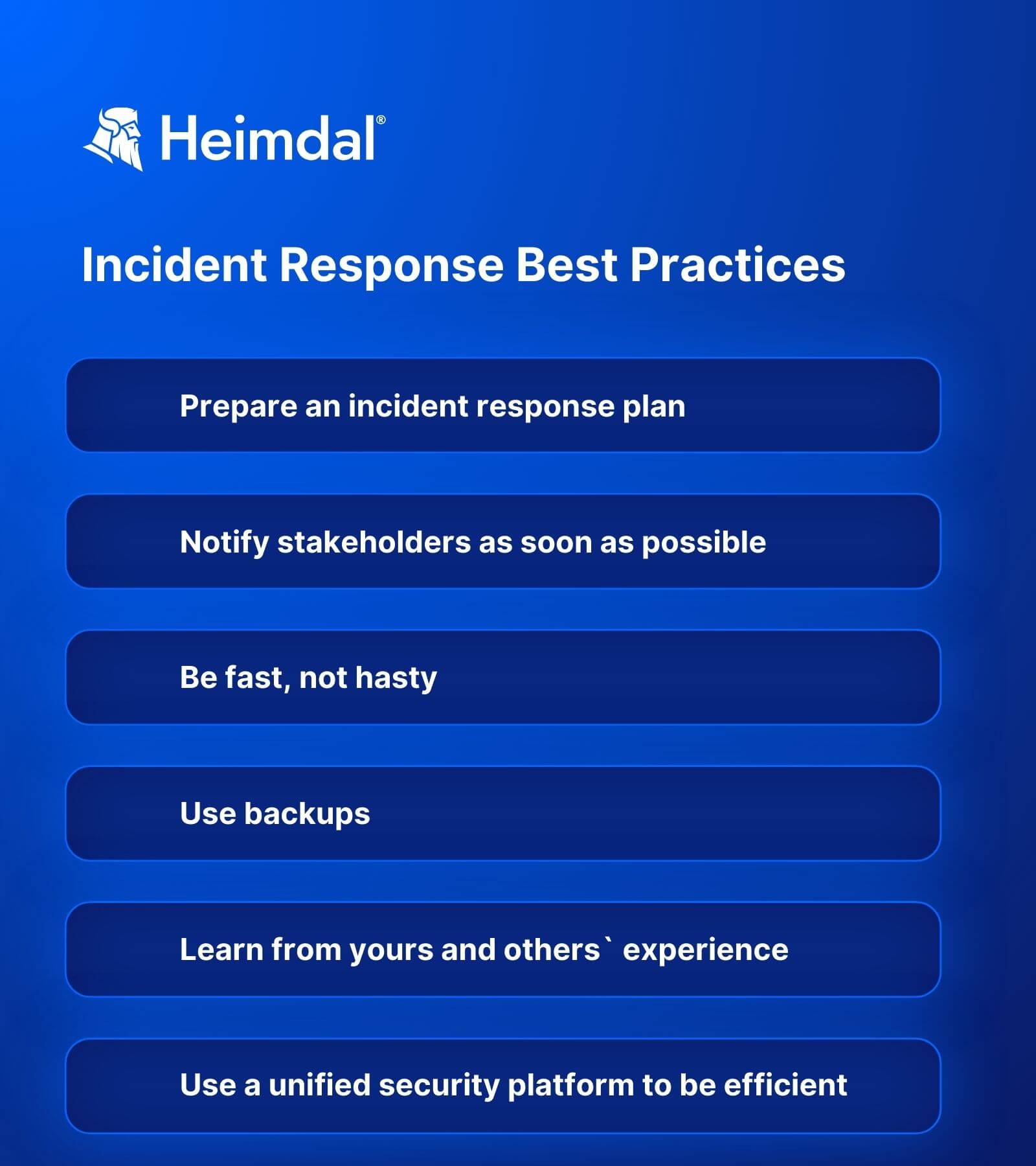
Dragoș’s has provided you with his incident response best practices checklist below too.
What are the first things a security team should do after detecting an incident?
The first things to do are:
- assess the severity and scope of the attack
- contain the incident
- start gathering evidence
Follow the steps in your Incident Response Plan. If you don’t have one, make creating it a priority. Incident response planning is critical in protecting your company’s assets.
Notifying the key stakeholders should also be a priority and you should include this step in the incident response plan. By key stakeholders, I mean the IT department, the internal or external security team, other departments that could be affected, etc.
How should an IT department prepare for an incident?
Learn from experience. Ask yourself:
- what went well
- what went wrong
- why was that
- what were the tools and policies that would have helped?
If you’re just starting your career, learn from others. Analyze case studies of companies that suffered a security incident.
Other than that, you need to cover several cautionary measures:
- Create a backup database to avoid data loss.
- Create a backup communication channel in case the main one is compromised during the incident.
- Implement strong authentication and access control measures. For example, use multi-factor authentication.
- Educate employees about the risks. Don’t lose them in technical details. Stick to the essentials and make it easy for everybody to understand.
- Continuously keep assets up to date. Automated patch management solutions do this in a few clicks.
- If you have an internal Security Operation Center (SOC), constantly update them with the latest threats. If it happened once, it would happen again.
To summarize it, take a look at the incident response best practices checklist I share below.
What could go wrong when trying to isolate the threat?
If you don’t do it right, you could damage normal operations or overlook a fake threat. Also, there’s a chance the threat could spread more in the network.
Follow my or build your own incident response best practices checklist. It will help you see clearer and keep things on the right track.
How can you isolate an incident without impacting the company’s productivity?
Your goal is to limit the impact. It’s almost impossible to leave a security incident unscathed.
However, there are some caution measures in incident response planning that will help keep things under control:
- Have good heuristic settings in place.
They examine the impacted code and search for virus specific functionalities to detect unknown threats.
The aggressiveness of the detection varies depending on the heuristic detection level you choose:
- low
- medium
- high
As the level escalates, more detection rules activate, so you need to adjust the sensitivity of the detection process.
Setting the heuristic level to high may lead to an increased incidence of false positives. This is often the preferred choice for environments where security is paramount. It offers a more rigorous scanning protocol.
- Have a backup that will prevent you from having to repeat work.
How fast do you need to report a security incident?
The reporting of a security incident to the stakeholders – IT crew, Management, Communication and PR, etc. should be immediate. Quick action is crucial in mitigating risks and limiting potential damage.
The sooner you report an incident, the faster you can move on to initiating a response and reduce the window of opportunity for the threat to escalate.
How does Heimdal cover this?
Heimdal provides an effective isolation solution, complemented by our Managed XDR team’s ability to adjust detection heuristics.
Managed Extended Detection and Response (MXDR) is a service that offers companies access to advanced detection and response security tools without burdening their budgets. You get the best tools on the market along with the expertise of a highly skilled team.
The Heimdal MXDR suite integrates various modules and solutions, streamlining communication and issue resolution. So, it’s faster and more efficient than any mix of random cybersecurity tools.
A key aspect of our service is the 24/7 coverage. Prompt response to attacks is crucial.
Why?
Because attackers conduct reconnaissance and often strike during non-business hours.
I see many companies relying on siloed teams for network security, endpoint protection, and patching. This can complicate things.
Faulty communication or the fact that not all cybersecurity tools can work well together leads to security gaps.
To deal with this, move to a unified security approach. Platforms that integrate all necessary tools, like Heimdal MXDR, make sure everyone is on the same page and security is more effective.
Does Heimdal MXDR help people report faster?
Absolutely. Our product features live alerting and detection for high-risk triggers. So, as soon as a potential threat is identified, both the customer and our team are notified in real-time or near real-time.
This immediate awareness allows for quicker decision-making and response. It reduces the time between the detection of a threat and the reporting and addressing of the incident.
It’s not just about speed but also about enhancing the efficiency and effectiveness of the incident response.
How long does it take to get the necessary data for a security incident report?
The time required to gather data for a security incident report varies. Some of the influencing factors are:
- the nature of the attack,
- the existing security measures of the company,
- whether they utilize or not a log engine, like our eXtended Threat Protection.
Typically, getting everything together can range from a few hours to several days. This variation is due to processes like patching vulnerabilities, cryptographic analysis, and decryption.
All these processes can extend the time needed in some instances.
What are the Don’ts in incident response?
Do not delay
Immediate action is crucial. Even if the threat appears contained, it may not be fully neutralized. Delays can allow the threat to escalate or spread, potentially leading to more damage.
Don’t keep stakeholders in the dark
Communicate with all relevant parties, including management, IT staff, and potentially affected users. This way you’ll avoid confusion and aggravation. Timely and clear communication is key to a coordinated response and maintaining trust.
Never cover up the incident
Be as transparent as possible. In many countries, there are legal obligations to report certain types of incidents in a certain amount of time.
Avoid making rash decisions
You should move fast, but don’t take hasty decisions. Acting without analyzing can lead to more harm.
Do not overlook documentation
Detailed recording of the incident’s timeline, the actions you took, and evidence gathered are crucial for post-incident analysis and potential legal proceedings.
Resist the impulse to modify or delete data
In the heat of the moment, you might think that changing or deleting data will mitigate the threat. However, this can destroy vital evidence that could help understand the attack. Nonetheless, it can hinder recovery efforts.
What are the most common mispractices that aggravate incidents?
Poor communication
If you don’t communicate promptly and clearly about an incident, you leave room for confusion, panic, or a delayed response.
Delay in response
Procrastinating or underestimating the urgency of an incident just gives threat actors time to escalate.
Incomplete understanding of the incident
Jumping to conclusions and acting without a thorough investigation can lead to incorrect responses.
Ignoring or bypassing protocols
Skipping steps in the incident response plan or ignoring best practices can lead to critical oversight.
Failing to learn from the incident
Some cyber incident response teams overlook reviewing the incident post-event or ignore its findings – a recipe for mistakes.
What incident response myths have you stumbled upon in your career?
Loads. I’ll just name the most common:
Small businesses don’t need an incident response plan
Being a 200-employee business doesn’t mean you can’t be a target. The security team will still have to put in a lot of effort to contain the incident and repair the damage.
In small teams, the pressure will be higher.
A strong security strategy is enough
No defense is impenetrable. Threats keep evolving, and attackers are producing new malware every day.
More tools mean better security
Effective security and incident response are not about more tools. Having the right tools, properly integrated and managed, will save the day.
If you liked this article, follow us on LinkedIn, Reddit, X, Facebook, and Youtube.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security







