Contents:
Businesses need to adapt and find the best approach to protect their networks and data from potential attacks. That’s where threat hunting and incident response come into play.
In this article, we’ll explore the similarities and differences between these two approaches and hopefully help you determine which one is best suited for your organization’s needs.
What Is Cyber Threat Hunting?
Cyber threat hunting is a proactive approach to cybersecurity that involves searching for potential threats and vulnerabilities before they can cause harm.
Threat hunting usually requires a high level of expertise, specialized tools, and a thorough understanding of the system and network architecture.
An important part of the security operation center services, cyber threat hunting spots the early indicators of a potential cyberattack and can uncover sophisticated malware that uses advanced evasion techniques.
In a way, threat hunting is like detective work, where you have to assess the existing infrastructure and anticipate potential weaknesses that could be exploited by attackers.
Threat hunting is valuable to businesses because detecting attacks in real time and before they cause any damage can significantly reduce the risk of costly breaches and disruptions.
They can also better protect sensitive data, meet compliance standards, and reduce the risk of regulatory penalties.
If you want to learn more about threat hunting, my colleague Vladimir wrote an extensive piece about it: Cyber Threat Hunting Techniques & Methodologies.
What Is Incident Response?
Unlike threat hunting, which is proactive, incident response (IR) is a reactive process that occurs after a security breach has been detected. The objective of incident response is to mitigate the damage caused by security incidents and return the affected systems to their normal working state as quickly as possible.
IR begins when a security incident has been detected. This can happen through various methods, such as IDS/IPS alerts, user reports, or suspicious behavior. Once detected, the incident response team investigates the incident, determines its scope and severity, and proceeds to contain it to prevent further damage. In a way, incident response is like a fire alarm, and IR experts are the firefighters.
Incident response typically involves a series of coordinated steps, including containment, identification, investigation, remediation, and recovery. These steps are detailed in the incident response plan, along with all of the incident response team’s procedures and responsibilities.
Cyber incidents are more than just technical issues; they also present business challenges. The sooner they are dealt with, the less damage they will cause, which is why more and more businesses recognize the importance of having a cybersecurity incident response plan.
If you want to learn more about Incident Response, make sure you check out this article: Incident Response – Everything You Need to Know.
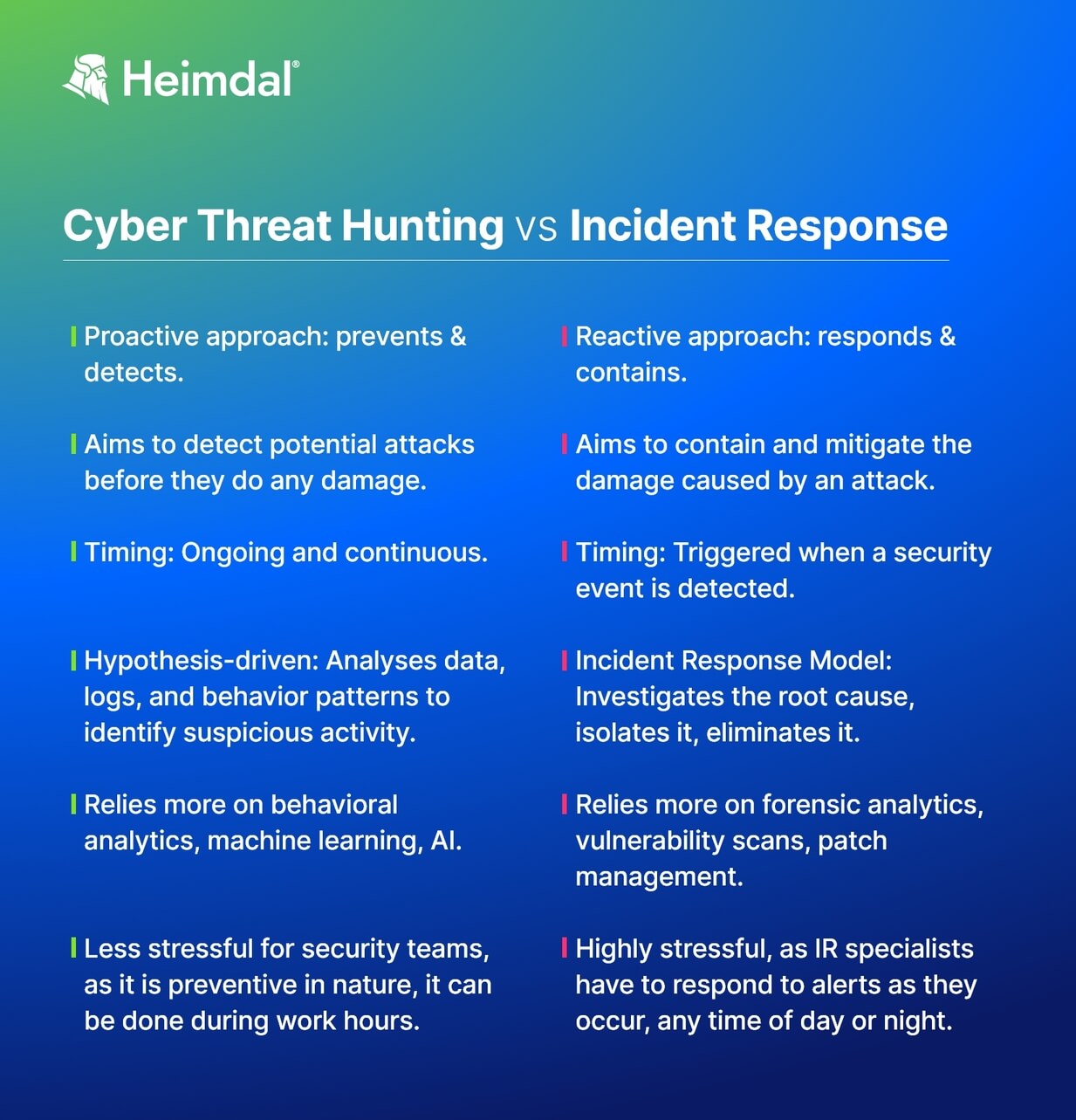
Threat Hunting vs Incident Response: Differences
Threat hunting and incident response are two different security approaches that can be used to protect a system from cyber threats. But how do they differ?
Proactive vs Reactive
Threat hunting is proactive, while incident response is reactive. In threat hunting, analysts actively search for potential threats within the network before they result in an actual attack. Incident response, on the other hand, aims to contain and mitigate the damage caused by an active cyber-attack.
Ongoing vs Triggered
In terms of timing, threat hunting is an ongoing and continuous process, whereas incident response is typically triggered when a security event is detected.
Marathon vs Sprint
In terms of scope, threat hunting is the marathon, while incident response is the sprint.
Threat hunting has a broader scope as it involves a comprehensive and systematic search for potential threats across an entire system or network. It aims to identify both known and unknown threats.
Incident response, in contrast, has a narrower scope, focusing on containing and mitigating the effects of a specific security incident that has already taken place.
Hypothesis-driven vs Incident-driven
Threat hunting is hypothesis-driven, where threat hunters formulate hypotheses based on available data, threat intelligence and knowledge of attack techniques. They then conduct investigations and collect evidence to validate or disprove the hypotheses.
On the other hand, incident response is incident-driven, as it reacts to an actual security incident or breach that has been detected. Incident responders focus on understanding the incident’s scope, impact, and causes to effectively respond and mitigate.
Hidden Threats vs Threat Impact
Threat Hunting involves analyzing logs, network traffic, endpoint data, and other relevant information to detect hidden or advanced threats. Incident responders analyze incident data, logs, artifacts, and other evidence to understand the incident’s cause, impact, and extent.
Flexibility vs Immediate Reaction
In terms of time sensitivity, threat hunting allows for a more flexible timeline, enabling teams to conduct investigations and refine techniques over an extended period, which can be achieved during “normal” working hours.
In contrast, incident response demands swift action to contain and recover from a security incident, prioritizing immediate response to minimize impact. IR specialists have to respond to alerts as they occur, any time of day or night.
Threat Hunting vs Incident Response: Similarities
Despite their differences, threat hunting and incident response share several commonalities:
- Data Analysis. Both threat hunting and incident response rely on data analysis to identify potential threats and mitigate damage caused by incidents.
- Collaboration. Both threat hunting and incident response require collaboration among different teams in an organization, including IT, security, and management.
- Risk Assessment. Both processes require a risk assessment to prioritize potential threats and vulnerabilities.
- Threat Intelligence. Both processes rely on threat intelligence to develop their strategies. Threat intelligence involves collecting and analyzing data from different sources to understand the latest trends and methods attackers use.
How to Choose Between Threat Hunting and Incident Response?
When choosing between threat hunting and incident response, it’s essential to consider your organization’s specific needs and cybersecurity posture. Assessing your security infrastructure’s current state will help identify gaps that need addressing.
Analyze the size of your IT environment and the nature of the data you handle. If you operate in a high-risk industry or handle sensitive data, proactive threat hunting can provide added protection by identifying potential threats that traditional security controls may miss. Focusing on effective incident response could be more practical if your organization is smaller with limited resources.
Consider expertise available within your team. Threat hunting usually requires specialized skill sets; thus, investing in training existing personnel or hiring dedicated professionals might be necessary. Incident response can also benefit from experienced staff but leans more towards robust processes and tools.
Evaluate your budget constraints. While both approaches are valuable investments in security measures, allocating funds strategically based on priorities will ensure optimal results in strengthening cyber defense mechanisms for your business operations.
However, instead of choosing one approach over the other, organizations should aim to integrate both threat hunting and incident response into their cybersecurity strategy. Threat hunting aids in identifying potential threats that automated systems may miss, while incident response ensures a prompt and efficient response to security incidents.
Cyber Threat Hunting with Heimdal®
We made it our goal to empower security leaders, professionals, and providers at all levels to aptly balance threat-hunting, incident response, and advanced analytics with the help of a revolutionary solution, the Heimdal Threat-hunting and Action Center.
The Threat Hunting and Action Center is engineered to handle SOC, CSIRT, Incident Response, and malware analysis workloads. It enables security teams to visualize (threat telemetry, risk scoring, categorized events), hunt (threat hunting, investigation, and deep analysis), and act (remediation, action controls, and protection stats reporting) using the same dashboard.
TAC offers a comprehensive cybersecurity approach that enables customers to safeguard all attack surfaces, including infrastructure, applications, endpoints, IoT devices, cloud environments, and supply chains. Book a demo and test its features!

- Granular telemetry across endpoints and networks.
- Equipped with built-in hunting and action capabilities.
- Pre-computed risk scores, indicators & detailed attack analysis.
- A single pane of glass for intelligence, hunting, and response.
Wrap up
Both threat hunting and incident response are critical components of an effective cybersecurity strategy. Threat hunting is detective work, while incident response is more like police work.
Choosing between threat hunting and incident response depends on your organization’s needs and risk profile. A comprehensive cybersecurity plan should include both strategies to protect against modern cyber threats.
Using the best tools is also essential in both approaches to effectively detect, analyze, and respond to security threats, especially if all the data, intelligence, and hunting capabilities can be managed in a single console. For this, you can count on our revolutionary Threat Hunting and Action Center!
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and Youtube, for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








