Like with all cybersecurity products, endpoint detection and response sits inside a confusing Venn diagram of overlapping terms, concepts, and products. Some of these are designed to work alongside EDR as part of a layered defense. With other products, it’s more of an either/or.
So how do you know if you need an EDR product or something else? To make that decision, it helps to first understand the difference between EDR and its threat detection relatives.
1. EDR vs NDR:
Network detection and response (NDR) products are similar to EDRs, because they aim to monitor activity to detect and repel suspicious behavior.
However, they are much narrower in focus. Unlike EDRs, they only focus on network activity and traffic – rather than all endpoint-related behavior. Some EDR products (like Heimdal) also include network monitoring features, meaning an effective EDR should feature tools from both products under one license.
Find out more: NDR vs EDR: A Comparison Between the Two Cybersecurity Solutions
2. EDR vs EPP:
An endpoint protection platform (EPP) is similar to EDR, but with a slightly different focus: It mostly specializes in defending against known malware-based threats. Effectively, it acts as a perimeter around your IT environment, and can generally be deployed without your IT team having to monitor or supervise it.
EDR products, on the other hand, are generally broader in focus. Often, they include the same anti-malware protections as EPPs. But they also include tools to monitor behavior, and are much more effective at identifying unknown threats. EDRs require more active maintenance and can stop attacks from escalating, rather than just filtering out incoming threats. Again, an effective EDR or XDR product should include features of both, avoiding the need to duplicate licenses.
Find out more: EPP vs. EDR [How to Choose the Best Endpoint Protection Platform]
3. EDR vs XDR:
Extended detection and response (XDR) is essentially EDR+. It features the same functionality as EDRs, alongside a diverse range of additional cybersecurity tools. These can include network monitoring, privileged access management, SIEMs, email protection, vulnerability management, and more.
XDRs therefore aim to provide as wide a range of cybersecurity protections as possible under one license, avoiding the need for multiple, overlapping security solutions.
Find out more: XDR vs. EDR – A Comparison
4. EDR vs MDR:
Managed detection and response (MDR) is a managed service that’s offered by a cybersecurity provider, partner, or an MSSP – alongside the fundamental EDR product.
Generally, customers purchase an EDR license through the managed services provider, who then charges an additional rate for their own services. These can include active monitoring, threat response, vulnerability management, and more.
Find out more: Why Is MDR Better Than EDR: Enhancing Cybersecurity in the Modern World
5. EDR vs NGAV:
Next-generation antivirus (NGAV) is essentially the most modern evolution of anti-malware tools, which have been the bedrock of cybersecurity for decades. Unlike traditional tools, NGAV relies on advanced behavioral analysis to detect realtime threats. NGAV functionality is generally included in EDR and XDR products.
Find out more: EDR vs NGAV: Which Works Better for Your Organization?
6. EDR vs antivirus:
Antivirus is an umbrella term for all cybersecurity products that focus on viruses, ransomware, and malware more generally. This includes both traditional and next-generation antivirus tools. EDR or XDR products are generally the best way to get antivirus protections, since they’re included alongside a range of other tools.
Find out more: EDR vs. Antivirus: Choose the Best Security Solution for Your Endpoints
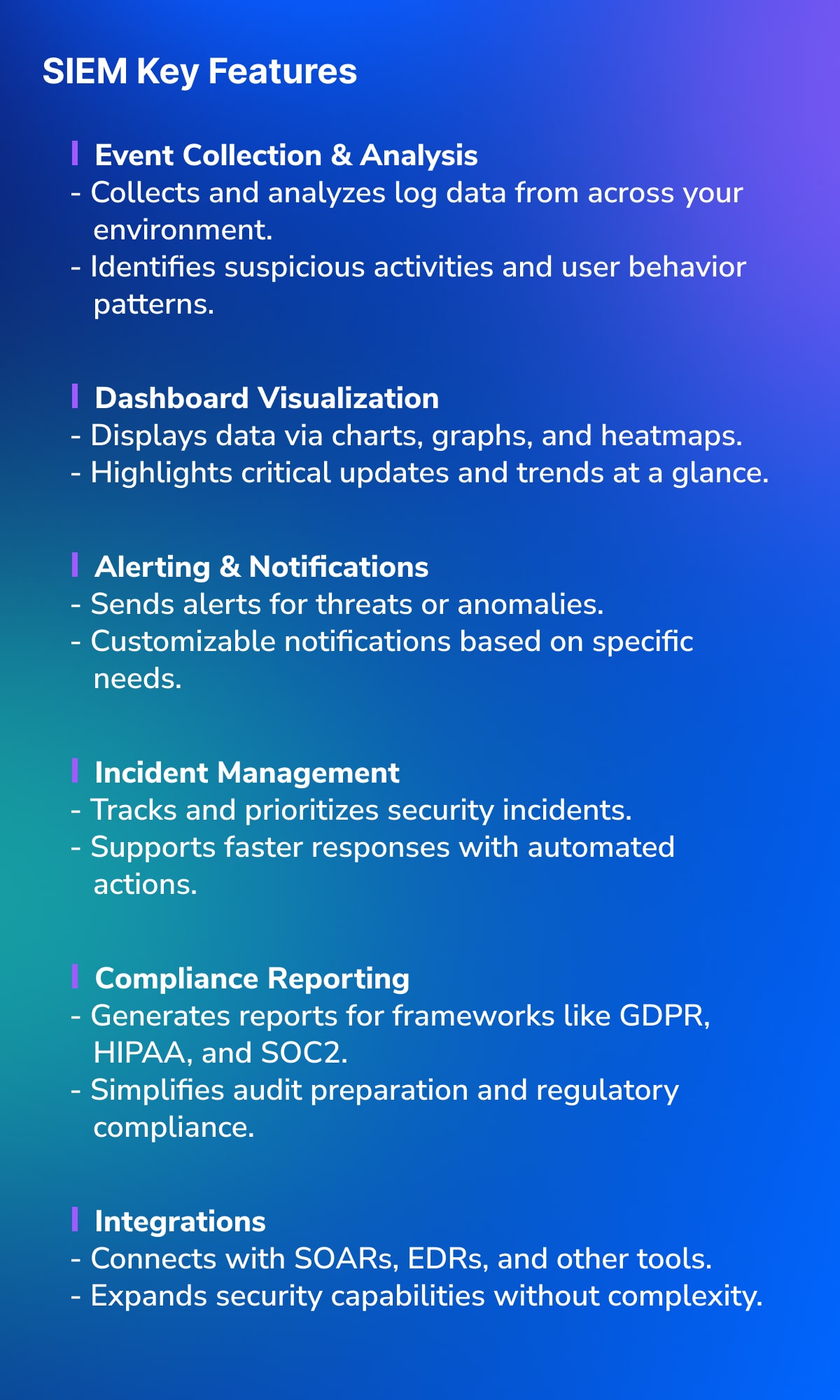
7. EDR vs SIEM:










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security



 “EDR is crucial; it’s a foundational control. Businesses, regardless of size, need it, especially as cyber insurance carriers recognize its importance. It’s like putting locks on your doors – a necessary step for awareness and security.””
“EDR is crucial; it’s a foundational control. Businesses, regardless of size, need it, especially as cyber insurance carriers recognize its importance. It’s like putting locks on your doors – a necessary step for awareness and security.””