Contents:
Sophos Intercept X is one of the top choices for ransomware protection. However, some users report that it is resource-intensive and also asked for more flexibility.
Sophos Intercept X is deeply integrated into the Sophos EDR platform. So, using it often requires a full commitment to the Sophos ecosystem. In some cases, that might mean paying for tools that you don’t really need.
Both reasons are strong enough to make you look for Sophos Intercept X alternatives. Here’s my list of the most efficient, adaptable, and cost-effective Sophos Intercept X competitors to consider.
Key takeaways:
Heimdal – Signature-free ransomware protection with real-time encryption detection and seamless cloud integration.
ESET Protect – Multi-layered endpoint security with behavior-based detection and low system impact.
CrowdStrike Falcon – Cloud-native protection with AI-driven threat detection and automated remediation.
ThreatDown – Lightweight, signature-less threat detection tool formerly known as Malwarebytes Endpoint Protection.
Norton 360 Deluxe – Consumer-focused suite with ransomware protection, VPN, and identity theft monitoring.
ThreatLocker – Zero-trust application control solution that prevents unauthorized software execution.
WatchGuard Endpoint Security – AI-powered endpoint security with threat hunting and cloud-based management.
Bitdefender GravityZone – Advanced AI-driven threat detection with fileless attack protection and risk analytics.
1. Heimdal
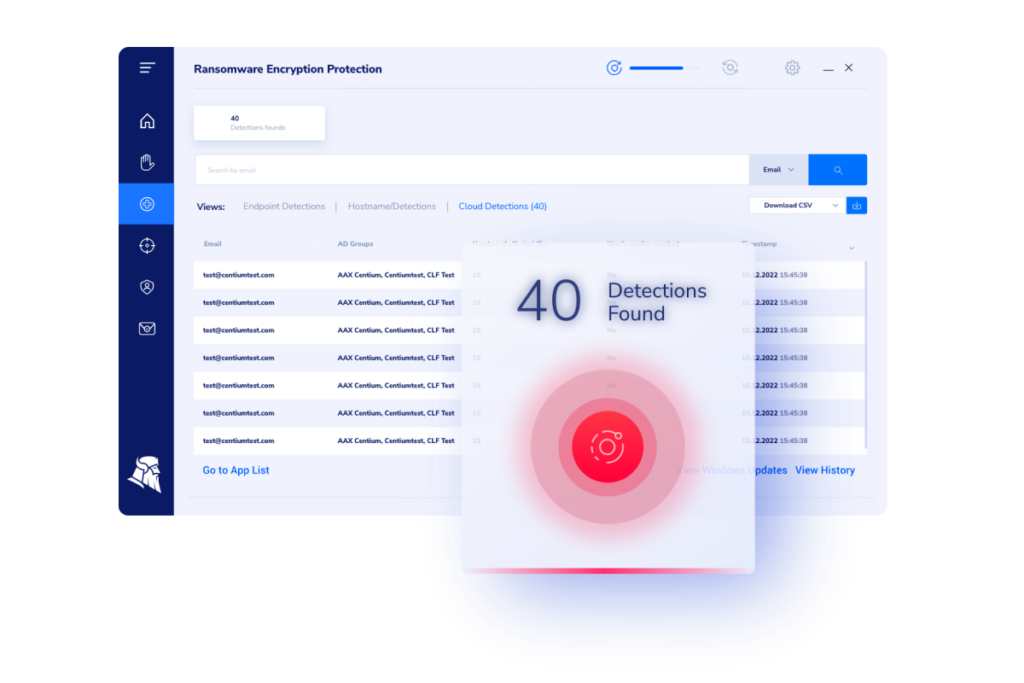
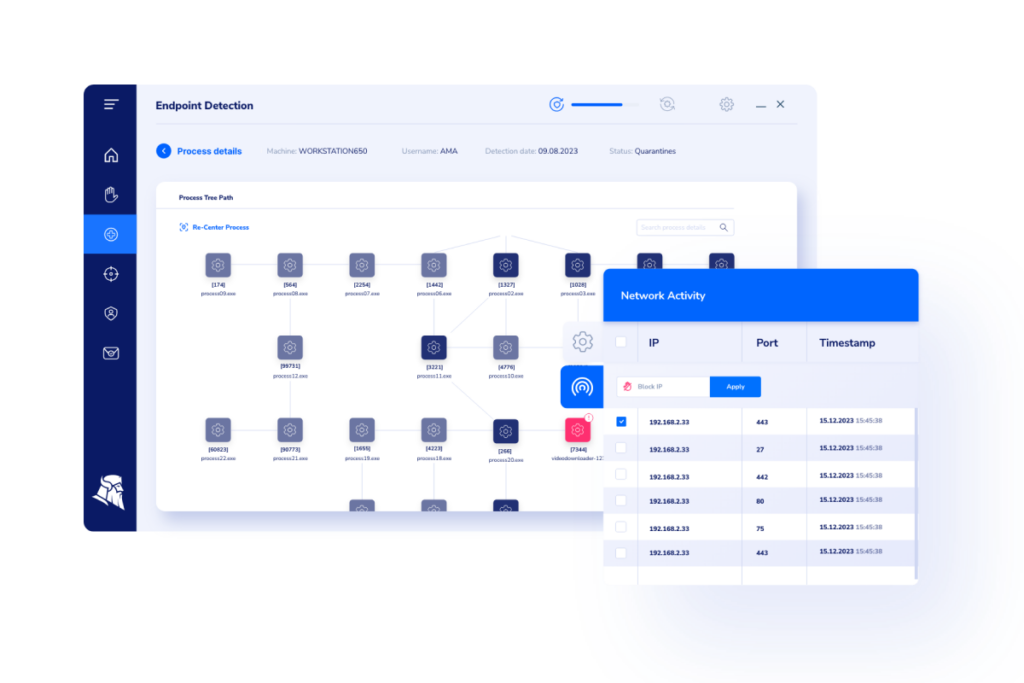
Heimdal’s modular and unification-oriented approach gives users complete flexibility. This means you can use any tool in the XDR platform together or as point solutions. The same goes for the Ransomware Encryption Protection module. You can integrate it with any in-place solution you have or build your custom safety mix inside Heimdal’s XDR suite.
What makes Heimdal the best alternative to Sophos Intercept X?
One of Heimdal REP’s best features is its signature-free approach. The tool detects and stops ransomware encryption attempts even from files that were not marked as malicious.
Main capabilities
- Minimal detection gap due to its advanced threat intelligence reducing false positives
- Ransomware incident tracking with timestamps, tree diagrams, PowerShell script analysis, and more
- Ransomware Rollback option – restores the system to a time prior to the attack & encryption
- Real-time encryption protection through continuous monitoring of file modifications. Heimdal’s REP detects and stops ransomware variants on the spot
- Detects ransomware regardless of signature, so it protects against new ransomware strains too
- Works well and you can use it with any antivirus or EDR suite
- Is lightweight compared to the resource-intensive Sophos Intercept X
- Integrates with Microsoft, Amazon, and Citrix cloud workspaces, including OneDrive, SharePoint, and Teams
What do customers say about Heimdal?
Not having to worry about ransomware attacks is the most important solution that Heimdal provides. The biggest benefit, in addition to avoiding data loss, is that there is no need for costly and time-consuming training of your employees.
Pricing
Heimdal offers customized pricing that fits various business requirements and usage patterns. To see Heimdal in action watch the video below and book a custom demo.
2. ESET Protect
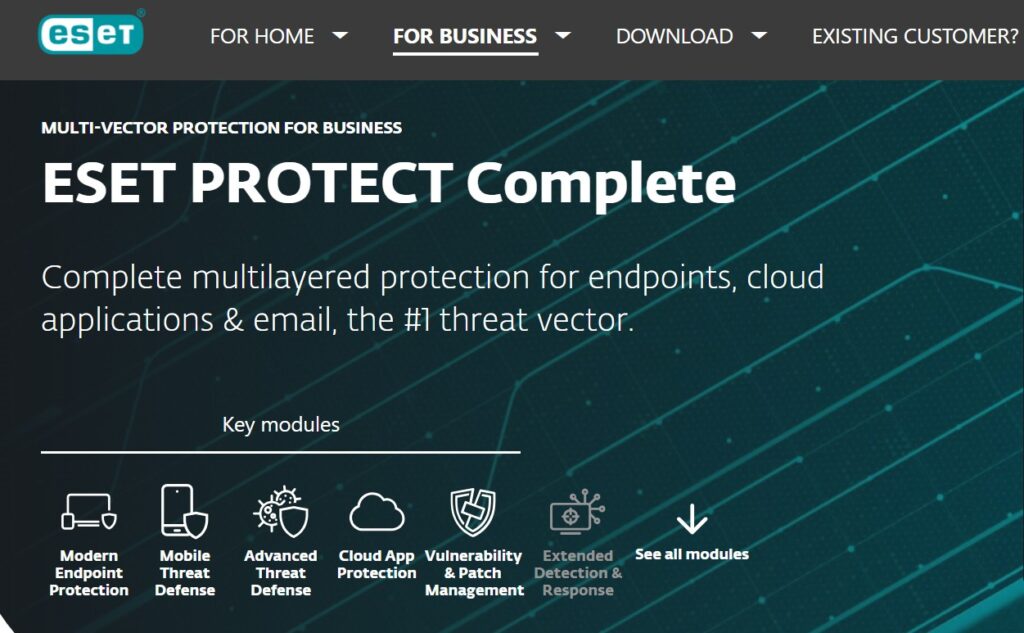
ESET Protect is an endpoint protection platform offering multi-layered security against ransomware. It provides real-time monitoring and incident response capabilities while maintaining a low system footprint.
Main capabilities
- Advanced threat defense
- Multi-layered security
- Remote management
- Behavior-based detection
Cons
- Limited third-party integrations compared to competitors.
- Some users report difficulty configuring policies for large-scale deployments.
- Advanced features can be overwhelming for beginners.
Pricing
ESET Protect pricing varies based on the modules you choose and the number of your endpoints.
3. CrowdStrike Falcon Endpoint Protection Platform
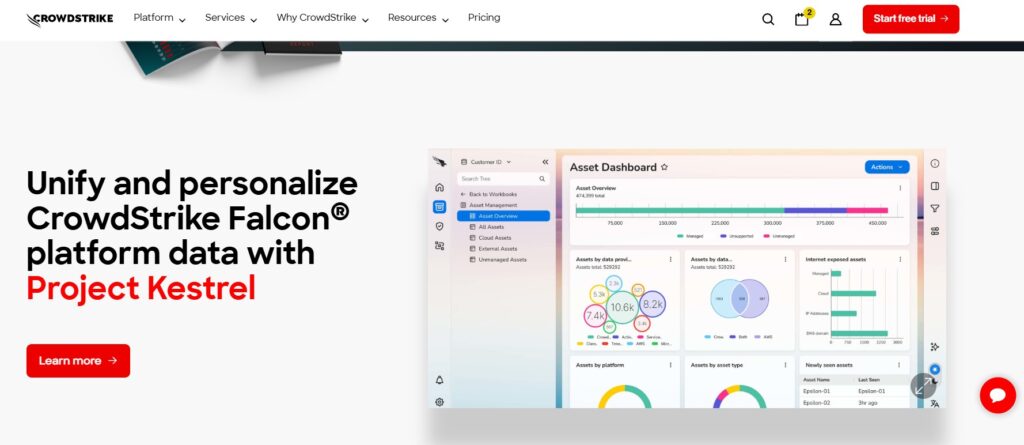
CrowdStrike Falcon is a cloud-native endpoint protection platform with AI-driven threat detection and response capabilities. It offers real-time monitoring and incident investigation tools.
According to a 2024 SE Labs Enterprise Advanced Security Ransomware Test, they’re great at blocking known ransomware.
Main capabilities
- Behavioral AI threat detection
- Threat intelligence integration
- Automated remediation
- Cloud-Native architecture
Cons
- Premium pricing compared to other alternatives.
- Advanced features may require a steep learning curve.
Pricing
Pricing is based on modules and the number of protected endpoints. If you’re interested in this solution, you can test it for free for 15 days.
One thing I don’t love about the CrowdStrike Falcon is that it can be a bit pricey compared to other options. But, we do get solid protection for the cost.
4. ThreatDown
ThreatDown is the former Malwarebytes Endpoint Protection. The endpoint security platform provides comprehensive ransomware protection and proactive threat prevention.
It uses advanced signature-less detection to identify and block known and unknown threats.
Main capabilities
- Signature-less threat detection
- Automated threat remediation
- Endpoint isolation capabilities
- Lightweight agent for low resource consumption
Cons
- Lacks full EDR and XDR capabilities.
- Some users report delays in customer support response.
Poor customer service and slow response to concerns that should be easy to remedy.
Pricing
Pricing is not public, so contact ThreatDown for a quote.
5. Norton 360 Deluxe

Norton 360 Deluxe ensures endpoint security for individuals and businesses. It offers ransomware protection, a firewall, and a VPN solution. The solution includes AI-driven threat detection to block malware before it executes. Additionally, its dark web monitoring and identity theft protection help safeguard personal and business data.
Main capabilities
- Ransomware protection for Windows, macOS,Android, and iOS
- AI-Based threat detection
- VPN and dark web monitoring
- Identity theft protection
This is one of the known antiviruses in the market. It has improved a lot, and we had a lot of issues with the system slowing down. The product is well integrated with antivirus, internet security, and malware which gives good choices for customers requiring a set of products.
Cons
- Primarily suited for individual users and small businesses rather than enterprise-level security.
- Can slow down system performance on older devices.
Pricing
Subscription-based pricing starts at $99.99 per year. For businesses, Norton offers a 30-day free trial.
6. ThreatLocker
ThreatLocker provides zero-trust endpoint security by allowing only approved applications to run. Thus, it reduces the ransomware attack surface. Its granular control over application execution helps businesses prevent unauthorized software and malware from operating.
Main capabilities
- Zero-trust application control
- Ringfencing technology
- Ransomware rollback features
- Granular endpoint security policies
Cons
- Complex setup process for non-technical users
- May require frequent rule updates
Pricing
Contact ThreatLocker for a custom quote.
7. WatchGuard Endpoint Security
WatchGuard delivers comprehensive endpoint security with AI-driven threat detection, behavioral analysis, and automated incident response. Its advanced EDR capabilities enable threat hunting, helping organizations detect and mitigate ransomware attacks.
Main capabilities
- AI-powered threat intelligence
- Threat hunting capabilities, including AI-powered threat detection and behavioral analysis
- Automated incident response
- Cloud-based endpoint management
Cons
- Steep learning curve for new users.
- Tech support is slow, often taking days to respond.
Unfortunately, Tech Support is lacking. When you need support, regardless of whether it’s considered mission-critical, it may take days to respond. Watchguard needs to improve in this area.
Pricing
Pricing is available upon request.
8. Bitdefender GravityZone
Bitdefender GravityZone provides advanced ransomware protection, machine learning-based threat detection, and endpoint security for businesses of all sizes.
It uses HyperDetect AI threat analysis to find and neutralize threats before they can cause damage.
Main capabilities
- HyperDetect AI threat analysis
- Fileless attack protection
- Integrated risk analytics
- Patch management
Cons
- Can be resource-intensive during scans.
- For optimal performance, Bitdefender GravityZone needs frequent adjustments. That means fine-tuning security policies, managing exclusions, and optimizing resource usage. Without regular tuning, users may experience false positives, performance slowdowns, or missed detections.
The automatic product updates always seem to have issues, at any one time over half of our endpoints will have errors with updates, despite being online. They don’t have a stable download link, so we can embed the link in our installer scripts or onboarding.
Pricing
Pricing varies based on deployment size and is available on request.
Frequently Asked Questions (FAQ)
How does ransomware encryption work?
Ransomware encrypts files by using cryptographic techniques, making data inaccessible. Once the hacker encrypted your data, they will ask for a ransom in return of the decryption key. You can read about the most dangerous ransomware groups here.
How does Sophos Intercept X protect against ransomware attacks?
Sophos Intercept X uses deep learning AI and CryptoGuard technology to detect and block ransomware encryption attempts.
How can I protect my data from ransomware encryption?
- Use real-time, signature-free encryption protection like Heimdal’s Ransomware Encryption Protection to stop malicious encryption processes.
- Keep regular backups of your data on different servers
- Enable multi-layered endpoint security.
- Educate employees to recognize phishing emails.
Are all encryption processes malicious?
The encryption process is not always malicious. It can be useful to protect data from hackers who might try to enter databases and steal or compromise valuable information.
In fact, security specialists use encryption to prevent hackers from reading sensitive data. Even if a breach happens, the threat actors won’t be able to use the data. So, you should use encryption for your data in transit or at rest.
Heimdal’s REP is able to tell if an encryption process is legitimate or malicious.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and Youtube.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security