Contents:
Session hijacking lets hackers steal your online session and perform actions on your behalf. You don’t want to fall into their trap, do you? Then you are now in the right place. We’ve got your back. We have gathered all you need to know about what is session hijacking, how session hijacking works, and session hijacking prevention. Keep reading and stay safe!
What Is Session Hijacking? Definition
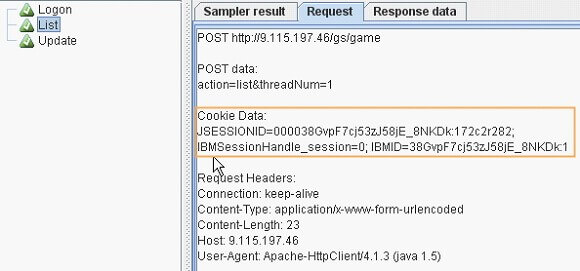
Session hijacking stands for a cyberattack where a malicious hacker places himself in between your computer and the website’s server while you are engaged in an active computer session (the time between you first log into your bank account, and then log off after your operation, for example) in order to steal it. The hacker actively monitors everything that happens on your account, and can even kick you out and take control of it. It is often called cookie hijacking or cookie side-jacking because the hacker gains knowledge of your session cookie giving him access to the session ID that lets him impersonate the user and perform actions on his behalf: transferring your money to his account for instance.
What’s a session cookie? A temporary session cookie is created when you login into an application. This helps the server remember you are logged in and identify your session through the HTTP stateless application protocol attached to the HTTP header.
What Can Attackers Do After They Successfully Hijack a Session?
The biggest threat of session hijacking is that the malicious attacker can also enter the server and access its information without having to hack a registered account. In addition, he can also make modifications on the server to help him hack it in the future or to simplify a data-stealing operation.
If successful, threat actors would:
- Use your bank app to transfer your money to their account
- Perform identity theft
- Buy stuff on your behalf
- Perform a ransomware cyberattack, where you’ll have to pay the decryption key to have your stolen data back
Sounds nasty? Let’s dive into session hijacking types for a better sprinkle of awareness.
How Session Hijacking Works. Session Hijacking Types
When we talk about session hijacking broadly, we can do it at two different levels: the first is the session hijacking application level (HTTP), the second it’s the TCP session hijacking (network level). The first targets a session cookie, the hacker steals the session ID and performs actions on the behalf of the user, the latter means intercepting packets transmission between the user and the server.
We will talk about session hijacking types at the application level in this article, as when hijacking a session hackers generally target websites and web applications that involve cookies found in the HTTP application-level protocol, hence its generic nickname cookie hijacking. The TCP session hijacking is not relevant in a session cookie hijacking context, however, an example of this is mentioned at the end of the article to make you understand the difference.
Here are the top 6 session hijacking types:
1) Cross-Site Scripting (XSS) or Misdirected Trust
- Meaning: The hacker will infect websites or web applications with a malicious script.
- Reason: the web application has vulnerabilities.
- Method: the hacker takes an online app and sends malicious code (Java, HTML, Flash, etc.) to an end-user. The code seems to be trustworthy because it belongs to the server. When a user visits or does a certain action on infected websites, the scripts activate. Then the malicious script will track the visitor’s session ID or cookie, and then send it over to the malicious hacker. The hacker hijacks the session.
- Types: DOM-based XSS (the vulnerability lies in the client-side code, not in the server code), Stored XSS (the database of the website contains the malicious script), and Reflected XSS (the current HTTP request sends the script).
2) Session side-jacking
- Method: This takes advantage of an open, unencrypted communications channel to look for a session ID or token, more specifically the user’s network traffic, permitting the hacker to perform a man-in-the-middle attack.
- Typical targets: unsecured Wi-Fi connections and websites without an SSL certificate (they don’t encrypt data sent between computer and server).
- How does the hacker do this? Using a sniffing device or software such as Wireshark or Owasp tool that will allow session hijacking owasp and perform session sniffing.
- Goal: incoming and outgoing traffic scanning through packet sniffing and looking for the session token (session ID).

3) Session fixation
Session fixation is a session hijacking example method a hacker uses to access your account with a Session ID of his choosing.
Session fixation example:
- Let’s say the attacker wants to obtain the money you have in your bank account, at www.example.com.
- He will then send you a phishing email or text message.
- The message will contain some promotional offer at the bank or a password reset link.
- The link does point to your bank’s login page, but it also contains the Session ID the malicious hacker supplied.
- Example of Session ID: example.com/SessionID=I_want-your_money.
What does this session fixation example show?
By logging into your account from this link, the malicious hacker has “fixed” your Session ID as “I_want_your_money”. He can now use it to access your account at the same time as you, and clean it of any money or do any other operation.
4) Malware infections
- Method: browser hijackers steal information saved in your cookies including the Session ID. They can make this by tricking you into clicking a compromised link.
- They use that to conduct unauthorized actions on your computer by installing malware on it.
- Then the hijacker might install programs, browser toolbars, or simply siphon your private information.
5) Brute-forcing the Session ID
- The attacker guesses the Session ID through a brute-force attack depending on its length.
- He will bombard the server with thousands, or tens of thousands of requests, hoping that one of these is the ID he is looking for.
- Targets: smaller, and more insecure websites, because technical infrastructure isn’t always present to preempt this type of threat.
- Bigger websites are more secure and better equipped to deal with this threat. Reasons? Longer IDs and built-in security features such as IP blocking.
6) Man-in-the-Browser
- Your browser is infected with a Trojan horse.
- It monitors what you do on the web.
- Goal: collecting data and changing the input values in banking forms and similar websites.
- A man-in-the-browser attack will also target browser extensions and plugins. A lot of the time, smaller companies will code these extensions, but they lack the resources they need to secure the software.
What Is a Session ID?
As you can guess, the SessionID is basically the “name” of a particular session. For instance:
Your Facebook session might have the SessionID 1233vs%fav.
Your Amazon session might have the SessonID 684s`9lbd.
What Are the Ideal Targets of Session Hijacking?
Session hijacking usually targets:
- Big websites and servers
- Forums
- Banking websites
- Online shops
Also, the fact the organizations use SSO (Single Sign-On) makes them a target, since authenticated users are identified through cookies in these systems, giving threat actors access to everything: financial systems, web applications, customer data, and so on.
How to Prevent Session Hijacking
Here you can find the session hijacking prevention measures that will keep you away from cookie hijacking. Start to implement them today and be a step ahead!
1) Check if the website is HTTPS
HTTPS indicates the security of a website. Therefore, if you access a website’s URL starting with HTTPS instead of HTTP, this means that the data your computer sends to the server will be encrypted.
Without HTTP, data packets sent between your computer and the server are essentially plain text, meaning the malicious hacker can just read them as they are.
![]()
2) Log out at the end of every session
Regenerate your session key
Logging out of your account will terminate the session. This means you will also force the attacker to log out, stopping him to hijack the session.
Ideally, you want operations on sensitive accounts such as your bank to be “hit and run” operations, where you go in, do the operation, and immediately log out. This will significantly cut down the amount of time an attacker has access to your account, and limit how much damage he can inflict.
3) Use a good antivirus
While not the end-all, be-all solution to cybersecurity, an antivirus goes a long way in keeping you safe. The best antivirus programs have a significant database of malware signatures, a good behavioral analysis engine, and removal capabilities.
Here’s a more in-depth resource that might help you find the best antivirus.
Heimdal™ Security’s Next-Gen Antivirus & MDM can help you with this.
4) Prevent Cross-Site Scripting with HttpOnly
Go to the HTTP Header, find the Set-Cookie, and set the HttpOnly attribute. This way, threat actors will not have the possibility to access cookies from client-side scripts. You can also apply the Secure and Same Site directives.
5) Don’t log in on open wireless networks
An unencrypted Wi-Fi network is an open invitation for a malicious hacker to steal your information.
Using either a hardware tool or software, a malicious hacker can easily intercept the traffic, and see what is communicated over the open network.
This includes everything, from credit card data to passwords, instant messages, or emails.
As a takeaway, do your best not to use open Wi-Fi networks. If you have to use the Internet, switch to your data plan instead.
Or, if you still need public Wi-Fi, make sure you use a VPN that protects and encrypts your data.
6) Keep your browser and other software updated at all times
Software vulnerabilities are a major security risk since hackers design their malware to target a specific vulnerability in a certain kind of software.
Outdated browsers, Flash, and other toolbars exponentially increase the risk of a session hijacking, so be sure to always update this software.
If this sounds like too much of a hassle, then we suggest you use HEIMDAL™ THREAT PREVENTION HOME, a security tool that automatically updates critical software on your computer, without bothering you with popups and other nuisances.
7) Traffic filtering
Another way to make sure session stealing malware doesn’t infect you is to use traffic filtering solutions. These programs scan your traffic and then block any malware that might be coming towards your PC.
A traffic filtering solution will also scan your outgoing traffic. If it notices personal information of yours going to a suspicious site, it will cut off communications, keeping it safe and out of the hands of malicious hackers.
The Additional Security Pill
Remember that we talked at the beginning about classifying session hijacking at two levels? Before you go, read an example of TCP session hijacking for your extra info and to help you make the difference between cookie hijacking (what’s the article about) and TCP session hijacking. What is out on the internet is all about cookie hijacking at the application level.
This example is not related to session cookie whatsoever; therefore, the hacker will not steal the session ID to hijack your computer session but will use transmission of data packets between the user and the server to hijack a session at the network level.
The TCP session hijacking is not actually relevant when talking about cookie hijacking, because it does not involve the stealing of the session cookie, but focuses on sequence numbers of data packets. It is just worth mentioning as another type of session hijacking, generally speaking, that could be performed at the network level.
TCP session hijacking
- The attacker guesses the sequence numbers of data packets sent between the victim’s computer and the server.
- Then he creates his own data packets.
- He wraps them in the sequence numbers and sends them to the server.
- The website server is thus tricked into believing the real computer to be a malicious hacker.
The question is: are guesses always correct? Well, if the threat actors fail to properly guess the sequence number, this can result in the server sending a reset packet, that will basically restart the connection from scratch. In other cases, the server might decide to end the session entirely.
Wrapping up…
An old attack method, that will still be around for a long time to come, session hijacking is an understated threat, overshadowed by the bigger ones such as ransomware, DDoS attacks, or banking Trojans.
However, its ease of use combined with the outsized potential for profit still makes it a potent and heavily used tool in the arsenal of malicious hackers.
Have you ever suffered a session hijacking? What are some other security methods that you use to stay safe online?

Also, drop a line if you have any comments or suggestions. We will be more than happy to answer you!
And if you really want to be updated, you can also subscribe to our newsletter!
This post was updated by Andra Andrioaie in July 2021.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security







