Contents:
A port scan attack is a technique that enables threat actors to find server vulnerabilities.
Ports enable devices to recognize different kinds of traffic: webpages, emails, instant messages, etc. Ports monitoring helps network admins track all the traffic that comes and goes through the network.
Security analysts also use port scanning as a method to check what are the open ports that receive or send data. After they send packets to certain ports, they evaluate the responses in order to spot vulnerabilities.
The difference is that hackers use this process to discover open points, breach the network, and launch attacks.
Port Scanning as an Attack Method
Threat actors use port scanning in their attacks to find vulnerable servers. It`s one of their first steps when they plan to breach a network.
Some of the most hacked TCP port numbers are port 21 (FTP), port 22 (SSH), port 23 (Telnet), port 25 (SMTP), port 110 (POP3), and port 443 (HTTP and HTTPS). Port 53 (DNS), ports 137 to 139 (Windows NetBIOS over TCP/IP), 1433, and 1434 (Microsoft SQL Server) are also on the list.
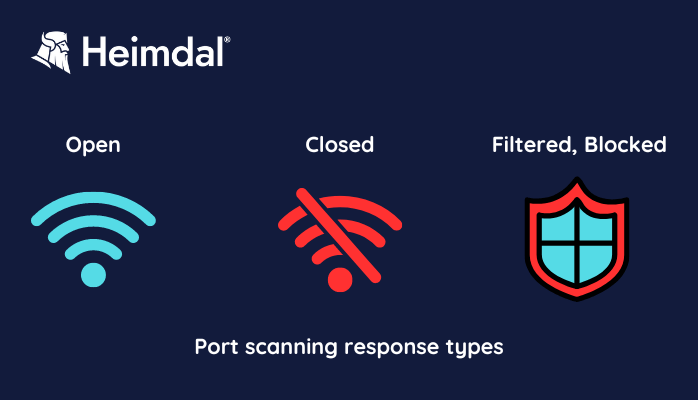
Port scanning response types
Here are some of the information they collect:
- Which one of the ports is open, closed, or filtered?
- What OS is running on the machine?
- Is there a firewall protecting the network? How efficient is it?
- What apps are running?
- Which network services ask for authentication?
- Are anonymous logins allowed?
- Which of the devices are online?
- Which network and which server could be vulnerable?
- What organization is running a specific DNS or web server? Mind that sometimes hackers use fake traffic for port scans.
- Which are the users that own services?
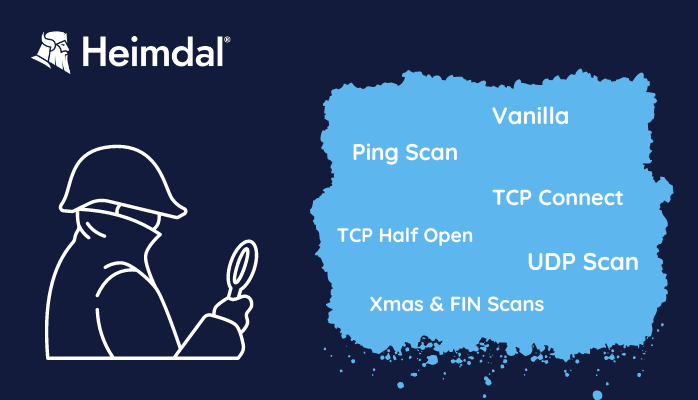
Port Scanning Techniques
There are several open-source port scanning tools you can use for network mapping. Nmap is one of the most popular and offers different port scanning techniques:
- Ping Scan
Ping scans, also known as internet control message protocol (ICMP) requests, are the simplest port scanning technique. This network scanning technique determines which IP addresses map to live hosts. Ping scans are used by network administrators to troubleshoot issues.
Admins usually disable pings for external traffic on the firewall or the router, but leave them open inside the network. This way, malicious operators can`t use this technique to scan the network.
Hackers can also use pings to launch a DoS attack. To do that, they write a script that pings the WAN IP address on and on. The amount of traffic that pings your IP overwhelms the router, so you`ll get slow access to the Internet.
- Vanilla Scan
This is another basic technique and it attempts to connect to all of the 65,536 ports simultaneously. It sends a request to connect (SYN flag), then, after it receives an acknowledgment of connection (SYN-ACK), returns an ACK flag. This SYN, SYN-ACK, ACK exchange comprises a TCP handshake. As a full connection is logged by firewalls, the Vanilla port scanning technique is easy to spot.
- TCP Half Open
This one is also called an SYN scan. It sends an SYN and waits for the target to send back an SYN-ACK, but it won`t answer back. Because the TCP connection is not complete, the system will not log the process. So, a TCP Half Open is hard to detect. However, the sender does find out if the port is open or not.
Port Scanning Techniques
- TCP Connect
The TCP connect port scanning technique works just like the SYN scan, but it completes the TCP connection. Since it sends one more packet, it is noisier and therefore easier to spot. So, the TCP connect scan is less common and popular.
On the plus side, the user won’t need the same level of privileges to run it, as it would need for an SYN scan. It just uses the same connection protocols like any user that connects to other systems.
- UDP
This offers lots of exploitable UDP services that attackers can use. DNS exfiltration is only one of them.
For this technique, it is important to send a specific payload to the target. In order to check if a DNS server is up, you should send a DNS request.
You can send a DNS request to UDP port 53 and see if you get a DNS reply. If the system responds, it means there`s a DNS server.
- Xmas and FIN Scans
The FIN scan means you send to a port a FIN flag, although you don`t intend to end an established session. The system’s response allows you to check the state of the port or gather insights about the firewall. If a port is closed and receives an unsolicited FIN packet, it sends back an instantaneous abort packet (RST). If the port is open, it will ignore it.
The Xmas scan sends various flags – FIN, URG, and PUSH – with the intent to create an illogical interaction. The sender then analyzes the system’s response so it can find out more about the system’s ports and firewall.
Hackers love these port scanning techniques because they are usually overlooked by logs. These flags can go unnoticed by firewalls, so the info they bring back is more reliable.
How to Detect Port Scans
These days, professional security tools have high efficiency in detecting port scans. You can detect a port scan if you keep track of the number of requested ports for a certain IP address. This way you can see if hackers are actively searching for attack opportunities.
To get relevant data about a network and its devices, threat actors will keep trying to check many different ports. It`s also important for them to do it in a short period of time. Checking the numbers will help you stay one step ahead of malicious actors.
How to Prevent Port Scan Attacks
You can`t prevent port scanning, but you can strengthen your business` cybersecurity strategy. Your security team should focus on closing whatever gates might be available for attackers to find. Have them run a port scan themselves in order to find out what the hackers might discover.
Here are three things you should enforce as protection measures against port scan attacks:
- Install a firewall. This will prevent unauthorized access to your network. A firewall will not only control the ports` visibility but also detect and stop unwanted port scans. Configure it to alert admins if they find a single host that sends connection requests to several ports.
- TCP wrappers allow admins to accept or block access to servers based on IPs and domain names.
- Use a port scanner to check if there are unneeded open ports. Port scanners will constantly check the system and report potential vulnerabilities.
Heimdal®`s Solution Against Port Scan Attacks
The threat landscape is continuously evolving, as hackers keep coming up with new ways of reaching their goals. So, if you want to avoid a port scan and many other threats that may occur, make sure you use a cutting-edge cybersecurity solution.
Heimdal helps you protect your enterprise`s network and endpoints through its threat-detection oriented Next-Gen Antivirus and MDM product.
It offers you 4 advanced malware detection layers, anti-brute-force safeguards, full E-PDR solution with Threat Prevention DNS, and Zero Trust Execution Protection. Its special design will protect your enterprise against data leaks. It has a 100% certified detection rate for known malware and is really simple to use.
Some of the most customer appreciated benefits the easy-to-use management console provides are:
- Quarantine of TTPC processes (Threat Prevention)
- Firewall Management and attack detection
- Remote full scan per device or per group
- Remote delete per device or per group
- Tamper Protection including Isolation
The solution also comes with strong Mobile Device Management (MDM) features. This enables the security team to watch over your mobile devices from literally anywhere. And in the Work from Home Era, this feature really is a must-have. It empowers the crew to pinpoint the location of a lost or stolen device, remotely wipe data or lock the machine.
Heimdal`s Next-Gen Antivirus and MDM are just one of the important steps that will make your business hacker-proof. Match them with other Heimdal solutions to benefit the most powerful Endpoint Prevention, Detection, and Response (EDR).
Your security team will surely appreciate they`ll be able to have all that tools on one platform.

Heimdal® Next-Gen Endpoint Antivirus
- Multiple layers of detection.
- Enhanced Brute-Force Protection.
- Remote device control with MDM.
Wrap Up
As stated before, it is impossible to block port scanning. One of the reasons is that your security team needs to use it too, to run penetration tests and detect potential vulnerabilities. And it`s not that easy to determine for sure the malicious nature of a port scanning.
The best bet is to choose carefully your security partner. That way you will be well prepared to detect and stop the threat actors` attacks. Heimdal® is only one click away whenever you need to upgrade your cybersecurity strategy and assets.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and Youtube for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security