Contents:
What is network firewall security? An essential component of a successful cybersecurity strategy, it relies on the firewall, a known companion of any device that connects to the Internet. The firewall is near and dear to any online user, whether they know it or not. But let’s not get ahead of ourselves. First things first, what is a firewall? You most likely have heard this name before. The concept is almost as old as that of personal computers, but a minor explanation might still be in order. As per the Heimdal Security Glossary,
A firewall is a network security system designed to prevent unauthorized access to public or private networks. Its purpose is to control incoming and outgoing communication based on a set of rules.
Simply put, a firewall is a basic network security defense tool whose primary objective is to monitor traffic. It does so by following a preset checklist, which is why it is an essential, yet simple layer of protection you definitely need to include in your cybersecurity strategy. All in all, the firewall is a must-have that we’re all familiar with by now. So, what is network firewall security then? In the following lines, I will go over the elementary notions of this topic, as well as clarify what the function of a firewall in network security is.
What Is Network Firewall Security?
A discussion on the online perimeter is necessary to better understand the connection between firewalls and network security. Just like your company’s physical perimeter, its digital counterpart requires protection as well. This is where online perimeter security comes in. Generally speaking, a strategy of this kind consists of four main layers that work with each other:
- border routers, which are the first outpost in terms of data filtering;
- firewall, which further monitors traffic and blocks threats;
- Intrusion Detection System (IDS), which rings the alarm if attackers try to get into;
- Intrusion Prevention System (IPS), which proactively shields your network from cyber-threats.
Thus, network firewall security can be defined as a subset of online perimeter security dealing with threats exclusively at the firewall level. Although it is only the second protective stratum, and therefore not necessarily the most advanced, it is still an important defense mechanism whose integration into your enterprise’s systems can save you a world of trouble. What is more, firewalls have come a long way since its much-disputed invention in the late 1980s. Nowadays, there are plenty of models on the market to choose from depending on your needs and the size of your enterprise. Below, I will discuss the core types of firewall in network security, as well as their key benefits and shortcomings. As always, stay tuned until the end for some concrete recommendations on what to choose for your business network.
Types of Firewall in Network Security
When it comes to types of firewall in network security, the concept is split into a couple of overarching categories: firewalls according to structure and firewalls according to process. Each category then has its corresponding types, all of which I have discussed in more detail in the sections that follow.
Firewalls According to Structure
In terms of structure, two main types of firewalls can be identified:
A. Hardware Firewall
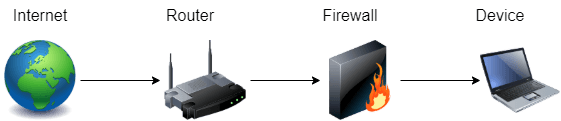
A hardware firewall is a stand-alone security device. They are placed between an organization’s internal network and the external network represented by the Internet. Also known as an appliance firewall, the hardware firewall has its own resources and does not rely on those of the machines. It stands as a gateway filtering outgoing and incoming traffic and is primarily used by medium to large enterprises as part of a network security strategy.
B. Software Firewall
A software firewall is installed directly on the device it protects. Also known as a host firewall, it needs to be set up on each machine in a network and relies on system resources such as RAM and CPU to operate. While they are more time-consuming to manage than their hardware counterparts, software firewalls are also more efficient in distinguishing between traffic sources when filtering requests.
Firewalls According to Process
When it comes to the firewall’s method of operation, there are seven types to keep in mind:
I. Packet Filtering Firewall
The packet filtering firewall is the most basic type of firewall available. It is commonly attached to your network router or switch. As its name suggests, this type of firewall filters incoming traffic packets by inspecting their protocol, source IP, and destination IP, as well as their source port and destination port. Depending on the information carried by each packet, the process is either passed along or stopped. This is determined by consulting a predetermined list of access control rules.
II. Circuit-Level Firewall
A circuit-level firewall monitors Transmission Control Protocol (TCP) sessions. Its primary function is to vet the safety of an established connection, as it is built into another firewall or piece of software by default. The main advantage of a circuit-level firewall is that is simple to set up, which makes it a highly practical option. However, its filtering capabilities are still at a basic network firewall security level similar to those of the packet filtering solution.
III. Stateful Inspection Firewall
The stateful inspection firewall blends the methods of operation of the packet filtering firewall and the circuit-level firewall. This means that it monitors TCP sessions, while at the same time inspecting packets and establishing whether they are malicious or not by following a fixed set of rules. Even though the level of security offered by the stateful inspection firewall is higher than that of the previous two, it also takes a higher toll on the machine’s local resources.
IV. Proxy Firewall
A proxy firewall functions as an intermediate in the online communication between internal and external systems. It masks requests from the original client as being its own and forwards them, thus offering a fair amount of network firewall security. The name proxy means serve as a substitute, which is exactly what it does. Not only does it prevent contact with outside sources, but it also protects user anonymity in the process.
V. Cloud Firewall
The cloud firewall operates as firewall-as-a-service (FaaS) and is maintained by a third-party vendor. It is commonly used in place of a proxy server. The main advantage of a cloud firewall is its scalability, as it runs independently to internal resources and thus offers increased bandwidth to increase traffic load capacity. It is a viable option in terms of network firewall security, but it can also create the risk of losing command over your security assets.
VI. Deep Packet Firewall
A deep packet firewall performs in the same way as an IPS. Unlike traditional packet filtering systems, it examines the data in the packets and can thus investigate application-level attacks properly. Still, if your enterprise already has an IPS, this type of firewall provides more or less the same function. It is thus recommended to install one as a first, more encompassing step towards a network security solution, and not as an add-on.
VII. Next-Generation Firewall
The next-generation firewall is a device that combines the functions of several other firewalls (packet filtering, deep packet, stateful inspection) to provide advanced network security. Its main selling point is the fact that it verifies the actual payload delivered within a traffic packet, rather than looking at predetermined data. In terms of security, it is the most efficient type of firewall. Nevertheless, its cost also reflects this, which can be a drawback for small businesses.
Why Firewall Is Required in Network Security
Now that we’ve established what firewalls can do for you depending on their type, it’s time to ask the real question that has been on your mind ever since clicking on this article. How is a firewall useful in ensuring network security? The firewall has been around since the heyday of the World Wide Web, which is why nobody really knows what it does, they just know it does it. Simply put, when any machine connects to the Internet, it has a publicly addressable IP that allows for this to happen. If your devices wouldn’t have an inbuilt firewall, anyone online could take control of their services.
Network Firewall Security Benefits
To exemplify, let’s take the early 21st-century event that solidified the importance of the firewall in network protection. I’m talking about the release of Windows XP in October 2001. While the operating system did include a limited protective layer known as the Internet Connection Firewall, it was disabled by default and hard to locate by regular computer users. As a result, network worms such as Blaster and Sasser managed to compromised Windows XP computers in as little as 20 minutes back in 2003. Facing backlash from customers, Windows released the much-improved Windows Firewall in 2004. Although this took place more than a decade ago and cybersecurity solutions have come a long way since, the firewall remains an essential tool in the combating of online threats. A firewall:
- monitors and filters traffic,
- blocks Trojans and network worms,
- impedes the spread of spyware,
- and stops cybercriminals in their tracks.
Choosing the Right Firewall for Your Business
In terms of proper firewall implementation for network security, several variables come into play:
- the size of your business,
- what your cybersecurity needs are,
- and the software you already have (if any).
These are all things you should consider when choosing a network firewall security solution. One constant you should also consider on top of all the variables is that, when it comes to cybersecurity, it’s always better to be overprotected than underprepared in the wake of an attack. To have all your bases covered regardless of your enterprise’s size, my recommendation is Heimdal™ Next-Gen Antivirus & MDM. It has endpoint detection and response (EDR) attributes and an integrated firewall that will prevent brute force attacks and isolate machines in your network when needed. When merged with our core offering of Heimdal™ Threat Prevention, a market-leading DNS filtering, and the patch management solution, it becomes a complete Endpoint Security Suite. This unified and multi-layered cybersecurity suite prevents, hunts, and mitigates threats, keeping your network safe from any unlawful intrusions.
Beyond the Firewall – Amp Up Your Network Security
While the firewall is indeed an indispensable tool, achieving foolproof network security is beyond its realm. Even a holistic package such as our endpoint security suite can only protect your endpoints. To shield your business from harm entirely, you will need to secure the online perimeter in its physical form as well. If you are looking to take your company’s network cybersecurity strategy one step further, I suggest implementing an advanced IPS solution such as Heimdal’s own Heimdal™ Threat Prevention Network on top of any pre-existing solutions. Heimdal™ Threat Prevention Network combines the functionalities of a Host Intrusion Detection and Prevention System (HIDS/HIPS) with a strong Indicators of Attack and Compromise (IoA/IoC) add-on that will strengthen the security of your online perimeter.
Heimdal® Network DNS Security
With proprietary DarkLayer Guard™ & VectorN Detection technology that acts at perimeter level rather than focusing on endpoints, Heimdal™ Threat Prevention Network prevents malicious actors from communicating to Control & Command servers. This stops malware and network APTs from penetrating your system, preventing serious organizational threats such as data breaches.
Wrapping Up…
Network firewall security is essential for a rounded cybersecurity strategy. A standard defensive solution, the firewall has been around for decades and it has only gotten better with time. However, it is merely the second layer in what should be a complex system, which is why the smart approach is to not rely solely on it for protection.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security









