Contents:
Social media is mostly about entertainment. Facebook’s for keeping up with what our friends are up to. Twitter is our favorite tool for staying informed with the latest news (or for starting a revolution for that matter).
But when we turn to our LinkedIn account, we try to keep things serious and professional. This network focused on business is for keeping connected to people that worked with us, or with whom we may want to work with or collaborate some time in the future.
However, even if we try to keep it pro on our LinkedIn account, we still need to address privacy and security aspects. This is especially true in light of the recent mega breaches.
LinkedIn can become our vulnerability when it comes to cyber criminals, since we expose more personal information about us than on any other popular social networks. And it’s not just work experience that we share, it’s also past colleagues.
Therefore, make sure that you follow these 10 steps in order to enhance your LinkedIn security.
1. Set a Strong Password for your LinkedIn account
If you’ve been reading our blog (or any other security blog, for that matter), you already know how much we emphasize this matter.
A strong and unique password matters a lot.
Why should it be strong?
Because you want to make it as hard as possible for a cyber criminal to find out your password. That’s why you shouldn’t set passwords such as:
- abcde
- 12345
- qwerty
- password
- your name, nickname or birthdate
- a family member’s name or birthdate or nickname
- your pet’s name
- any other information remotely related to you and publicly available on any other social media account or on your blog or wherever else someone might find data about you

Why should it be unique?
Because recycling passwords leads to news like this ones:
- Mark Zuckerberg’s social media accounts were hijacked because of the recent LinkedIn data breach. Yeah, he was using the same password everywhere.
- Drake’s social media account was also breached. And yeah, he was also recycling passwords.
And these are only from the past week.
In case a cyber criminal manages to find out your password, they will not only have access to that account, but also to all other accounts where you set the same password.
So make sure you take a few minutes to change the passwords to your accounts with strong, unique ones.
You can also use a password management software – it will make it easier for you to handle all the passwords.
More advice on this matter in this password security 101 guide.
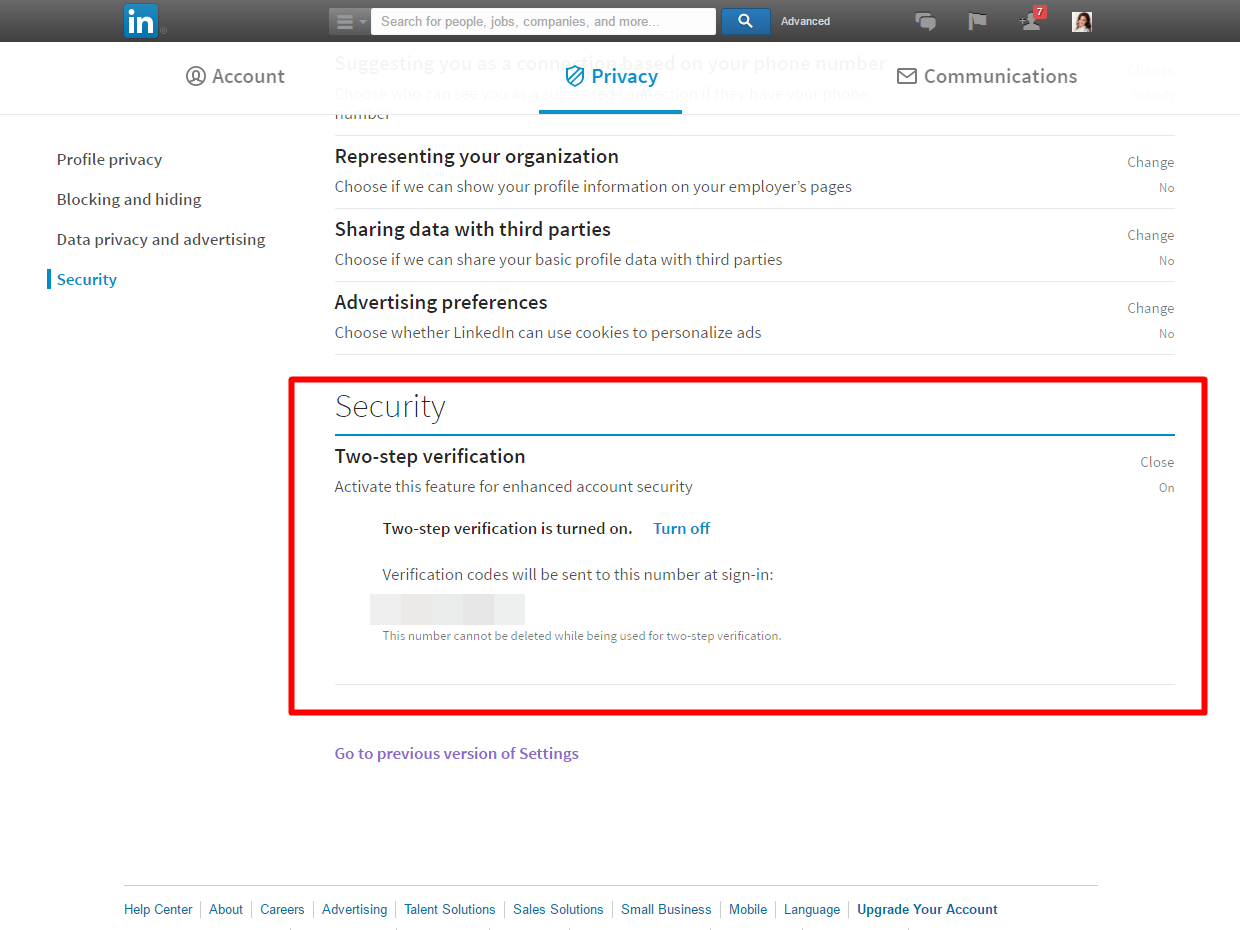
2. Activate Two-Step Verification
This one is as important as passwords and we’re advocating for activating it wherever it’s available.
Two-factor authentication is an essential step in our online security, as it works as an extra protection layer.
When you want to login to our LinkedIn account, you use a password. That password should be strong and unique, in order for cyber criminals not to break it.
However, in case they somehow do manage to find out your password, two-factor authentication comes into action. It would be extremely hard for them to be able to breach this second layer of verification.
Here’s how it works: whenever you’ll want to log in to your LinkedIn account, besides your password, you’ll be requested to provide another security code. It will be an unique one, time sensitive, and you’ll receive it via text message on your mobile phone.
This security measure should be enabled and used for each and every account that you have. Major companies offer you the option to activate it, from Google to Facebook, Instagram or Twitter.
For more details on how two-factor authentication works, we recommend you this security guide.
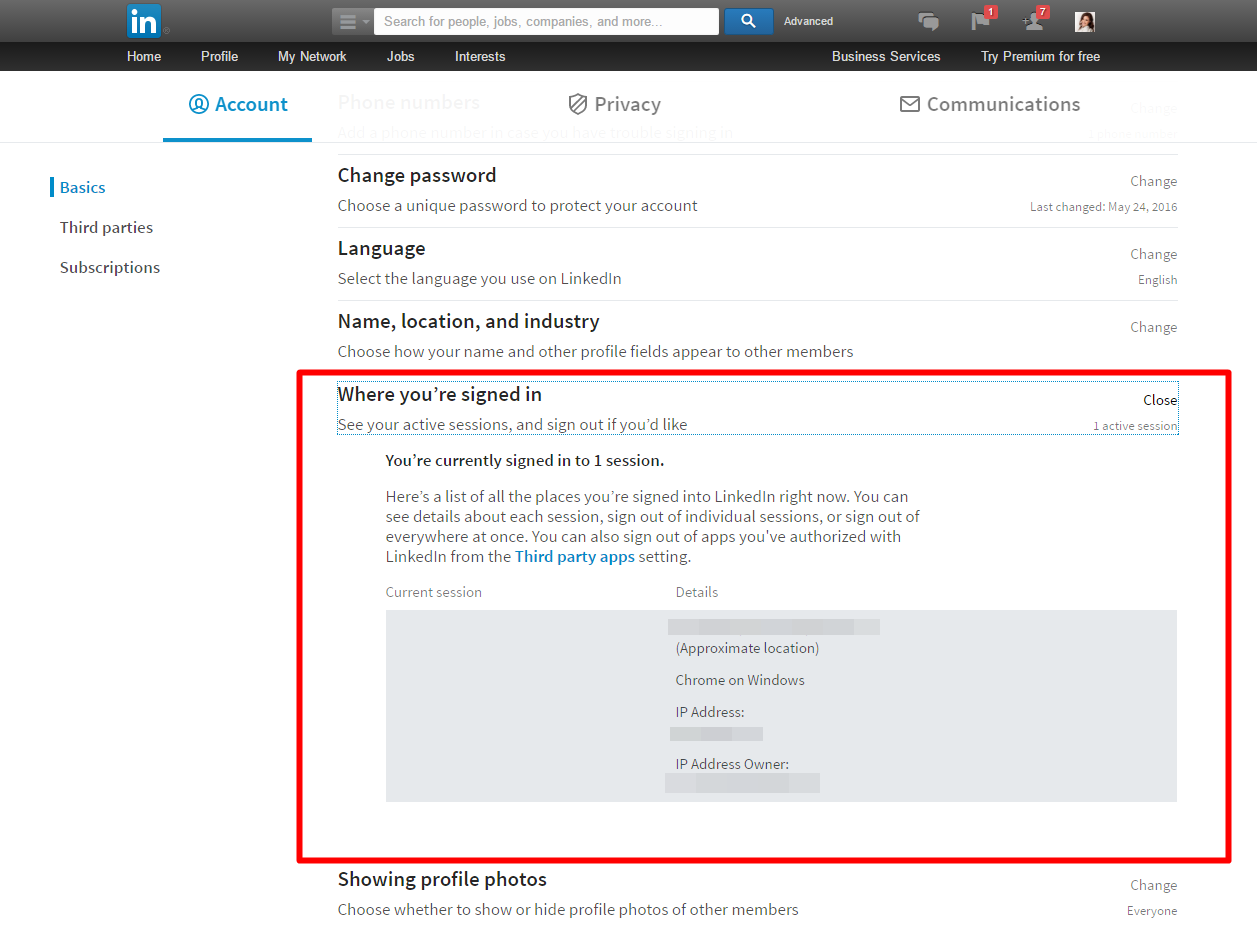
3. Check from what devices you’re still connected to LinkedIn
This option is very useful as it allows you to see which devices you have used to connect to your LinkedIn account. Use it to see what sessions are still active.
It’s a feature that can help you see if you have connected to your LinkedIn account from a publicly shared computer or from a place where you don’t have access to anymore.
In case you notice that your LinkedIn account is still connected on an unknown device, choose the option to disconnect it and sign out as soon as possible from that device. Afterwards, make sure you urgently change your password.
You never know who’s gonna use it to hijack your account or use sensitive data from it.
4. Who do you connect to?
Only connect to people you actually know. Stop adding to your network unknown people or ones that you don’t actually know very well. This only increases the risk of adding possible cyber crooks who only want to use your personal information.
This kind of professional data can be combined with personal information from your other social media accounts, such as Facebook, Twitter or Instagram.
Cyber criminals can use your data for spear-phishing attacks, identity theft, selling on the black market, etc.
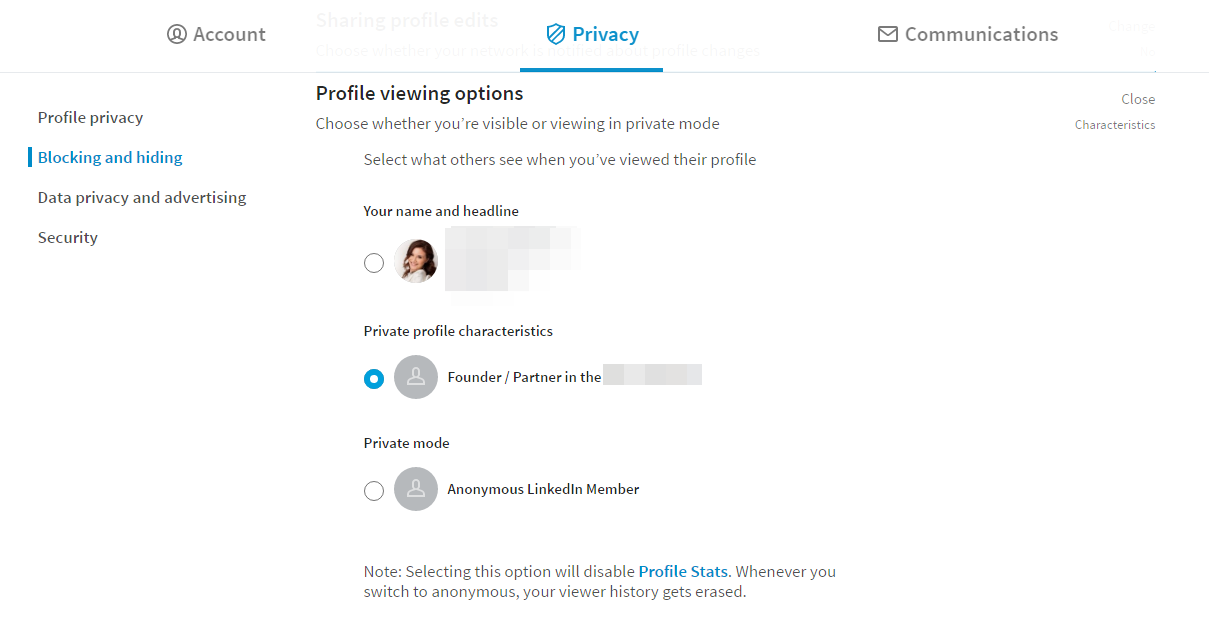
5. Lets keep it private: protect your sensitive information
Online security is closely connected to privacy. As we mentioned before, private information can be used against you if it ends up in the wrong hands.
Therefore, we need to pay close attention to what we reveal to others, especially to unknown people we have connected on our LinkedIn profile.
Adjust the following options to enhance your online privacy:
- Turn On/Off your activity broadcasts. If you want to hide from your connections the changes you choose to do on your profile, the people you follow or the recommendations you make, uncheck this one.
- Select who can see your activity feed. You can hide your actions on LinkedIn or select only some connections who will see your actions. To do this, choose the most suitable option from the drop-down menu (Everyone, Your Network, Your Connections or Only You).
- Adjust what others will see when you view your LinkedIn profile. Do you want your connections to see that you ended up on their account? You can choose to go anonymous (this will also mean that you won’t be able to see who viewed your profile).
- Edit your public profile. How do other people see you? Did you know that you can control how your public profile looks like and how you appear on search engines? This is the place where you can make the necessary changes. You can choose what information you want to make visible online, such as your current or past work places, skills or education. Choose wisely.
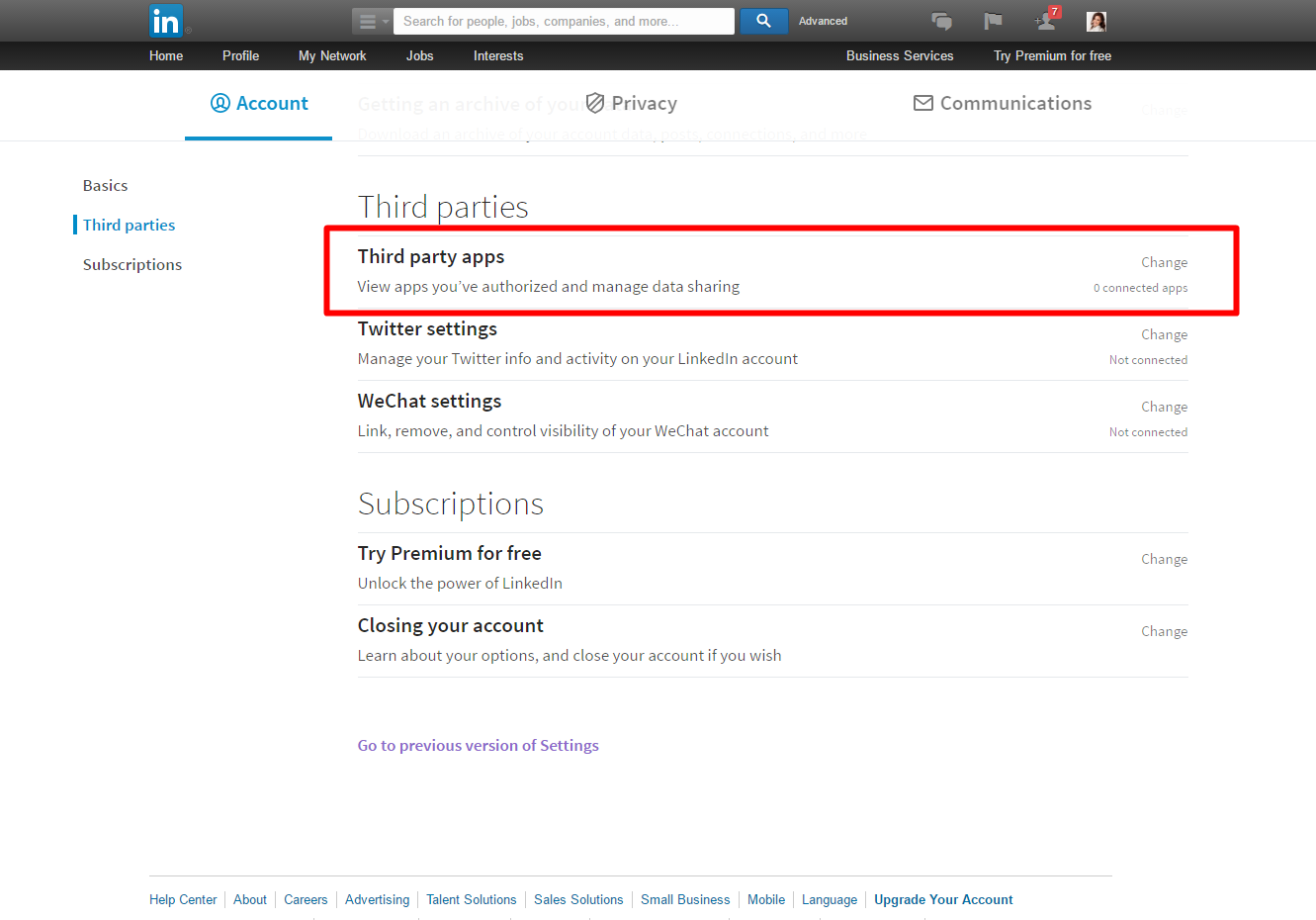
6. Check third-party apps connected to your account
Take a look over what third-party apps you authorized to connect to your LinkedIn account. Those are apps that can access your account and all the data on it.
Only authorize trustworthy apps. Deactivate all apps that you don’t remember or don’t use anymore.
Here are more details on how to master app permissions so you won’t get hacked.
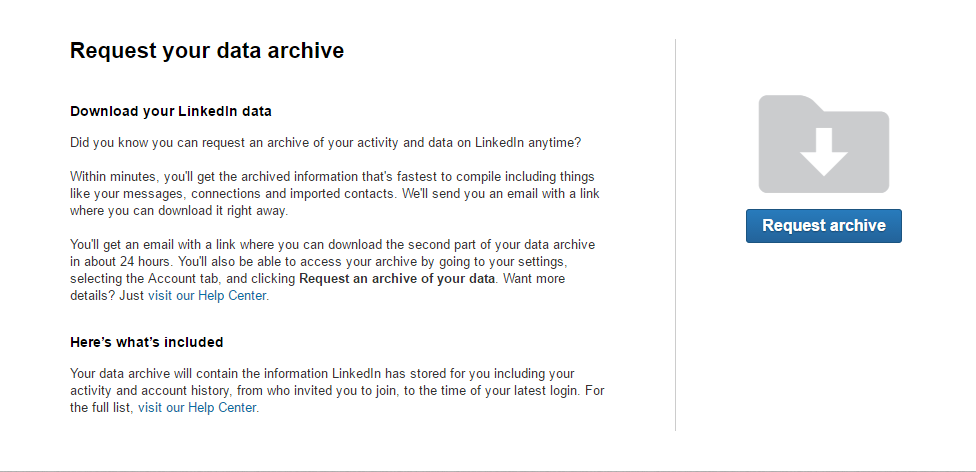
7. Request an archive of your data
Here’s an option that you can use to request LinkedIn an archive of your account data.
It’s an important step for your online privacy if you want to see what information you made available online for others.
From this archive you can also check the IP records from your past login connections, recent searches and other similar details.
8. Don’t forget to sign out of your online account
This is something that everyone is aware they should do, but often forget. We might also tend to think that closing the web browser as soon as we are done with our online activity is enough, but it’s actually not.
It’s especially important after we used a publicly shared computer or a public wireless network.
Otherwise, any person accessing the browser afterwards may connect to our accounts.
We also recommend using a “private browsing” session when you use a PC from a public location and you’re insecure about its security settings. This way, it will prevent the web browser from saving the history and credentials.
[Tweet “Found this useful and extremely easy to follow guide on LinkedIn security:”]
9. Watch out for phishing messages requesting personal or sensitive information
Phishing is a classic, old tactic used by cyber crooks in the attempt to steal your personal information.
Keep an eye not only on your emails, but also on private messages that you receive on your LinkedIn account.
Always look closely at the messages you receive before opening any attachment or clicking on any link from it.
Here’s a comprehensive guide on how phishing attacks work and how to steer clear from them.
10. Keep your software up to date
Last but not least, keep your software up to date. Cyber criminals are taking advantage of their vulnerabilities in order to attack our systems.
By not keeping our Windows operating system and apps up to date (including browsers and plugins or add-ons), we allow them to exploit these security gaps.
You can also use a dedicated solution that will help you keep that software updated – silently, without bugging you for an approval.
Conclusion
LinkedIn is the place where we gather all our professional connections and our past and present colleagues.
We use it as a digital resume to contact potential employers or even employees. But what exactly can we find out about a person by simply analyzing its work experience?
This is the question that we should ask ourself if we want to understand a cyber criminal’s mind.
Our online accounts are extremely vulnerable to privacy breaches and profit-seeking crooks who want to steal our personal information.
Keep this in mind before making any information about you public.
P.S. if you want, you can also follow our LinkedIn company page.

INSTALL IT, FORGET IT AND BE PROTECTED
Download Heimdal™ FREE* This article was published by Aurelian Neagu in November 2014 and brought up to date by Cristina Chipurici in June 2016.


 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management
 Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security