Contents:
While achieving compliance with industry standards is the minimum, it’s not enough to prevent insider threats, supply chain attacks, DDoS, or sophisticated cyberattacks such as double-extortion ransomware, phishing, business email compromise (BEC), info-stealing malware or attacks that leverage the domain name system (DNS).
That is simply because being compliant does not necessarily imply being cyber secure, which is why additional measures must be taken into consideration.
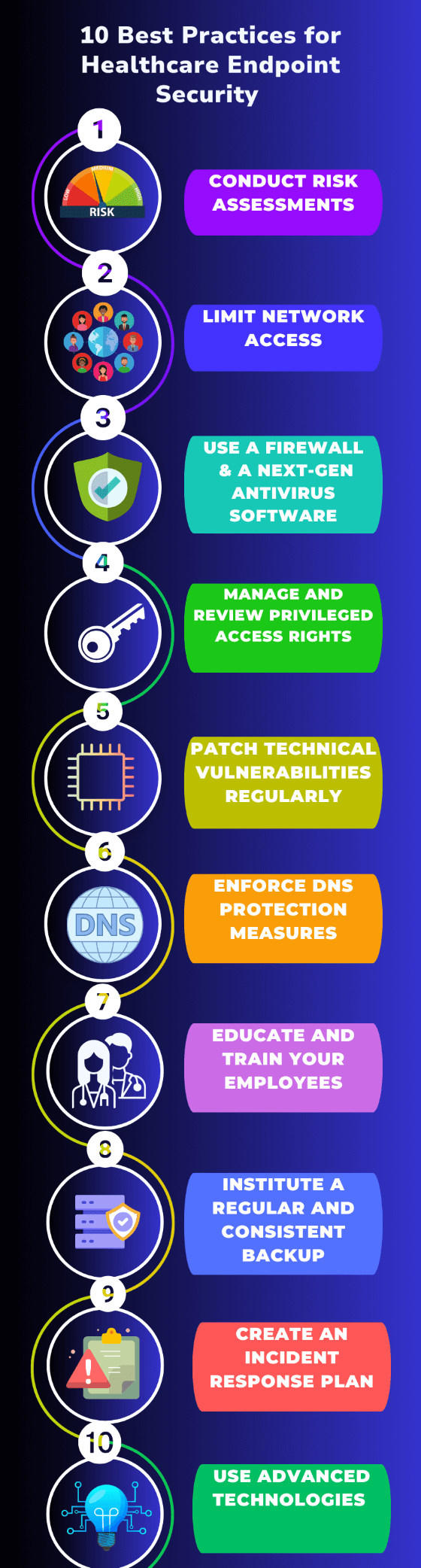
Endpoint security measures make the difference when it comes to protecting sensitive patient data. Here are 10 best practices we recommend for securing endpoints:
1. Conduct Risk Assessments
Conducting regular risk assessments is essential to identify vulnerabilities and potential threats to endpoint security. Healthcare institutions should assess the risks associated with endpoints, such as medical devices, workstations, and mobile devices, and prioritize security measures accordingly.
This includes identifying potential entry points for attackers, evaluating the impact of a potential breach, and implementing appropriate controls to mitigate risks.
2. Limit Network Access
Limiting network access can also help reduce the attack surface and minimize the potential for unauthorized access to endpoints.
Healthcare institutions should employ network segmentation, access control lists, and virtual private networks (VPNs) to restrict network access to authorized users and systems.
3. Use a Firewall and a Next-Gen Antivirus Software
Implementing a firewall is a fundamental step in securing the network and endpoints. Firewalls help monitor and control incoming and outgoing network traffic, filtering out potential threats and unauthorized access attempts.
Installing a next generation antivirus software is also essential for detecting and mitigating malware and other malicious threats. Healthcare institutions should deploy reputable antivirus software on all endpoints and keep it regularly updated.
4. Manage and Review Privileged Access Rights
Controlling and monitoring privileged access can be particularly useful for protecting endpoints in healthcare institutions. Implementing strong authentication mechanisms, least privilege principles, and access controls helps prevent unauthorized access and limit the potential damage in case of a security incident.
Regular review and monitoring of privileged accounts and privileged user activities further enhance security. An automated Privileged Access Management tool would be a great addition to your cybersecurity plan, helping you proactively and easily manage, monitor, and control privileged account access.
5. Patch Technical Vulnerabilities Regularly
Patch management involves regularly updating software, applications, and operating systems with the latest security patches and fixes from vendors. This helps healthcare institutions address known vulnerabilities, reducing the risk of exploitation by cybercriminals. To do this effectively, establish patch management processes, including automated tools for patch deployment.
6. Enforce DNS Protection Measures
Implementing DNS protection is a very effective way to prevent threats leveraging DNS vulnerabilities. Measures like DNSSEC add an extra layer of protection by ensuring DNS data authenticity and integrity, reducing the risk of DNS-related attacks like cache poisoning and man-in-the-middle attacks.
DNS filtering tools can block access to malicious domains, preventing malware distribution, phishing, DNS hijacking, DNS tunneling, fast flux botnets, and more. By integrating threat intelligence into DNS security, real-time detection and response to emerging threats improve significantly.
7. Educate and Train Your Employees
Cybersecurity is a shared responsibility, and humans are often the weakest link in the IT security chain because they are prone to misconduct and can be exploited by malicious actors through social engineering.
That’s why healthcare institutions should provide education and training programs to raise awareness about security threats. This includes training employees on identifying suspicious emails, practicing safe browsing habits, and understanding the importance of strong passwords and data protection protocols.
Healthcare institutions should promote a cybersecurity culture and encourage employees to prioritize security in their daily activities. This includes fostering a sense of responsibility and encouraging reporting of suspicious activities.
8. Institute a Regular and Consistent Backup
Implementing a regular and consistent backup and data recovery process is vital to ensure data integrity and availability in the event of a security incident or system failure.
Healthcare institutions should establish backup procedures for critical data, regularly test the backups to ensure their effectiveness, and store backup copies securely.
9. Create an Incident Response Plan
Develop an incident response plan in case of a cyberattack. This plan should include steps for reporting, containing, and mitigating the attack.
Regular training and simulations will help staff understand their roles and responsibilities, ensuring a coordinated effort in the face of any cybersecurity threat.
10. Use Advanced Technologies that Leverage Threat Intelligence, Behavioral Analytics, and AI
Traditional security measures such as firewalls or antivirus are efficient to an extent but bear in mind that cybercrime is already a well-established business that keeps up with technology.
Modern cyberattacks are no longer signature-based. Threat actors now leverage signature-less techniques to deliver malware, which is why healthcare institutions must keep up with them and employ advanced technologies based on behavioral analytics, machine learning, and artificial intelligence to fortify their endpoint security.
Next-generation endpoint security solutions offer features such as advanced threat detection, real-time monitoring, and behavior-based analysis to identify and prevent sophisticated attacks.
Threat intelligence feeds and security information and event management (SIEM) systems help in detecting and responding to emerging threats promptly. Behavioral analytics can identify abnormal user behavior and potential insider threats, adding an extra layer of security.
Achieve Endpoint Security with Heimdal®
In the midst of the 2023 worldwide financial crisis, healthcare organizations, like many others, are grappling with limited budgets and constrained resources. They are challenged to reduce cyber risks while maintaining costs, striving to achieve the best-case scenario of maintaining current budget levels.
In most cases, however, healthcare businesses are expected to accomplish more with fewer resources. To overcome these challenges, healthcare institutions must leverage automation as a means of amplifying their cybersecurity efforts, enabling teams to optimize their IT Security operations while minimizing security risks.
This is where we come in to help, empowering healthcare institutions worldwide with AI-enhanced, revolutionary endpoint security solutions built to prevent, detect, hunt, and respond to the most sophisticated cyber threats.
Heimdal ® Endpoint Detection and Response
Our comprehensive Endpoint Detection and Response (EDR) module encompasses a suite of five cutting-edge products strategically designed to fortify various vulnerable attack surfaces. And because these offerings are consolidated into a unified platform, users can conveniently manage their security operations through a single agent, streamlining their cybersecurity efforts.
Let’s take a closer look at the main benefits that each of these great products has to offer:
- Next-Gen Antivirus, Firewall & MDM – This product combines the techniques known by both traditional and next-gen Antivirus to detect and remediate viruses, APTs, financial fraud, ransomware, and data leaks. Using a powerful XTP engine, it offers evidence-based information about sophisticated cybersecurity risks and a holistic view of weaknesses, categorized on MITRE ATT&CK tactics and techniques.
- DNS Security – Endpoint: Our DNS product includes a unique feature called Predictive DNS, which uses artificial intelligence and machine learning to scan user traffic in real-time, proactively block infected domains and stop communications with criminal infrastructure, and accurately predict threats with a 97% accuracy rate. It’s fully compatible with every other security product on the market and can be deployed in your environment in less than an hour.
- Ransomware Encryption Protection – Our ransomware-specific product complements any antivirus by scanning the disk structure and detecting processes that initiate file encryptions quickly. It isolates infections automatically and can be used to identify attacker origins and file connections. It is suitable for endpoints, servers, and cloud workloads.
- Patch and Asset Management – A fully automated solution that allows patches and updates to be deployed on the fly from anywhere in the world. Using this product, administrators can patch Linux, Microsoft, and even third-party applications. It also offers automated vulnerability and full inventory management, allowing administrators to easily track their software assets.
- Privileged Access Management – Enables system administrators to automatically escalate and de-escalate user rights and manage permissions, supporting organizations in achieving compliance, facilitating productivity, and effectively preventing the sneakiest of threats: the insider threat.
From endpoints and networks to emails, identities, and beyond, Heimdal has you covered with advanced detection and response capabilities.Request a demo and see it in action!

- Next-gen Antivirus & Firewall which stops known threats;
- DNS traffic filter which stops unknown threats;
- Automatic patches for your software and apps with no interruptions;
- Privileged Access Management and Application Control, all in one unified dashboard










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








