Contents:
What is Patch Tuesday, and why does it matter in our fight against cybersecurity threats?
Simply, it’s when Microsoft systematically delivers security updates for its products on the second Tuesday of every month.
This practice is pivotal for preventing cyber attacks by addressing known vulnerabilities promptly. Our article dissects the significance, process, and benefits of Patch Tuesday for users and IT professionals.
Key Takeaways
- Patch Tuesday is a scheduled event occurring on the second Tuesday of each month when Microsoft releases security updates for its products, enhancing the cybersecurity posture of organizations and individuals by addressing vulnerabilities and exposures.
- The predictability of Patch Tuesday allows IT and cybersecurity professionals to plan and implement long-term security strategies, while post-Patch Tuesday, a phenomenon known as ‘Exploit Wednesday,’ emerges when attackers attempt to exploit the newly disclosed vulnerabilities.
- Efficient patch management involves thorough testing prior to deployment, a clearly structured policy, prioritization of patches based on risk, and the use of automated patch management tools to streamline the process for a variety of devices and systems.
The Essentials of Patch Tuesday
Patch Tuesday, introduced by Microsoft in October 2003, represents a systematic schedule for releasing security updates for its software products on the second Tuesday of every month. This is when Patch Tuesday occurs.
These updates are not confined to the Windows operating system alone. They extend to other core Microsoft products such as Microsoft Office and Visual Studio, ensuring a comprehensive coverage of critical patches.
The choice of Tuesday for releasing these patches was not arbitrary.
Administrators benefit from this dedicated day, as it gives them ample time to prepare for deployment and resolve any arising issues before the weekend.
This well-considered schedule cuts the chaos of daily updates, offering a structured and predictable routine instead.
The Genesis of Update Tuesday
In the early days of Patch Tuesday, the tech giant was struggling with erratic patch releases. Cyber disasters like Code Red and Nimda, along with the trauma of 9/11, precipitated a change in Microsoft’s approach to security patch delivery, driving them to create a predictable monthly cycle.
This shift ushered in a new era of systemized patching, where the second Tuesday of every month marked the arrival of a slew of security updates.
Before the introduction of Patch Tuesday, corporate users used to grapple with issues related to Windows Update.
The lack of a structured routine meant that system administrators had to manage updates and potentially reverse problematic patches across multiple systems.
The advent of Patch Tuesday led Microsoft to improve tools for system administrators, facilitating efficient scanning and identification of computers requiring security updates, hence streamlining the patch deployment process.
What Constitutes a Patch?
When we talk about Patch Tuesday, we are referring to a collection of updates. But what exactly constitutes a patch?
The updates provided during Patch Tuesday encompass:
- Security fixes
- Bug corrections
- Feature refinements
- Enhancements to the efficiency of Microsoft Office and Windows operating systems
While Patch Tuesday primarily delivers security updates, non-security updates, such as software patches for office application enhancements, may be released separately.
In critical situations, security vulnerabilities are addressed through out-of-band patches. These urgent updates can protect against zero-day exploits, which are vulnerabilities actively exploited before patches are available. This strategy highlights the importance of speedy patch deployment in guarding against potential security threats.
The Impact of Patch Tuesday on Security Posture

Patch Tuesday plays a significant role in shaping an organization’s security posture. Regular patching does more than just fix software vulnerabilities; it also brings new features to boost the overall security of the system.
Updating systems promptly during Patch Tuesday is fundamental for addressing common vulnerabilities and exposures (CVEs), fortifying the security posture of organizations and individuals alike.
Patch Tuesday has become a foundational event for cybersecurity and IT administrators, aiding in vulnerability management and serving as a performance benchmark.
The predictable schedule of Patch Tuesday grants technology and security decision-makers the ability to better plan and develop long-term cybersecurity strategies.
Significantly, during severe ransomware attacks like WannaCry and EternalBlue, Microsoft issued patches even for unsupported OSes, showing the company’s commitment to safeguard all systems during a crisis.
From Reactive to Proactive: The Role of Security Teams
Recent changes in the Patch Tuesday process have spurred security teams to adopt a more proactive approach by necessitating additional time to comprehend patch urgency.
Cybersecurity entities like Tenable have enhanced their processes to adapt to Patch Tuesday changes, ensuring prompt and accurate security response through a blend of automation and expert analysis.
Security teams must handle patch management thoroughly, safeguarding not just Windows systems, but the entire range of digital assets across the network.
Proactively patching digital infrastructure, with particular emphasis on public interfaces and devices, is key to reducing vulnerabilities known to attackers.
The shift towards proactive defense against entry-point attacks is indicative of the strategic change in security practices.
The Aftermath: Exploit Wednesday
But what happens after Patch Tuesday?
The day after Patch Tuesday, colloquially known as Exploit Wednesday, often sees exploits for newly disclosed vulnerabilities emerging in the wild.
This day signifies a race between security professionals and attackers, where both parties aim to either mitigate or exploit the vulnerabilities exposed by Patch Tuesday before they are weaponized.
Real-world examples include the incidents in January and October 2023, when attackers exploited CVE-2023-21768 and the CitrixBleed vulnerability respectively, demonstrating the real-world impact of Exploit Wednesday.
One such attack involved reverse-engineering Windows’s afd.sys, identifying a missing pointer check, and creating a kernel exploit within 24 hours of the patch release.
Navigating Patch Deployment: Best Practices
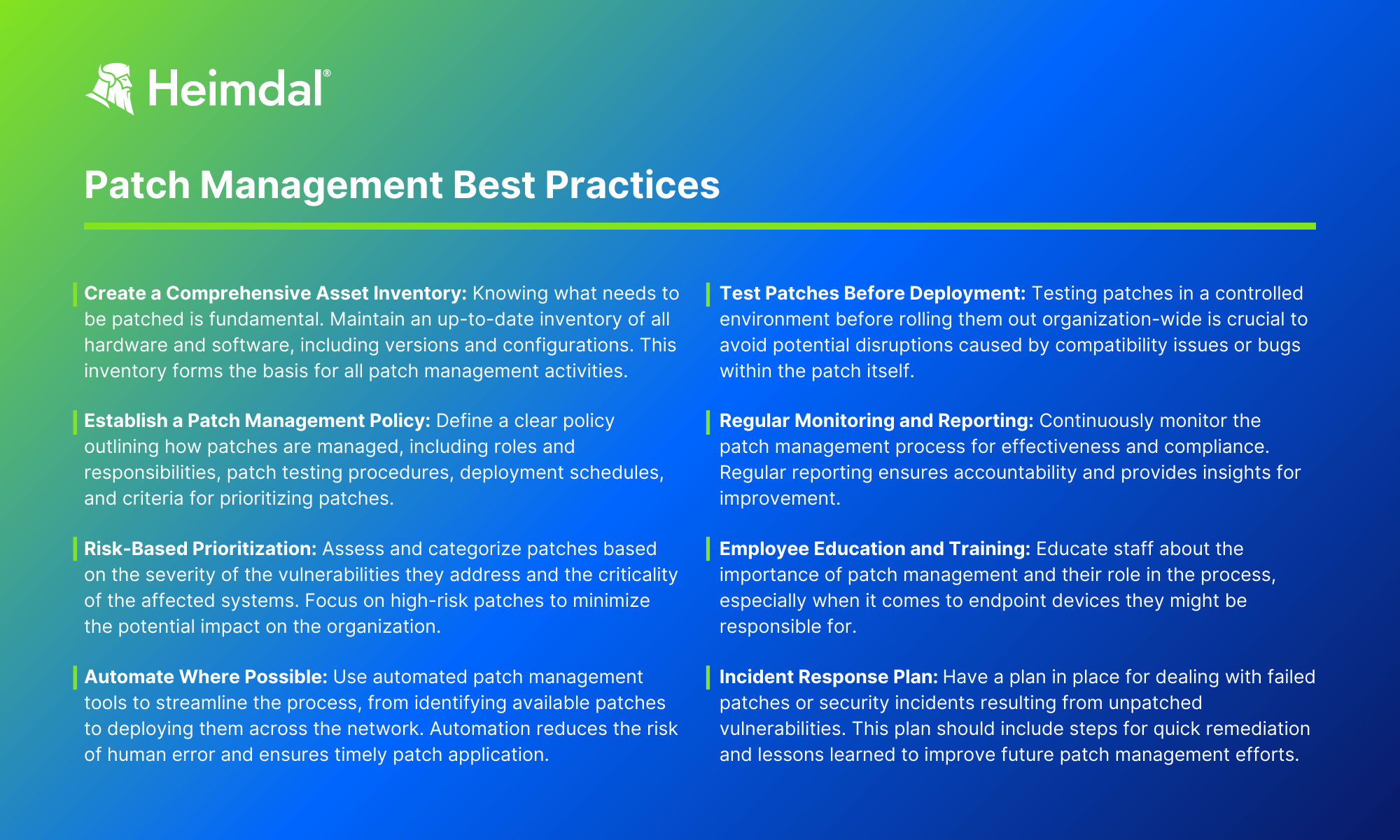
Patch deployment is more complex than it appears. It involves a series of steps, including:
- Establishing routine patch management policies with clear procedures and timeframes
- Ensuring that these policies are well-communicated throughout the organization
- Deploying patches first to a small test group for sandbox testing before broad-scale deployment
- Prioritizing patches by assigning risk levels to assets
By following these steps, you can ensure a more effective and efficient patch deployment process.
Post-testing, it is vital to take backups and promptly apply priority patches, with a focus on operating system updates.
It is equally important to inventory all software and hardware, including security applications and peripherals, to identify necessary patches across the organization.
Keeping detailed records of deployed patches and communicating any changes to staff and stakeholders is critical to maintaining operational clarity.
Testing Before Applying
Before applying patches, comprehensive testing is imperative to ensure the patch does not adversely affect other applications in the target environment.
It’s important to simulate test cases in a controlled lab setting that mimics production systems, then proceed with sandbox testing or deploying patches in batches to a select user group before a full-scale rollout.
It is also essential to verify that a patch can be successfully removed without causing any application or system issues, highlighting the importance of having a backout plan.
Resource allocation for patch testing should prioritize systems that cannot be readily redeployed, such as specialized equipment in healthcare, and consider the severity rating of patches to understand their impact and urgency.
Patch Management Tools and Strategies
In today’s digital landscape, automated patch management tools have moved from being a luxury to a necessity. These tools are essential for:
- Keeping up with security patches and ensuring their timely application
- Automating organizational tasks such as notifying admins of failed updates
- Enabling the creation of complex deployment scenarios
- Supporting bulk patch deployment
- Waking sleeping or turned off devices for patching, simplifying IT administrative tasks.
Technologies like Intel’s vPro platform and Endpoint Management Assistant enhance patch management by enabling features such as scheduled device wake-up for patching and cloud-based remote device management.
Broadening patch management to include non-Windows assets and reallocating resources to patch remote access points are critical strategies, alongside partnering with managed services providers and deploying local update distribution systems to cut bandwidth usage.
The Symbiosis of Patch Tuesdays and Windows Update

Patch Tuesday and Windows Update work in tandem to deliver crucial updates.
Patch Tuesday updates are delivered through the integrated Windows Update service, ensuring that all devices running supported versions of Windows receive relevant security and feature updates.
Feature updates for Windows 10 and 11 have a support period ranging from 18 to 36 months, after which it’s necessary to update to the latest feature release to continue receiving updates from Windows Update service.
The Windows Update service uses the Background Intelligent Transfer Service (BITS) for downloading updates.
This helps to optimize the process by utilizing idle network bandwidth and minimizing disruption.
It’s noteworthy that Microsoft offers specialized versions of Windows, such as the Long-Term Servicing Channel (LTSC), which feature extended support timelines and are impacted by Patch Tuesdays differently than mainstream versions.
Automatic vs. Manual Updates
Windows’ automatic updates are crucial for device health as they provide bug fixes and close security gaps, enhancing the device’s usability and security.
On the other hand, disabling automatic updates can result in missed important security patches and bug fixes, potentially exposing the system to exploits and decreasing its stability.
Despite the importance of automatic updates, users have criticized Windows updates for a lack of control over the timing of the updates, which can lead to interruptions and forced restarts at inconvenient times.
This feedback calls for a balance between security and user convenience, underscoring the need for monthly software updates that include:
- a flexible and user-friendly update mechanism
- options to schedule updates at convenient times
- notifications and reminders before updates are installed
- the ability to postpone updates if necessary
By implementing these features, the Windows OS can provide a better user experience while still ensuring the security of the system.
Keeping Up with the Latest Windows Version

Staying updated with the latest Windows version is key to maintaining a strong security stance.
Older Windows systems become increasingly prone to data breaches over time, since they stop receiving updates that protect against newly identified threats.
Updating to the latest Windows version ensures access to ongoing Microsoft support, including security features and patches that defend against new exploit techniques.
For customers using legacy systems such as Windows 7, Microsoft offers Extended Security Updates to continue receiving security protections after official support ends.
This provision underscores Microsoft’s commitment to ensuring the security of all its users, regardless of the Windows version they are using.
The Broader Influence of Patch Tuesday
Beyond its immediate sphere, Patch Tuesday has had a broader influence on the tech industry.
Its structured approach to releasing patches has inspired other companies to adopt similar strategies.
For instance, Oracle now releases updates quarterly, creating an industry standard for update release management.
The collaboration inspired by Patch Tuesday with hardware vendors like AMD and Intel, as well as other software vendors, has provided a united front against vulnerabilities, amplifying the collective security posture of multiple ecosystems.
Its predictable schedule has become central to technology and security decision-makers, serving as a benchmark for program metrics and key performance indicators in the domain of vulnerability management.
Microsoft’s strategy of implementing Patch Tuesday has marked a continuous evolution of cybersecurity practices within the industry.
Unpacking the Latest Patch Tuesday Updates
The recent Patch Tuesday tackled numerous critical vulnerabilities, offering detailed FAQs, mitigations, and workarounds for each one.
The updates were cumulative for Windows 10 and included all past security fixes along with additional non-security updates.
Specific security updates were released for Microsoft products such as .NET Core, Azure services, Microsoft Office, Edge browser, Dynamics, and core Windows components like Active Directory, DNS, and Windows Kernel.
In addition to the security fixes, Microsoft introduced several new features in the latest Patch Tuesday.
For instance, the general availability of the Hotpatching feature for Windows Server Azure Edition virtual machines was announced.
For detailed information about the vulnerabilities addressed, users can refer to the Microsoft Security Response Center, which publishes bulletins with CVE numbers for each vulnerability available on the Security Update Guide website.
Summary
In conclusion, Patch Tuesday is a vital cog in the wheel of cybersecurity.
It provides a structured approach to releasing security updates, ensuring that all supported Windows devices are protected from the latest threats. The predictability of Patch Tuesday aids organizations in planning their patch management and remediation strategies, thereby fortifying their security posture.
As we continue to navigate the often-turbulent seas of cybersecurity, Patch Tuesday serves as a beacon, illuminating the path towards a more secure digital infrastructure.
Frequently Asked Questions
Why is Patch Tuesday important?
Patch Tuesday is important because it delivers security patches to protect users from new threats and allows system administrators to plan updates efficiently, reducing the risk of cyber attacks. It’s crucial for maintaining system security and stability.
What types of updates do you receive on Patch Tuesday?
On Patch Tuesday, you receive security updates that address vulnerabilities in Microsoft operating systems and software, along with fixes for Microsoft Office applications and other software. Patch Tuesday is the day Microsoft releases these updates each month.
How long has Patch Tuesday been around?
Patch Tuesday, which started in October 2003, was established as part of Microsoft’s Trustworthy Computing initiative to standardize the release schedule of software updates. This regular schedule has greatly benefited users and companies.
What is Patch Tuesday?
Patch Tuesday is a scheduled release of security updates for Microsoft software products, occurring on the second Tuesday of each month.
How has Patch Tuesday influenced other companies?
Patch Tuesday has influenced other companies to adopt a regular patch release schedule, with Oracle now releasing updates on a quarterly basis, setting a standard or update release management in the industry.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security







