Contents:
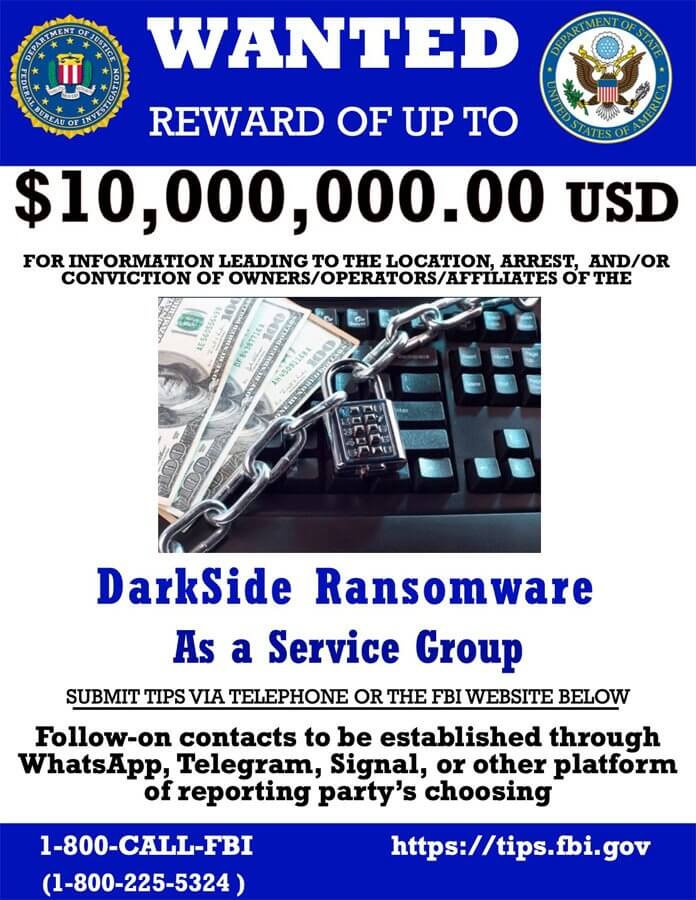
The US government has announced a $10 million reward for information leading to the identification or apprehension of DarkSide ransomware operation members in key leadership roles.
According to the official announcement, the Department of State is also offering an additional reward of $5,000,000 to anyone with information that could lead to the arrest of individuals who intend to take part in a Darkside ransomware attack or an attack that is conducted by one of its rebranded variants, such as BlackMatter.
In addition, the Department is also offering a reward offer of up to $5,000,000 for information leading to the arrest and/or conviction in any country of any individual conspiring to participate in or attempting to participate in a DarkSide variant ransomware incident.
Any kind of information can be sent to the FBI via https://tips.fbi.gov, as well as WhatsApp, Telegram, and Signal.
This reward will be applicable to DarkSide rebrands, including the ransomware group’s most recent BlackMatter campaign, as specified in the statement.
Several Ransomware Gangs Have Changed their Name in the Past
As we already noticed, every time ransomware gangs start to feel the pressure of law enforcement following an attack on a highly sensitive entity, they rebrand under a new name.
In August, we were writing about a new ransomware group calling itself BlackMatter that was claiming to be a successor to defunct Darkside and REvil, two notorious ransomware threat actors responsible for the cyberattacks on Colonial Pipeline and Kaseya.
Other ransomware groups that have previously changed their names are REvil to GandCrab, Maze to Egregor, Bitpaymer to DoppelPaymer to Grief, or Nemty to Nefilim to Karma.
This week, we saw that due to pressure from authorities and recent law enforcement operations, BlackMatter decided to shut down its activities.
The Department of State’s reward on DarkSide ransomware gang demonstrates that changing the ransomware’s name will not prevent law enforcement from chasing and eventually arresting them.
This reward is offered under the Department of State’s Transnational Organized Crime Rewards Program (TOCRP).
The program gives the Secretary of State statutory authority to offer rewards of up to $25 million for information leading to several desired law enforcement objectives, including the arrest and/or conviction in any country of any individuals participating in, or conspiring to participate in transnational organized crime; the disruption of financial mechanisms of a transnational organized crime group; and the identification or location of an individual who holds a key leadership position in a transnational organized crime group.
The US government hopes that by offering such huge rewards, cybercriminals will turn on one another in order to obtain a legitimate, stress-free recompense.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.


 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management
 Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security