Contents:
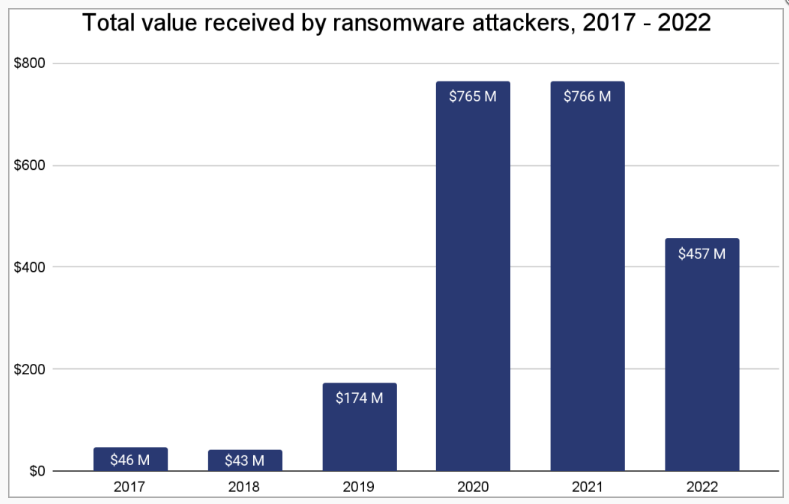
A total of $456.8 million was extorted by ransomware groups from their victims in 2022, down by almost 40% from the previous two years’ record-breaking total of $765 million.
Chainalysis, a company that analyzes blockchain data, has found that the drastic drop in ransomware earnings is not due to fewer attacks, but rather to the victims’ refusal to pay the hackers.
Ransomware attacks on businesses of all sizes increased dramatically in 2022, with thousands of different strains of file-encrypting software discovered and used.
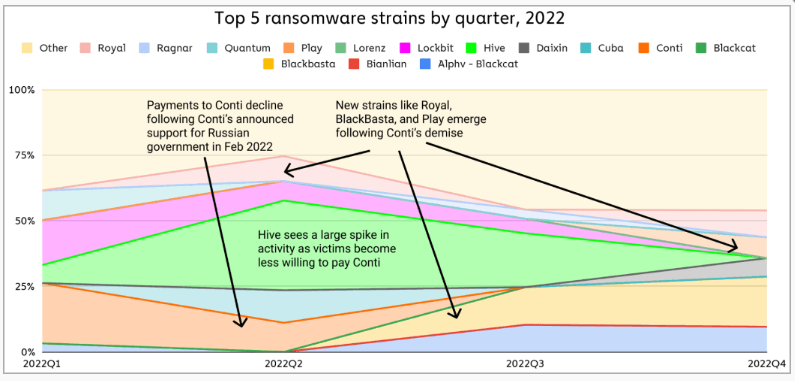
The Conti operation came to an end, and new ransomware-as-a-service operations like Royal, Play, and BlackBasta emerged. However, the LockBit, Hive, Cuba, BlackCat, and Ragnar ransomware operators maintained a pretty consistent flow of victims throughout 2022.
Victims Refused to Pay the Ransom
Ransomware operators use a variety of extortion tactics, such as file encryption, distributed denial of service attacks, threats to expose stolen data, and reports of breaches to data protection authorities, however, an increasing percentage of victims are not paying the ransom.
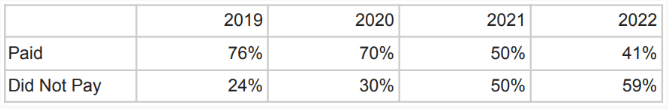
According to data compiled by cyber-intelligence firm Coveware, victim payout rates have been steadily decreasing since 2019.
The majority of ransomware victims (76%) paid the demanded sum in 2019, while the remaining 24% suffered the repercussions. In 2022, however, this trend changed, explains Bleeping Computer, as 59% of victims decided to not pay the ransom.
What Made Victims Change their Behavior?
For the first time, more ransomware victims in 2022 chose not to pay the ransom. This change in behavior reveals a difference in how ransomware attacks are perceived and handled.
Three factors, in particular, can be attributed to this change:
- Victims are aware that even if they pay the ransom, the perpetrators will still destroy the data they stole.
- The public has a more comprehensive understanding of ransomware attacks, and the damage done by these incidents has less of a negative impact on a company’s reputation.
- There is a growing trend of organizations adopting stronger backup procedures, which is a requirement of many ransomware coverage insurers. This allows businesses to recover their IT systems after an attack.
Even though victims are responding differently to ransomware attacks than they were two years ago, totally discouraging the operators by refusing to pay them remains a distant goal. Ransomware attacks will continue to be a concern as long as the ratio of paying victims remains high.
If you want to learn more about ransomware mitigation, we have a dedicated article on the subject: How to Mitigate Ransomware.
If you’re building a strategy to prevent ransomware attacks, take a look at: How to Prevent Ransomware.
And if you want to learn all about the inner workings of ransomware and how to construct a robust anti-ransomware security strategy, you can download, free of charge, our Ransomware Topography e-Book.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security