Contents:
A new cyber-threat is making waves online, as more and more users are starting to report infections. I’m talking about Kolz ransomware, a relatively unknown strain that is as nefarious as better-known names in the industry such as Netwalker or Sodinokibi. But what is it that makes Kolz ransomware so hard to pin down? Below, I have gathered a brief compendium of the available information on it, as well as offered some pieces of advice for your protection. So, if you want to learn what Kolz ransomware is and, more importantly, how to deal with it, then keep on reading.
What is Kolz Ransomware?
Kolz is a ransomware strain that is part of the STOP Djvu ransomware family that was discovered by independent ransomware hunter Michael Gillespie. The operation has been active since at least December 2016, when the first variant was spotted. As of September 2020, as many as 160 variants of Djvu ransomware have been released, if not more. The STOP Djvu cybercrime family has made over 116,000 confirmed victims over the years, with the real estimate being around a whopping 460,000. In fact, more than half of the deployed ransomware attacks from around the globe consist of a form of Djvu. Strains from the STOP Djvu family run on RSA-1024 cryptography, an asymmetric encryption algorithm that generates both public and private keys for each victim. While the former facilitates encryption, its latter counterpart is created for decryption purposes. This method of operation applies Kolz ransomware as well.
How Kolz Ransomware Encrypts Devices
We still aren’t 100% sure of how Kolz ransomware spreads, as its preferred infection medium has not been reported on thus far. However, this type of cyber-threat usually propagates through one (or more) of the following five ways:
- malspam campaigns
- network Trojans
- unofficial third-party tools
- fraudulent files
- peer-to-peer (P2P) networks
Once Kolz ransomware has successfully infiltrated your device, it proceeds to encrypt any pictures, documents, databases, and other files on your device. You can tell which files have been encrypted because an additional .kolz extension is added to their name in the process. So, for example, gerbil.jpg would become gerbil.jpg.kolz. After corrupting all viable files, Kolz deploys a text file entitled _readme.txt in all folders containing encrypted resources. You can see what the document looks like in the image embedded below: 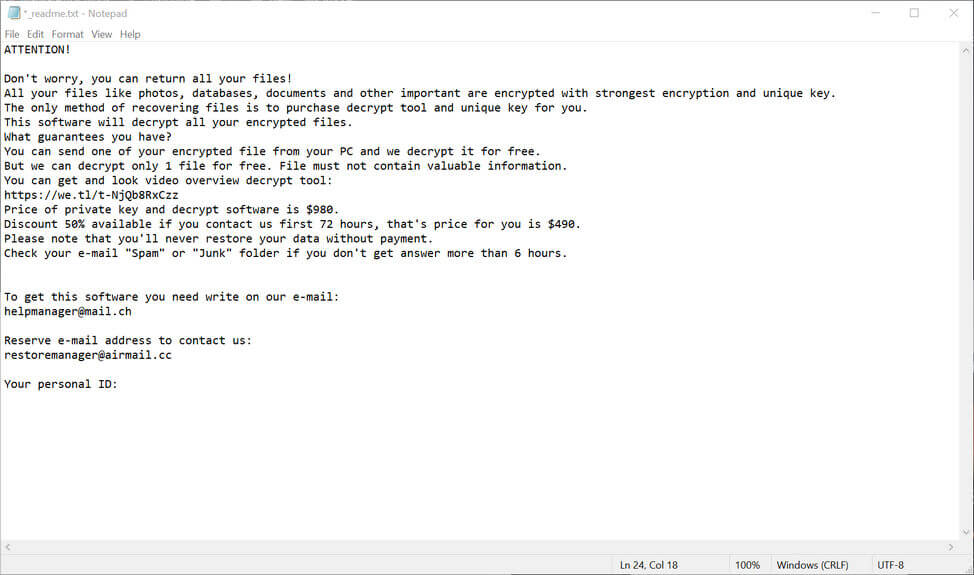
Image Source: MalwareTips
The text in the image above reads as follows:
ATTENTION! Don’t worry, you can return all your files! All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: hxxps://we.tl/t-18R6r7GGG8 Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that’s price for you is $490. Please note that you’ll never restore your data without payment. Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours. To get this software you need write on our e-mail: helpmanager@mail.ch Reserve e-mail address to contact us: restoremanager@airmail.cc Your personal ID:
Please note that the final part of the ransom note reading “your personal ID” has been left blank in the sample. This is because the key is generated individually for each user through the aforementioned method of RSA-1024 cryptography. Reading through the text document, you might be inclined to think that it seems quite amenable, all things considered. However, cybercriminals never mean well and I strongly advise not putting more money into their pockets to further fuel their illicit activities. Simply put, do not pay the ransom. It’s not worth it. Instead, my recommendation is to either look into how to remove Kolz ransomware or how to prevent an attack entirely. In the following sections, I will discuss each of these topics in more depth so that we can establish what can be done about this particular strain of Djvu. So, without further ado, let’s get into it.
How to Remove Kolz Ransomware
First and foremost, let’s see how you can deal with a Kolz ransomware infection. Whether you are at home or within your company network, the ensuing three steps are vital for a successful cleanup operation.
1. Isolate the Infected Device
Quick response is essential when you’re dealing with any ransomware infection, including one involving the Kolz strain. Therefore, the initial action you want to take is to isolate the infected device to prevent the threat from spread to other computers that operate in the same local network.
- Disconnect the machine from the Internet by unplugging the Ethernet cable. If your computer is coupled to a Wi-Fi network, I recommend disabling the connection from your computer’s Control Panel.
- Eject any external storage devices by going to My Computer, right-clicking the drives in question, and selecting the Eject option. This stops Kolz ransomware from encrypting them as well.
- Log out from the cloud to prevent cybercriminals from hacking applications and data stored there as well. You might even want to consider de-installing its adjacent management software.
These are the three stages that you need to follow to ensure that the infected machine is completely offline. After achieving this, you can proceed with the removal process.
2. Identify the Encrypted Files
After you’ve ensured that the infected device(s) is no longer connected to others in the network, it’s time to ascertain the extent of the damage that was done. In the case of a Kolz ransomware attack, doing so is relatively easy. As previously mentioned, files encrypted by this STOP Djvu strain will have a .kolz extension addended to its regular one of .jpg, .doc, and so on. What is more, every folder containing one or more corrupted files will have the ransom note located in it as well.
3. Look for a Kolz Ransomware Decryptor
In October 2019, a STOP Djvu ransomware decryptor for 148 of the cyberthreat’s known variants was released. However, the tool is efficient for infections leading up to August 2019, which means that nobody infected after that date can use it. Unfortunately, Kolz ransomware is not a version of Djvu that can be decrypted with the help of free tools just yet. Furthermore, searching the web for one at random might even add insult to injury. In June 2020, security researchers discovered that a program pretending to be a Kolz ransomware decryptor was actually a fraudulent software delivering a ransomware strain known as Zorab. For this reason, I suggest getting your decryptors from verified sources only. For example, the BleepingComputer site has a constantly updated section on this very topic where you will find the latest releases, as well as any other useful info on the subject. Or, you can give Heimdal Security’s very own blog article on free ransomware decryption tools a try. We also vouch to keep you posted regularly and we’ll add the Kolz ransomware decryptor there as soon as it comes out. In the meantime, what you can do in the case of infection is to contact the relevant cybercrime authorities in your region or reach out to competent third-party vendors that can help you deal with mitigation.
How to Prevent a Kolz Ransomware Attack
1. Perform Routine Data Backups (Online and Offline)
Creating copies of crucial data in the cloud is a known security procedure. Still, cyberattackers can get to you there as well. This is why I cannot stress the importance of an offline data backup system enough. At the end of the day, nothing competes with the good ol’ flash drive, external hard drive, SSD, or HDD. In addition to this, you should also consider how well the files on your machine are protected. Backups can only take you so far. A viable option, in this case, is spreading your data across several partitions. In this way, it will be harder for hackers to reach all of it before you take note and kick them out.
2. Familiarize Yourself with Social Engineering Practices
Above all else, ransomware, as well as malware, Trojans, and other associated threats, spread through clever social engineering practices. Cyberattackers have become increasingly cunning nowadays. They have the ability to not only mimic the email addresses of people you know, but also the imagery of beloved brands, service providers, or institutions. Even experienced Internet users can sometimes fall prey to this type of ruse. For this reason, you should always keep your eyes peeled if you are an active Internet user at home or in the workplace. When it comes to phishing emails, incorrect or misleading spelling attempts (such as using lowercase “L” instead of capital “i” and vice versa) are the number one thing you look out for. The same goes for seemingly familiar branding attempts. Slightly darker or lighter color schemes, suspicious links, and the lack of any trademark or copyright symbols are some other common telltale signs you are dealing with a malicious scam.
3. Always Deploy Patches and Updates Immediately
Unpatched or outdated software and applications can become a gateway for ransomware in the blink of an eye. Malicious actors are notorious for shrewdly exploiting system vulnerabilities, which is why you should always keep your devices up to code. A solution such as our very own Heimdal™ Threat Prevention Home can help you with closing those mean security holes as soon as updates are deployed. 
4. Install a Next-Generation Antivirus Solution
Let’s circle back for a minute. Heimdal™ Threat Prevention can help you protect your home against ransomware and other malicious threats, but it can’t do it alone. My recommendation is to pair it with a next-generation antivirus solution, such as Heimdal’s Heimdal™ Next-Gen Antivirus Home. Easy to install and light on your device’s resources, it is the ideal at-home defense against APTs. Together with Foresight, Vigilance forms the Heimdal™ Premium Security Home cybersecurity suite that can stop even the most robust ransomware and malware from gaining unlawful access to your precious data. A holistic solution, Premium is both proactive and reactive, offering you all-around protection from any form of online harm.
To Sum It Up…
As part of the notorious STOP Djvu family, Kolz ransomware is a cyber threat to be reckoned with. Albeit relatively unfamiliar, it’s worth taking note that it already made a few victims among online users. And with a compatible decryptor nowhere to be found just yet, prevention remains your best bet, as always.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








