Contents:
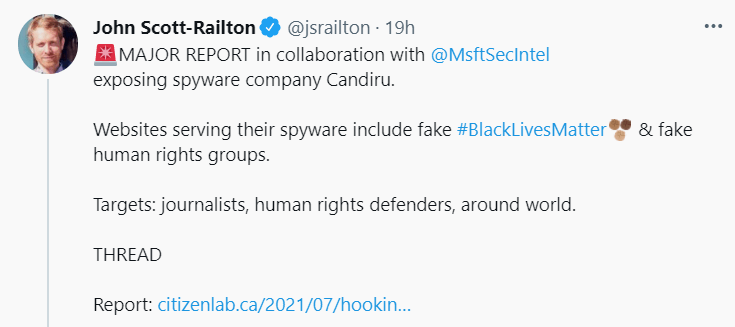
A new report by Microsoft and Citizen Lab has tracked DevilsTongue spyware, a threat that targets zero-day vulnerabilities in Windows systems. Threat actors seem to belong to an Israeli-based spyware company by its name Candiru or Sourgum.
What Is a Spyware?
Spyware is basically a kind of malware whose goal is to steal users’ private data and remain undetected. It can store keystrokes or browser history and gather sensitive data such as credentials and banking info. These are sent to the malicious hacker’s servers to perform cyberattacks.
How Does This DevilsTongue Spyware Work?
According to Bleeping Computer, DevilsTongue malware operated like this:
- It was sent to users’ computers through an exploit chain.
- This exploit chain took advantage of flaws in Windows operating systems and common browsers.
- The hackers’ method it’s based upon the theft of users’ files, Signal messages on Windows devices stealing, and decryption.
- Cookies and credentials stored in Internet Explorer, Safari, Firefox, Opera, Chrome, and LSASS were also targeted.
- Hackers can also collect sensitive data, read messages and withdraw pictures from cookies related to Twitter, Gmail, Yahoo, Facebook, Vkontakte, Mail.ru, and Odnoklassniki.
- Another capability is that it is able to spread malicious links in a row: every person that has talked with the victim on social channels could receive a malicious link on behalf of the affected user.
Who Is Behind the DevilsTongue Spyware?
Microsoft was aware of the issue when Citizen Lab informed them of the malware linking it to an Israeli-based firm Sourgum.
CitizenLab wrote a report on this and Microsoft Threat Intelligence Center (MSTIC) worked together with Microsoft Security Response Center (MSRC) to discover that Candiru or Sourgum exploits CVE-2021-31979 and CVE-2021-33771, two privilege escalations vulnerabilities that Microsoft patched on 13th of July.
CitizenLab also says that the Israeli-based company that is supposedly linked to DevilsTongue Spyware is
A secretive Israel-based company that sells spyware exclusively to governments. Reportedly, their spyware can infect and monitor iPhones, Androids, Macs, PCs, and cloud accounts.
What’s the Impact of DevilsTongue Spyware?
750 websites are linked to Candiru’s infrastructure, built to simulate media and advocacy organizations’ domains related to Black Live Matter and Amnesty International movements.
Microsoft noted that the DevilTongue Spyware’s victims seem to be particular individuals and include
more than 100 victims around the world including politicians, human rights activists, journalists, academics, embassy workers and political dissidents.
Mitigation Measures Provided by Microsoft
Microsoft has provided some mitigation measures to fight DevilsTongue spyware including advice for users when they click on a link from untrusted parties to use a virtual machine that provides an isolated environment. Windows 10 has such kind features within: Credential Guard, for instance, that blocks credentials’ theft.
The protections we issued this week will prevent Sourgum’s tools from working on computers that are already infected and prevent new infections on updated computers and those running Microsoft Defender Antivirus as well as those using Microsoft Defender for Endpoint.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security