Contents:
One might think that threat actors target only big enterprises, so small businesses are left out of sight. This is unfortunately not true. Cybersecurity for small businesses should be a top priority for all organizations.
Statistics show that businesses that have less than 100 employees are being affected by 76% of cyberattacks. Why? As threat actors know that these are easy to get to, due to a lack of proper security system protection and expertise. These organizations work on a budget. Small businesses do not afford to invest in experts and tools to keep them well protected and do not have the time to be informed on cybersecurity. Disregarding cybersecurity for small businesses could lead to real damage. Thus, they should pay $3,533 per employee in case of a cyberattack. The life of a data breach takes 279 days because risk can be identified in 206 days and contained in 73 days.
Recently, cyberattacks have grown, especially with the working from the home policy during pandemic times. If you are strongly hit by a cyberattack, this might let you with one option: to be out of business, because the costs can be too high to stay in. If you don’t know where to start, you don’t have the money for it or you just simply don’t have time, read the below guide that will surely offer you a fresh perspective on cybersecurity for small businesses.
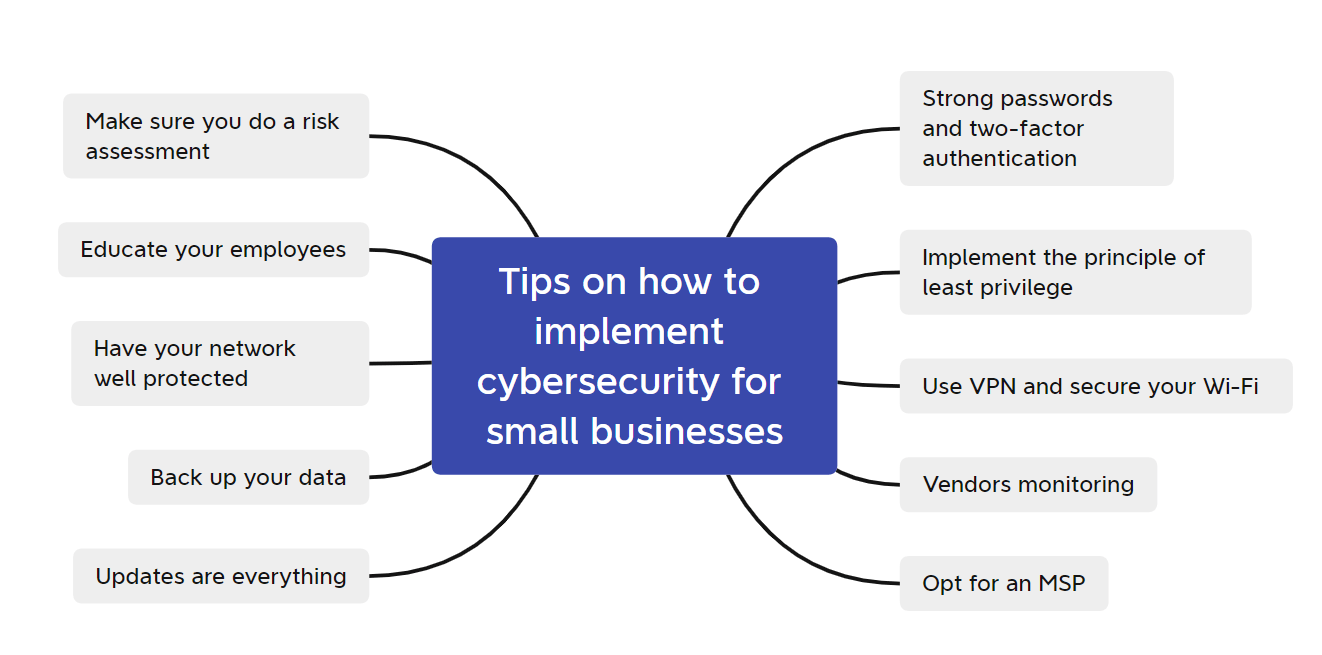
Tips on How to Implement Cybersecurity for Small Businesses
#1 Make sure you do a risk assessment
A risk assessment is the first step when you want to strengthen cybersecurity for small businesses. See where you are vulnerable and what you need to start working on. You can identify the most important data such as clients’ records, financial information, intellectual property for instance, and perform an audit on everything. You need to be aware of the method you use to store data, if this is a secure way, who can access it, and make changes if necessary.
There is a basic equation for risk: Risk = Threat x Vulnerability x Impact. The risk formula is impacted by your choices, if you have the right tools and update software regularly, you limit vulnerability. If you do all the steps that will follow below, you limit the impact.
You have to treat the cause, not the effects. So, don’t wait until the next data breach to start knowing your organization’s vulnerabilities and where it needs improvement in terms of safety. Small business cybersecurity is a must.
#2 Educate your employees
It all starts with your employees’ awareness. If you want to protect your business, make sure the people that work with you are well informed on cybersecurity topics such as: how to make sure they have a strong password, tips to avoid phishing e-mails, and so on. Make them vigilant.
Basic security practices and policies for small businesses should be straight off implemented. Your employees must be aware that strong passwords mean using unique, complex, often changed, and long enough ones. A phishing e-mail that determines an employee to click on a malicious link can be easily avoided if they look for mistakes: the key is in the details. Usually, bad grammar, misspelled words, the writing styles, the fonts, if the e-mail asks to click on a link or to send money somewhere, these all should make them suspicious and think twice, in order not to click on every link they receive and make them attentive to the consequences of violating the security policies of the organization.
A fake phone call that asks for private information should not be trustworthy, an USB in the organization’s parking lot with a “sensitive data” label on it should not be inserted into anyone’s computer out of curiosity before checking who’s the owner. Thus, it’s a win-win situation for everybody: they do not make deliberate mistakes, you are protected.
This is the best way to avoid one of the main threats for small businesses: social engineering, where people are psychologically manipulated to do what the threat actor wants them to do as making them provide their credentials, sensitive info, open a compromised attachment that will deploy a malware, etc.
Another tip would be to invest in small business cybersecurity pieces of training for your people. Especially in these times of pandemic, when it is of vital importance to maintain hygiene in cybersecurity for small businesses. This, in long term, will surely pay off.
#3 Have your network well protected
How? Through good tools that promote cybersecurity for small businesses.
Have a good next-gen antivirus, have a firewall, have a threat prevention tool, and a good ransomware encryption tool. Here’s why each of them is worth it.
Traditional antivirus is nowadays not enough, as the simple, code-base detection algorithms are not powerful enough against the new malware. Keep up with the new threats with a next-gen antivirus that has firewall integration too. You can thus identify everything that’s new or sandbox everything suspicious.
A good threat prevention tool is better than an antivirus, because it hunts, prevents, and blocks threats before reaching the network. It can analyze the traffic and behavioral patterns and neutralize everything a traditional tool will not do. Make a combo, using it together with the next-gen antivirus, and reach ultimate protection!
A ransomware encryption tool will protect you against ransomware, you know, that malware that encrypts all your data and then asks you for money to have it back. How? It identifies previously unknown malicious activity and prevents it from causing a DDoS attack on your sensitive data.
#4 Back up your data
This should be a motto. If you want to avoid the damage caused by a ransomware attack, this is the winning method besides a ransomware encryption protection tool. Because, if ransomware affects your organizations and encrypts all your private files and asks money for their recovery if you backed them up somewhere else, then the IT guys should only remove the malware and restore the data from the backup place.
I know that there is a debate about whether you should pay a ransom or not. The answer is that this is risky. Even if you pay it, you do not know for sure your valuable data will come back to you, so a backup solution is vital to ensure your small business cybersecurity.
You can do a full backup, by taking all your information and moving it somewhere else, or an incremental backup by storing it gradually. So, if there’s anything new since the last time you made a backup, you store that data too. This way financial documents, databases, electronic spreadsheets, HR, or accounts payable/receivable files are in a safe place. Make sure you have a tool that performs an automated backup to save you from forgetting to do it and check regularly if your backup process is still working properly.
You can use tools like EaseUs or pCloud or additionally, store the data offline too using a physical backup.
In times of working from home, like this pandemic one, cloud-based collaboration tools are also useful. They will allow you to store and share files, track progress, exchange files, monitor the status of your ongoing projects, measure progress, create to-do lists, send instant messages, make phone/video chats, and so on.
Microsoft Teams
It offers a 6-months free trial for Microsoft Teams in an Office 365 trial. Share documents and keep in touch easily with your team.
Cisco WebEx
It offers 90-days unlimited usage. There are no time restrictions and provides also and toll-call dial-in in addition to existing VoIP capabilities.
Zoho Remotely
Which has 11 applications (ranging from video conferencing, instant messaging, business presentation, to project management and remote support) is a good cloud-based tool too.
#5 Update your software regularly
You will not enjoy the latest security measures if your software, machines, and devices are not updated. Threats are constant, same should be the software updates. You should keep up with everything that changes by enforcing software updates as soon as they are available.
Every software has regular updates and patches security experts are working on providing a safer program. Therefore, updates are of absolute importance because they cover your small business cybersecurity with real-time protection and promote better application features designed to make your life easier.
Just look at the PrintNightmare vulnerability in Windows Spooler that let hackers perform remote code execution and exploit local privileges. Microsoft provided updates to mitigate these. So, keep an eye on updates and make sure you implement them right away.
#6 Strong passwords and two-factor authentication
Strong passwords and multi-factor authentication are a must if you want increased cybersecurity for small businesses. Your employees could use passphrases instead of passwords and use a password manager to store them. Similar to a password and used to check a system or program access, a passphrase is how you gather together random words and combine them in a sentence easy for you to remember that makes hackers’ life difficult. A password manager will help your employees remember just one password to access everything they need, so they only need to remember one unique, complicated password.
Common sense tips here: employees should not share passwords, should not store them in unsafe and visible places, and should not let their computers unlocked while going out for coffee.
Multi-factor authentication (MFA) such as random pin, biometrics, physical token, an authenticator application, or SMS build more layers of security. The two-factor authentication method is the most common MFA method. If your employees have to access sensitive data and have to follow two steps to do it and hackers managed to compromise the first step, they still do not have access to anything, as they cannot bypass the second security step.
Another good technique in terms of small business cybersecurity is the Bruce Schneier method for creating a good password by taking the first two letters from each word of a sentence and create a strong password: cybersecurity for small businesses would be Cyfosmbuwo.
Password policies should be applied also to any employee’s mobile device that connects to the company network.
#7 Implement the principle of least privilege
You might wonder what that is. Well, the principle of least privilege is a crucial rule in terms of cybersecurity for small businesses. It means to grant users the minimum access they need to perform an assigned task. Look at the sysadmin accounts that have unlimited privileges. If they will use one-time-use passwords or just store the credential in a digital vault then they can enforce this concept.
Or if an HR employee needs access to the database, he does not need access to payroll files to pull out a report. So, every employee should be granted minimal rights to do what they have to do and for a limited time only. Thus, you avoid data leakage, make sure something malicious is not installed in a place where unauthorized employees normally should not have access.
#8 Use VPN and secure your Wi-Fi
A VPN (a virtual private network) works like a shield on a public internet connection. It creates a private network and your employees are protected and anonymous while surfing on the internet. If an employee accesses sensitive data from public Wi-Fi, the VPN will protect the data.
Also, home Wi-Fi should be encrypted and the default router password changed. And an enterprise one should be always encrypted and hidden.
#9 Vendors monitoring
Your vendors can have access to a lot of information that you are not aware of. Check what data your vendors have access to, how it is used, and if they have the necessary security measures to ensure cybersecurity for small businesses.
#10 Opt for an MSP to enforce cybersecurity for small businesses
If you don’t have the money to pay for security experts to take care of your organization, you can always choose an MSP. It can be more efficient and less expensive in terms of costs and expertise. A manage service provider is basically a company that helps you remotely manage the IT infrastructure by providing a computing framework platform. Obtain IT expertise with less money!
Impact of an Attack on Small Businesses
You should start to implement the above-listed measures to avoid devastating damages in the matter of small business cybersecurity. In this jungle of cyberattacks, you can be out of business in a wink.
Through a lot of tactics like phishing e-mails, malware such as ransomware, spyware, trojans, and others, the impact of cyberattacks is huge. If you are hit by a ransomware attack and all your organization’s data is encrypted, then your network is paralyzed and you have to limit threat actors’ access to your data by just closing off the business.
Then, recovery and fines can be very stressful. It will cost you a lot to recover from a cyberattack, to notify all your customers, or explain and prove to your data protection authority that this was not a GDPR issue, so you’ll be fined and suffer penalties.
Your data can be destroyed, leaked online, you lose money because your company is not operational anymore and you also lose reliability. Clients are skeptical. If they see: oh, this company was hit by a cyberattack because of poor security measures. How can I put my trust in it? How can I be a client of this organization? A damaged reputation is really, but really hard to restore.
And last, but not least, keep in mind that you could be one of the third parties working for a big company and that hackers hit you to reach the parent organization. So, your organization will be just a tool in their hands. You not only lose your business but your partners too.
Wrapping up…
This being said, now you can see how important is cybersecurity for small businesses and why these are actually the most targeted nowadays. We also offer cybersecurity solutions and have a unique approach, because we provide a unified dashboard where you can manage all the protection solutions that work in synergy. Threat Prevention, Next-gen Antivirus, Patch Management, Privileges Access Management, Ransomware Encryption Protection, and many more in one place. It’s good to invest in the finest tools to avoid future damage. If this makes you raise eyebrows, take a look at our website.

Heimdal® Network DNS Security
- No need to deploy it on your endpoints;
- Protects any entry point into the organization, including BYODs;
- Stops even hidden threats using AI and your network traffic log;
- Complete DNS, HTTP and HTTPs protection, HIPS and HIDS;
We also have a cybersecurity course for small businesses that you will surely enjoy.
Be a step ahead of hackers and start implementing small businesses’ cybersecurity best practices today!
Feel free to drop a line below if you have any suggestions or why not, if you’d want to share with us how much you liked this article!










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security