Contents:
Recently, Delta Electronics, a Taiwan-based company, and provider for big names like Tesla, Apple, Dell, or HP, has announced that it was impacted by a cyberattack.
More Details on the Delta Electronics Cyberattack
According to the statement the company released, only non-critical systems were impacted by this incident. It seems that the attack was identified on the 18th of January by the AdvIntel “Andariel” platform.
The enterprise is now conducting an investigation and recovery process with the help of third-party security experts. Meanwhile, an attempt to restore the impacted system is ongoing.
Government law enforcement agencies were also notified about the incident in order to to take part in the investigation.
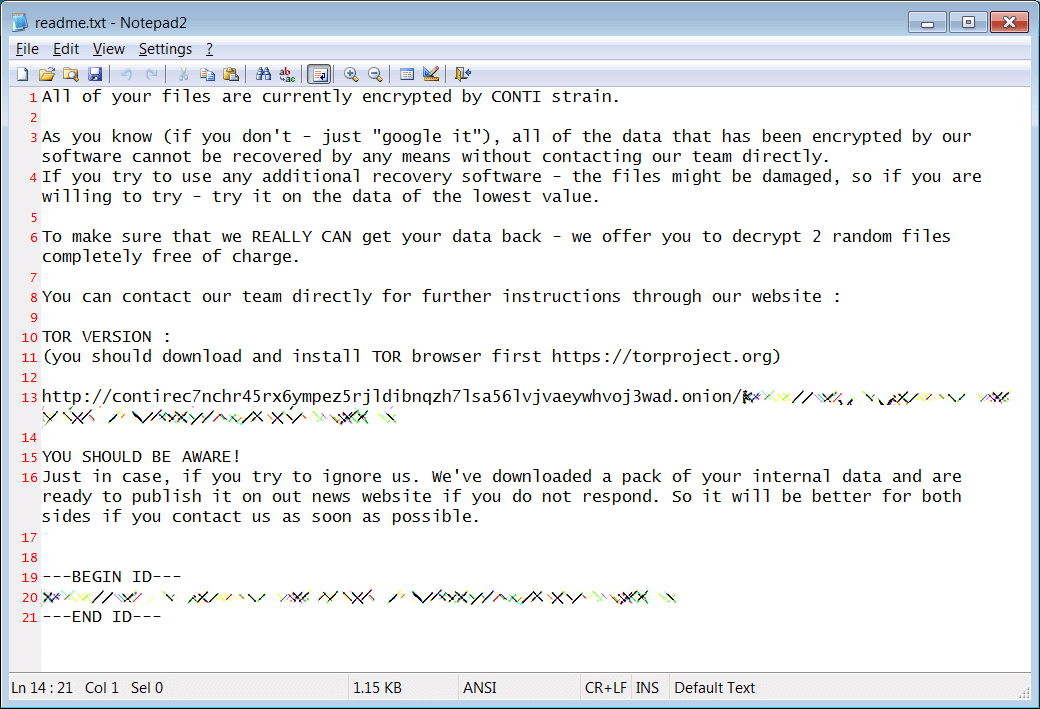
Information on the identity of the cybercriminal was not provided by Delta, but according to CTWANT, an information security enterprise discovered on Delta’s network a sample of Conti Ransomware. Below, there is an illustration of the ransom note:
The Company Is Reportedly Asked to Pay $15 Million Ransom
According to BleepingComputer, there were some negotiations carried on between the impacted company and the hackers, the latter giving the information that 1,500 servers and 12,000 computers were encrypted. Reportedly, the cybercriminals asked for a ransom amounting to $15 million in order to provide the decryption key along with ceasing the stolen data leakage. What’s more, the hackers even offered a discount if the payment is done in a timely manner.
Investigation Ongoing but Website Still Down
Allegedly, the collaboration of the impacted company Delta Electronics and the security teams from Microsoft and TrendMicro is still in progress. According to the enterprise, the cyberattack did not have any impact on the production, however, a week has passed since the attack, and their website it’s still down.

Until the main website is up again, there is a workaround for customers. They can use this alternate domain.
Vitali Kremez, the CEO of AdvIntel, shared with Bleeping Computer that
The Conti ransomware group revealed a specific pattern part of the Delta attack leveraging Cobalt Strike with Atera for persistence as revealed by our platform adversarial visibility. Certainly, this attack is reminiscent of the REvil Quanta one affecting one of the Apple suppliers.
More Details on Conti Ransomware
Conti ransomware is a very popular figure in the nowadays threat landscape.
As my colleague, Dora thoroughly explained in her article “What is Conti Ransomware?”, this malicious actor stands out through its ability to perform data encryption and network propagation. Their usual attack is based on phishing techniques to eventually deploy TrickBot and BazarLoader Trojans. The group also employs double-extortion techniques, blackmailing the impacted entity to leak their private data if the ransom is not paid.
Among its most famous attacks, we can mention JVCKenwood, the Japanese multinational electronics enterprise, the City of Tulsa, and Ireland’s Health Service.
How Can Heimdal™ Help?
Ransomware is one of the most dangerous threats to business-critical assets nowadays. Keep it away with our Ransomware Encryption Protection tool, which protects against malicious encryption attempts while a ransomware attack is going on, making sure that your business does not become a victim of data loss and exfiltration.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








