Contents:
Threat actors used an unnamed cloud video hosting service to inject malicious scripts into over 100 real estate websites owned by the same holding company. The goal of this supply chain attack was to steal private information contained in website forms.
These malicious scripts, also known as skimmers, are becoming increasingly popular and are often injected into compromised websites in order to steal sensitive data provided by users on the targeted website. Skimmers are frequently used on checkout pages for online stores to steal payment information.
How Does the Attack Work?
According to BleepingComputer, Palo Alto Networks Unit42 spotted a new chain attack in which hackers were exploiting a cloud video platform feature to inject skimmer code into a video player. The moment a website embeds that player, the malicious script is also embedded, compromising the site.
It appears that the supply chain attack was highly effective since more than 100 websites have been impacted by the operation, according to the cybersecurity company. The researchers alerted the cloud video provider and assisted the compromised websites in removing the malicious code.
The cloud video hosting service used in the attack enables users to create video players that may be customized with custom JavaScript scripts.
As explained by BleepingComputer, one such customized video player, which is frequently embedded in real estate websites, used a static JavaScript file hosted on a remote server.
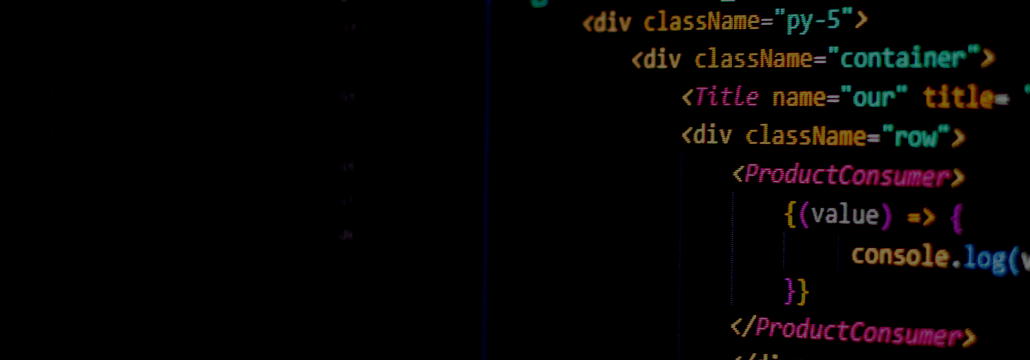
According to Unit42 experts, the attackers managed to gain access to the upstream JavaScript file and altered it to include a malicious skimmer script.
Upon the next player update, the video platform started serving the skimmer code to every real estate website that already had the player embedded, enabling the script to gather confidential data entered into website forms.
The JavaScript code is heavily obfuscated, hence it’s difficult to raise any suspicions at first sight or be detected by rudimentary security software.
What Kind of Data Was Accessed?
Following an extensive investigation, Unit42 discovered that the skimmer code was designed to identify credit card patterns, steal victim names, email addresses, phone numbers, financial information, and send them to the threat actors.
The skimmer itself is highly polymorphic, elusive, and continuously evolving. When combined with cloud distribution platforms, the impact of a skimmer of this type could be very large.
For website administrators, it is advisable to safeguard any accounts, avoid theft by phishing or social engineering, and manage permissions well. Also, we highly recommend conducting web content integrity checks on a regular basis. This can help detect and prevent injection of malicious code into the website content.
Palo Alto Networks has provided a complete list of the IoCs (indicators of compromise) on this GitHub repository.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.


 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management
 Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security