Contents:
Browser hijacking appears to be increasing at an alarming rate globally, and it can be a real nuisance, and at times dangerous as well. In this post, we have gathered all you need to know about what is browser hijacking, how it works, and how you can prevent it. Keep reading and stay safe!
What Is Browser Hijacking?
Browser hijacking is the process of changing the default homepage or search engine in your web browser by a malicious program without your permission. The victim can notice that the affected changes can not be reversed and a security tool needs to be used against this type of software. Although it is not considered a serious threat to the overall system security, it needs to be addressed as soon as possible since web browsing is affected.
What Can A Browser Hijacker Do?
After hijacking your browser, the threat actor will modify your settings to do one or more of the following:
- Feed you with a lot of malvertising popups and ads.
- Steal your information by dropping malware into browsers. The data could include user IDs, passwords, full names, addresses, social security numbers, etc.
- Spy on you.
- Add new Toolbars, Bookmarks, or Favorites.
- Change your browser homepage to a new one. For example, it changes your default home page from Google to another search engine.
- Constantly redirect you to a particular website, such as an online store. This one is called DNS hijacking.
- Drive-by downloads can download a packet of data onto the user’s computer without his/her knowledge.
But it doesn’t stop here. It won’t even allow you to change your settings since it keeps reverting to its own default configuration. In other words, it will keep changing your browser’s homepage until you give up fighting it and accept the hijacker’s new homepage.
Compared to other malware infections, browser hijacking is a less severe form of malware infection.
Most browser hijacking malware isn’t conceived to damage or steal your files. Instead, the authors of the malicious code seek to profit from you either by feeding you ads, redirect you to a certain page or, like in the example above, install various useless toolbars and other software on your device.
However, other types of browser hijackers may act as “gates” for truly damaging attacks, such as ransomware, keyloggers, or even botnet malware that can enslave your device.
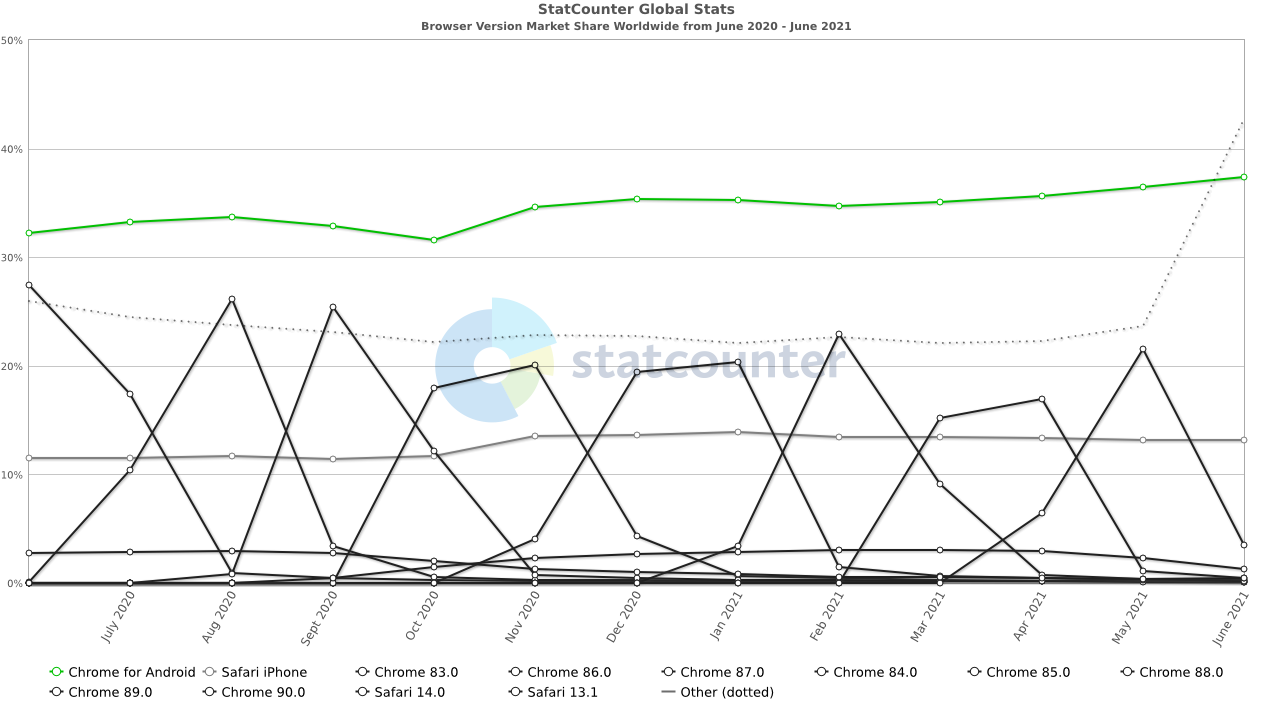
The fact that most users don’t run the latest version of their web browser is also a major problem and helps hijackers spread with relative ease.
Browser Hijacking Symptoms
In general, browser hijackers make it impossible for you to use your browser normally and can open up your computer to a host of additional infections. Nevertheless, once you know what to look for, the majority of hijackers are easy to detect.
#1. Unfamiliar Homepage and URL Redirecting
One of the most common symptoms of browser hijacking is discovering that your homepage has been reset. If your browser displays an unknown website after launch, particularly one that is pornographic or advertising fake security software, this is almost definitely the work of a hijacker. If you enter a URL only to be redirected to a different website than the one you intended to access, it is also an indication of hijacker infection. Although you will be able to reset your homepage straight away, once you launch your browser again it will probably revert to the hijacked state. The only way to get your settings back to normal is to remove the hijacker.
#2. Unavoidable Popups
You may think of popup windows as nothing more than a hassle, but the truth is that popups are a preferred form of malware delivery for browser hijackers. Highjacked browsers usually display overwhelming outbreaks of popup ads, allowing hijackers to even disable your browser’s popup blocker. The main purpose of these popup ads is to get you to click on one of the links by mistake and install malicious programs in the process, or redirect you towards rogue websites.
#3. Fake Security Alerts
Another symptom of browser hijacking is the fake security alert. If a message saying that your computer is being hacked or that your security has been compromised appears on your browser or desktop, make sure you read the message carefully before clicking on any links. If the message comes from a program you don’t remember installing, it’s probably the work of a hijacker. Since these messages are intended to mimic real system alerts, keep an eye out for any discrepancies (colors that vary from your desktop color scheme, spelling errors, etc).
How to Remove Browser Hijackers
#1. Manually Removing a Browser Hijacker
Most of the time, simply uninstalling the troublesome app will solve all your problems. That being said, we recommend you use the Control Panel for the removal process. After all, how much can you trust the “Uninstall” option on malicious software?
To access this uninstallation method, press your Windows start button on the bottom left of the screen, then click on Control Panel (or use the search function if you can’t see it), and under the Programs section, click Uninstall a program.
This will then take you to a menu, simply click on the malicious app, and then press the Uninstall/Remove button.
But there is a chance this won’t completely remove the malicious app from your PC!
It’s possible the app downloaded another program. In this case, you need to uninstall that one too, otherwise, you are still exposed to further browser attacks. Be careful not to uninstall any Windows-critical programs.
Finally, scan your PC with your antivirus software.
#2. Use Specialized Tools
Usually, removing a browser hijacker can be done simply by uninstalling the malicious free programs behind it. However, if your real problem is actually a malware infection, then you will probably need some specialized tools and a bit more patience.
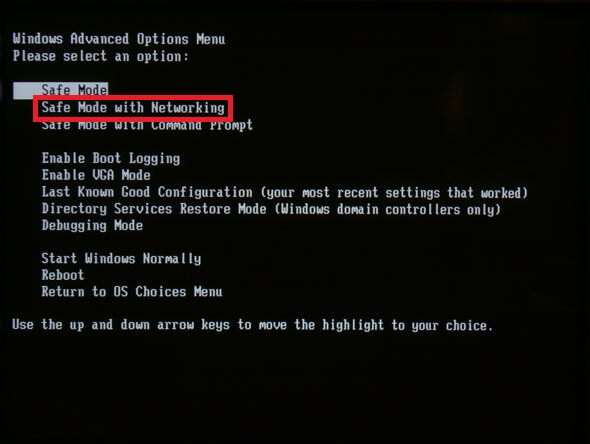
First, you need to restart your computer in safe mode with networking.
To restart your computer in Safe Mode, you need to restart it and press the F8 key at boot-up. Assuming you pressed the key at the right time, you should get a screen similar to this one.
Be sure to select Safe Mode with Networking, since you’ll need an internet connection to download some necessary programs.
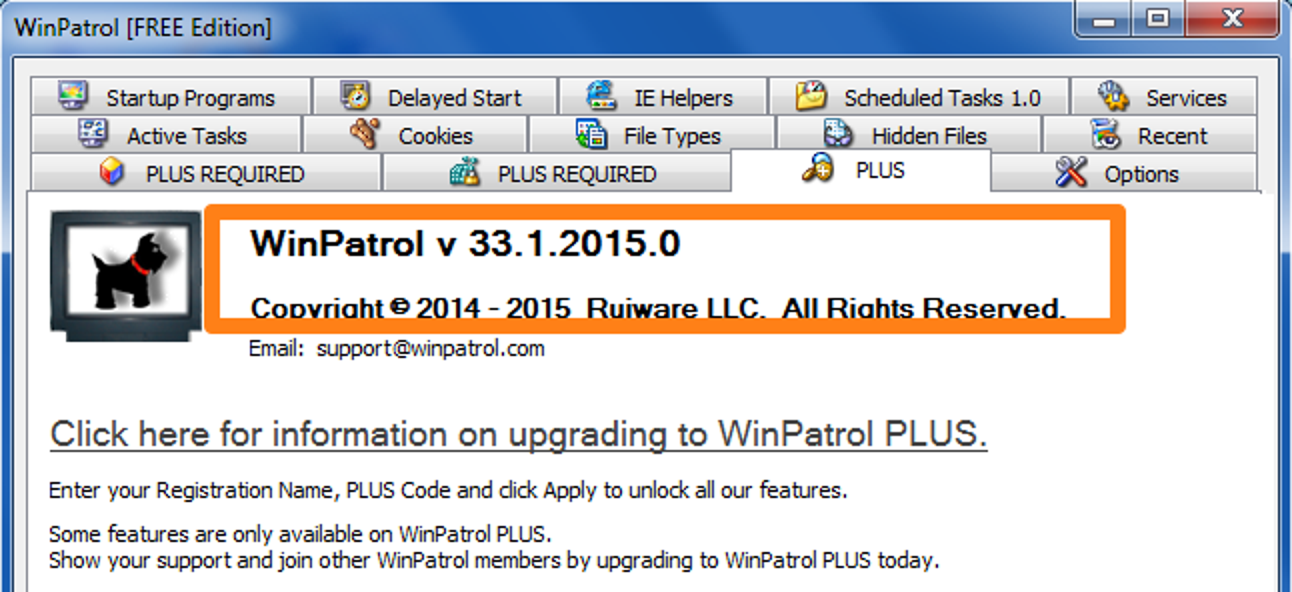
1. WinPatrol
WinPatrol is a great tool that you can use to protect your computer if you know how to use it to monitor changes made to your files and folders. Since its main function is to monitor your system for any changes, it is highly useful when you are installing new programs and when you are browsing sites with bad reputations as malware hosts. Whenever it detects a change in your system, it will bark and present a popup screen that asks you whether or not you intended to make any changes and will ask for permission to carry out the operation.
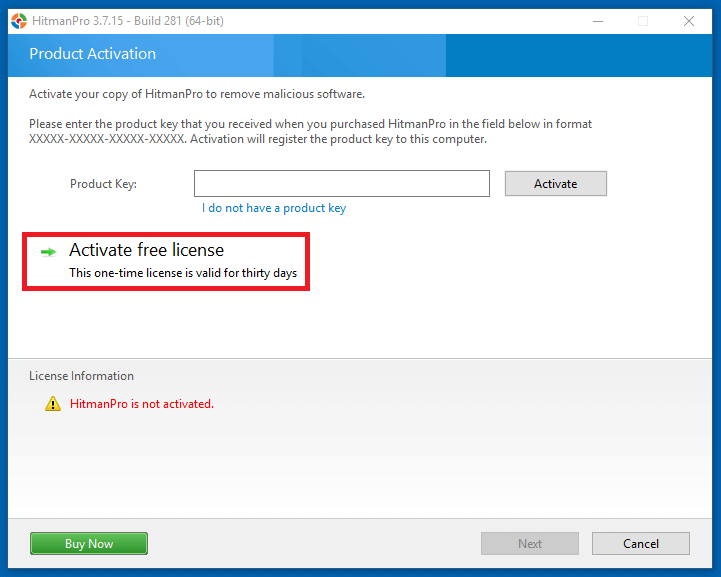
2. HitmanPro
A well-known and trusted security tool, HitmanPro doesn’t interact in any negative fashion with known antivirus or security programs.
It’s worth mentioning that is a premium software, but it does a trial version, so you’ll need to press “Activate free license” in order to enjoy the 30-day trial and get on with the malware removal process.
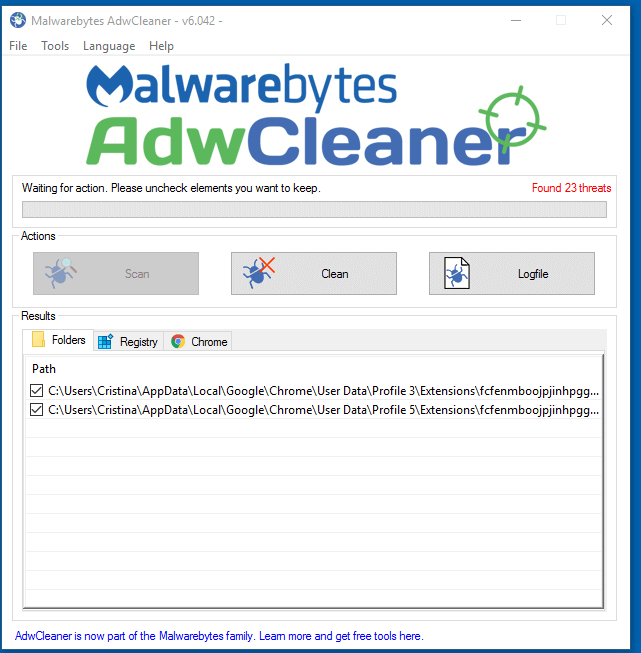
3. AdwCleaner
AdwCleaner is a free browser hijacker removal tool specialized in removing adware and other similar types of malware you might have hidden on your PC.
The program is an executable one, meaning you don’t need to install it. Just press it and run.
Once you finished the scan, press the “Clean” button to remove the threats you might have on your PC.
Examples of browser hijackers:
Ask Toolbar
Ask Toolbar hijacker alters your browser’s settings, including the new tab page, homepage, and search engine by default, while installing unwanted extensions on your computer. This is the main reason why you need to remove Ask Toolbar from Windows OS and return your browser search engine and homepage back to default.
GoSave
GoSave is a browser add-on claiming to save time and money by displaying special offers and discounts while browsing shopping websites. Since victims are not properly informed at installation, it adds a plugin or extension to the default browser and inserts ads into web pages.
Coupon Server
Coupon Server is an adware program bundled with multiple freeware applications. It claims to save money by providing discount coupons for various online shops. What’s more, updates of the application promote fake search engines.
CoolWebSearch
CoolWebSearch gets installed on your PC while you download other free programs or apps. The program can change an infected computer’s web browser homepage, and though originally thought to only work on Internet Explorer, recent variants affect Mozilla Firefox as well as Google Chrome, and others. Infected computers can create pop-up ads that redirect to other websites, collect private information about users, and slow the connection speed.
RocketTab
RocketTab is a browser hijacking program that gets into your system while you download other free programs online. It sets itself as a proxy and runs all HTTP and HTTPS traffic through itself, creating problems for security applications.
Browser Hijacking Prevention
You’ve probably noticed how time-consuming and complex is to remove a browser hijacker or any other malware for that matter. Remember: it’s always easier to prevent an infection rather than clean up after one.
In this section, we’ll go over all the steps you should follow to prevent a hijacker from taking over your browser.
Keep your software updated at all times
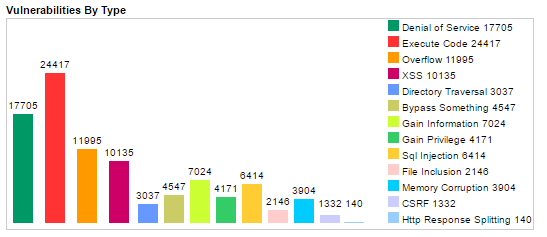
Browsers are some of the most vulnerable apps you can have on your computer. Because they are the first point of contact to the Internet, browsers are exposed to some of the worst kinds of attacks and exploits.
Not only that but browsers are developed by humans, meaning they are flawed by design. Here’s a graph from CVEdetails showing just how many security vulnerabilities have been identified for browsers over the years.
Image Source: CVEdetails
Because of this, we recommend you make sure your browser is updated to the latest version so that known vulnerabilities are patched up.
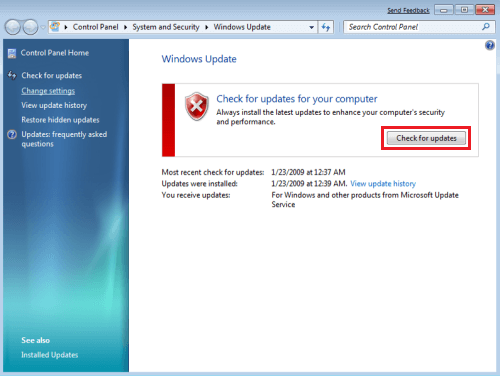
However, you should also keep all other software on your PC updated as well, most importantly your Windows operating system.
We admit that constantly monitoring your apps to make sure they are updated can be a chore, but thankfully, our own Heimdal™ Free can take away a lot of the pain involved in the process, since it automatically updates the software without bothering you with pop-ups and other useless notifications and dialog boxes.
Use a good antivirus to keep the hijacker away
A good antivirus can make all the difference between an infected PC and a clean one. That’s why you should put some thought into finding the best one for your needs. Here’s a complete guide to finding the best antivirus you could use.
Be suspicious of free programs
There is no such thing as a free program, so make sure you double-check how secure and legit a free program is with a quick web search before you download it.
Trustworthy free apps and software should have good reviews and user opinions. If you can barely find any information about the software in question, then that’s a bad sign. If the little information you do find is negative and claims the software is actually malware or adware in disguise, then run for the hills and don’t look back, since you’ve just avoided some unnecessary cyber pain.
Most of the time, this should be enough to weed out the bad software out there and leave you with the ones that are truly good.
Avoid suspicious websites at all costs
Never install software from unauthorized portals or untrusted sources. If you are an organization, it is safer to restrict admin rights on computers for employees and limit access only to specific data they need and use. Also, restrain the authority to install software programs and encourage them to report back to you when they notice/receive suspicious emails from untrusted sources.
Conclusions
Browser hijackers are an annoying and aggravating type of malware. Fortunately, it’s not as severe as a ransomware attack or financial malware, but if you don’t take it seriously, it might snowball into a much more serious problem.











 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security