Contents:
Threat actors use data stolen from Columbian bank customers as lures in email phishing attacks. Cyber researchers warn that the campaign aims infecting endpoints with BitRAT remote access trojan.
On the bright side, according to researchers, none of the sensitive data exfiltrated from the bank seems to have been spilled on the dark web or clear web.
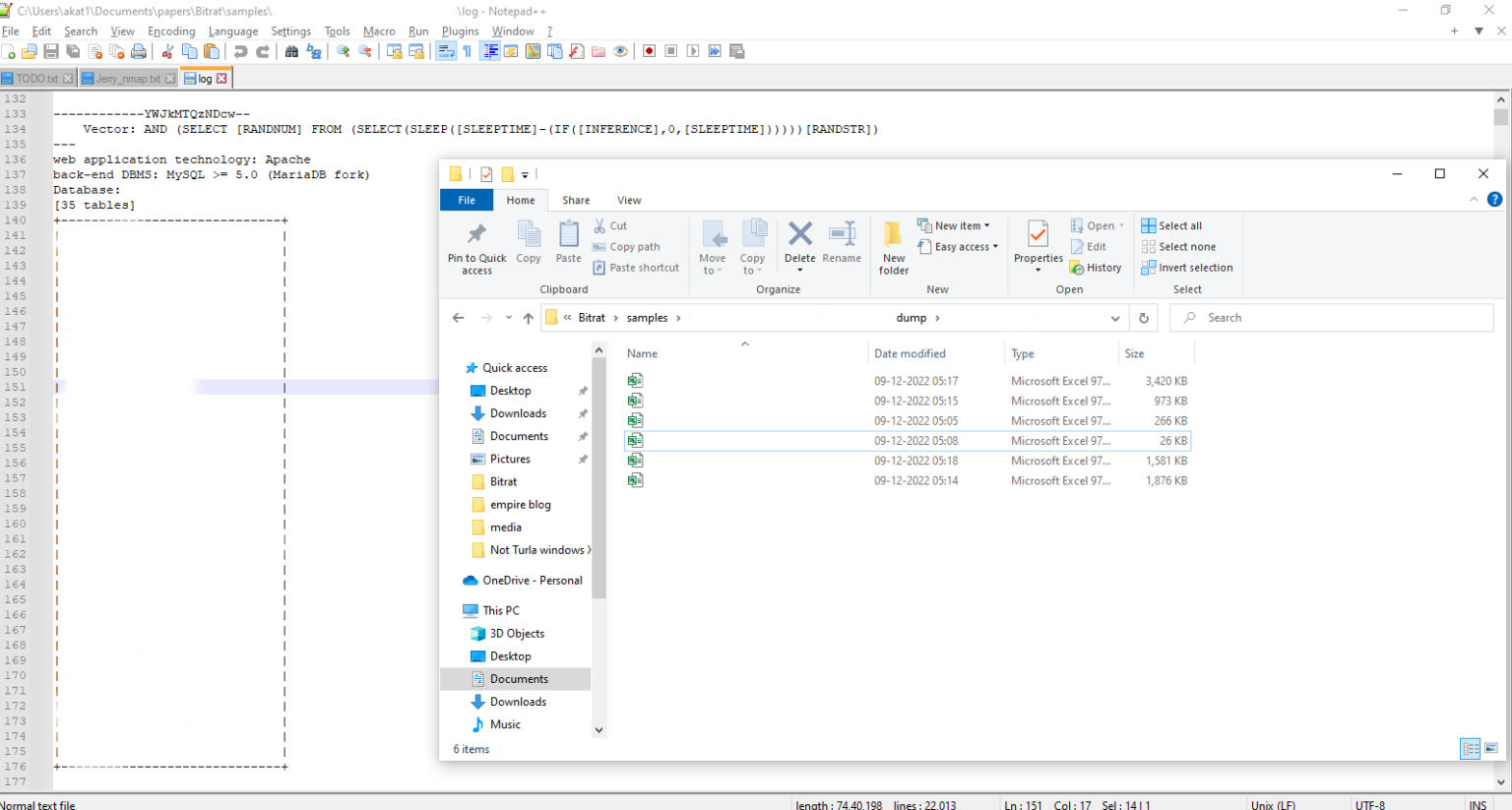
While investigating the BitRAT lures, cyber researchers discovered that servers of an undisclosed Colombian bank were hijacked and 418,777 files were stolen. The breach resulted in extremely sensitive customer data, like ID numbers, addresses, payment records, and salary information being available to threat actors involved in the attack.
The above-mentioned data are now used for making phishing emails that aim to deploy BitRAT malware look more credible.
Moreover, the lures themselves contain sensitive data from the bank to make them appear legitimate. This means that the attacker has gotten access to customers’ data.
The Attack`s Structure Explained
When the malicious email completes its mission, an Excel file drops and executes a .inf file into the victims’ machines. Next, the BitRAT payload is from a GitHub repository through the WinHTTP library. Once the computer is infected, threat actors use the WinExec function for execution.
The RAT malware relocates its loader to the Windows startup folder during the last phase of the attack to obtain persistence and restart automatically when the system reboots.
More About BitRAT and Why It Became So Largely Used
BitRAT is a relatively new name in the malware market, with a historic that barely reaches two years’ time.
On the dark web markets and cybercrime forums, BitRAT is sold for only $20 and offers lifetime access. The cost is pretty low for the versatility and opportunities the „product” offers.
Once they get the license for it, threat actors are free to use BitRAT however they like. Cyber researchers noticed it being largely present on social media, with various purposes like recording video and audio, stealing data, DDoS attacks, and cryptocurrency mining.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security