Contents:
A zero-day attack is intimidating, as it gives hackers a unique opportunity to bypass typical cybersecurity defenses. In this article, I will explain what exactly a zero-day vulnerability is and how you can protect yourself and your organization against threats.
Key Takeaways:
- Definition and Nature of Zero-Day Vulnerabilities;
- Exploitation and Impact;
- Reporting and Scoring of Vulnerabilities;
- Zero-Day Vulnerability Timeline;
- Protection Against Zero-Day Attacks.
What Is a Zero Day Vulnerability?
A zero-day vulnerability is a vulnerability that has been publicly revealed but has not yet been patched by the developers and, as a result, can be exploited.
A zero-day attack is a cyberattack that manages to exploit a zero-day vulnerability – an unknown or newly discovered software/hardware vulnerability.
A zero-day exploit refers to the method used by attackers to infiltrate and deploy the malware into a system.
The term “zero-day” is an imaginative time, as this type of cyberattack happens in a very short timeframe from the awareness of the security flaw. Thereby, not giving developers enough time to eradicate or mitigate the potential risks associated with this vulnerability.
In zero-day attacks, software vendors are reactive, not proactive. Therefore, since patches have not yet been released, the attackers are already making their move.

What Is a Software Vulnerability?
Defects, as well as programming mistakes in software or operating systems, can lead to vulnerabilities. Vulnerabilities generate security gaps that hackers can exploit if they are not fixed.
Anyone can report a vulnerability – a vendor, a researcher, or an individual who discovered a flaw and intends to bring it to someone’s attention. Many vendors offer bug bounties to encourage responsible disclosure of security flaws. If you find a vulnerability in open-source software you should submit it to the community.
Short for Common Vulnerabilities and Exposures, CVE is a list of publicly disclosed software security flaws.
The Common Vulnerability Scoring System (CVSS), for example, is a set of open standards for assigning a number to a vulnerability to establish its severity.
CVSS scores are used by the NVD, CERT, and others to assess the impact of vulnerabilities. Scores range from 0.0 to 10.0, with higher numbers representing a higher degree of severity of the vulnerability. Many security vendors have created their scoring systems, as well.
Zero-Day Vulnerability Timeline
Zero-day exploits generally involve using malware to attack specific weaknesses in software. Once the malware is in place, it interferes with the software’s normal operations
Sounds complicated, right? Malware infiltration is remarkably easy. Hackers can conceal malware as links to a particular site. All a user has to do is click on the link and the doubtful software starts downloading automatically. Downloads like these usually occur when attackers have found a way to exploit unprotected vulnerabilities in a browser.
Let’s assume your browser has updated its version to add more features. You log in to a site you trust and click on what you believe is a valid link. However, the link contains malicious code.
Before patches, your browser would have prevented the link from automatically downloading the software to your computer. However, due to changes in the browser code, the download begins and your computer becomes infected. Later, the browser is updated with a new patch to prevent infecting other users. Unfortunately, it is too little too late.
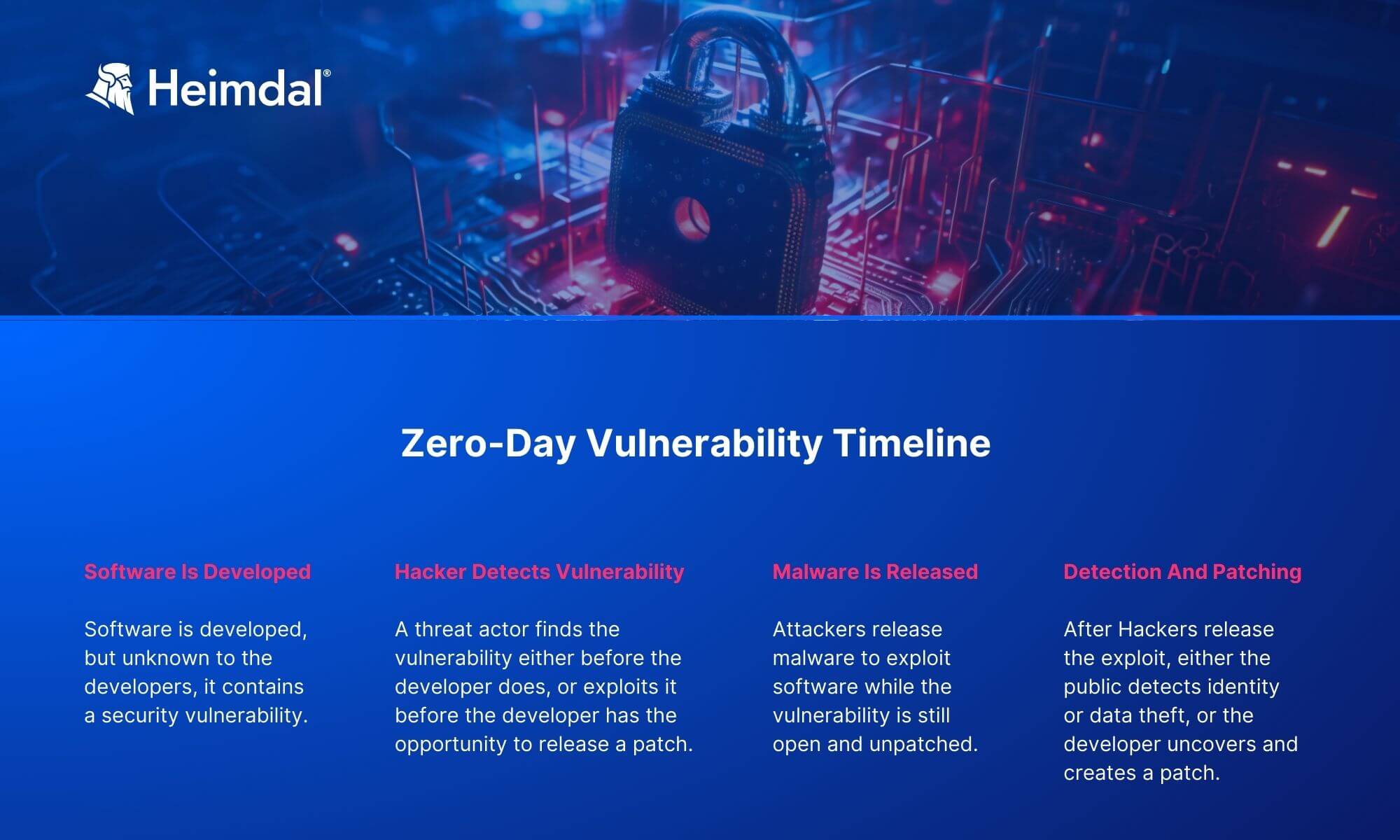
In short, the timeline of a zero-day vulnerability goes as follows:
- Software Is Developed – Software is developed, but unknown to the developers, it contains a security vulnerability.
- Hacker Detects Vulnerability – A threat actor finds the vulnerability either before the developer or exploits it before the developer has the opportunity to release a patch.
- Malware Is Released – Attackers release malware to exploit software while the vulnerability is still open and unpatched.
- Detection and Patching – After hackers release the exploit, either the public detects identity or data theft, or the developer uncovers and creates a patch.
Examples of Zero-Day Attacks
The period between a security gap’s discovery and its mitigation is known as a window of vulnerability. This is when a zero-day attack can take place. I have included some examples below to better illustrate this type of incident, so let’s have a look at each one.
Kaseya
On July 2nd, 2021, the REvil ransomware operation launched a massive attack by exploiting a zero-day vulnerability in the Kaseya VSA remote management application and encrypting about 60 managed service providers and an estimated 1,500 businesses. After the attack, the threat actors asked for $70 million to provide a universal decryptor.
The FBI briefly described the incident as a “supply chain ransomware attack leveraging a vulnerability in Kaseya VSA software against multiple MSPs and their customers.”
In June 2021, LinkedIn reported that it had been hit by a zero-day attack that affected 700 million users (over 90% of LinkedIn’s user base). Hacker “GOD User TomLiner” advertised the data of LinkedIn users for sale with samples that the information is real and up to date as of June 2021.
It’s still uncertain what the origin of the data is but the scraping of public profiles might be the starting point. That was the generator behind the collection of 500 million LinkedIn records that were advertised for sale in April 2021.
Back in 2019, detailed information about 540 million Facebook users was left publicly viewable for months after a zero-day exploit. Facebook confirmed at the time that the data had been scraped due to a vulnerability that the company later patched.
However, in April 2021, it was revealed that the same vulnerability led to the leak of 533 million Facebook users’ information (approximately 20% of all accounts).
The publicly accessible database had personal details of Facebook users with phone numbers, Facebook IDs, full names, locations, birthdates, bios, and, in some cases, email addresses. Even Facebook CEO Mark Zuckerberg’s private credentials were reportedly leaked in the process.
Microsoft
Another recent zero-day attack that was made public not too many months ago is on Microsoft, the esteemed Washington-based multinational technology company. You can read all about it in my colleague’s article on the incident.
The operation is attributed to the Chinese hacker group Hafnium, and it affected Microsoft’s Exchange Server 2013, Exchange Server 2016, and Exchange Server 2019.
DNC
One of the most popular zero-day attacks is what we know as the Democratic National Committee (DNC) hack. There have been about six zero-day exploited vulnerabilities for gaining access to the stolen data.
The state-backed these discovered vulnerabilities by Russian hackers in Adobe Flash, Microsoft Windows, and Java. To operate on the vulnerabilities, the hackers got involved in a campaign of spear-phishing.
Sony
The 2014 zero-day attack on American entertainment company Sony Pictures is a pivotal moment in cyber history. Rumors that a certain nation-state actor infiltrated the enterprise’s systems as retaliation for a then-unreleased film parodying its totalitarian leader quickly arose and were debunked, creating a global buzz around the incident.
The reality of the situation is unknown cybercriminals sought and successfully gained access to private corporate data, such as exec emails, business plans, and film release dates.
Protecting Your Business from Zero-Day Attacks
Zero-day vulnerabilities feature serious security risks, leaving you exposed to zero-day attacks, which can further result in potential damage to your computer or personal data. To keep them both safe, it’s smart and highly recommended to take proactive and reactive security measures.

1. Patch
As my colleague explained in Vulnerability Management, patching is the first recommended step to prevent potential exploits. It is quickly followed by traffic filtering and scanning both of which prevent communication with command & control servers. Most software vendors work fast to patch a security flaw, so make sure you check for a solution when a zero-day vulnerability is announced.
The Heimdal Patch and Asset Management solution enables you to automate your patching process and efficiently manage vulnerabilities. Applying the software patches as soon as they become available will minimize the exploit window and therefore can help you prevent zero-day attacks.
2. Implement Proactive and Comprehensive Security Software
Traditional cybersecurity tools such as intrusion prevention and detection systems detect incoming cyber threats by comparing their signature against a list of known issues. However, zero-day attacks have no signature because the vulnerability has not been analyzed yet. Chances are the criminals using it are among, if not the very first to discover it.
Therefore, zero-day attacks are very hard to detect through standard methods. This is why your business needs a defense-in-depth cybersecurity strategy approach. This is why, we here at Heimdal, are focusing on offering cybersecurity protection at different layers in an integrated way.
But as mentioned already, one of the most efficient ways to prevent a zero-day attack from taking hold of your corporate network is by applying patches as soon as they are released by their respective developers.
3. Implement Recovery Strategies
Even if you follow all of the advice above, it is unlikely that you or an organization will be able to completely clear away the threat of zero-day vulnerability. Therefore, to react, you need to prepare for the worst. Having a disaster recovery strategy is essential. In the unfortunate event of a security breach, your data is safe and you can continue your operations as usual.
4. Constantly Educate Employees
I’m just going to say it – the majority of zero-day attacks capitalize on human error. It’s a fact. Thus, you should always keep yourself up to date with good security habits, tips, and best practices that will help keep you safe online and protect your organization from zero-day vulnerabilities and other digital threats.
Heimdal® Patch & Asset Management Software
Final Thoughts
Protecting your business against zero-day vulnerabilities is essential to the integrity of your data. These types of threats are especially slippery since they usually can’t be found on standard blacklists. For this reason, your company needs to have an adequate detection, mitigation, and prevention strategy in place.
As always, Heimdal Security can help you with that, so don’t hesitate to check out our cybersecurity solutions suite.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security









