Contents:
Software vulnerabilities are one of the biggest nuisances for cybersecurity because cybercriminals love to exploit them. Read on to find out how you can be one step ahead by applying the virtual patch approach!
What Is a Virtual Patch
The term “virtual patch” was first used by Intrusion Prevention System (IPS) vendors and refers to a layer of security policy enforcement that inhibits the use of a known vulnerability. The security enforcement layer looks at transactions and intercepts attacks when they are in transit, so web applications are free of malicious communications and any exploitation attempt fails, despite the fact that the application’s source code has not been updated.
To better understand the concept of the virtual patch, let me clarify a few other important terms you’re going to find in this article:
- software – a collection of instructions and data that tells a computer how to work is referred to as software. Computer software contains programs, libraries, and non-executable data like online documentation or digital media. Both computer hardware and software are interdependent, and neither can be used effectively on its own.
- patch – in general, a patch is a small software update that manufacturers deploy to correct or improve a software application. A patch can address security flaws or other bugs, as well as improve the software’s functionality, usability, and performance.
- patch deployment – this term refers to the process of deploying updates or patches. This process is also known as patch management.
Automate the Patch Management Process with Heimdal®
Find out more 30-day Free Trial. Offer valid only for companies.Virtual Patches and Vulnerability Management
In cybersecurity, a vulnerability refers to a gap that allows cyber attackers to damage a system. Vulnerabilities must be fixed as soon as they are detected, before they are exploited by a cybercriminal.
Known vulnerabilities are actually the primary catalyst of successful cyberattacks. In this race against the clock, the best option remains patching. Or the newest innovation in the field – the so-called deep security virtual patching.
Challenges of Virtual Patching
As any organization that gave vulnerability/patch management some thought knows, implementing such a system comes with a few challenges:
Business continuity
Unless it’s automated, the process of patch management can be slow and disruptive, causing some operational downtime.
Quantity
If a company thinks to upgrade their entire IT infrastructure, they will need to patch a significant number of vulnerabilities – and this number will most probably increase over the years.
Limited visibility
The visibility of large online infrastructures can be limited due to different operating systems or application versions, which might also be in distinct geographic places.
Legacy software/software rot
Software rot can be defined as follows:
Software rot, also known as bit rot, code rot, software erosion, software decay, or software entropy is either a slow deterioration of software quality over time or its diminishing responsiveness that will eventually lead to software becoming faulty, unusable, or in need of an upgrade. This is not a physical phenomenon: the software does not actually decay, but rather suffers from a lack of being responsive and updated with respect to the changing environment in which it resides.
Software rot can also be linked to legacy software. As my colleague Miriam explains in one of her articles, “legacy software is any piece of software that can’t receive continued patching or support from its developer, or can’t meet the compliance standards in use.”
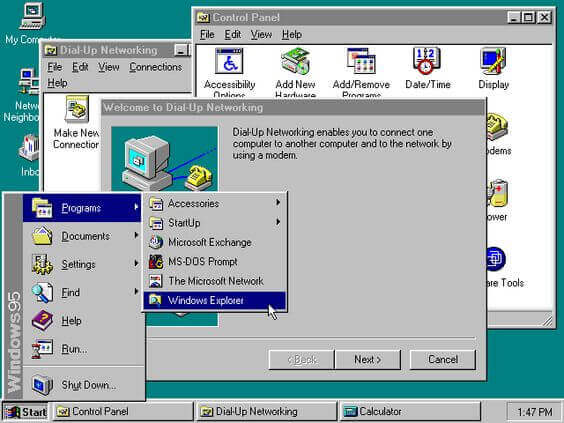
Source: Pinterest
Virtual Patching Benefits
Virtual patches can externally address issues outside of an application’s code. Moreover,
- a virtual patch is a scalable solution – it can be implemented in a few locations too, not necessarily on all hosts.
- a virtual patch minimizes risks until vendor-supplied patches are released.
- a virtual patch provides efficient protection for critical systems that cannot be taken offline.
- a virtual patch can reduce or completely eliminate the time and money spent on emergency patching.
Let’s not forget that a virtual patch can also:
- buy security teams additional time to assess vulnerabilities and apply the necessary tests.
- eliminate downtime, because it offers the freedom to enforce patches on your own schedule.
- improve regulatory compliance and meet the requirements of the EU General Data Protection Regulation (GDPR).
- provide security control for legacy software, ensuring a stronger defense strategy.
Best Practices
This article would not be complete if I didn’t provide you with some recommended practices for the road. Ergo, here’s what you should try to do if you want to apply the virtual patch approach in your company:
Assess and Prioritize
As Joseph Faust notes in his paper, “Reducing Organizational Risks Through Virtual Patching”,
To be successful with your Virtual Patching approach, one should be prepared to spend adequate time in determining what priorities exist for your applications and what level of risk is acceptable. Scan and have your applications penetration tested for flaws, revisiting them on a continuous schedule, working through the identified vulnerability lists to determine real weaknesses in your applications that need to be patched.
Test
Another important aspect is testing: spend sufficient time testing each virtual patch against the applications you’re defending to ensure that false positives are kept to a minimum. Make sure you also take into consideration false positives, which deny legitimate traffic behaviour. Moreover, implement a clear method for employees to report issues and have an escalation process in place to resolve them.
Communicate
Communication within the organization is essential too. You should offer management metrics on a regular basis, by examining logs for statistics and trends, as well as explaining and communicating the organization’s active dangers and difficulties. Make reporting on malicious attack activities and the given defenses implemented by virtual patching a regular occurrence.
If you’re interested, you can find an intuitive patch & asset management solution in the Heimdal™ suite too. Our Heimdal™ Patch & Asset Management will see any software assets in your inventory, alongside their version and number of installs, create inventory reports for accurate assessment and compliance demonstration, and allow you to update or downgrade software and operating systems from an intuitive, unified dashboard.
Heimdal® Patch & Asset Management Software
Wrapping Up
Achieving great cybersecurity is a complex mission – but not an impossible one. The best strategies include being informed and implementing powerful, effective solutions that can protect your IT infrastructure, buy you additional time and help you achieve compliance like virtual patches do.
Drop a line below if you have any comments, questions, or suggestions related to the topic of virtual patches – we are all ears and can’t wait to hear your opinion!
P.S. Did you enjoy this article? Follow us on LinkedIn, Twitter, Facebook, Youtube, or Instagram to keep up to date with everything we post!










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security









