Contents:
WSUS still works for what it was built to do. That’s not really the issue.
The issue is everything around it changed.
Teams are patching remote laptops, hybrid server environments, third-party applications, and machines that rarely touch the corporate network. Audit pressure is higher.
Vulnerabilities are exploited faster. And most mid-market IT teams are trying to hold all of that together without a dedicated patch management specialist.
Microsoft has also made its direction clear. Windows Server Update Services (WSUS) is deprecated and no longer receiving new features, with Microsoft steering endpoint management toward Intune and Windows Autopatch, and server patching toward Azure Update Manager.
So when people search for a WSUS alternative in 2026, they’re usually not looking for a neat one-to-one replacement.
They’re trying to answer a messier question:
How do we handle Windows update, third-party patching, and patch deployment across endpoints and servers without adding more overhead?
That’s what this guide is really about.
Best WSUS Alternatives and Competitors
These are eight options worth considering if you still use WSUS today but feel like you’re working around it rather than with it.
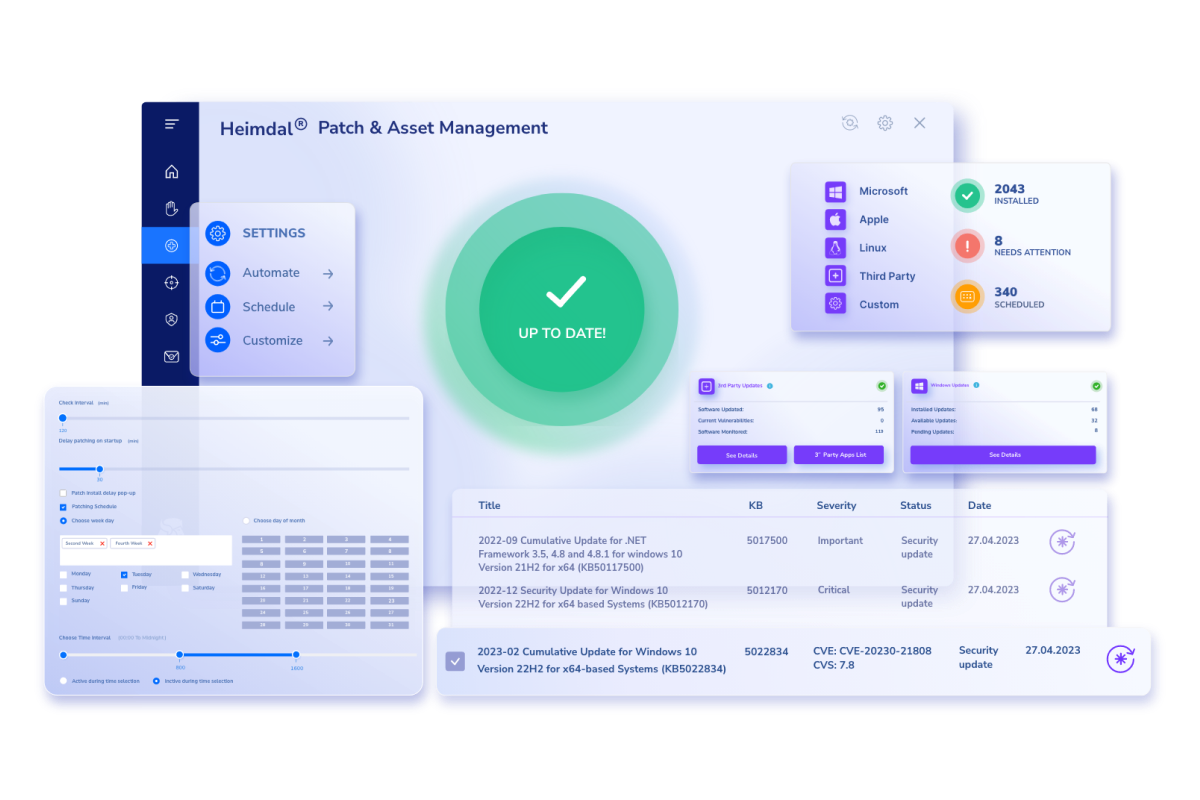
1. Heimdal® Patch & Asset Management
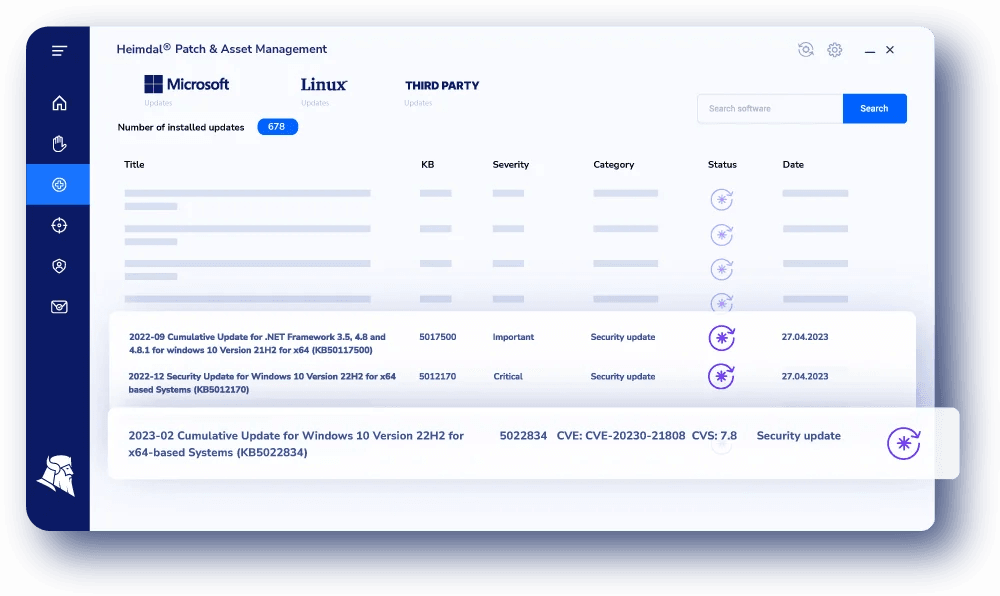
If your problem goes beyond Windows updates, Heimdal is usually one of the first platforms teams evaluate.
This is aimed at organizations that want patch management to sit inside a broader endpoint management workflow rather than exist as a standalone tool. The main draw is consolidation. Fewer agents, fewer tools, and less context switching.
Heimdal supports patch deployment across Windows 10, Windows 11, macOS, Linux, and a wide range of third-party applications, alongside custom software deployment.
Why teams look at it
- Fit for lean IT and security teams trying to reduce tool sprawl
- Covers both OS and third-party patch management in one platform
- Better aligned with remote and hybrid environments than WSUS
- Appeals to teams trying to simplify operations, not expand them
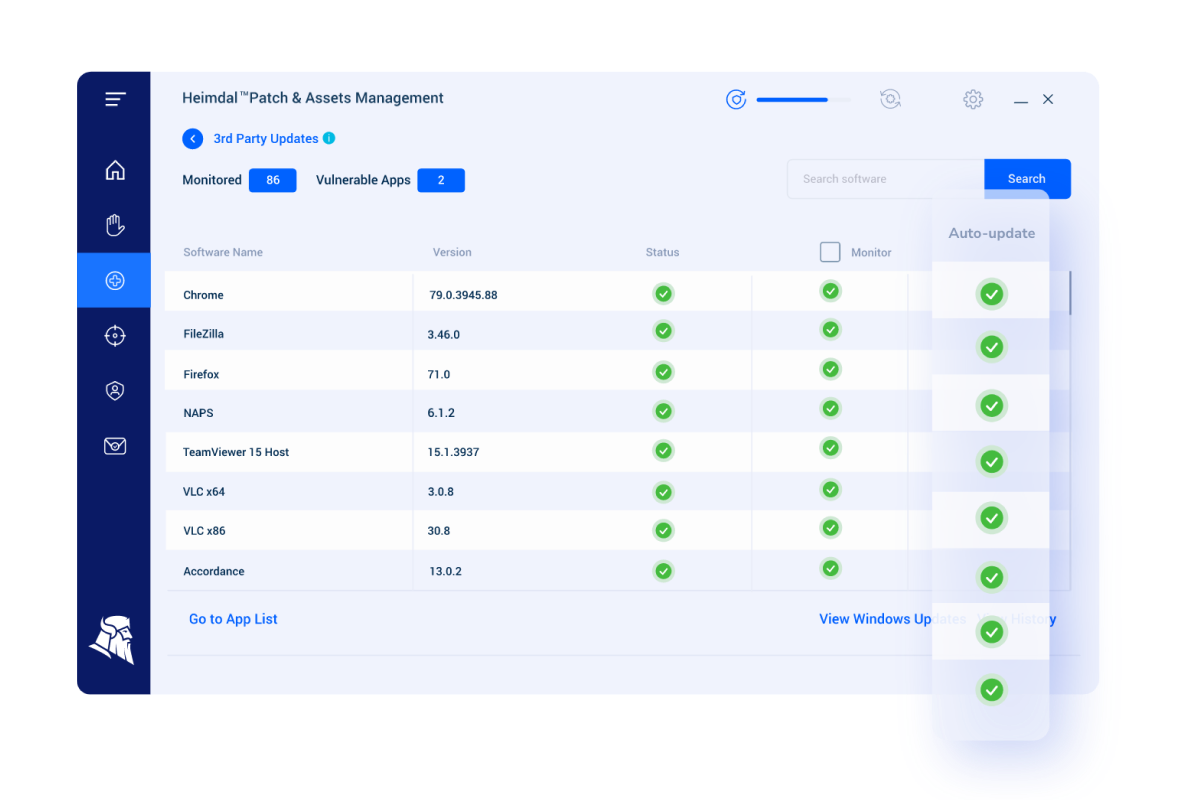
What stands out
- Cross-platform patch deployment
- Support for third-party applications and custom software
- Visibility into patch status and vulnerabilities
- Centralized scheduling across endpoints and servers
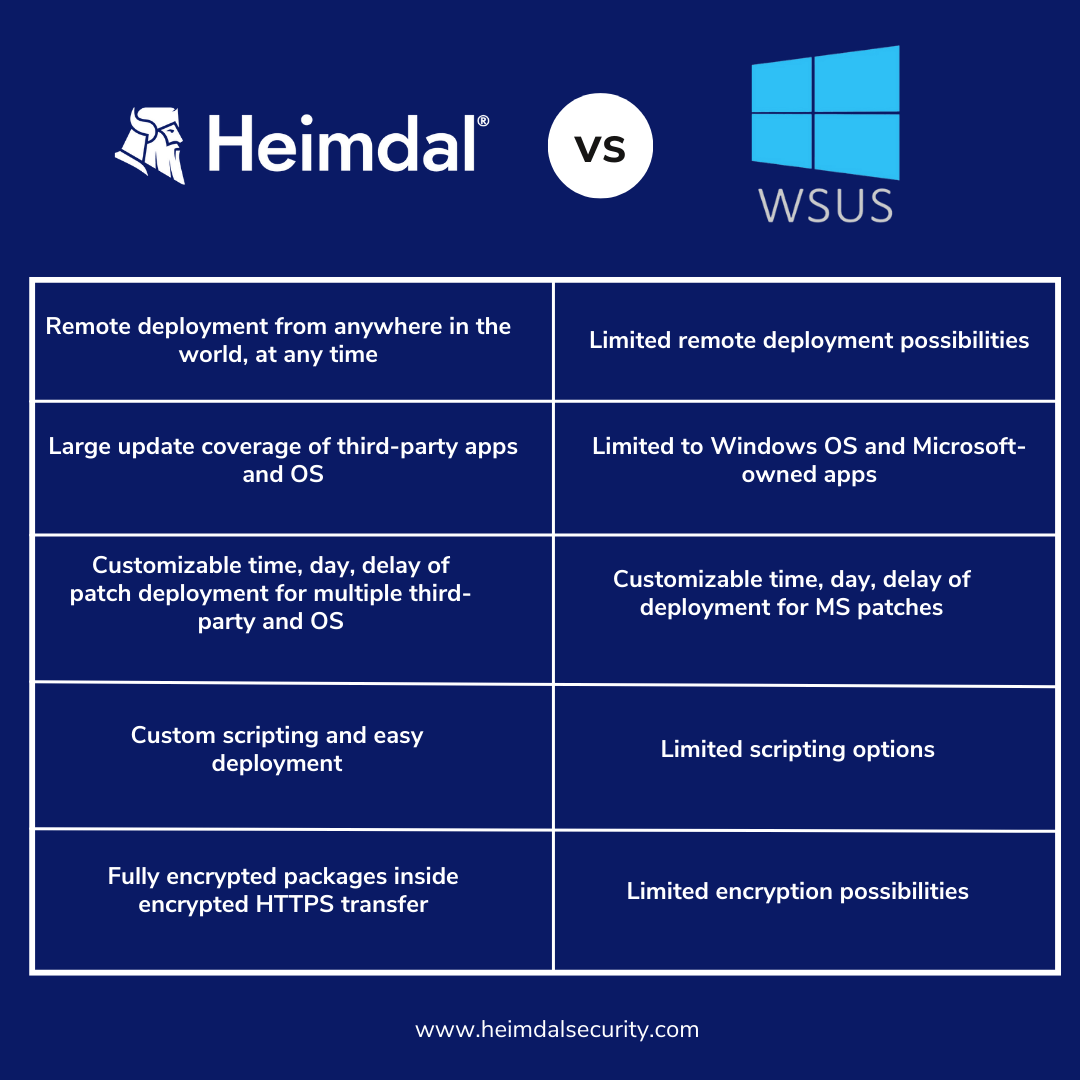
Where to be careful
- More platform than needed for simple, Windows-only environments
- Value depends on how much consolidation you actually use
Pricing
You can get Heimdal’s pricing on using their pricing calculator here.
Testimonials
Understanding real-world experiences can help you gauge how Heimdal Patch and Asset Management performs in practice. Let’s delve into what users and industry experts are saying about this tool to give you a clearer picture of its strengths and areas for improvement.
As a customer of Heimdal who was using their other modules it made sense to add this piece and stop using our previous Patch Management vendor. Due to lower cost and agent consolidation we thought this was the best option and we were not wrong. It caught things the other program missed.
Overall, use has been great and once setup – we don’t need to constantly monitor it.
William S., Senior Director (Source)
Some users highlighted the ease of setup and capabilities of the support:
From setup to deployment and support, the Heimdal experience has been unlike any other software I’ve used in recent years.Having a single pane of glass to manage critical end-point protection helps you easily get an overview of your estate.
Iain K., IT Manager (Source)
2. BatchPatch
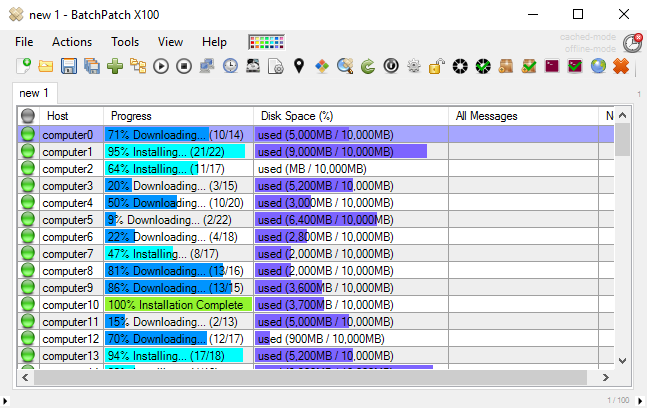
BatchPatch is a lightweight option focused on Windows environments.
It’s often used by teams that want something simpler than WSUS without moving to a full patch management tool or cloud-based model.
BatchPatch has become an essential tool during our Information Systems maintenance nights.
For those seeking a straightforward, no-frills WSUS alternative, BatchPatch offers an easy way to automate Windows updates efficiently.
The ability to download and install updates for all of our servers at once has saved us countless hours and simplified the process of managing our server infrastructure.
Why teams look at it
- Straightforward Windows patch and update management
- Lightweight alternative to WSUS
- Can be used alongside or instead of WSUS
What stands out?
- Multi-machine patch deployment
- Remote command execution and scripting
- Centralized control across Windows servers and workstation environments
Where to be careful
- Limited beyond Windows environments
- Not designed for modern, multi-OS or remote-first endpoint management
- Manual effort can increase as environments grow
Pricing
Commercial licensing is required. Pricing varies by license type.
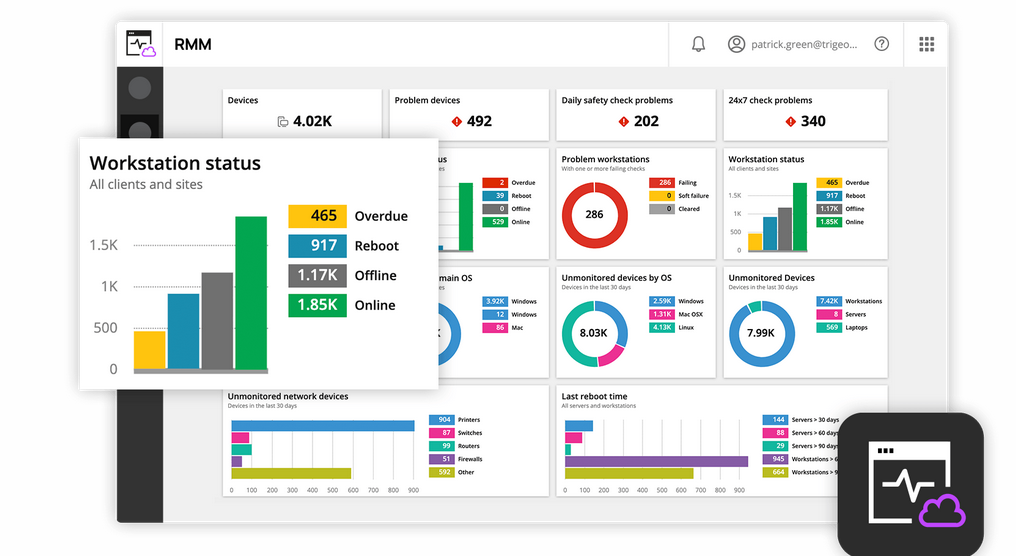
3. Kaseya VSA
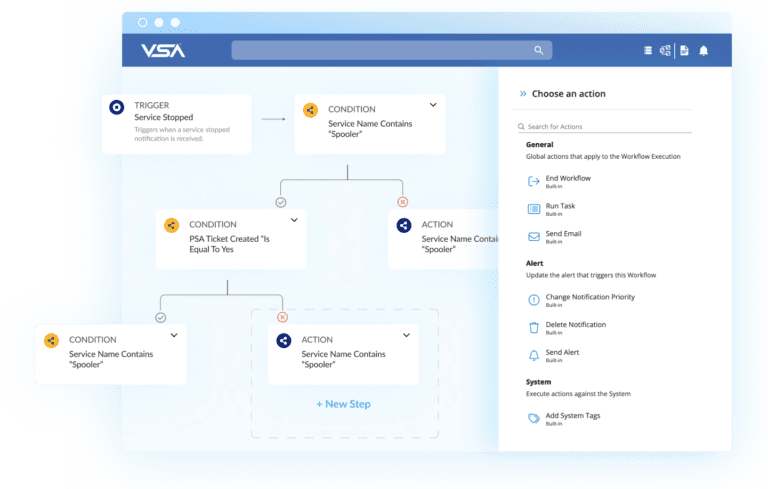
Kaseya VSA is an RMM platform where patch management is one part of a broader endpoint management and automation strategy.
This fits teams already operating within an RMM model rather than those looking for a dedicated patch management solution.
Why teams look at it
Let’s explore what Kaseya VSA offers:
- Combines patch management with endpoint and server monitoring
- Strong fit for MSPs
- Designed for remote environments
What stands out
- Automated patch deployment workflows
- Policy-based configuration and deployment
- Remote endpoint and server management
Where to be careful
- Can be complex compared to standalone patch management platforms
- Patching is one feature among many
Pricing
Quote-based
Testimonials
Hearing from others who have used Kaseya VSA can provide valuable insights:
We operate a large healthcare organization across multiple states and utilize Kaseya for 24/7 workstation management, software deployment, system reboots, report generation, and remote access.
This tool has been invaluable for our IT department.
The customer service provided by our local representative is exceptional, as he promptly assists us with any issues related to the program or billing.
Stacey G. (Source)
Other users reported that the software’s usability can be a drawback, and the high-price might also be an important considerent:
Kaseya is a powerful tool that offers extensive functionality, although its usability could be improved.
They have so many options, it’s hard to get your head around everything. I’m a smaller MSP and just can’t afford every option they have. They all have value but it’s hard to make it work.
Dana D. (Source)
4. NinjaOne
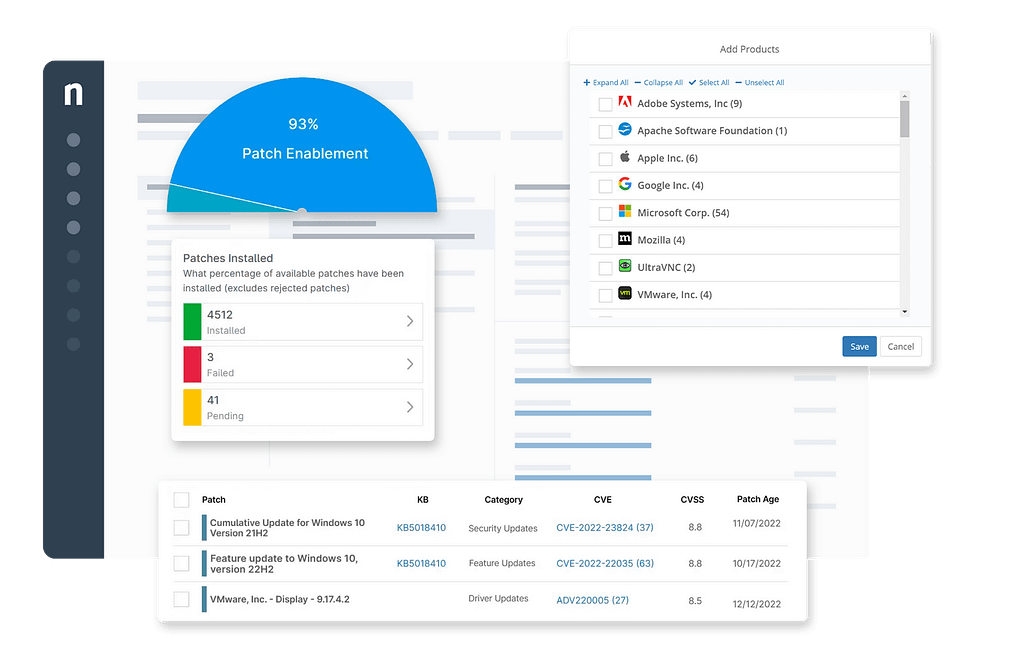
NinjaOne is a cloud-based endpoint management platform with integrated patch management.
It’s commonly shortlisted by teams managing distributed endpoints and remote devices.
Why teams look at it
Let’s explore what the solution brings to the table:
- Strong fit for remote and hybrid environments
- Combines patching with endpoint management
- Widely adopted in MSP and mid-market IT teams
What stands out
- Centralized patch deployment across endpoints
- Cross-platform support
- Visibility into patch status and compliance
Where to be careful
- Cloud-only deployment may not fit all environments
- Limited pricing transparency
Pricing
Per-device pricing model.
Testimonials
Let’s see what the NinjaOne users have to say about the solution.
I use NinjaOne daily to monitor dozens of company desktops and laptops.
It’s extremely easy to deploy and install the agent and begin to monitor from afar.
The interface provides detailed and extensive reports and information on system health, status, and usage, and makes the remote troubleshooting process a breeze with TeamViewer integration.
My first step upon arriving in the office is logging into the neat and simple NinjaOne web interface, and I can start my day confidentally knowing all of our devices are up to date with all software/OS updates and fully secured.
We also have a great account manager that actively reaches out to provide any support and information I need.
Alec N. (Source)
In terms of lacks from the product, users complained that newly added features still feel incomplete.
New features coming into the tool sometimes feel like they are first or second draft and often need to be updated in one or more future updates down the road.
While this is frustrating in some cases the updates usually come quickly and often include the improvements needed to make it user friendly or add some of the expected abilities around the feature.
Charles C. (Source)
5. Automox

Automox is a cloud-native patch management platform built for distributed environments.
It focuses on automated patch management and policy-based patch deployment across operating systems.
Why teams look at it
- Designed for remote-first environments
- Cross-platform patch management
- Automation-first approach
What stands out
- OS and third-party patch support
- Policy-based patch scheduling and deployment
- Flexible device targeting
Where to be careful
- No on-prem server deployment option
- Linux patching depends on repository structure
- Reporting flexibility can vary
Pricing
Tiered subscription model.
Testimonials
Let’s take a look at aspects that Automox clients highlight in reviews when it comes to the product. Users describe it as being a solution that does exactly what it says, and nothing more. It focuses on nailing down the basics.
It doesn’t do things it doesn’t need to. They don’t package a ton of things in the software I don’t want. It’s patch management and software distribution. I really do like the software reporting as well.
John G. (Source)
When it comes to suggestions from the community, the reporting feature could offer more flexibility to users.
Reporting is great but could be better when using custom worklets. Output isn’t always informative unless you write it to be.
Nick P. (Source)
6. ManageEngine Patch Manager Plus
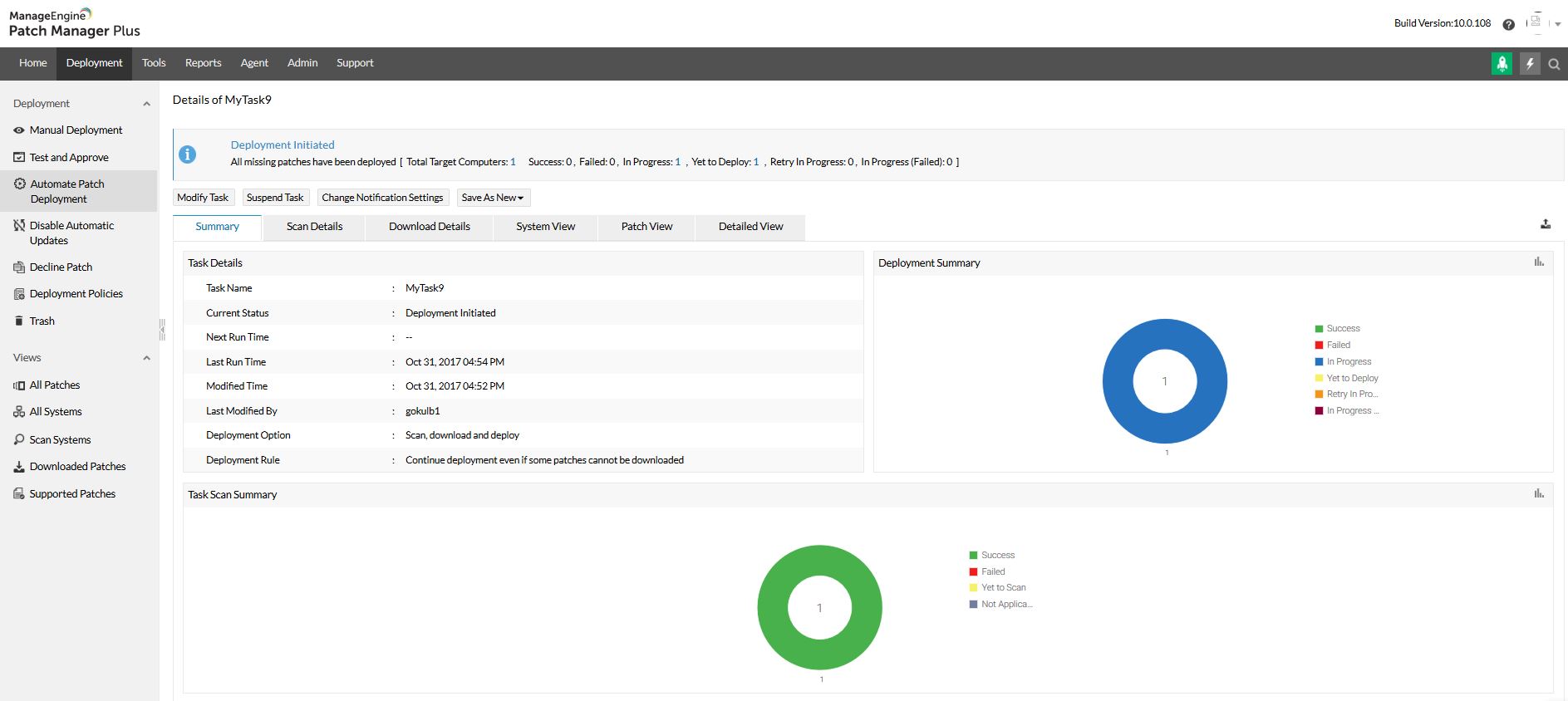
ManageEngine Patch Manager Plus is a patch management tool that sits between lightweight tools and full enterprise platforms.
It offers broader patch management capabilities without requiring a full RMM stack.
Why teams look at it
- Covers OS and third-party patch management
- Suitable for mid-sized IT teams
- Offers more control than basic tools
What stands out
- Automated patch deployment
- Support for third-party applications
- Policy-based patching and testing workflows
- Reporting and compliance features
Where to be careful
- Feature depth can increase complexity
- User experience and documentation can vary
Pricing
Subscription-based.
Testimonials
Let’s take a look at what professionals who have used the software have to say about it.
Using ManageEngine Patch manager plus you can patch your OS like Windows, Linux, MAC OS from centre of location as well as Patch Manager Plus support Microsoft as well as Third party patches.
Also, Patch Manager Plus give different methods of patching i.e Manual patch deployment and Automatic Patch Deployment (APD) from APD you can deploy patches without any human intervention. Overall you can patch your server, systems from centre of location.
Prathamesh K. (Source)
Users highlighted that the product can get ‘clunky’, functionality that ManageEngine could improve to offer its users a better experience.
We have a lot of ManageEngine products within our company, and we do run into “clunky” behavior with the apps, or we have to take extra steps in processes that could be mitigated through better coding on ME’s part.
Jamie M. (Source)
7. N-Able N-Sight
N-sight is an RMM platform with built-in patch management, primarily used by MSPs.
Why teams look at it
- Combines monitoring, support, and patching
- Designed for multi-tenant environments
- Easier entry point than some enterprise management platforms
What stands out
- Automated patch deployment
- Remote access and monitoring
- Reporting across endpoints and servers
Where to be careful
- More suited to MSP workflows than internal IT teams
- Reporting depth may not meet enterprise requirements
Pricing
Quote-based.
Testimonials
RMM is a great tool which links to many different products. From Take Control, Cove, Patch Management and other products. Having a central system to monitor these things makes management of client devices easy
William P. (Source)
Sometimes the errors on the checks are hard to resolve but the online support help.
Craig M. (Source)
8. PDQ Deploy
PDQ Deploy is a Windows-focused deployment tool used for software deployment and patching in traditional network environments.
Why teams look at it
- Strong reputation for Windows deployment
- Works well for on-prem servers and workstation environments
- Useful for scripting and automation
What stands out
- Pre-built package library for common applications
- Flexible deployment scheduling
- Integration with inventory tools
Where to be careful
- Primarily Windows-focused
- Less suited to remote-first endpoint management
- Relies on network-based deployment models
Pricing
Subscription-based.
Testimonials
Here is what some users have said about the product:
With PDQ we are able to visualize and coordinate maintenance of over 1600 devices between a relatively small and disparate IT support staff.
By leveraging smart scans on inventory and automating deployments of crucial business software, we are able to eliminate time wasted on mundane, repetitive tasks, freeing up support hours for the more unique problems and most importantly allowing time to be proactive instead of reactive in our organization.
Shelby J. (Source)
I would appreciate the ability to have a hold deployment ‘hold’ or wait for the machine to be powered on.
Sometimes we have deployments overnight for clinical updates, and I would like to deployment to not be in a ‘failed’ state if the machine is offline.
I would like it to just try again later that day.
Having a heartbeat deployment is a little different as that just generates a new deployment.
Nathan A. (Source)
What product should you choose?
That depends on what problem you’re actually trying to solve.
If you still use WSUS and want to stay close to the Microsoft ecosystem, tools like Intune and Configuration Manager (part of Microsoft products) offer a path forward for Windows update and endpoint management. Azure services also support modern server patching.
If you want a broader patch management solution, you’ll look at platforms that cover both OS and third-party patch management.
If you want simplicity, there are lighter tools focused on Windows patch deployment.
If you want to reduce tool sprawl and manage patch management across Windows, servers, and third-party applications, unified platforms become more relevant.
That’s the real divide.
Not which tool has the most features.
Which patch management platform fits how your environment actually works.
Because most teams don’t need more tools.
They need patch management that reduces risk without adding more operational overhead.
Frequently Asked Questions (FAQs) – Top WSUS Alternatives for Patch Management
What is WSUS and what does it actually do?
WSUS is Microsoft’s on-premise tool for managing Windows updates. It lets IT teams download patches once, store them locally, and control how updates are rolled out across devices.
How does WSUS get updates from Microsoft?
WSUS syncs with Microsoft Update servers to pull in available patches and metadata. From there, admins choose which updates to download and deploy internally.
Can you control how updates are deployed with WSUS?
Yes, but it’s fairly manual. You can approve or decline updates, set basic rules, and schedule deadlines. Most environments rely on a mix of manual approvals and automation rules to manage this.
How do you know if updates were installed successfully?
WSUS includes reporting that shows which devices are patched, missing updates, or failing installations. The catch is that reporting can be limited and often needs extra tooling or cleanup to stay reliable.
What do you need to run WSUS?
WSUS requires a Windows Server, database (WID or SQL), storage for updates, and ongoing maintenance. It’s not a “set it and forget it” setup.
What are the common challenges with WSUS?
- Manual patch approval takes time
- Limited support for third-party applications
- Reporting can be inconsistent
- Ongoing maintenance is required to keep it running smoothly










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security