Contents:
Malware-as-a-Service (MaaS) is the term used to describe the unlawful leasing of software and hardware for the purpose of conducting cyber-attacks.
Owners of MaaS servers provide threat actors with a remunerated botnet service that allows them to disseminate malware. Clients are often provided with access to a personal account on an online platform and will have the ability to manage the attack as well as get technical assistance via this channel.
This “service” is available for purchase on the Dark Web by hackers, and unfortunately, this scenario is becoming more common by threat actors, who pay the owners of the MaaS platform a membership fee in exchange for access to the platform’s features.
MaaS developers are often not concerned about the data stolen via their products; instead, they may sell it to the highest bidder on Dark Web forums or leave it to the MaaS subscriptions to deal with as they see fit.
What Makes MaaS Dangerous?
As with any service or product that is being sold, developers provide the seller with a comprehensive set of instructions.
It goes without saying that the prospective buyer does not need to be an expert in a particular programming language, and as a result, nearly anybody, regardless of computer science background, can administer a MaaS.
Anyone that wants to launch a cyberattack needs to simply find out the best technique to launch an assault and to know how to get access to the Darkweb in order to be successful.
As my colleague Vladimir thoroughly explained, the dark web is a most peculiar blend – on the one hand, it’s a cesspool, a rendezvous place for drug dealers, black hat hackers, hitmen, and human traffickers.
On the other hand, due to its covert nature, this Internet fold acts like a liaison between political outcasts and people in the free world. It’s also used by people who want to submit anonymous tips (whistleblowers).
The Malware-as-a-Service Ecosystem
Malware developers
Information security researchers and developers work together to identify information security vulnerabilities through designing exploits, writing malware, and doing research on information security issues.
It’s crucial to remember that virus creators aren’t necessarily hacking activists who are breaking the law in their activities.
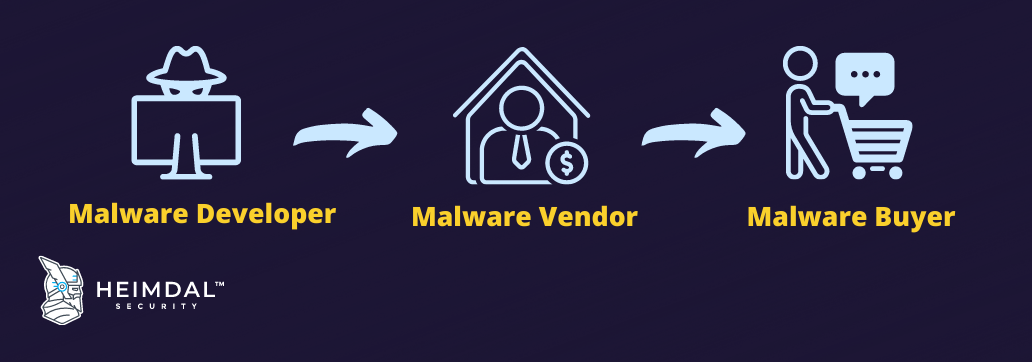
Malware distributors and sellers
Malware vendors often advertise their goods on darknet marketplaces and aggressively seek out new customers to purchase their malware.
Sellers often categorize their malware into two categories: malware packages that may be assembled by the customer and hosted management services that are required for malware distribution.
The virus in do-it-yourself malware packages is not only malicious, but it also includes thorough instructions on how to adapt the malware to meet the specific demands of the person who is deploying it.
Malware vendors often provide hosted management services, which enable their customers to propagate malware even farther across the Internet.
Malware buyers
Buyers of malware may be split into three types, namely, criminals who want to use the malware for nefarious reasons, security researchers who want to detect and solve security flaws, and government officials who want to identify and address security vulnerabilities.
How to Protect Yourself from MaaS?
As a result of MaaS, cyber attacks have become much more complex than they were before, as MaaSs make use of botnets, thus making their assaults are far more effective.
Since a single data breach has the potential to bring down a whole system in one fell swoop, attackers seem to have a significant edge for the time being.
Unfortunately, an effective defense cannot be built on commercial firewalls in order to cope with a certain threat type, therefore you might need to have a cybersecurity strategy properly tailored to the architecture of your system.
Another aspect that you should take into consideration is achieving total visibility into the attack surface, as security teams cannot guard what they are unable to see.
The ability to have complete insight into an organization’s environment is the cornerstone of every effective security operation.
Effective vulnerability management is crucial to protecting the organization’s assets in the face of an ever-expanding threat environment, as it allows the security teams to swiftly detect and repair vulnerabilities that are not protected by security measures and that could be exploited.
How Can Heimdal™ Help?
Threats at the domain level represent the new normal nowadays. That is why an efficient cloud-based security solution is the answer to this problem. Try out our awarded Threat Prevention, an outstanding DNS traffic filtering that has found the perfect way to mix together ingredients like Machine Learning, cybercrime intelligence, and AI-based prevention into a perfect cybersecurity recipe that safeguards your business-critical assets from DNS threats with an accuracy of 96%. No time to get hacked as you are busy taking threat hunting to the next level!
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security