Contents:
Solana cryptocurrency owners are being targeted by NFTs pretending to be alerts for a new Phantom security update. This will result in the installation of password-stealing malware and the theft of cryptocurrency wallets.
Upon a Closer Look
Since its beginning two weeks ago, the attack starts off with NFTs titled ‘PHANTOMUPDATE.COM’ or ‘UPDATEPHANTOM.COM’ sent as warnings supposedly from the developers of Phantom.
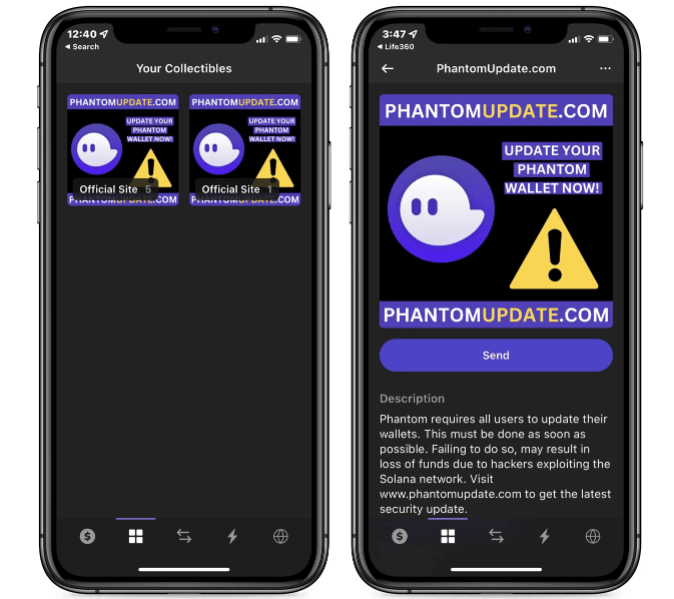
Fake Phantom security update NFTs –Source
When opening the NFTs, wallet owners are prompted to click the enclosed link or visit the site to download and install a newly released security update. These sites, whether accessed from desktop or mobile, will automatically download a Windows batch file named Phantom_Update_2022-10-08.bat from DropBox.
When the batch file is launched, it will check if it is running with Administrator privileges and, if not, show a Windows UAC prompt asking for permissions. If the UAC prompt is accepted, a PowerShell script will be launched that decrypts further commands to execute in Windows.
Ultimately, this will lead to a windll32.exe executable being downloaded from GitHub and executed from the C:\Users\<username>\AppData\Local folder. The windll32.exe file turns out to be a password-stealing malware that attempts to steal not only passwords, but also browser information, such as history and cookies, as well as SSH keys and other information.
According to BleepingComputer, victims who installed the fake Phantom security update are advised to immediately scan their device with an antivirus program and then transfer crypto funds and assets from their existing Phantom wallet to a new one.
While it is unclear what specific password-stealing trojan is currently being spread, previous campaigns distributed a file name lib64.exe, which was identified as Mars Stealer.
What Is Mars Stealer
An information-stealing malware launched in 2020 that allows threat actors to steal data from all popular web browsers, two-factor authentication plugins, and multiple cryptocurrency assets presents itself by the name of Mars Stealer.
In a report on Mars Stealer, the researchers claim they were able to link the cyberattacks to a Russian speaker and identify the threat actor’s GitLab accounts among other things.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, YouTube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security