Contents:
In August 2014 our security labs completed an intelligence analysis of software vulnerabilities. It indicated that the problem of software vulnerabilities is growing and that security gaps should be closed faster.
The main problem that we noticed was that security patches from the vendors don’t immediately follow the frequency of appearance by which online criminals launch new exploit kits.
The same analysis revealed that in the last years the most commonly used vulnerable 3rd party software are:
- Oracle Java Runtime environment
- Adobe Acrobat Reader
- Adobe Flash Player / Plugin
- Apple Quicktime
For more details, we invite you to read the entire article. It is still a relevant piece of information for our discussion.
What is Nuclear exploit kit?
Nuclear Pack, one of the most widely used exploit kits, has constantly evolved from 2009 – when it appeared for the first time – until now.
This kit is capable to deploy a wide range of attacks, from Flash, Silverlight, PDF, and Internet Explorer exploits to the possibility of launching advanced pieces of malware and ransomware.
Due to their polymorphic nature, exploit kits are main vehicles for zero-day attacks and software vulnerabilities and have become the main tools used by online criminals to launch data exfiltration operations.
Along the years various industries have been affected and the traffic volume of compromised websites have increased. Major sectors of economy have been subjects to major data breaches, from business services, finance, communications and government.
Recent developments
One of the most infamous exploit kits known as “Nuclear” has implemented an exploit in Adobe Flash Player that was patched just a week ago. The exploit in question is related to CVE-ID: CVE-2015-0336.
If you have not patched your Adobe Flash Player yet, you should do it as soon as possible. This exploit kit is able to deliver malicious code to Windows operating systems that lack the latest security patch from Adobe. The problem becomes so much more severe if we take into account that now this exploit kit is able to deliver not data-stealing malware, but ransomware.
And when we say ransomware, we are referring to various CryptoLocker variants, like Teslacrypt and CTB-Locker.
For more information on latest ransomware threats and how to stay safe, access the corresponding articles above.
How does it spread?
This latest Adobe Flash Player vulnerability exploited by Nuclear kit has been deployed through drive-by downloads in legitimate websites and online ads.
A part of this malicious activity is delivered via hijacked Godaddy domains (through which numerous subdomains are created) and also via iframe injections embedded in legitimate websites.
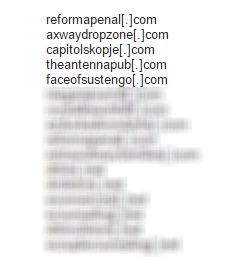
Our malware researchers have already blocked a large number of domains related to Nuclear, by using our advanced Secure DNS technology:
According to other sources from IT industry, it seems that more than 90% of computers affected are to be found in Japan. Apparently, this exploit is mainly distributed online by using compromised web pages and Japanese pornographic websites.
I have antivirus protection. I’m safe, right?
Well, not really. The bad news is that Nuclear, the latest Flash Player exploit kit has been protected with Protect SWF from Kindi [.] Com.
Though it is a legitimate piece of software, which has been designed to protect the Flash content from being decompiled by third party software, in this case this feature makes it difficult for antivirus solutions to access the hidden malicious code and block it from being delivered.
How can I keep my system protected from Nuclear?
Our malware researchers recommend the following security measures to keep your computer safe from Nuclear exploit kit:
- Keep your Windows operating system and your vulnerable software up-to-date with the latest security patches, in this case Adobe Flash Player. To make sure you are protected, use a patch management software to update the software automatically for you.
- Create a Backup for your operating system or for your most important data. Make sure the backup is not placed in the same location with your actual operating system. In case your system is affected by ransomware, you will not be able to access the backup.
- Make sure your security solution detects and blocks exploit kits or use an extra layer of protection, like Heimdal™ Threat Prevention, a solution that protects users from exploit kits that come even from legitimate websites and detects ransomware threats.
- Use a good anti-spyware solution to remove phishing or exploits focused on malicious emails.
- A solution to control the Adobe Flash Player browser integration is to enable this “click-to-play” plug-in that lets you control the Flash Player content loading.
Conclusion
Since software vulnerabilities and exploit kits go hand in hand, Adobe Flash Player will remain a hacker’s favorite target.
We know that online criminals use a vast array of weapons against computers, from phishing attempts in spam campaigns and drive-by downloads to deliver malware but, as we have recently disclosed in this article, 70% of web attacks target a software vulnerability on your computer and 90% of them are delivered from advertising networks and websites that deliver drive-by downloads.
For more technical details and an extended presentation on how exploit kits are used to deliver cyber-attacks, check our article.
Keep calm and update your software!











 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security