Contents:
GoTrim, a new Go-based botnet malware, scans the internet for WordPress websites and attempts to brute force the administrator’s password and take control of the site.
Compromise means potential security risks, including malware deployment and injection of scripts that steal credit card information, being capable of impacting millions, depending on the popularity of the breached sites.
GoTrim Targets WordPress Sites
The GoTrim malware campaign was first observed in September 2022 and is still ongoing. The botnet is notorious in the cybercrime underground but following a thorough analysis, the Fortinet researchers reported that the malware is still a work in progress.
GoTrim’s operators feed target websites and a specific set of credentials to the botnet network. Next, the malware connects with each site and tries to brute force the admin accounts using the given information.
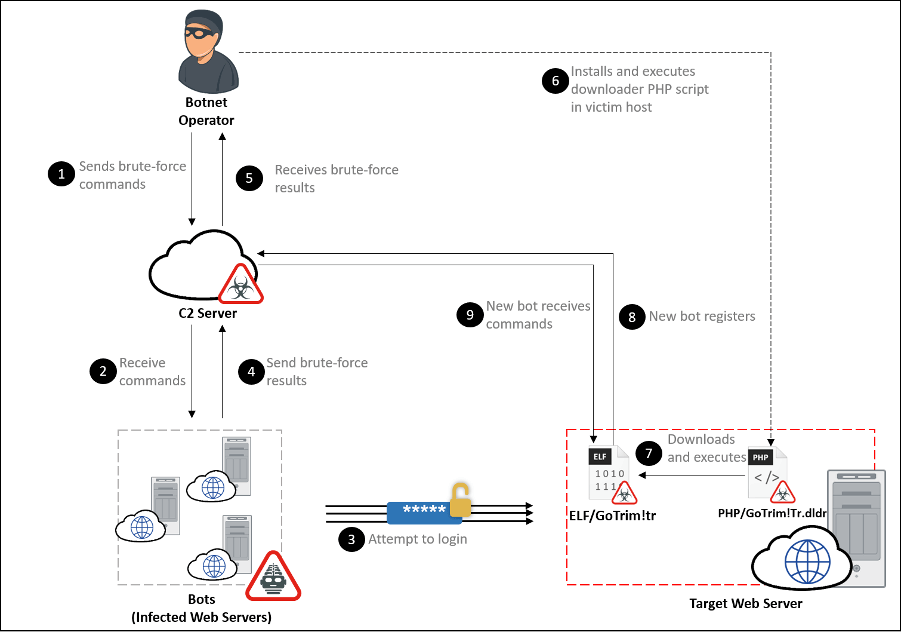
Once a website is breached, GoTrim logs in to the site and reports the infection to their C2 server. The bot ID is automatically generated using MD5 hashing. After this, the malware uses PHP scripts to fetch GoTrim bot clients from a hardcoded URL and deletes both the script and the brute-forcing component from the infected system.
How it Operates
The botnet operates in “client” and “server” mode.
In server mode, the malware will initiate a connection with the botnet’s C2. Meanwhile, in client mode, it starts an HTTP server and waits for requests from the C2. However, if the breached endpoint is directly connected to the internet, GoTrim defaults to server mode.
GoTrim sends beacon requests to C2 every couple of minutes. It will continue to send them until it receives a response, and if there is no response after 100 tries, the process will terminate.
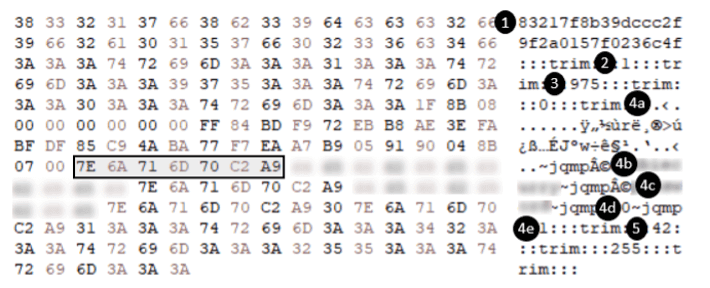
The response containing the command and its options.
According to BleepingComputer, the C2 can send encrypted commands to the GoTrim bot, such as:
- Validate provided credentials against WordPress domains
- Validate provided credentials against Joomla! domains (not implemented)
- Validate provided credentials against OpenCart domains
- Validate provided credentials against Data Life Engine domains (not implemented)
- Detect WordPress, Joomla!, OpenCart, or Data Life Engine CMS installation on the domain
- Terminate the malware
It Evades Detection
To avoid being detected by the WordPress security team, GoTrim will not target WordPress.com sites and will only target the self-hosted sites. To do this, it checks the ‘Referer’ HTTP header for “wordpress.com,” and stops targeting the site once it detects it.
As managed WordPress hosting providers, such as wordpress.com, usually implement more security measures to monitor, detect, and block brute forcing attempts than self-hosted WordPress websites, the chance of success is not worth the risk of getting discovered.
Furthermore, GoTrim replicates legitimate Firefox Web requests on 64-bit Windows to bypass anti-bot protection.
Finally, the malware will check if the targeted WordPress website uses a CAPTCHA plugin and automatically load the corresponding solver. As this is being reported, it supports seven of the most popular plugins.
The best way for site owners to avoid being a victim of the GoTrim threat is to use strong passwords that cannot be broken through brute force, or to use a 2FA plugin in conjunction with the password.
As an admin, the best way to protect your WordPress site is to upgrade the base CMS software and all active plugins to their latest versions. Doing this will help you avoid any known vulnerabilities that could get your site breached.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security