Contents:
Digital services made for consumers are opening up new opportunities and vulnerabilities. With more employees bringing unmanaged devices to the office, business networks can be accessed by many more people. Plus, remote work means that an organization’s IT perimeter is no longer restricted within its walls. This raises new challenges for privileged access management tools.
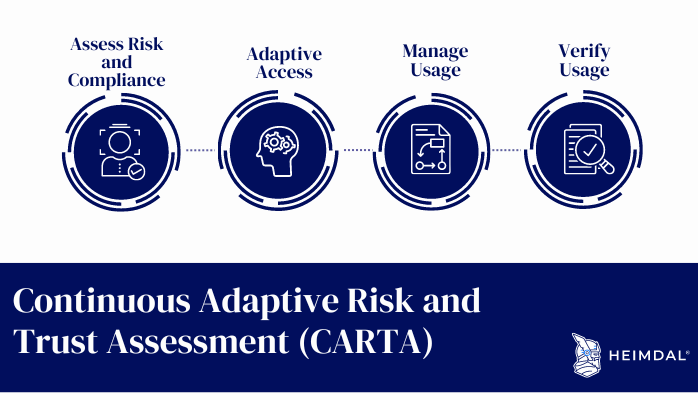
Continuous Adaptive Risk and Trust Assessment (CARTA) is an innovative new assessment methodology that combines the best of quantitative, qualitative, and psychometric approaches to produce better risk assessment data.
What Is Continuous Adaptive Risk and Trust Assessment (CARTA)?
CARTA is a security methodology that focuses on, as its name suggests, continuous, adaptive risk and trust assessment. In other words, CARTA is an IT security framework that goes beyond traditional Role-Based Access Control (RBAC). The addition of Attribute-Based Access Control (ABAC) enables continuous, context-aware security assessment in real-time.
First introduced by Gartner in 2010, CARTA aims to provide a more responsive approach to security than traditional approaches by constantly monitoring and responding to changes in the environment.
It does this by constantly assessing risks and trust levels across all systems and data sources, then using that information to adapt its security measures accordingly. This means that it can quickly identify and respond to new threats as they emerge, rather than waiting for attacks to happen and then trying to retroactively patch them.
Why Is Role-Based Access Control (RBAC) Inadequate?
RBAC can be complicated because it’s hard to keep track of permissions and restrictions. Further, some of RBAC`s drawbacks can be summarized as:
- a static security model and does not have the adaptive security capability.
- it cannot easily configure access, transaction, and data field level controls with policy requirements.
- a much less efficient approach to detecting threats and anomalies.
Instead of relying only on static controls, Gartner calls for a strategic approach known as “continuous adaptive risk and trust assessment”. The CARTA framework is focused on standardizing agility, enabling contextual awareness, and leveraging adaptive security technologies, thus helping organizations strengthen security and leverage automation for continuous improvement.
How CARTA Works
When it comes to traditional block/allow security solutions, decisions can’t be made based on context. Solutions also lack the ability to evaluate real-time data and can’t address employee mobility. The block and allow security strategy may pose more of a risk, because it automatically trusts all users or devices that have been “allowed” into the network. This can backfire without any reevaluation for unregistered or compromised users, potentially leaving open the possibility for zero-day attacks, insider threats, or other risks deriving from compromised credentials.
The Continuous Adaptive Risk and Trust Assessment aims to help reach informed decisions about risks and mitigation strategies.
CARTA Key Components
- Data Collection: it collects data from multiple sources (sensors, devices, networks, and people) and analyzes the information in order to identify risks.
- Identification: CARTA uses data analytics to recognize risks in real time, which includes identifying potential threats as well as vulnerabilities in people, devices, and systems.
- Assessment: Once risks have been identified, CARTA assesses the severity of these risks and determines the best course of action for mitigating them.
- Mitigation: it provides recommendations for mitigating risks, which may include changes to policies or procedures, training for employees, or the use of security technologies.
CARTA`s importance relies on providing a methodology for organizations to proactively and continuously assess and manage cyber risks. It also helps build trust within an organization by identifying potential risks and vulnerabilities and taking steps to mitigate them. Additionally, Continuous Adaptive Risk and Trust Assessment can help an organization establish a baseline of acceptable risk and ensure that its cybersecurity posture aligns with its business objectives.
How CARTA Relates to Other Risk Assessments
CARTA is not the only risk assessment methodology available, but it is one of the most comprehensive. Here’s how it compares to some other popular risk assessments:
– The National Institute of Standards and Technology (NIST) Risk Management Framework (RMF) is a government-developed process for identifying, assessing, and mitigating risks. CARTA can be used as part of the RMF, complementing its focus on compliance and security controls.
– The Open Web Application Security Project (OWASP) Risk Rating Methodology is a free and open-source tool for assessing the risk of web applications. CARTA can be used alongside OWASP to get a more complete picture of risks.
– The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards for businesses that handle credit card information. CARTA can supplement PCI DSS compliance efforts by identifying additional risks that may need to be addressed.
How to Implement Continuous Adaptive Risk and Trust Assessment
There are three essential phases to consider when implementing the CARTA model:
- Run -Organizations rely on automatic solutions during this phase. By using artificial intelligence to analyze data, anomalies are detected in real time. The net benefit is that the organization can respond to potential threats much sooner.
- Build -This goes hand-in-hand with the concept of DevSecOps. It involves building security into the development process by always evaluating and identifying security risks. With many modern applications pieced together from publicly available libraries, organizations need to make sure they are scanning those libraries for security risks before adding them to their program. Likewise, companies must evaluate ecosystem partners, including third-party developers or digital service providers, who need to interact with their environment.
- Plan -It is important to establish priorities when considering IT changes in the company. If you want to move your business to the cloud, how will you address the security implications inherent in that decision? Does remote work suit your staff’s needs better? By thinking about these aspects of IT and prioritizing them, businesses will be better positioned for making contextual decisions. That way, they avoid black/white decisions that are common with traditional IT.
CARTA vs. Zero-Trust
CARTA continuously evaluates all users and devices and makes contextual access decisions. It has its roots in the Zero-Trust framework, which advocates the idea that no user or device can be trusted, even if they’re already on your network. Companies with zero trust security go to great lengths to ensure that only appropriate access is granted to critical assets. To start this process, it’s important to prioritize and protect high-risk areas such as supply chains, contractors, temporary employees and sensitive networks. This initial step helps reduce the risk of attackers abusing accounts that might have less visibility or security.
Under this concept, everything starts with a zero-trust posture so that an organization can measure the extent of security protection it requires. The level of protection required depends on what data needs to be protected, for how long, and who needs access to it. If more control or restrictions are necessary to meet specific business requirements, then a micro-segment or individual asset can be assigned a different level of trust and verification.
How Can Heimdal® Help?
A good, automated Patch Management solution is a crucial aspect when it comes to software updates. Maintaining the security, integrity, and accessibility of the data and systems of every organization should be as thorough as possible but simple and fast at the same time. The more you keep up with your patching and update all your critical and non-critical systems alike, the less likely it is that your organization will be compromised.
Patch management plays a significant role in ensuring strong organizational protection. However, it should not be viewed as the answer to solving all security issues, but as an essential layer of protection for your business, alongside DNS filtering, Endpoint Antivirus & Firewall, and Privileged Access Management (PAM)

Heimdal® Patch & Asset Management Software
- Schedule updates at your convenience;
- See any software assets in inventory;
- Global deployment and LAN P2P;
- And much more than we can fit in here...
Wrapping Up….
CARTA is an improved security framework, especially for businesses that cannot apply RBAC to everyone accessing their network. As a cybersecurity approach, it emphasizes continuous monitoring and assessment of risks in order to adaptively respond to changing threats. This makes it an effective way to stay ahead of cyber criminals, who are constantly evolving their methods. While CARTA may require more resources than traditional security methods, the benefits make it worth the investment for many organizations.
If you enjoyed this article, follow us on LinkedIn, Twitter, Facebook, Youtube, or Instagram to keep up to date with everything we post!










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security