Contents:
Threat actors offer over 200 million Twitter users` profile data on the Breached hacker forum, asking no more than $2 for the whole database.
Cyber researchers say this is the cleaned-up version of the 400 million profiles database spilled in November last year, which contained lots of duplicates.
According to threat actors, the data was collected in 2021, using a Twitter API vulnerability that was fixed in July 2022.
When threat actors exploited the vulnerability in 2021, they came up with a huge list of email addresses and phone numbers. They further exploited another API bug and scraped the public Twitter data for the IDs. This way they managed to combine public data with private ones, such as email addresses and phone numbers.
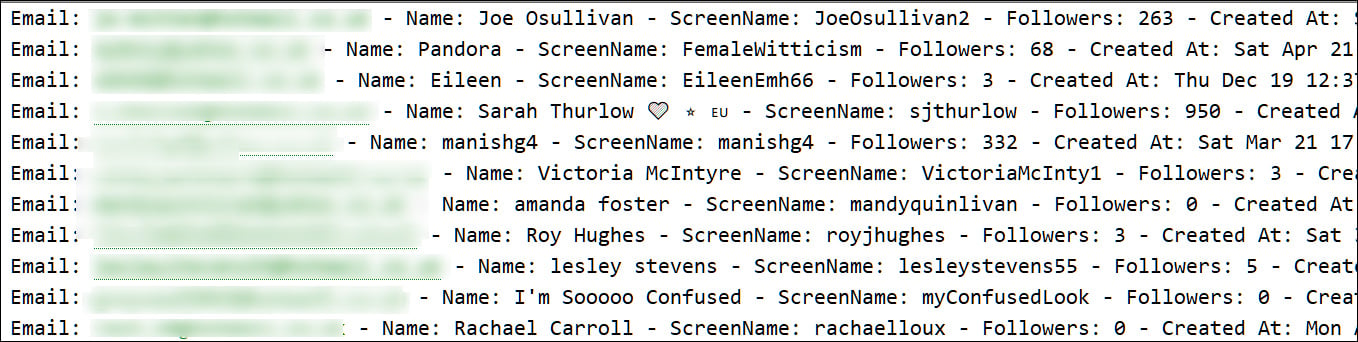
Each line in the files represents a Twitter user and their data, which includes email addresses, names, screen names, follow counts, and account creation dates.
Unlike previously leaked data collected using this Twitter API flaw, today’s leak does not indicate whether an account is verified.
How Does This Data Spillage Impact Twitter Users
For starters, the email addresses threat actors obtained can be used for launching phishing attacks. Also, the accounts that have lots of followers could be used for online scams, like stealing cryptocurrency.
Twitter users who preferred to keep their privacy and use the social media platform anonymously should be on guard. The leakage makes their accurate identification possible, and it`s very likely that they could be exposed. Unfortunately, there seems to be no solution for them to avoid publicity if hackers set their minds to reveal their identities.
Since data keeps being exposed on hacker forums, Twitter users are advised to beware of spear phishing attacks and watch out for any password-stealing attempts.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security