Contents:
Vulnerable security administration and frail organizational structures are turning manufacturing businesses into profitable targets for threat actors, with over half of manufacturers admitting they have been victims of cyberattacks. The WestRock ransomware attack is the most recent example.
For manufacturers, technology-level and organizational-level challenges often lead to potentially devastating disruptions. According to Decipher’s report, of the surveyed organizations that experienced cyberattacks, 75% suffered system outages, with 43% saying their outages lasted more than four days.
What’s more, Trend Micro revealed that 61% of manufacturers have experienced cybersecurity incidents in their smart factories and “are struggling to deploy the technology needed to effectively manage cyber risk”.
WestRock Ransomware Attack: A Timeline
On January 25th, 2021, WestRock, the second-largest packaging company in the United States, announced that it has been the victim of a ransomware attack.
The WestRock ransomware attack impacted some of the company’s core operational technology (OT) systems and hindered production and packaging-converting operations, which resulted in lagged production levels.
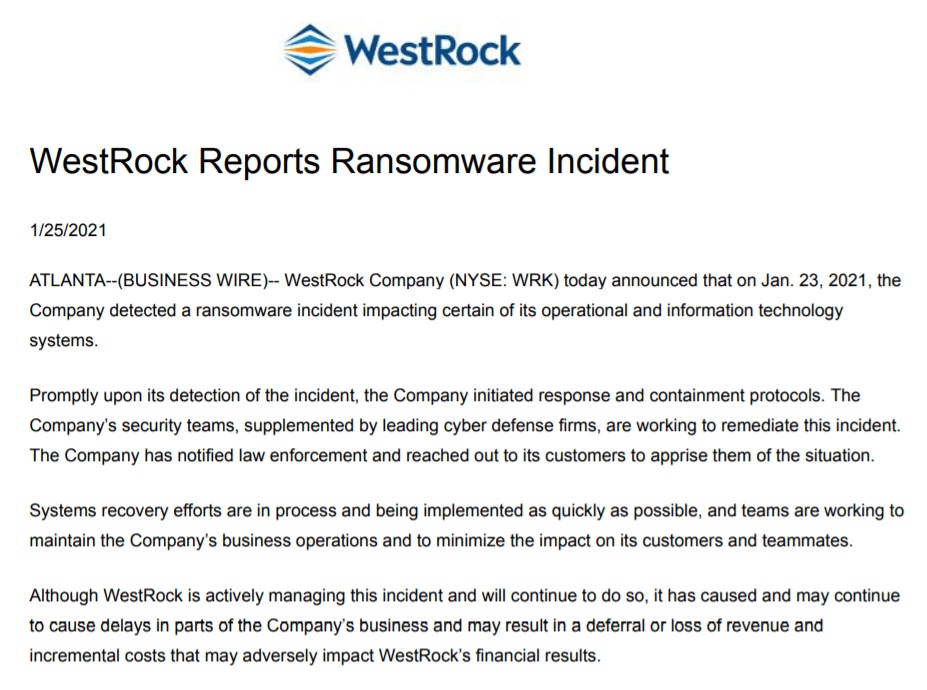
Source: WestRock
The manufacturing giant, which has over 300 facilities around the world, catering to the packaging needs of high-profile clients like General Motors, Heinz, and Home Depot, revealed that its teams are working to maintain the company’s business operations and to minimize the impact on its customers and teammates.
A week and a half later, on February 5th, WestRock released an update saying its “mill system production through February 04 was approximately 85,000 tons lower than plan”. As a response to the attack, the company had to implement business continuity processes, and initiate response containment protocols with the support of cybersecurity experts, including proactively shutting down certain systems in an abundance of caution.
The Company maintains a variety of insurance policies, including cyber insurance and business interruption insurance. There may be a time lag between the initial incurrence of costs and the receipt of any insurance proceeds as the Company’s operations return to normal. WestRock continues to assess the overall operational and financial impact of the incident.
Source: WestRock
In the same update, WestRock confirmed they started an investigation about the ransomware attack and were in the process of recovering from its disruptive effects.
On March 7th, WestRock provided an update regarding the running quarter. Despite the ransomware attack and some disruptions caused by adverse weather, the company has grown its North American box shipments per day by 6% over the prior year’s quarter.
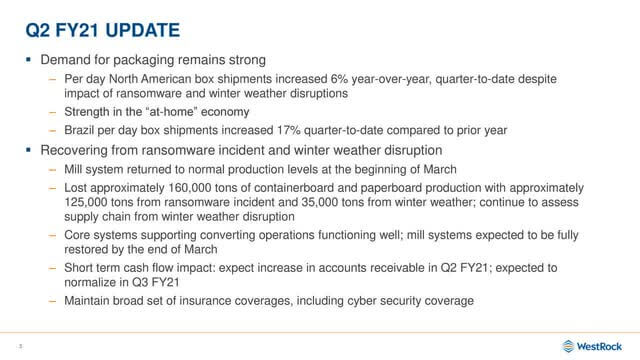
Image Source: Seeking Alpha
How Attacks on Operational Technology Became the Next Cyber Boundary
According to Control Automation, ransomware attacks that impact industrial production have severely increased over the past few years, with names like WannaCry, Ryuk, and MegaCortex being responsible for attacks in over 150 countries and overall losses summing billions of dollars.
Decipher journalist Lindsey O’Donnell-Welch notes that on top of the security issues plaguing OT systems, 67% of manufacturing experts believe flawed organizational processes within manufacturing companies are making security more difficult. Few organizations have teams that collaborate across the IT and the OT segments – which oversee ICS devices and manage physical processes tied to industrial equipment.
The immediate impact of a cyberattack on OT is business interruption, especially if a manufacturer’s logistics and supply chain processes go down, as was the case of the WestRock ransomware attack.
Depending on how elaborate and severe a cyberattack is, the longer-term impacts include:
- financial loss, due to theft of money, corporate information, trading disruption, loss of contracts/clients. We must not forget to mention the possible repairing that the affected systems, networks, and devices might require.
- reputational damage. Losing your clients’, partners’, and investors’ trust can lead to a serious reduction in profits, which translates again into financial loss.
- legal actions. It is highly important to protect the data of your employees, clients, and providers, especially in these times of GDPR and other similar regulations. If this data has been somehow compromised, you can expect fines and regulatory sanctions, maybe even civil lawsuits.
The WestRock ransomware attack is a prime example of how a cyberattack on manufacturing and other OT systems can be leveraged by cybercriminals to damage an organization.
This is especially true as these systems become increasingly modern and built of connected devices that are part of the Industrial Internet of Things (IIoT).
When interviewed by SecureWorld, Phil Quade, CISO at Fortinet and former NSA official revealed that a growing number of organizations are taking OT security seriously:
The cybersecurity of today is becoming connected enough and reliable enough that it can allow you to implement the newest features without risking a catastrophic loss to availability and reliability. So, I think that cybersecurity has shifted, and it’s becoming more of an enabler rather than a burden. I think more and more we’ll see cybersecurity creep into additional OT environments and they will become more connected.
Source: SecureWorld
Despite the production lag, WestRock explained that “this gap is closing immediately as methods are restored”. The company’s packaging changing operations were also shut to returning to total planned generation ranges.
The WestRock team remains in regular communication with its customers to share information and updates and to meet their business needs. WestRock is also working with its vendors so they are informed, and supply chains remain operational.
Source: WestRock
What is still unknown is what type of ransomware was used in the attack, whether a ransom was paid and how the attack was introduced. So far, WestRock provided no information in this regard.

Heimdal® Network DNS Security
- No need to deploy it on your endpoints;
- Protects any entry point into the organization, including BYODs;
- Stops even hidden threats using AI and your network traffic log;
- Complete DNS, HTTP and HTTPs protection, HIPS and HIDS;
Protect Your Organization
Reactive cybersecurity solutions can only get you so far in terms of incident mitigation. As cyber-threats become increasingly refined, they will eventually manage to outrun your antivirus. This is why your organization should focus on a proactive solution that reinforces the weak spots in your system and detects intruders before they manage to infiltrate.
Our Heimdal™ Threat Prevention does just that (and more), impeding the executable ransomware file from connecting to the Command & Control server giving it orders. This occurs not only at the level of your browser but through any process ongoing at the endpoints in your institution’s network. It achieves this by operating within the layers of the DNS, HTTP, and HTTPS alike with proprietary DarkLayer Guard and VectorN Detection technology.
In addition to this, Heimdal™ Threat Prevention also features an Heimdal™ Patch & Asset Management module that automatically deploys software patches within a few hours of their release. This will further close any vulnerabilities in your system and prevent malicious attackers from gaining entry.
Final Thoughts on the WestRock Ransomware Attack
The WestRock ransomware attack should be regarded as a teachable moment. Cyberattacks on Operational Technology are not something to be taken lightly. Strengthen your organization’s defenses today and let’s make sure together that this type of incident doesn’t hold another manufacturer too soon.
As always, don’t hesitate to leave any questions, comments, or concerns in the comments section below. I look forward to reading them all!










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security