Contents:
A new SMS smishing malware that targets Android mobile users in the U.S. and Canada has been discovered by cybersecurity researchers.
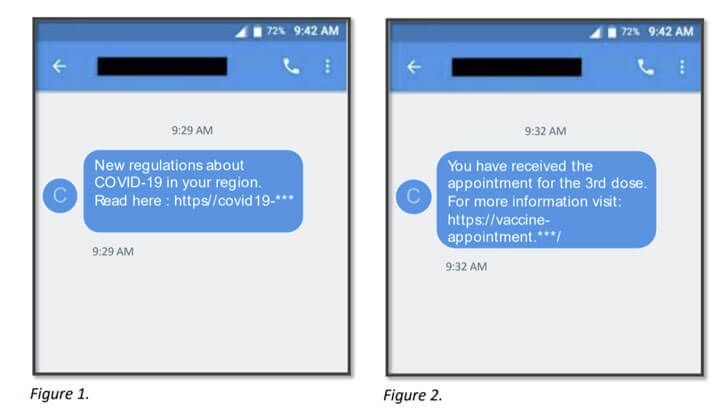
The malicious campaign uses text message lures related to COVID-19 regulations and vaccine news to trick victims into clicking on a link that will infect their mobile devices.
Analysts at the mobile and email security company Cloudmark dubbed the malware TangleBot and according to them, hackers use this new form of malware in an attempt to steal confidential and banking information.
The malware has been given the moniker TangleBot because of its many levels of obfuscation and control over a myriad of entangled device functions, including contacts, SMS and phone capabilities, call logs, internet access, and camera and microphone.
Not only that the malware is able to gain private data, but it can also overlay banking or financial apps and directly steal the victim’s account credentials.
How Does It Work?
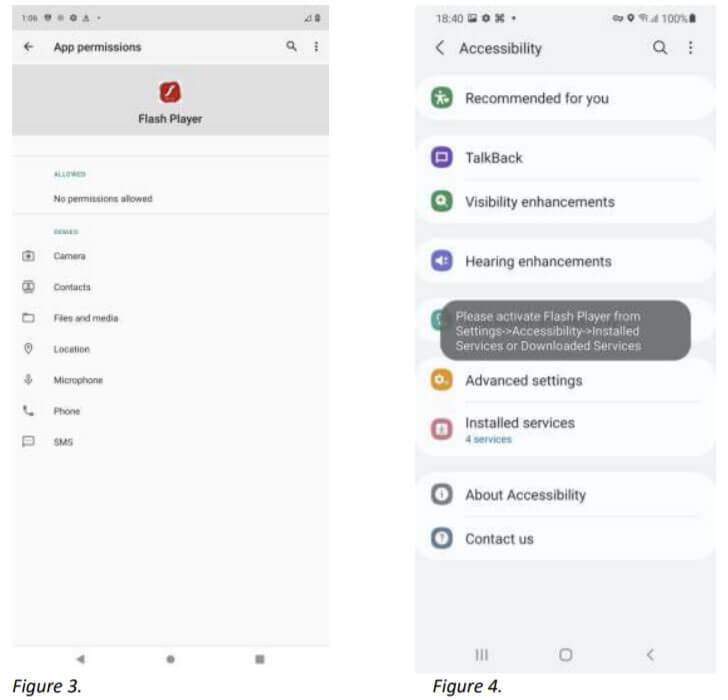
The attacks start with text messages that pose as COVID regulations and the third dose of COVID vaccines appointment confirmations content, urging subscribers to click on the link in the message. Then a website appears informing the victim that their Adobe Flash player is out-of-date and requires updates.
As soon as the user decides to “update” the software, the TangleBot malware gets installed on the Android device.
What Happens Next?
Following the fake update, the TangleBot malware can now access and manage functions such as contacts, SMS and phone capabilities, call logs, internet, camera, and microphone, and the location service and the hackers can:
- intercept phone calls;
- send and receive text messages;
- record the camera, screen, or microphone audio or stream them directly to the cybercriminals;
- implement other device observation capabilities.
What Can Users Do?
Cloudmark advises users to pay attention to suspicious messages and think twice before providing their mobile phone numbers to companies.
If users receive an SMS from a company that includes a web link, they shouldn’t click on the link provided in the text message. Instead, use their device’s browser to access the firm’s website directly.
The users are also advised to report any attempt of SMS phishing and spam and avoid the installation of software that’s outside a certified app store from the vendor or Mobile Network Operator.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








