Contents:
An alert has been issued by the Computer Emergency Response Team of Ukraine (CERT-UA) on October 21st regarding Cuba Ransomware attacks potentially targeting the country’s critical networks. CERT-UA observed a new wave of phishing emails impersonating the Press Service of the General Staff of the Armed Forces of Ukraine, which urged the recipients into accessing an embedded link.
Details on the Attack
The link embedded in the email takes the recipients clicking it to a third-party web page to download a document named “Наказ_309.pdf”. However, the victims are shown a fake PDF reader update alert, which if triggered will lead to the download of an executable (“AcroRdrDCx642200120169_uk_UA.exe”) imitating the Acrobat Reader installer.
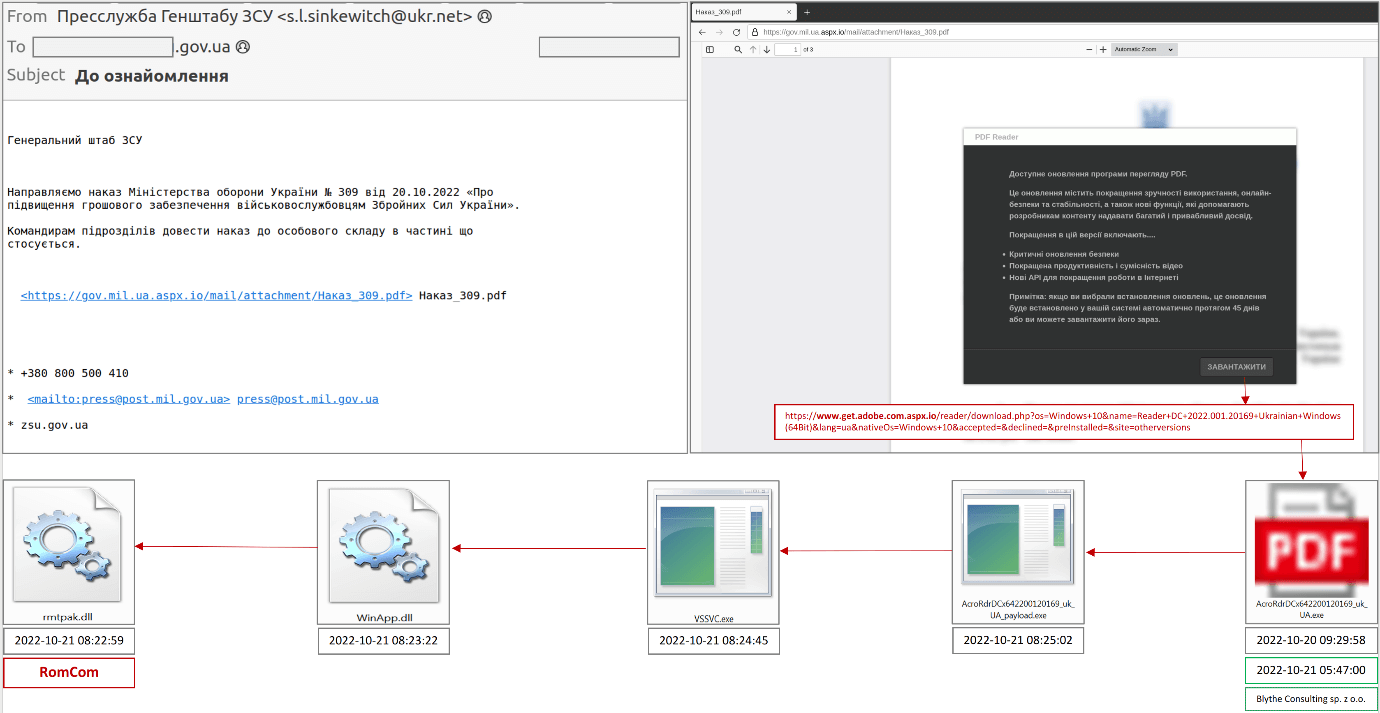
By running the installer, the victim will download and then automatically execute the “rmtpak.dll” file, also known as “RomCom RAT.”, which is Cuba Ransomware’s signature malware. RomCom was first spotted in August 2022 by security researchers, which gave the name “Tropical Scorpius” to the Cuba Ransomware affiliate using the forementioned RAT.
According to BleepingComputer, the malware allows threat actors to perform actions such as file operations on the host, steal data, spawn spoofed processes, start reverse shells and more.
In view of the use of the RomCom backdoor, as well as other features of the linked files, we consider it possible to associate the detected activity with the activities of the Tropical Scorpius (Unit42) group aka UNC2596 (Mandiant), which is responsible for the distribution of Cuba Ransomware; CERT-UA monitors activity by the identifier UAC-0132.
Cuba Ransomware has been operating since 2019 and its activity, although not as intense as other operations, has generated massive hits, obtaining millions of dollars through ransomware from more than 50 organizations.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security