Contents:
Database sharing and marketplace forum RaidForums has recently made a mistake that led to the exposure of internal pages from its website that were supposed to be accessed and seen only by its employees.
RaidForums is a clandestine marketplace and hacker forum that was founded in 2015. It has exclusive database breaches and leaks and an active marketplace to sell, or sometimes offer for free, these leaks.
With a total of 445K users, more than a thousand new members register at Raidforums every day and 15K individuals use the forum each day as members and guests.
What Happened?
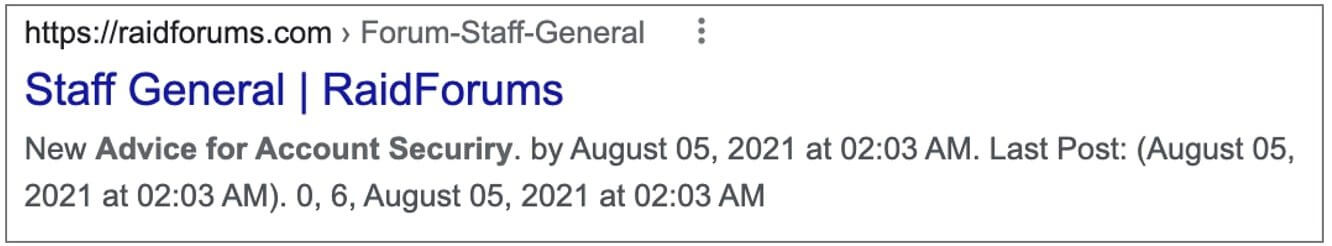
On the RaidForums website, the employees are the only ones who can access the “Staff General” section but due to a mistake, this section has been made public allowing everybody to see its topics.
As seen by BleepingComputer, some of the confidential pages, as recent as September 20th, were indexed by Google:
BleepingComputer noticed that the indexed post included “advice for account [security]” geared towards communicating security best practices to forum admins and moderators. The note contained tips on:
- using password managers;
- enabling two-factor authentication for an account;
- using VPNs.
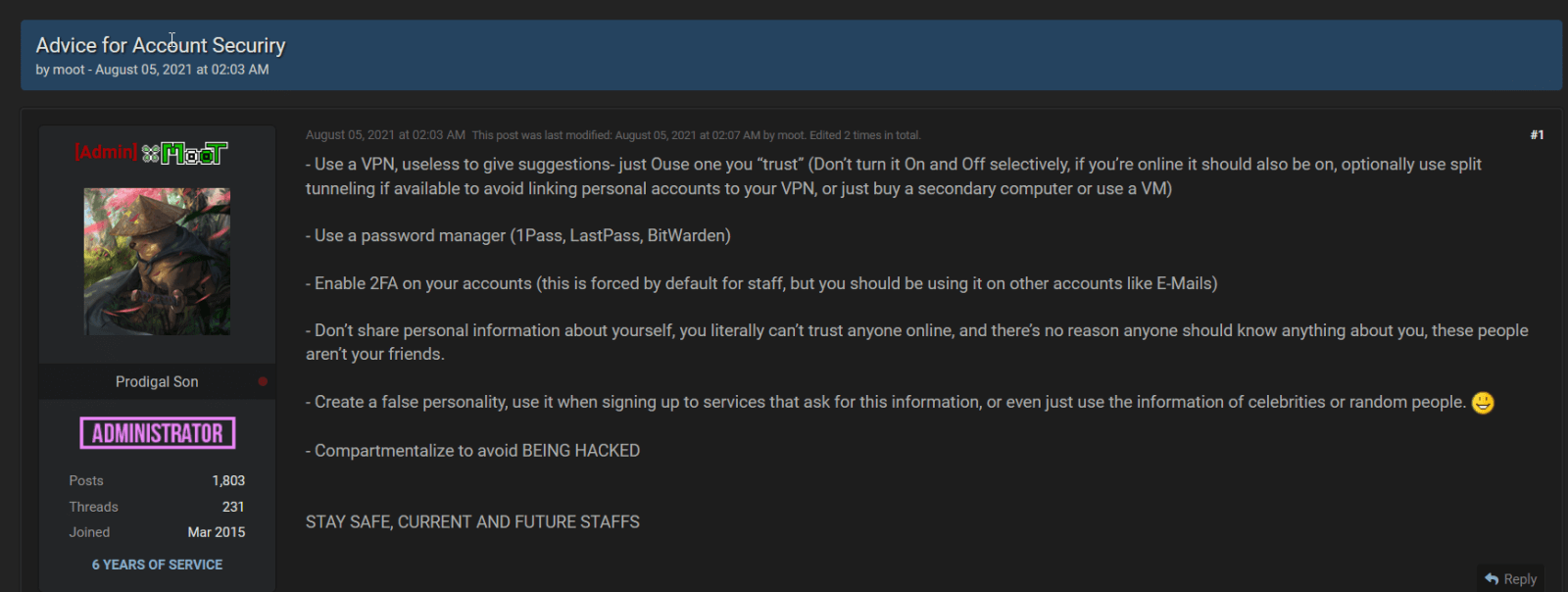
Create a false personality, use it when signing up to services that ask for this information, or even just use the information of celebrities or random people.
Bans-related conversations, the ideal location for hosting staff chat, and various requests are among the topics that have been made public.
As noticed by BleepingComputer, the internal pages were public up until this week, indicated by a timestamp at the bottom of the page stating the current time to be “September 20, 2021, 05:17 AM.
At the moment, the exposed section is back on being private.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security