Contents:
Security researchers witnessed and reported on a Trickbot resurgence in the past few days. Apparently, now Trickbot launches BEC attacks carefully targeting important people within US-based organizations. Key people within the targeted organizations receive highly worrying emails claiming that someone at work filed a sexual harassment complaint against them.
The emails are allegedly coming from the U.S. Equal Employment Opportunity Commission (EEOC), exactly the authority which deals with such complaints. The messages are looking official enough not to arouse suspicions right away. The hackers behind this new Trickbot campaign are really choosing their victims in a smart way, from the upper tier of businesses and organizations.
Here is how Trickbot aims to wreak havoc now and how to recognize it.
How Trickbot Launches BEC Attacks and How the Emails Looks Like
Over time, Trickbot achieved notoriety with its capacity to adapt and change strategy. Either it was targeting the financial sector (in the beginning), or gaining internet worm abilities, or spoofing trusted brands like Dropbox, or learning to disable Windows Defender. The attackers behind Trickbot were always creative and knowledgeable, which is how Trickbot managed to surpass Emotet and become the biggest malware threat today.
In its newest tactic, Trickbot now sends emails claiming to be on behalf of the U.S. Equal Employment Opportunity Commission, due to an alleged complaint against the target made by a colleague. In order to find out who accused them of sexual misconduct in the workplace, the victim has to open the email attachment.
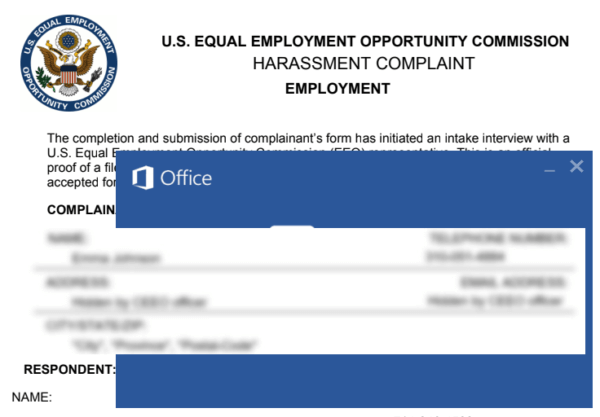
The caption of the fake Trickbot BEC email, via BleepingComputer.com.
The name of the attachment is something along the lines of Name_of_Victim – Harassment complaint letter (phone 111-222-3333).doc. Within that attachment, Trickbot is hiding, ready to infect the victim’s machine and potentially breach the network of the entire organization.
There are some other signs that something is amiss in the new Trickbot campaign. If the emails are analyzed carefully, one can notice spelling mistakes and all the things that usually give fake emails away.
Sadly, this newest instance of spear-phishing found a goldmine of social emotion to exploit: fear. Nothing new on this count, since that’s how all kinds of social engineering attacks work, by exploiting common human emotions and drives.
But lately, hackers are really upping their game on this account: last week it was fake court subpoenas, today it is fake sexual harassment complaints.
How to Protect Yourself from This New Wave of Trickbot Attacks and Spear-Phishing in General
No matter how urgent and serious an email seems to be, don’t click links and don’t open attachments if it’s about something out of the ordinary. That sense of urgency and seriousness is exactly what hackers are aiming for.

Heimdal® Email Security
- Completely secure your infrastructure against email-delivered threats;
- Deep content scanning for malicious attachments and links;
- Block Phishing and man-in-the-email attacks;
- Complete email-based reporting for compliance & auditing requirements;
Don’t click on links and attachments until you check the validity of the email through alternate means. These alternate means can include: getting in touch with the legitimate sender over phone / new email thread / social media accounts, checking with the police or your cybersecurity provider, running the email through an email security tool that protects against BEC attacks and so on.
Final Words
Personally, I am very saddened to see that Trickbot contributes to a #MeToo-like panic with these fake sexual harassment claims scare. I think that there’s this pervasive and really damaging myth, that the current campaign against sexism and harassment in the workplace can somehow make victims out of innocent men. While it’s wise to never say never, this is highly unlikely, and decent people really do not have anything to worry about.
But the way Trickbot launches BEC and phishing attacks now is capitalizing on this damaging myth and is also helping to spread it, unfortunately. My advice to anyone, regardless of the exact nature of a worrisome email you are receiving, is to not believe anything until you investigate.
Stay safe!










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








