Contents:
According to cybersecurity researchers at NCC Group, ransomware attacks in November 2021 increased significantly over the previous month, with double extortion remaining a powerful weapon used by all kinds of cybercriminals.
What Is Double Extortion Ransomware?
As I extensively explained in one of my articles,
“Double extortion, also known as pay-now-or-get-breached refers to a growing ransomware strategy and the way it works is that the attackers initially exfiltrate large quantities of private information, then encrypt the victim’s files. Following the encryption, the attackers threaten to publish the data unless a ransom is paid.”
Malicious actors’ interest is quickly shifting to government organizations, which have seen 400% more attacks compared to October.
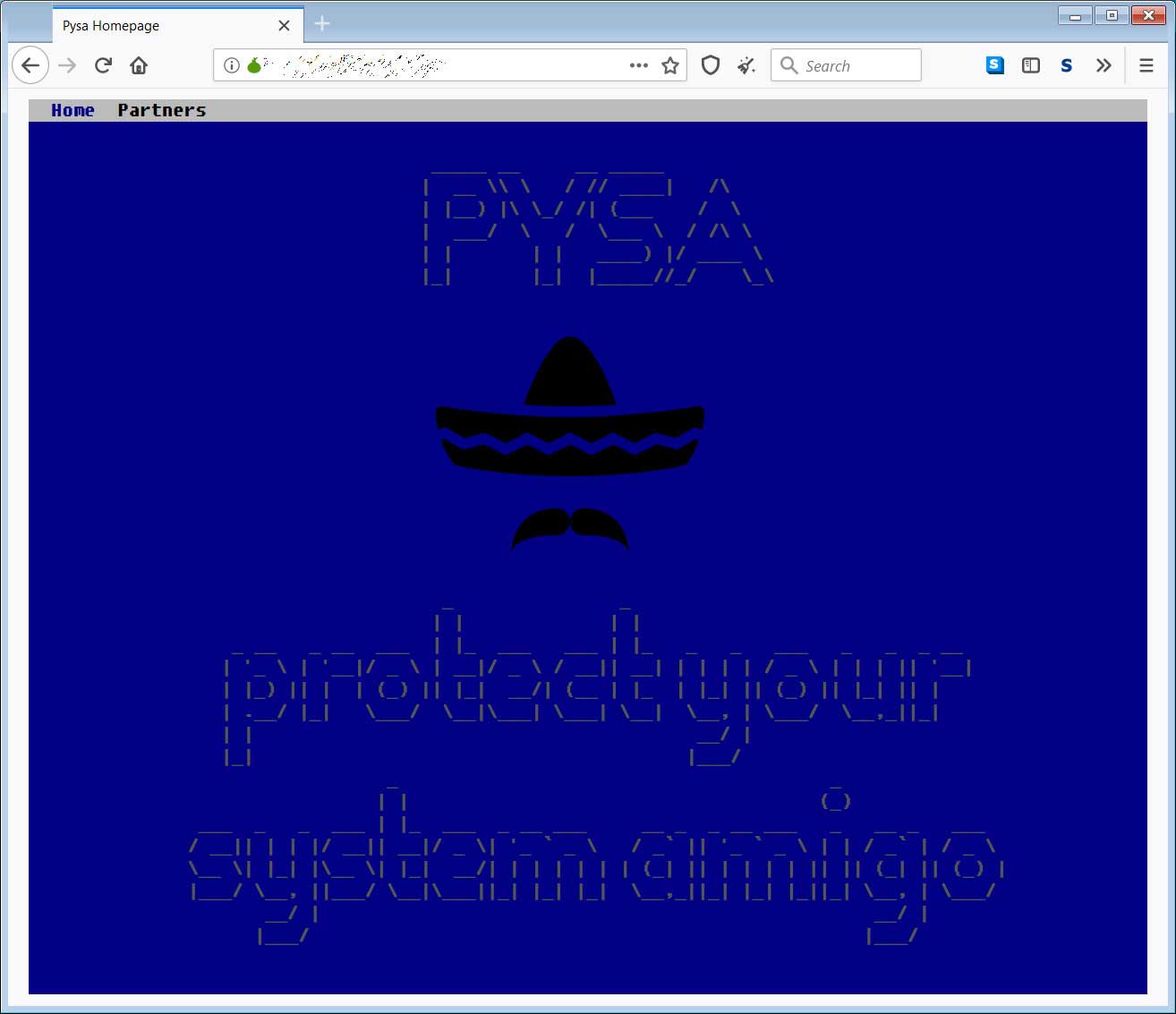
The Main Character: PYSA
PYSA ransomware organization (also known as Mespinoza) stole the show in November, with a 50% spike in infections.
PYSA is a form of ransomware that is increasingly being employed in “big game” assaults, in which attackers select their targets based on their projected ability to pay. PYSA is an acronym for “Protect Your System Amigo,” which is included in the ransom note left for the victim. According to cybersecurity analysts, PYSA is a variant of the Mespinoza ransomware family and has been active since at least October 2019.
Lockbit and Conti are two other major ransomware gangs that have conducted cyberattacks targeting critical infrastructure, although fewer than in previous months.
The FBI issued an alert regarding the ransomware gang’s activity increase after the first reports of PYSA operations reached worrisome levels in March 2021.
PYSA, like almost all ransomware gangs currently operating, steals data from a hacked network before encrypting the files in order to disrupt activities. Following the initial attack, the exfiltrated data is used as leverage in ransom discussions, with the threat actors threatening to make the information public unless the requested ransom is paid.
New “Faces”
Everest, a Russian-speaking ransomware organization that currently employs a different extortion strategy, is another actor mentioned in the NCC research. If their victims fail to pay the requested ransom, Everest sells access to their corporate network to other cybercriminals.
This approach complicates the impacted organizations’ lives even more, as they must now deal with several infections and attacks at the same time.
While selling ransomware-as-a-service has seen a surge in popularity over the last year, this is a rare instance of a group forgoing a request for a ransom and offering access to IT infrastructure – but we may see copycat attacks in 2022 and beyond.
Because ransomware is a constantly evolving threat that immediately adapts to new defenses, you should take adequate security measures in order to protect against it.
The CISA’s ransomware guide, which gives some strong security suggestions, is a fantastic place to start when identifying the best prevention strategies.
As Christmas is rapidly approaching and IT teams are operating understaffed during the holidays, implementing defenses even at the last minute could save the day.
Watch our new YouTube video about cyberattacks during the winter holidays and find out how to stay protected:
How Can Heimdal™ Help?
In the fight against ransomware, Heimdal™ Security is offering its customers an outstanding integrated cybersecurity suite including the Ransomware Encryption Protection module, that is universally compatible with any antivirus solution, and is 100% signature-free, ensuring superior detection and remediation of any type of ransomware, whether fileless or file-based (including the most recent ones like LockFile).
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.


 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management
 Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security