Contents:
A French security researcher discovered last week a security flaw through which cyber criminals could fully take over Windows domains: the PetitPotam vulnerability. This is basically an NTLM relay attack in the Windows system that permits hackers to take advantage of the domain controllers. This will eventually lead to the Windows domain’s whole takeover.
A lot of organizations use Microsoft Active Directory Certificate Services, the PKI server through which users, machines, and services authenticate on Windows domains, so they are exposed to this PetitPotam vulnerability.
How Does PetitPotam Vulnerability Work?
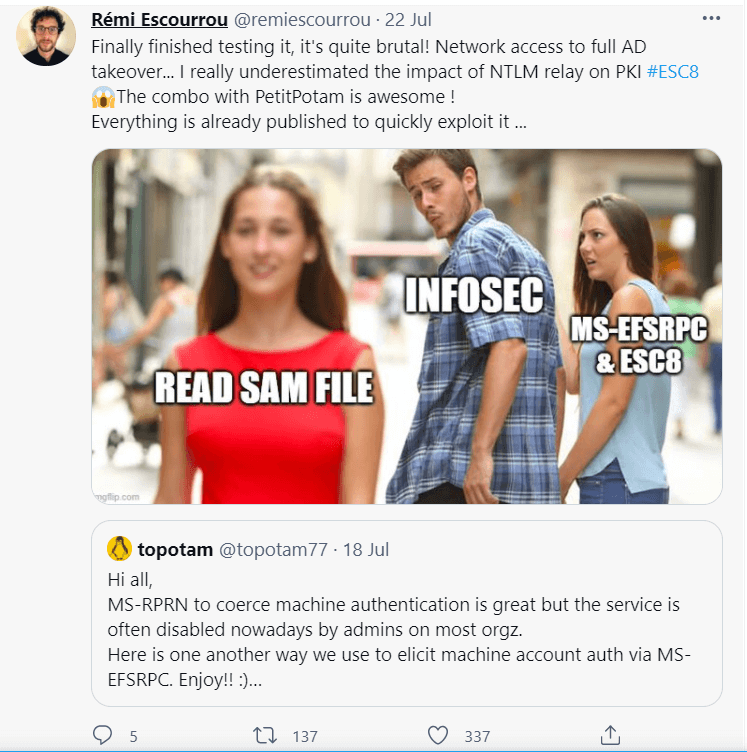
PetitPotam vulnerability was the discovery of Gilles Lionel (by his nickname Topotam), a French security researcher.
The flaw targets the EfsRpcOpenFileRaw function of the MS-EFSRPC API, Microsoft’s Encrypting File System Remote Protocol to perform an NTLS relay attack. A hacker could abuse this function in order to lead their malicious activities by abusing this protocol, designed to manage operations on data that is encrypted and stored on remote systems.
The French researcher Lionel published a POC (proof of concept) on Github where he explained the threat of the PetitPotam vulnerability. The MS-EFSRPC API could be exploited by a hacker who would determine a domain controller to authenticate against a remote NTLM.
Basically, the threat actor would send SMB requests to the MS-EFSRPC interface of a remote system, then the targeted computer starts the authentication procedure and discloses authentication information to the cybercriminal.
The goal of threat actors is to gather this shared data by stealing hash and certificates and take advantage of them for their malicious scopes in achieving access to remote systems, device identity, and privileges. This action eventually leads to a full domain takeover, so an enterprise internal network could be entirely in the hands of a hacker.
Hasain Alshakarti, another security researcher, also mentioned that
An attacker can target a Domain Controller to send its credentials by using the MS-EFSRPC protocol and then relaying the DC NTLM credentials to the Active Directory Certificate Services AD CS Web Enrollment pages to enroll a DC certificate.
Mitigation Measures Proposed by Researchers
As per Bleeping Computer mentioning, the researcher who found this flaw in Windows systems, Gilles Lionel added that NTLM authentication disablement or protections enablement would be the only methods to diminish this flaw. Protection enablement could be done via channels binding, SMB signing, or LDAP signing. However, even if the EFS service is turned off, this will not stop hackers exploit the PetitPotam vulnerability.
Another researcher who shared his input on mitigation measures is Benjamin Delpy, the creator of Mimikatz. He recommended removing web enrollment, use Kerberos instead of Nego/NTLM, so you can remove or disable the latter, and finally since the PKI Webserver does not possess a default certificate, Extended Protection for Authentication with SSL would be useful.
Microsoft Steps in and Provides Mitigation Measures
Microsoft addressed this issue and recommended to:
- Disable NTLM if it is not necessary, for example, it might not be needed on Domain controllers;
- Safeguard credential with the Extended Protection for Authentication;
- Make use of SBM signing or other signing characteristics on services that use NTLM authentication.
How Do You Know You Are Exposed to PetitPotam Vulnerability
Following Microsoft’s advisory on PetitPotam vulnerability, you and your organization could be exposed to malicious attacks if you use the Active Directory Certificate Services (AD CS) containing Certificate Authority Web Enrollment and Certificate Enrollment Web Service services and if your domain is set up for NTLM authentication.
PetitPotam Vulnerability Does Not Stop Here
If the MS-EFSRPC API is abused, this could lead to other extended attacks.
Lionel shared his opinion on other further attacks that could be done by exploiting the PetitPotam vulnerability with the Bleeping Computer publication. If successfully exploited, it could lead to
NTLMv1 downgrade and relaying machine account on computers where this machine account is local admin (SCCM, exchange server, are often in this situation for example).










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security